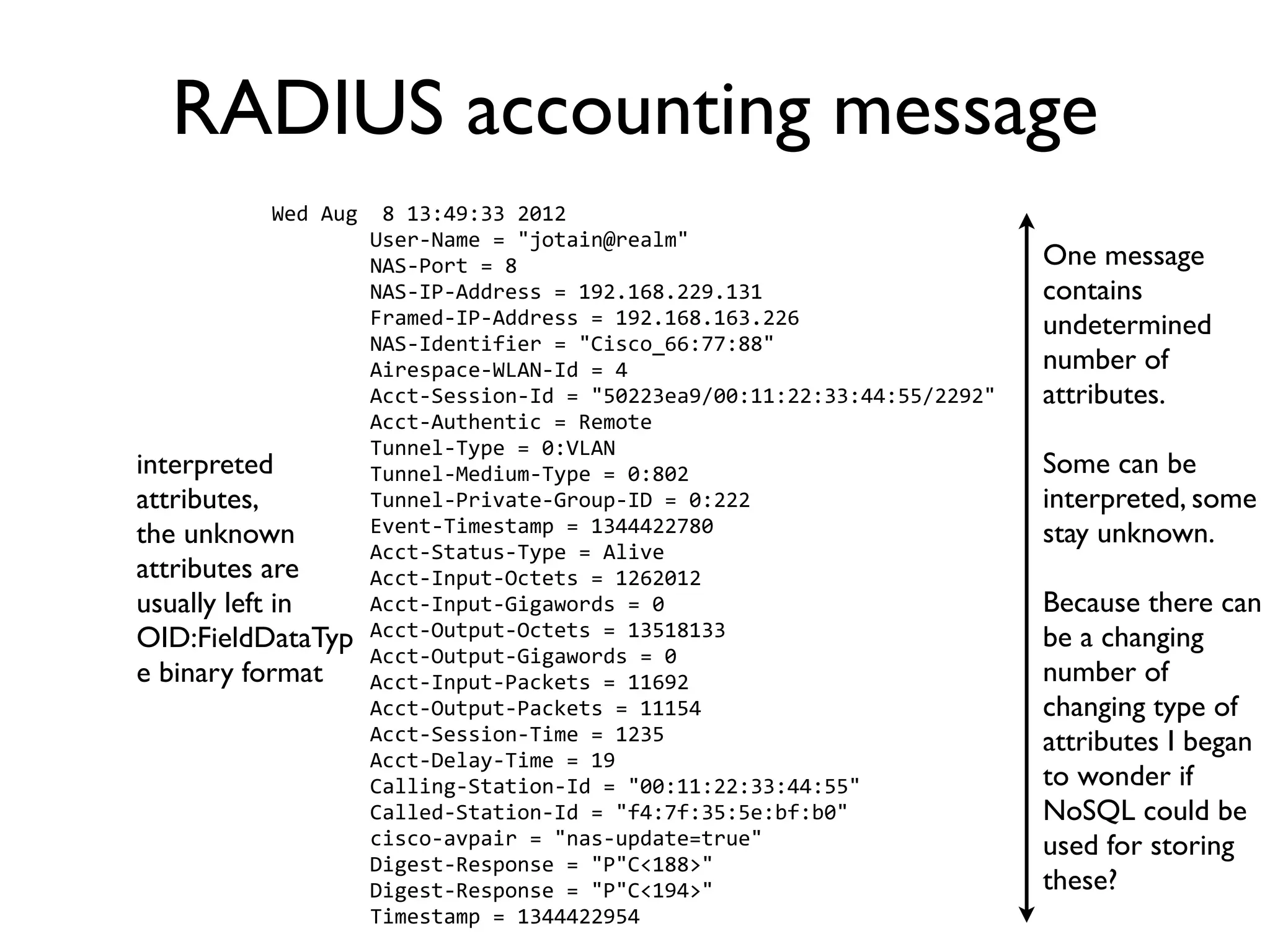
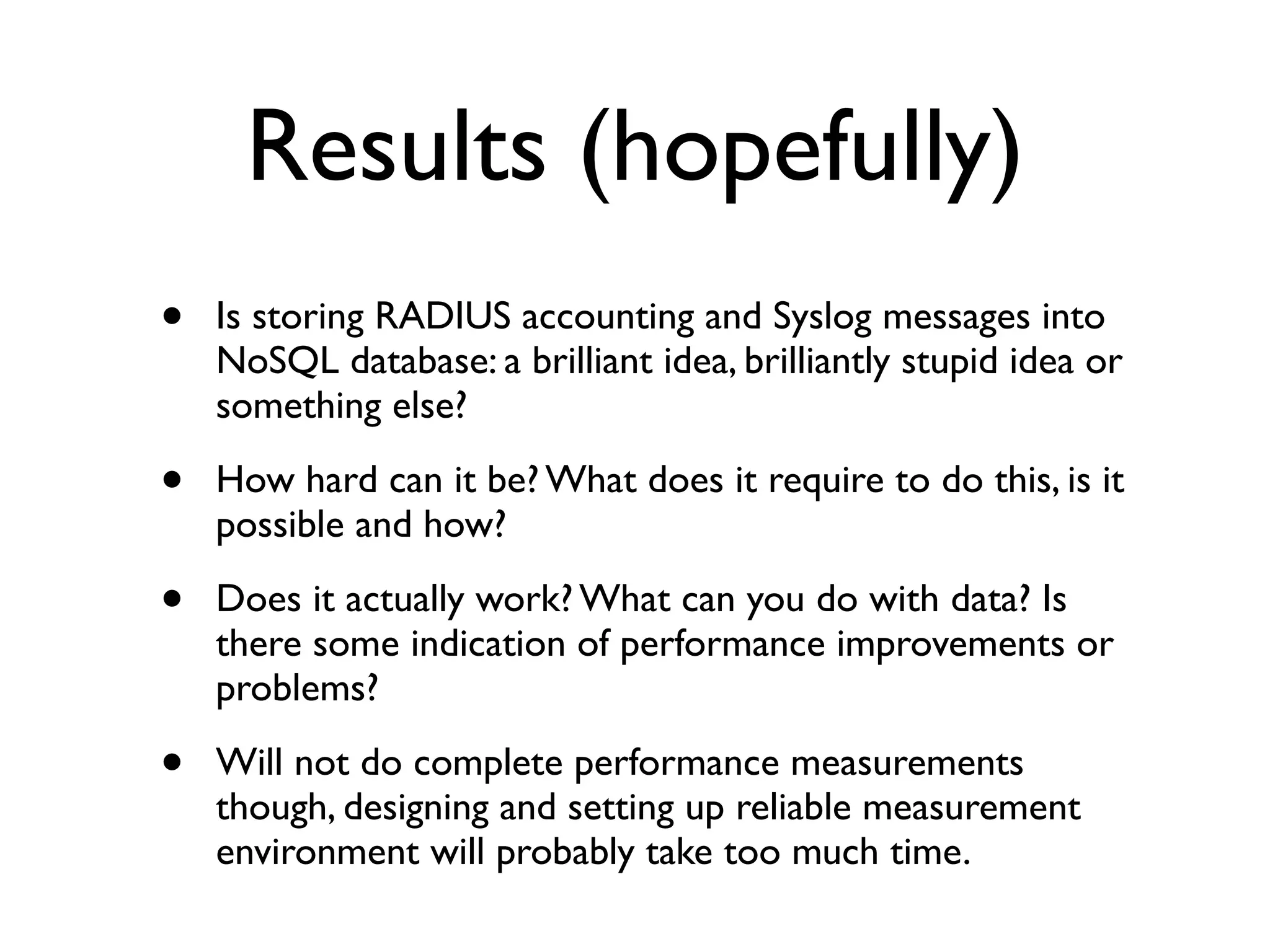
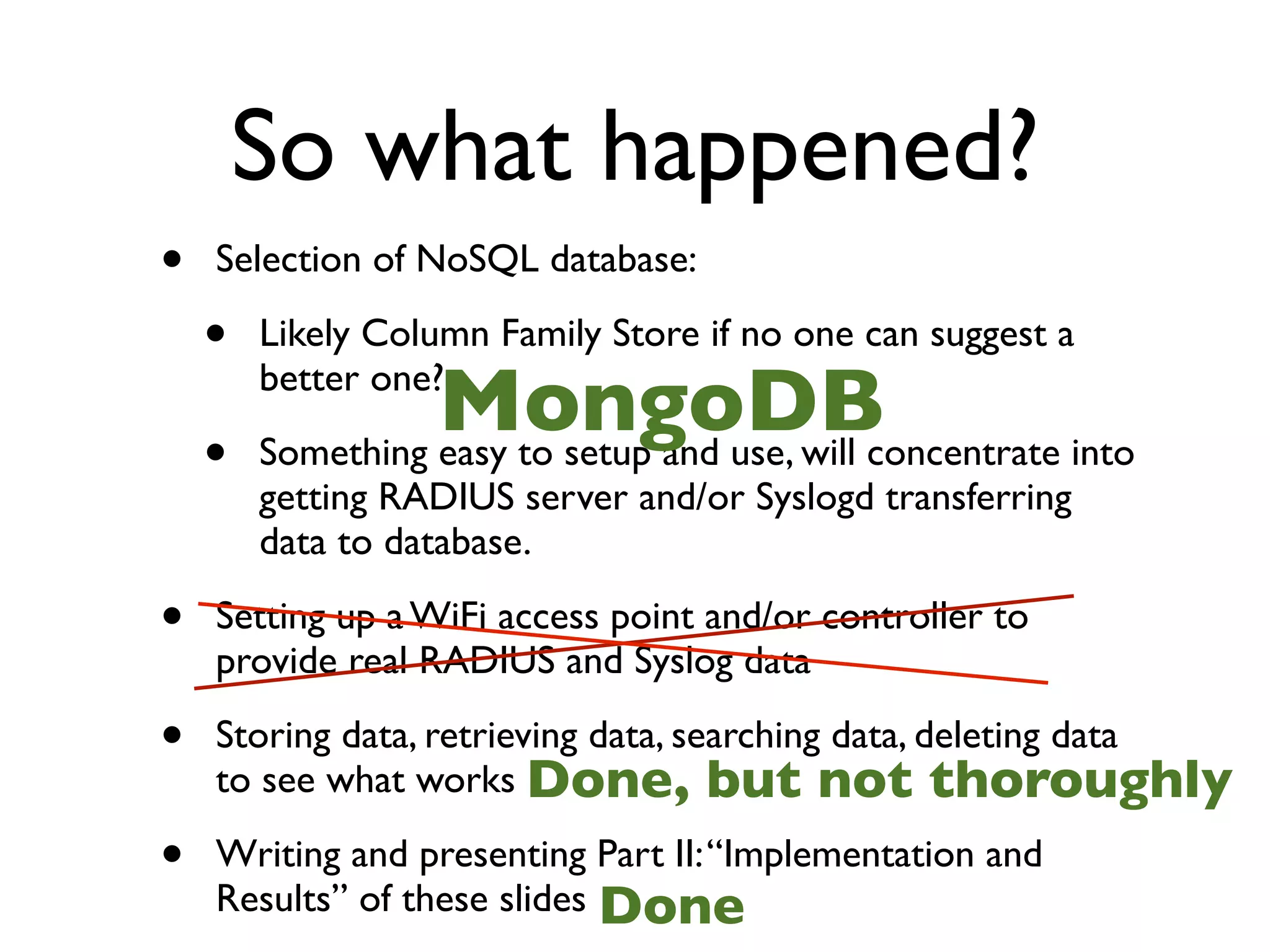
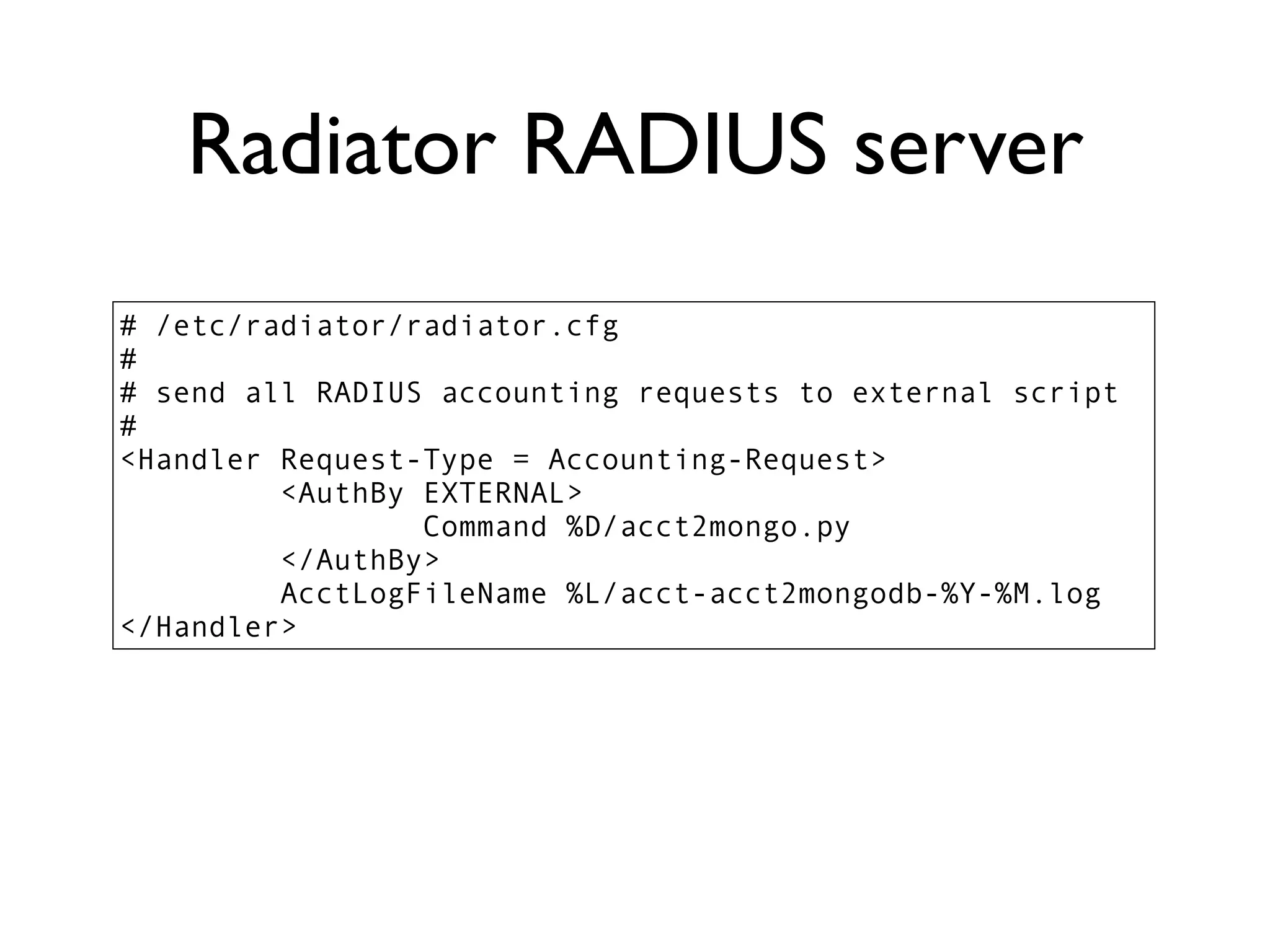
The document discusses the potential use of NoSQL databases for storing RADIUS accounting and syslog data, highlighting both advantages and challenges. It suggests that NoSQL may offer better scalability and flexibility for large data sets, but emphasizes the need for careful design and consideration of data types for effective production use. Despite its benefits, the author notes that the transition from SQL to NoSQL requires thorough planning and could be as complex as traditional database optimization.
![Syslog message
Until researching The
syslog
message
has
the
following
ABNF
[RFC5234]
definition:
into this I thought
SYSLOG-‐MSG
=
HEADER
SP
STRUCTURED-‐DATA
[SP
MSG]
Syslog messages had
HEADER
=
PRI
VERSION
SP
TIMESTAMP
SP
HOSTNAME
SP
APP-‐NAME
SP
PROCID
SP
MSGID
fixed structure and
PRI
=
"<"
PRIVAL
">"
PRIVAL
=
1*3DIGIT
;
range
0
..
191
could be then
VERSION
=
NONZERO-‐DIGIT
0*2DIGIT
HOSTNAME
=
NILVALUE
/
1*255PRINTUSASCII
handled with fixed
APP-‐NAME
=
NILVALUE
/
1*48PRINTUSASCII
database schema.
PROCID
=
NILVALUE
/
1*128PRINTUSASCII
MSGID
=
NILVALUE
/
1*32PRINTUSASCII
TIMESTAMP
=
NILVALUE
/
FULL-‐DATE
"T"
FULL-‐TIME
Then I read the
FULL-‐DATE
=
DATE-‐FULLYEAR
"-‐"
DATE-‐MONTH
"-‐"
DATE-‐MDAY
DATE-‐FULLYEAR
=
4DIGIT
RFC5424: http://
DATE-‐MONTH
=
2DIGIT
;
01-‐12
DATE-‐MDAY
=
2DIGIT
;
01-‐28,
01-‐29,
01-‐30,
01-‐31
based
on
tools.ietf.org/html/
;
month/year
FULL-‐TIME
=
PARTIAL-‐TIME
TIME-‐OFFSET
rfc5424
PARTIAL-‐TIME
=
TIME-‐HOUR
":"
TIME-‐MINUTE
":"
TIME-‐SECOND
[TIME-‐SECFRAC]
TIME-‐HOUR
=
2DIGIT
;
00-‐23
TIME-‐MINUTE
=
2DIGIT
;
00-‐59
TIME-‐SECOND
=
2DIGIT
;
00-‐59
TIME-‐SECFRAC
=
"."
1*6DIGIT
TIME-‐OFFSET
=
"Z"
/
TIME-‐NUMOFFSET
TIME-‐NUMOFFSET
=
("+"
/
"-‐")
TIME-‐HOUR
":"
TIME-‐MINUTE Here we have once
STRUCTURED-‐DATA
=
NILVALUE
/
1*SD-‐ELEMENT
again parameters,
SD-‐ELEMENT
=
"["
SD-‐ID
*(SP
SD-‐PARAM)
"]"
SD-‐PARAM
=
PARAM-‐NAME
"="
%d34
PARAM-‐VALUE
%d34
although they are
SD-‐ID
=
SD-‐NAME
PARAM-‐NAME
=
SD-‐NAME
within one defined
PARAM-‐VALUE
=
UTF-‐8-‐STRING
;
characters
'"',
''
and
;
']'
MUST
be
escaped.
STRUCTURED-
SD-‐NAME
=
1*32PRINTUSASCII
;
except
'=',
SP,
']',
%d34
(")
DATA field.
MSG
=
MSG-‐ANY
/
MSG-‐UTF8
MSG-‐ANY
=
*OCTET
;
not
starting
with
BOM
MSG-‐UTF8
=
BOM
UTF-‐8-‐STRING
So could NoSQL be
BOM
=
%xEF.BB.BF used also for Syslog?](https://image.slidesharecdn.com/kh-using-nosql-databases-to-store-radius-and-syslog-data-121210101815-phpapp01/75/Using-NoSQL-databases-to-store-RADIUS-and-Syslog-data-4-2048.jpg)


![#!/usr/bin/env python
from pymongo import Connection
import datetime
acct2mongo.py
import sys
def main():
line = str()
post = dict()
# opening connection
connection = Connection( 'localhost', 27017)
# database 'radius'
db = connection['radius']
# collection 'accounting'
collection = db['accounting']
post['acct2mongotimestamp'] = datetime.datetime.utcnow()
for line in sys.stdin.readlines():
pieces = line.split(' = ', 1)
if len(pieces) == 2:
post[pieces[0].strip().strip('"')]=pieces[1].strip().strip('"')
collection.insert(post)
connection.end_request()
connection.disconnect()
# 0 Means reply with an acceptance. For Access-Requests,
# an Access-Accept will be sent. For Accounting-Requests,
# an Accounting-Response will be sent.
return 0
if __name__ == '__main__':
main()](https://image.slidesharecdn.com/kh-using-nosql-databases-to-store-radius-and-syslog-data-121210101815-phpapp01/75/Using-NoSQL-databases-to-store-RADIUS-and-Syslog-data-19-2048.jpg)