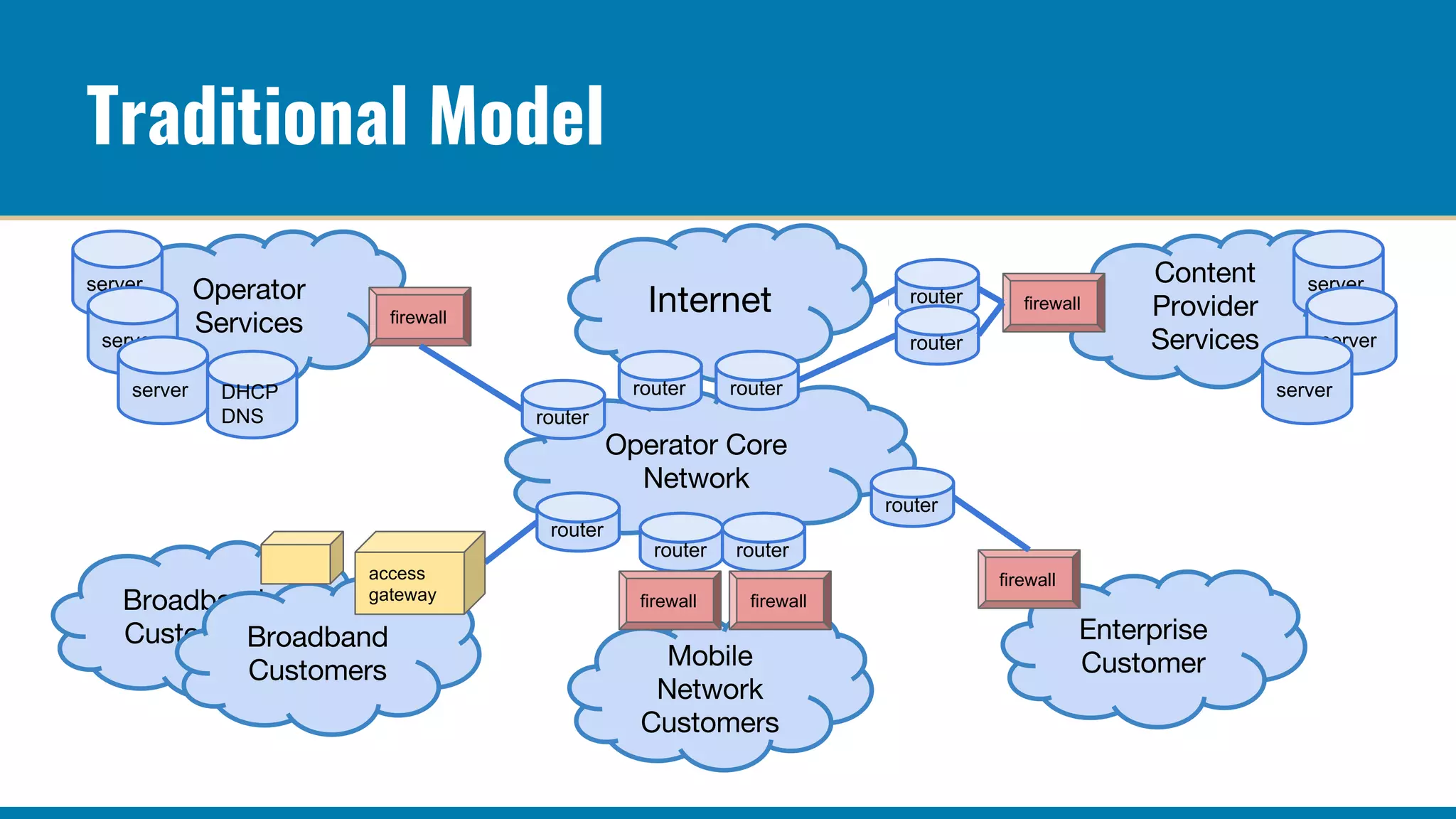
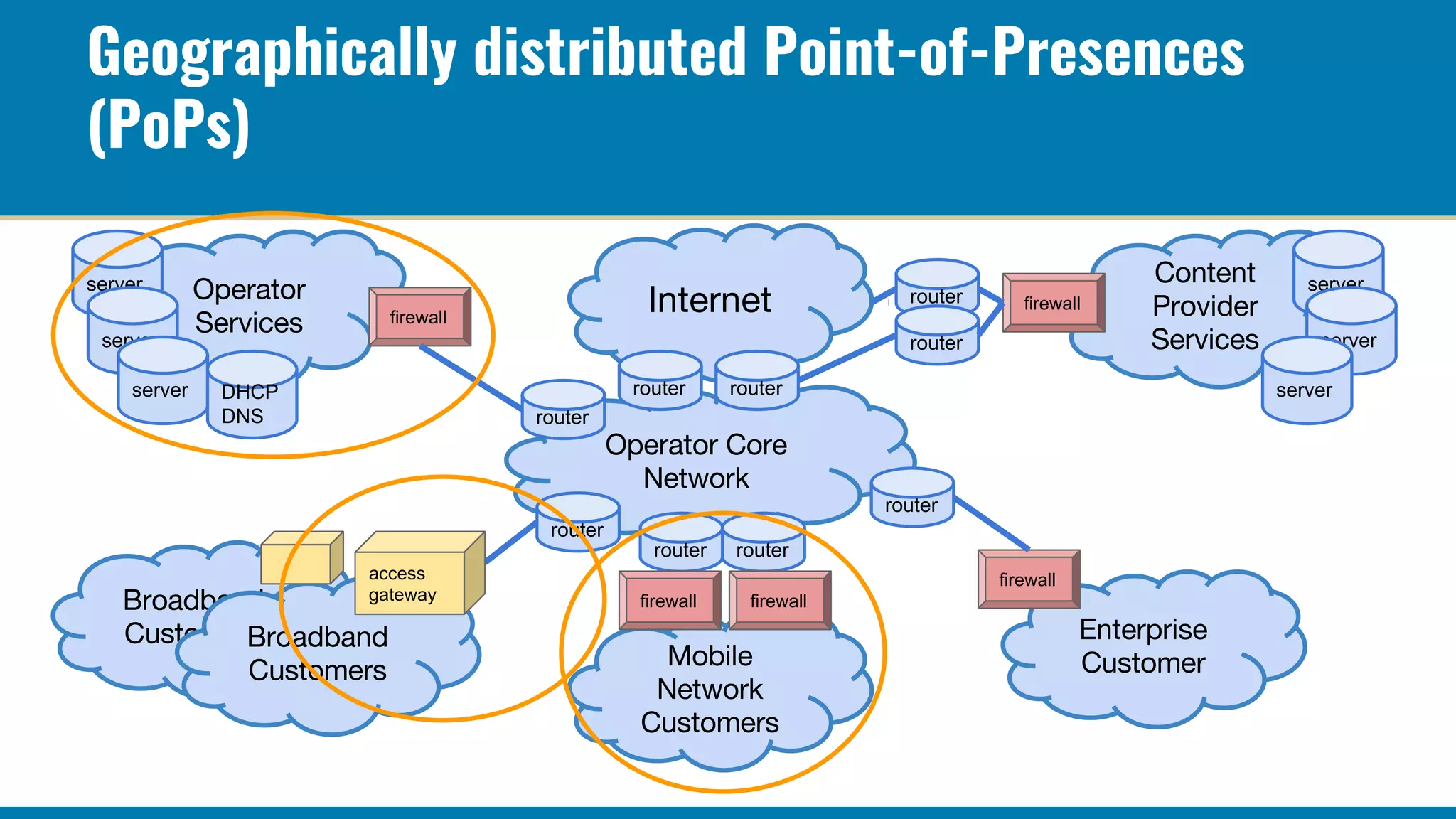
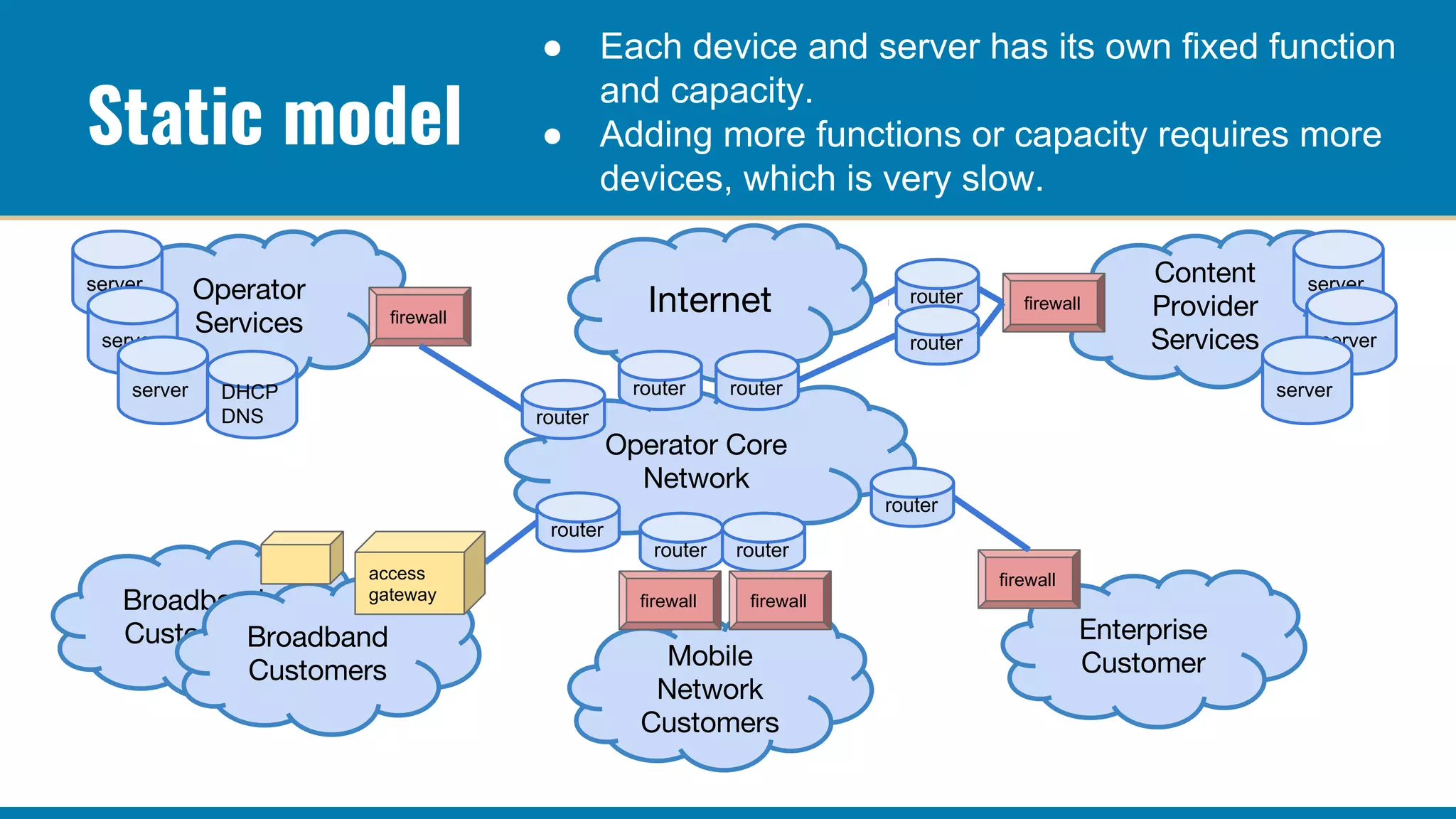
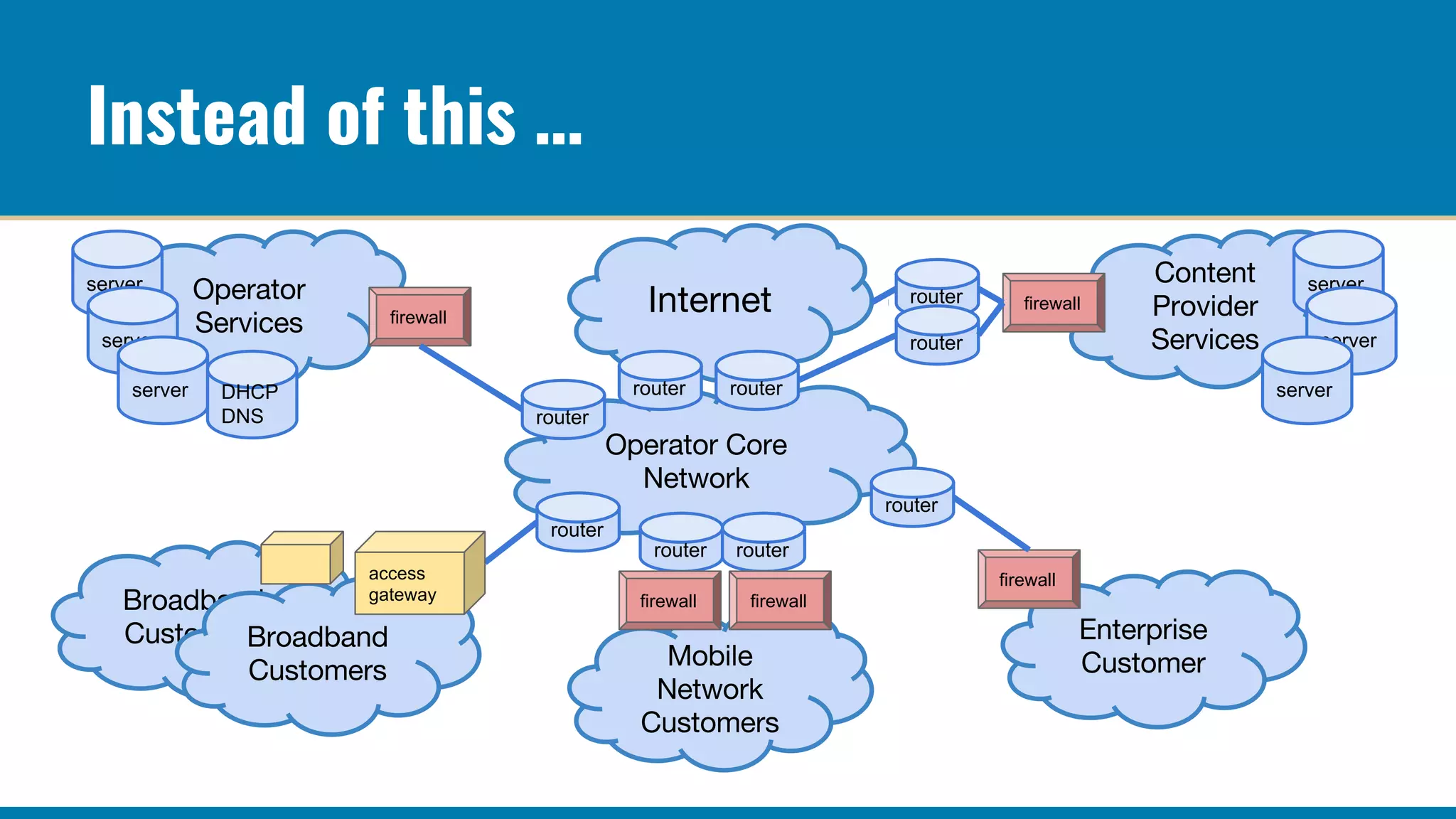
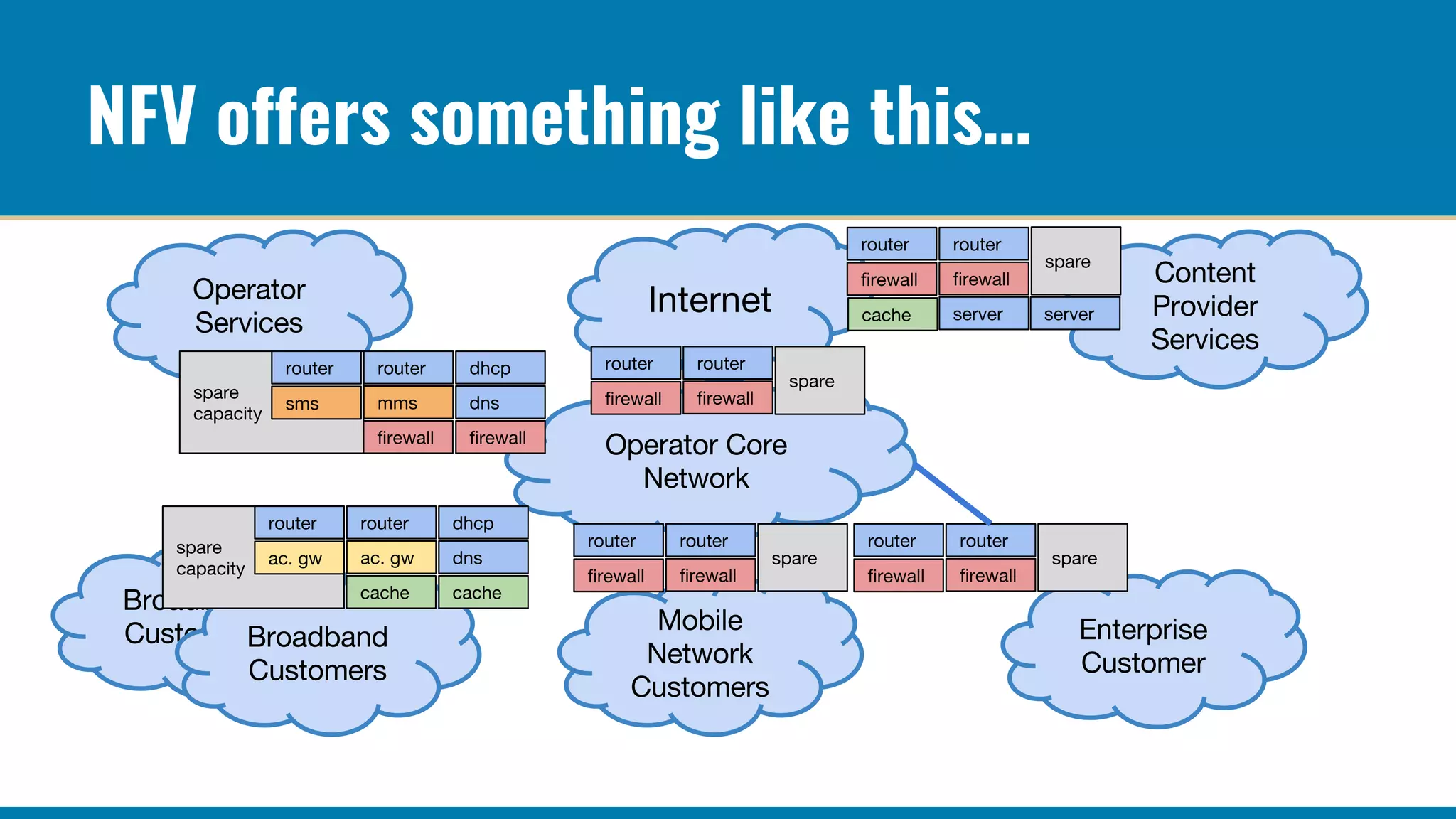
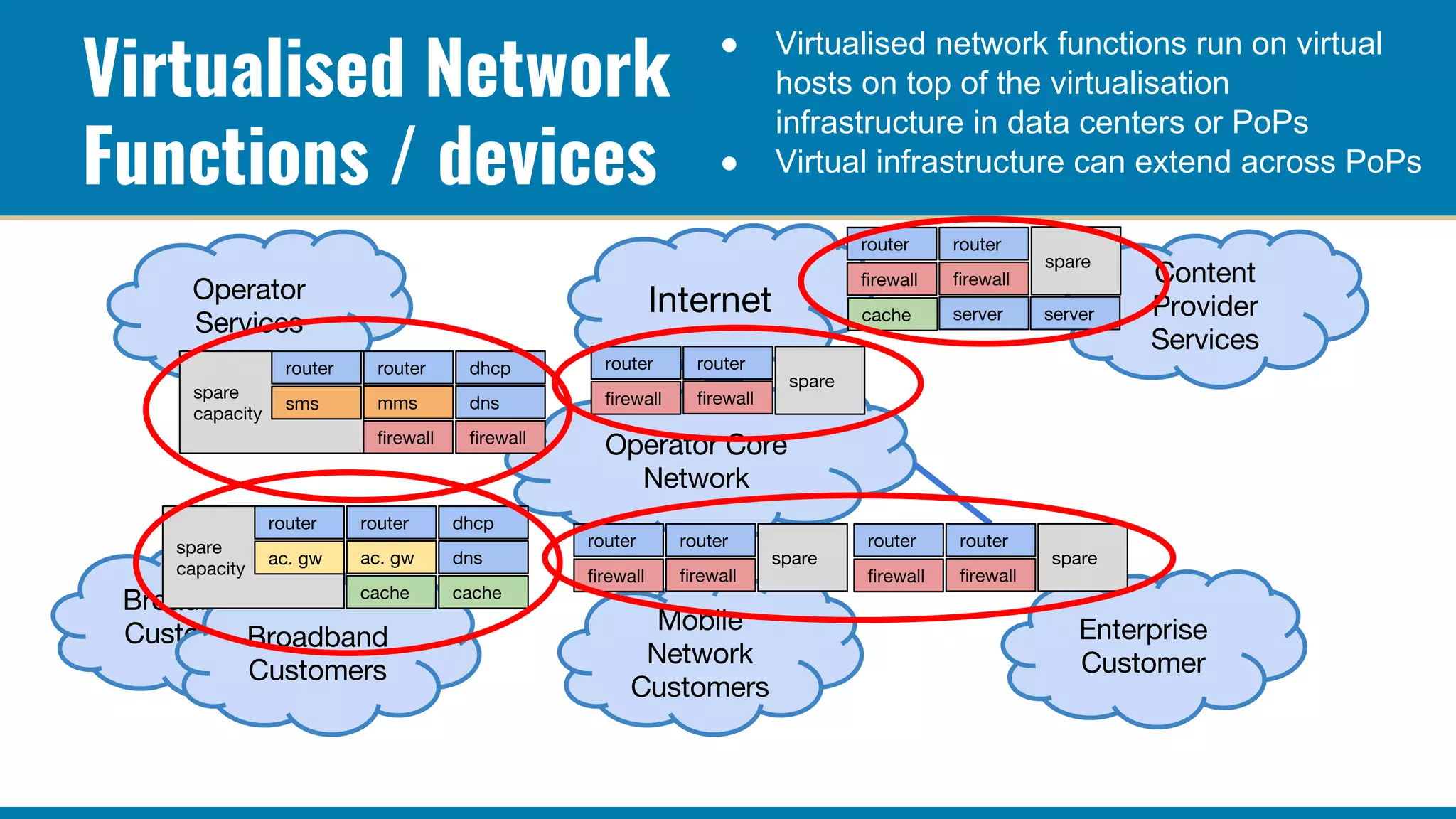
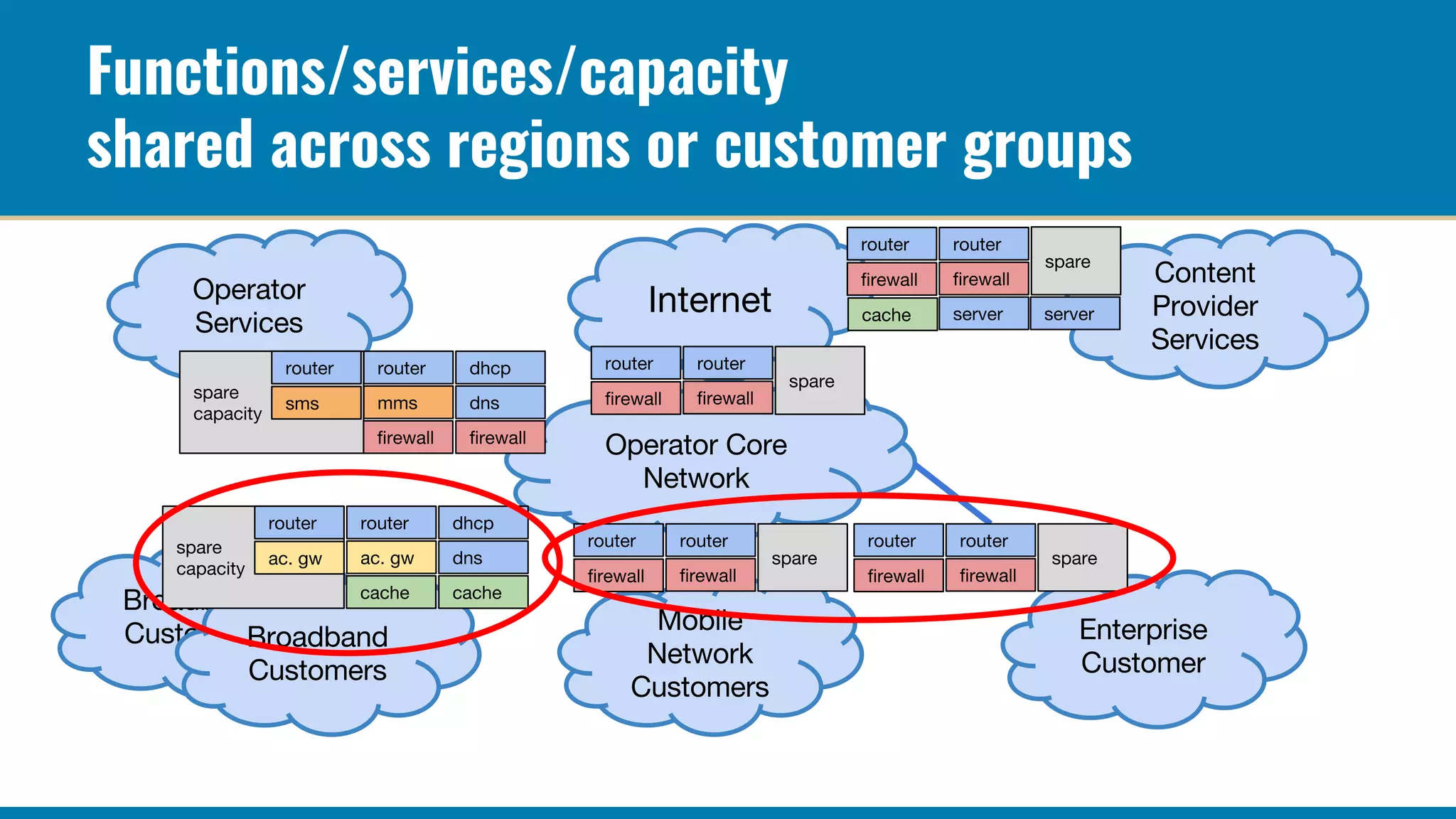
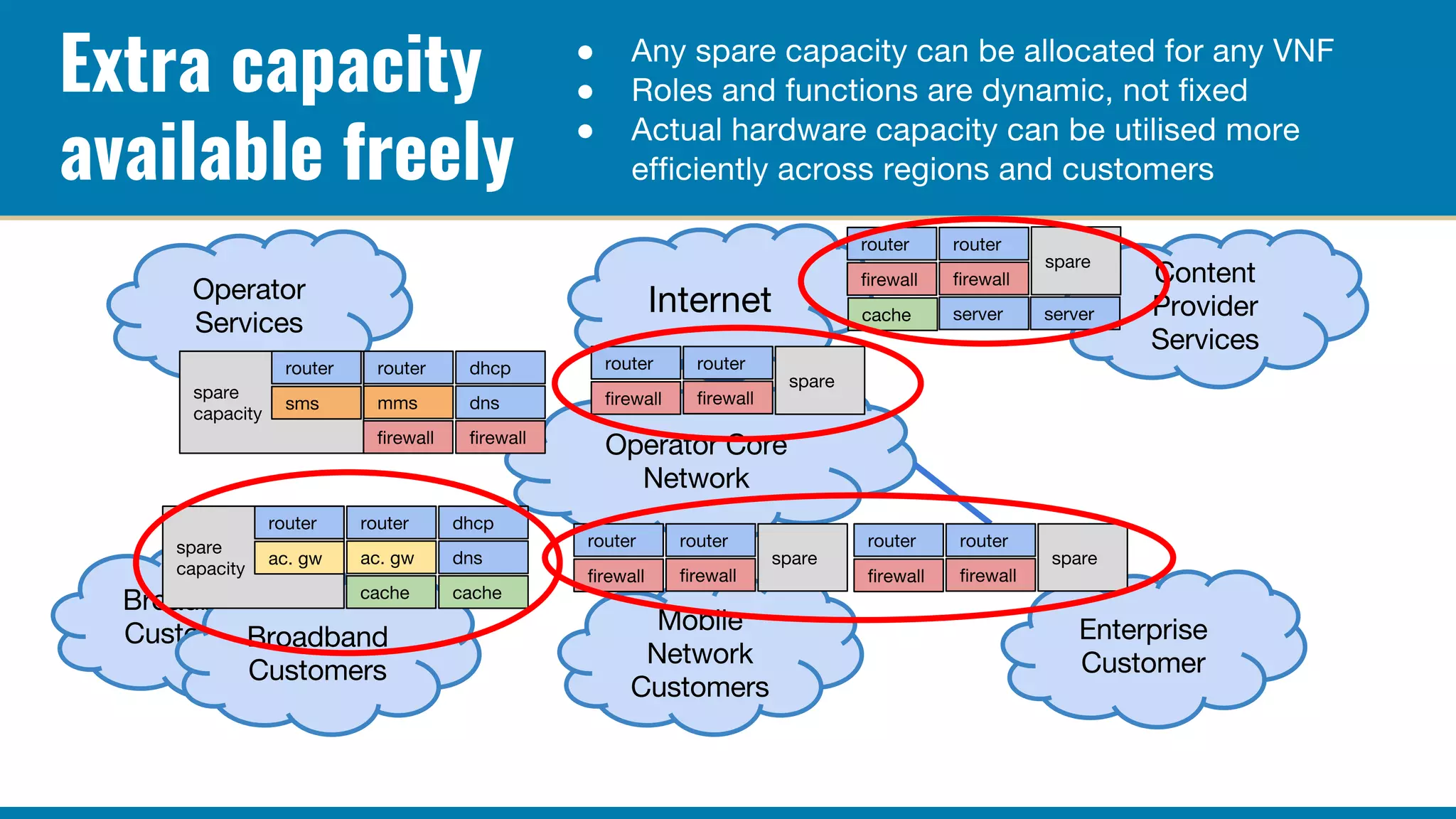
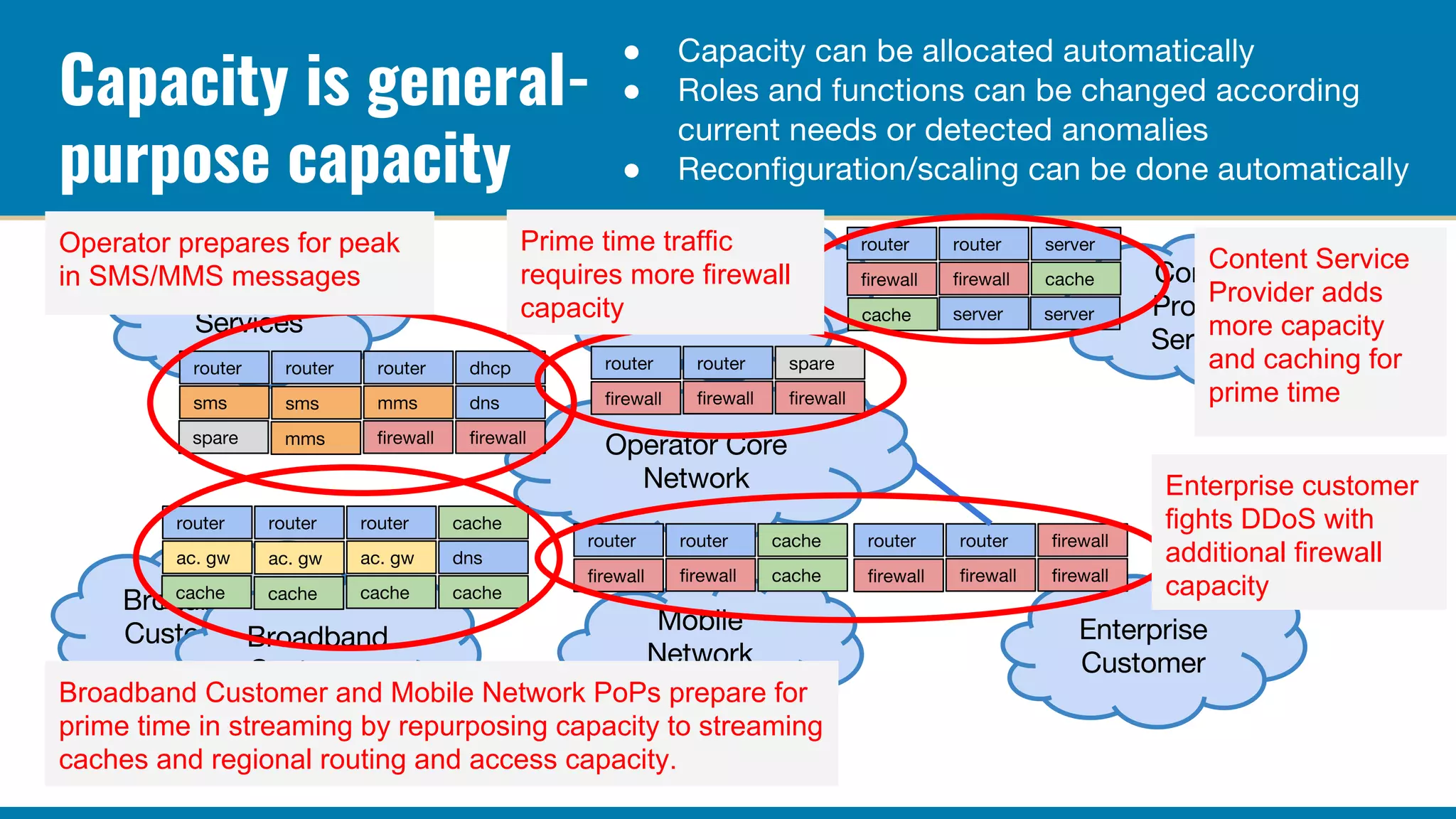
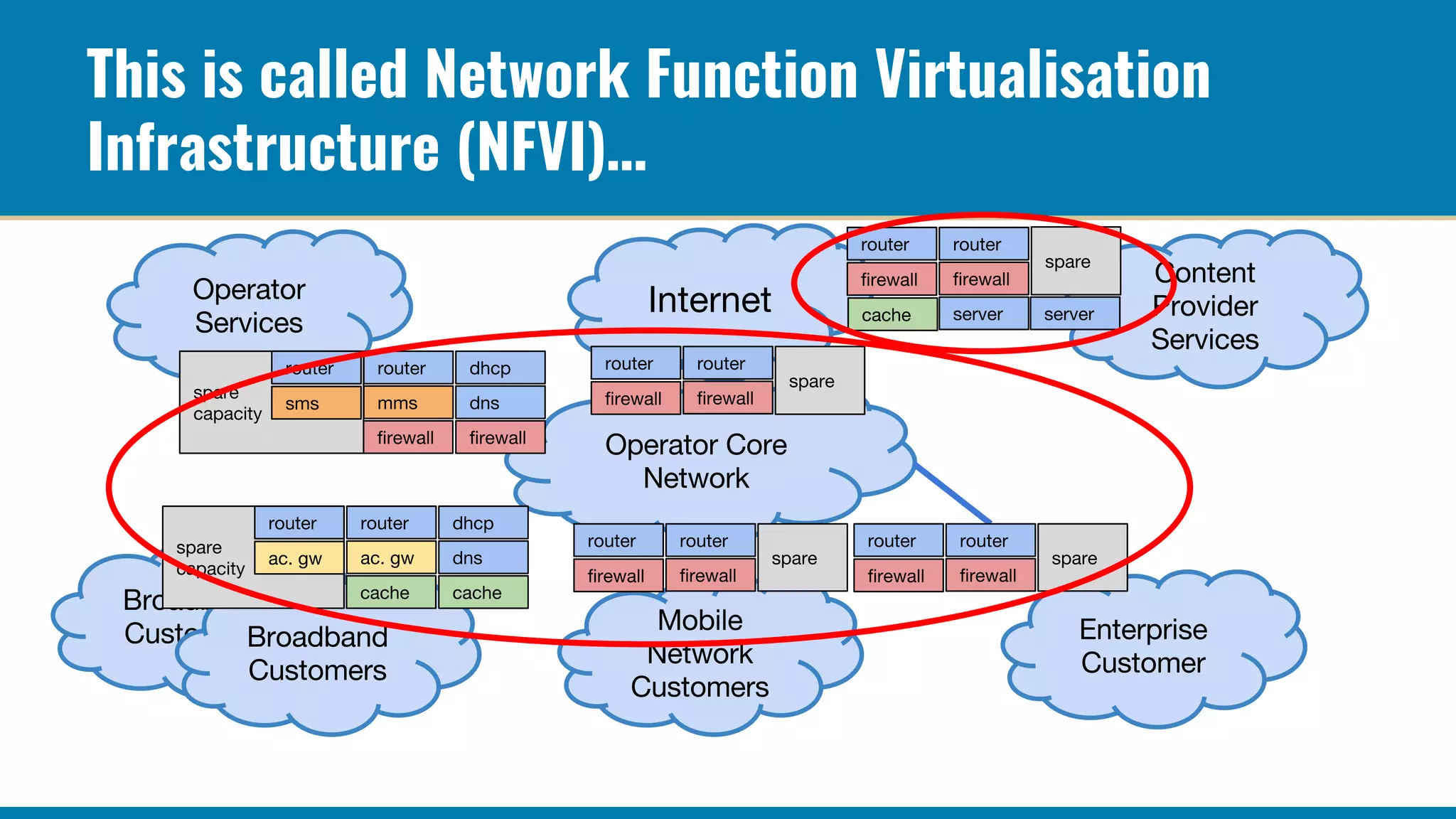
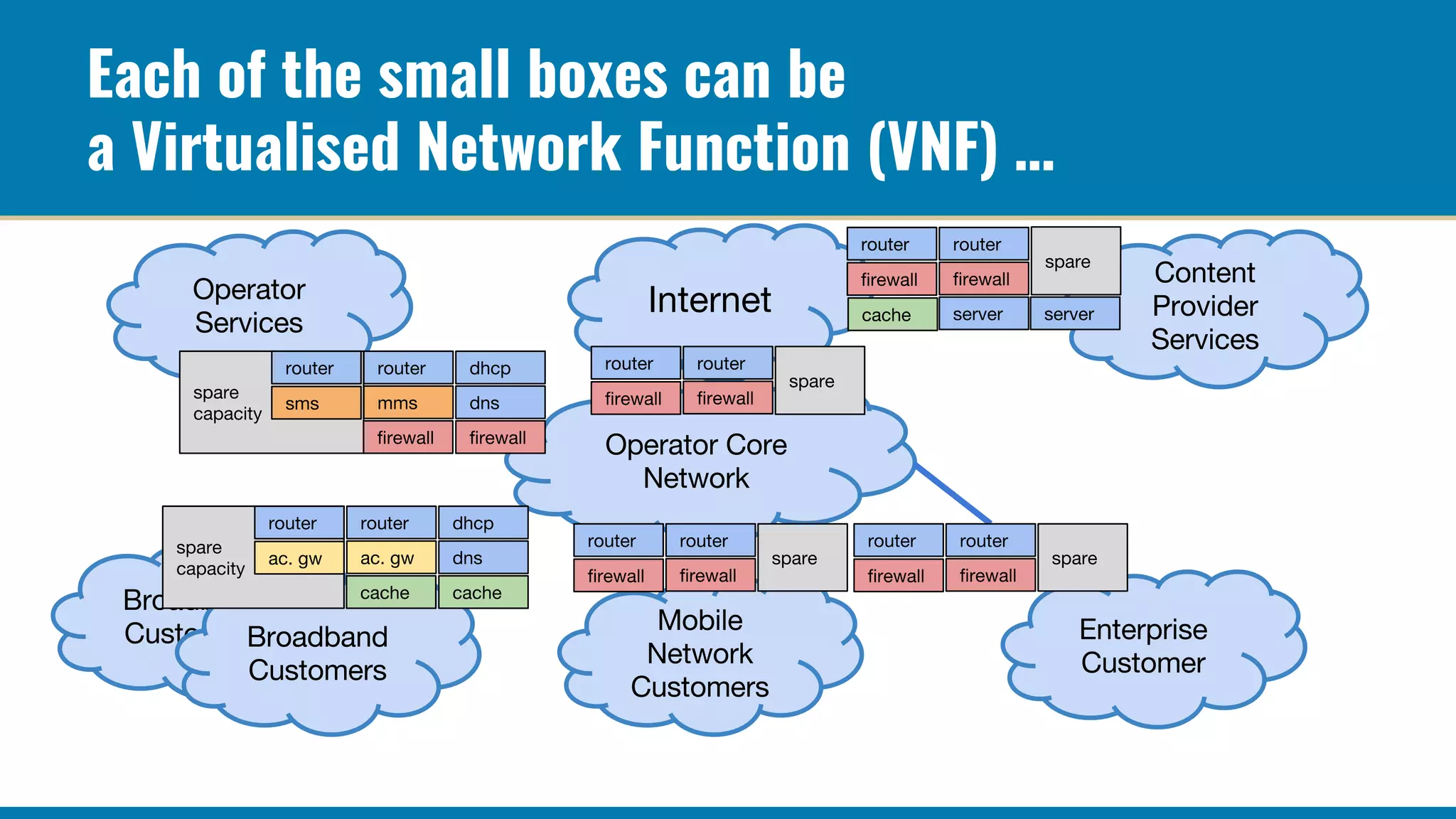
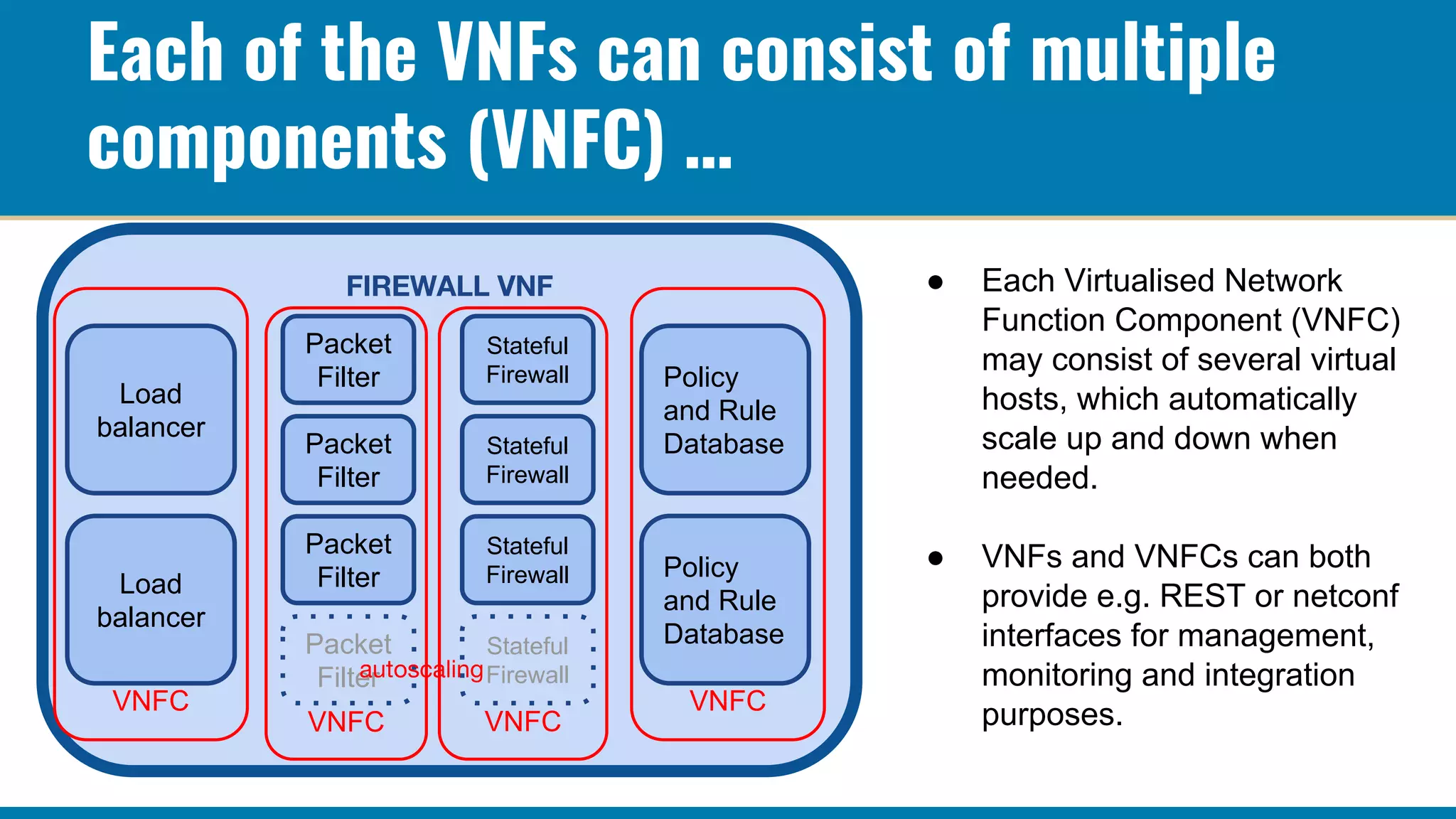
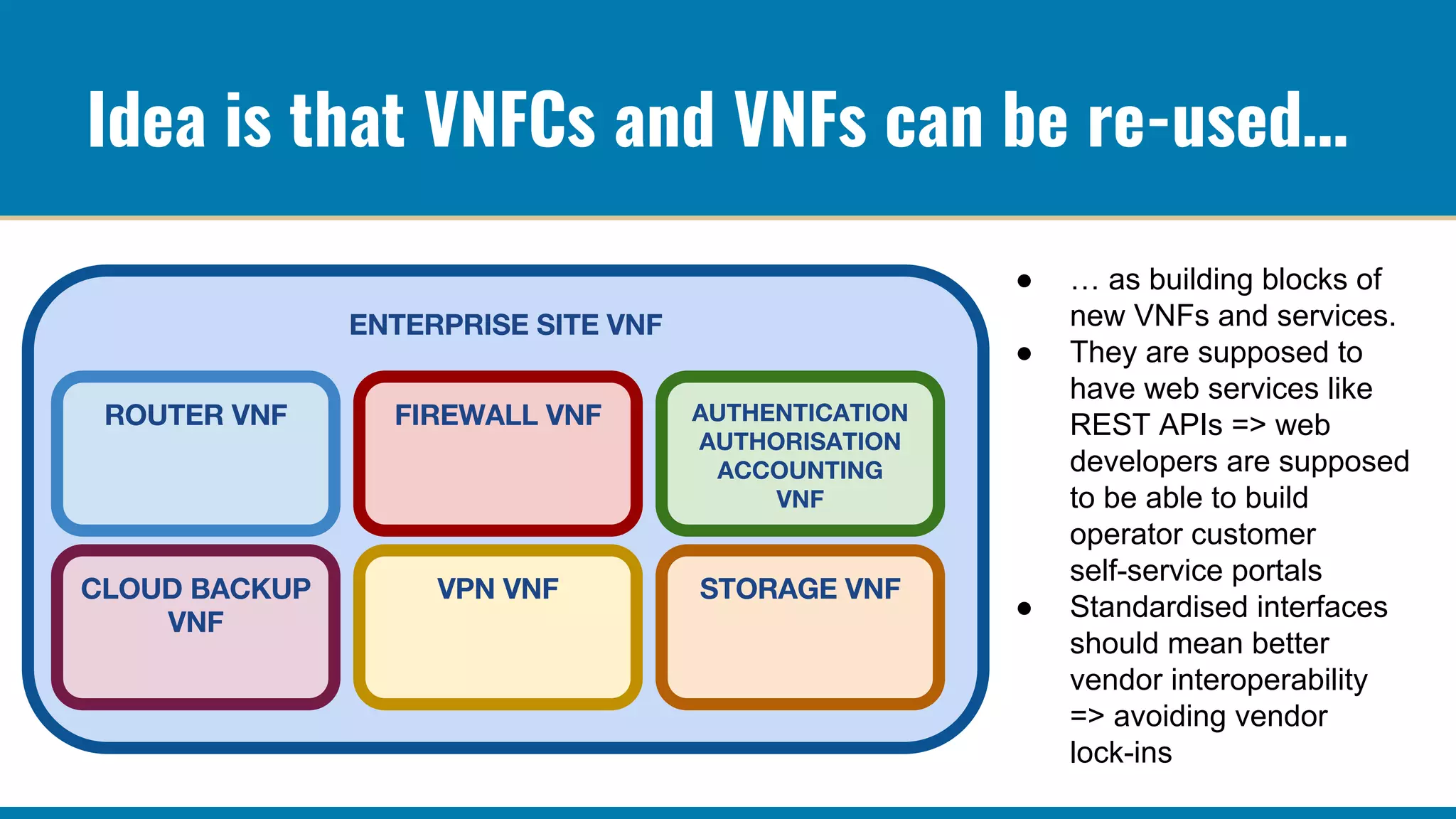
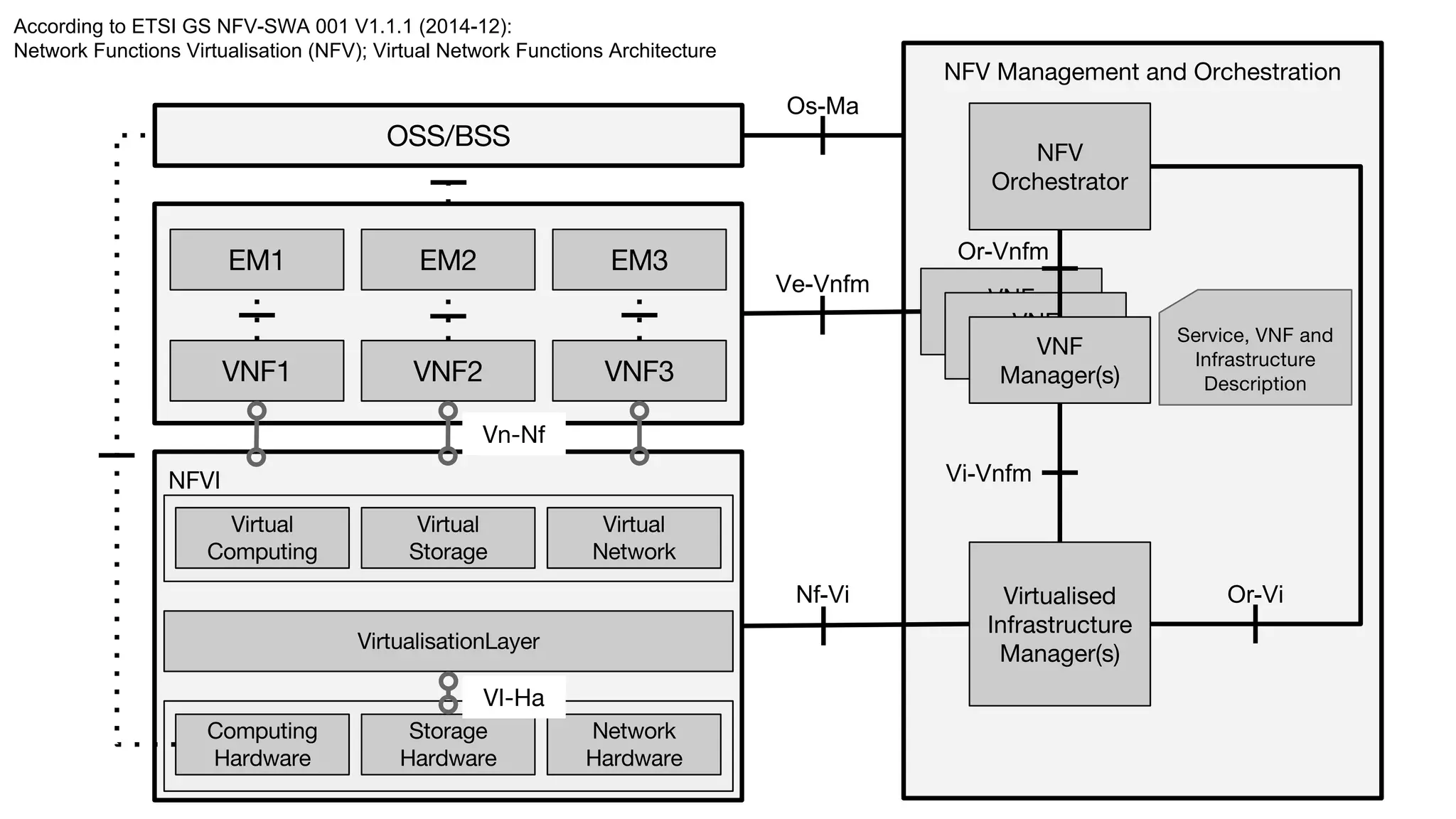
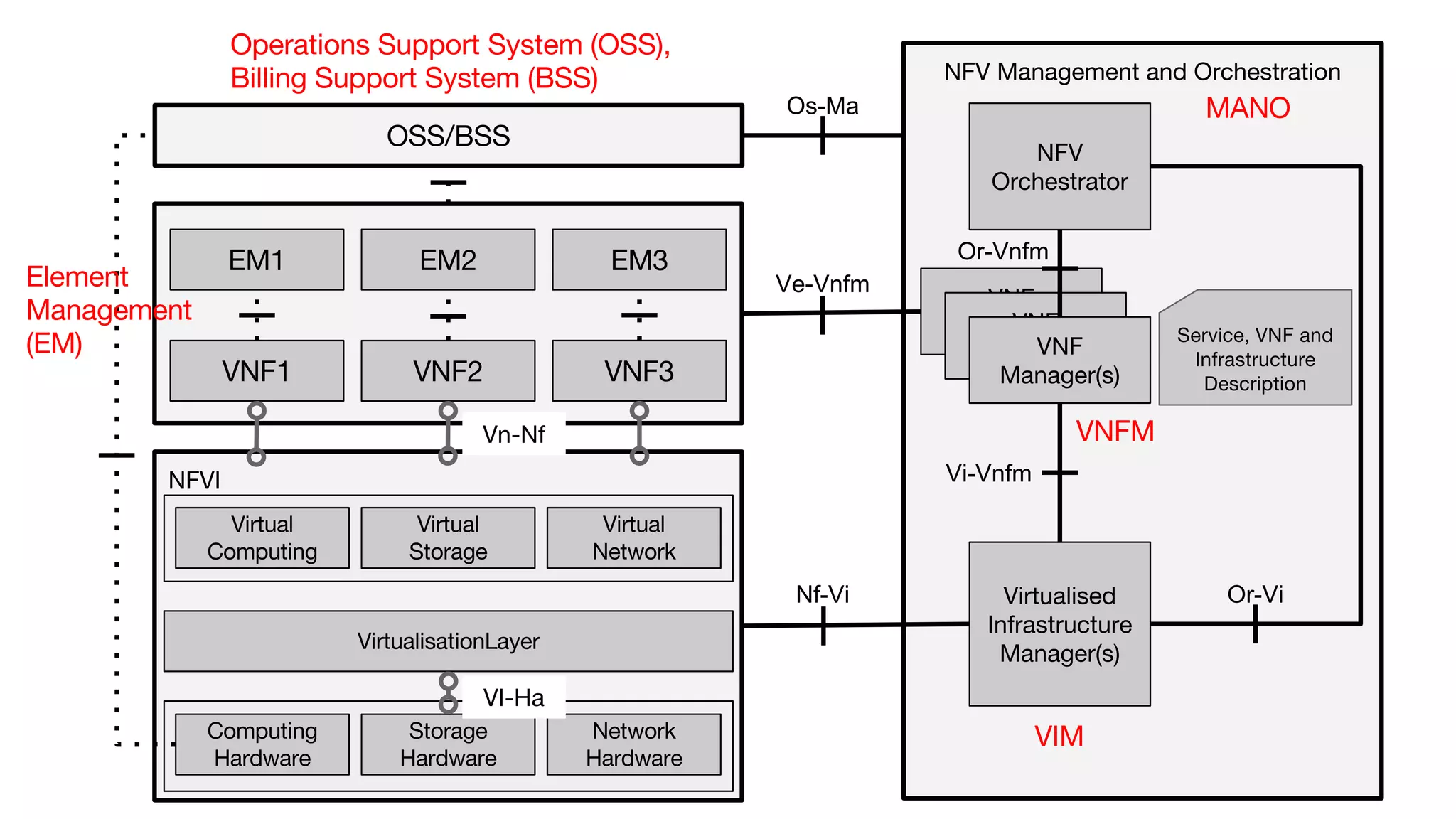
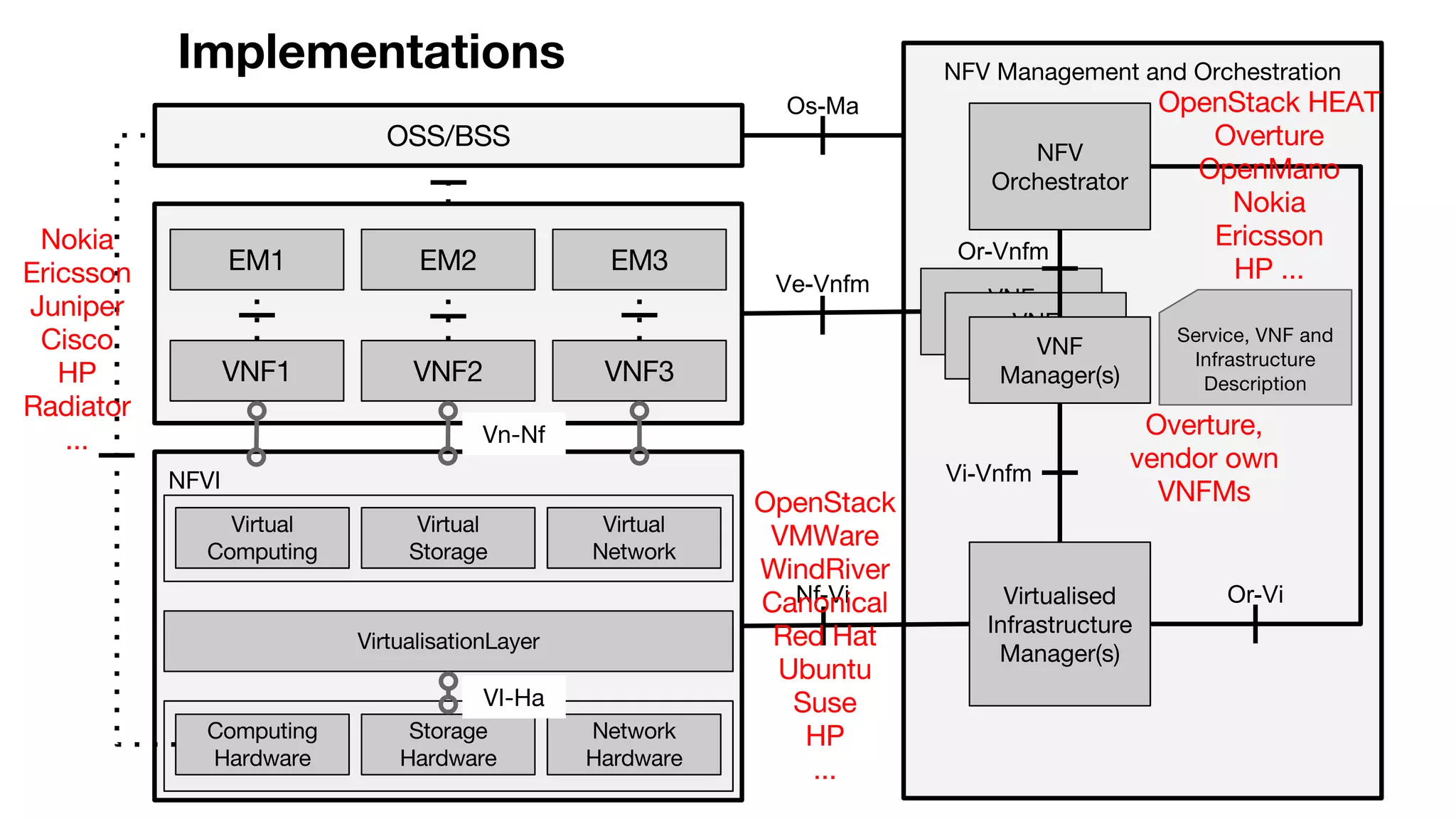
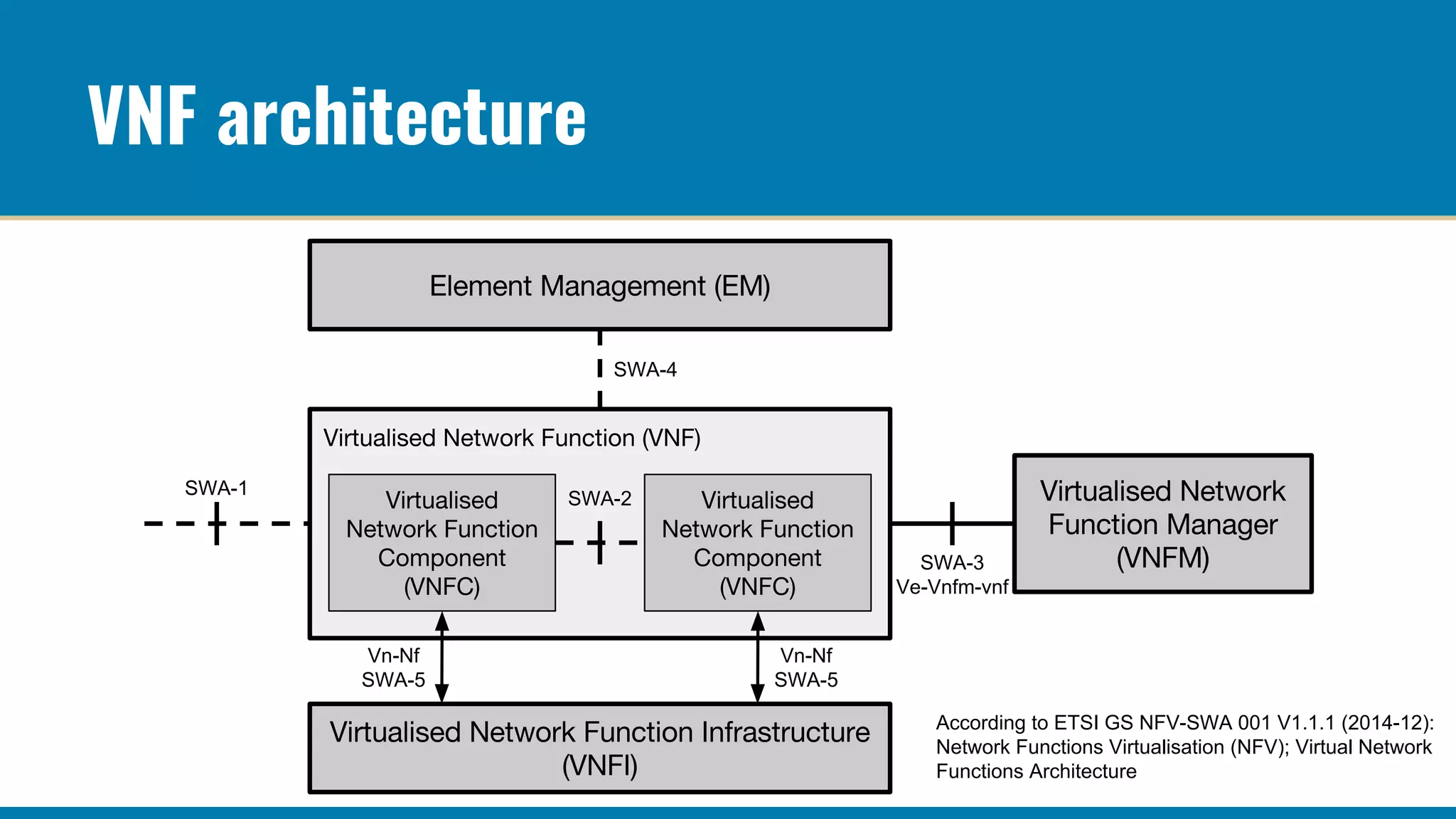
Network Function Virtualization (NFV) seeks to replace traditional fixed-function network devices with virtualized network functions (VNFs) that run on shared infrastructure across distributed points-of-presence (PoPs), enabling greater flexibility and scalability. NFV allows for dynamic capacity sharing, automatic scaling, and the ability to repurpose resources in response to varying demands, such as during peak traffic periods. Additionally, it promotes interoperability through standardized interfaces, reducing vendor lock-in and facilitating the development of self-service portals for operators.