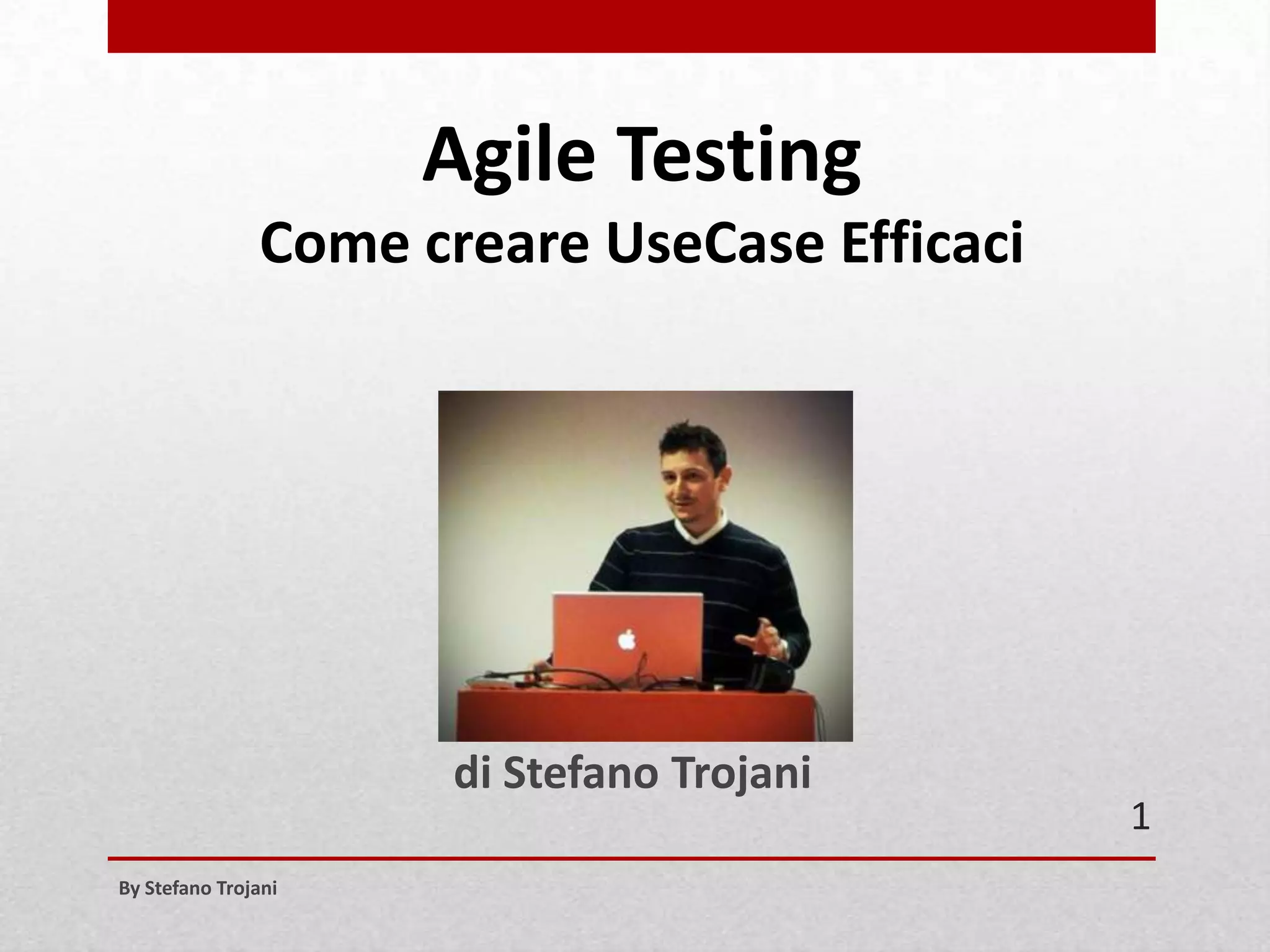
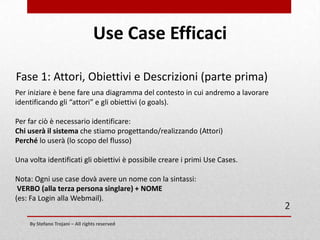
Il documento di Stefano Trojani descrive come creare use case efficaci, iniziando con l'identificazione di attori e obiettivi. Viene enfatizzata l'importanza di scrivere scenari di successo e di mantenere il livello di dettaglio appropriato per evitare ridondanze e complessità eccessive. Le fasi principali includono l'identificazione, la scrittura e l'adattamento degli use case per gli sprint di sviluppo.
![Use Case Efficaci
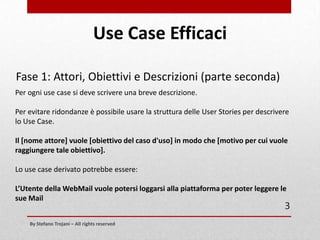
Fase 1: Attori, Obiettivi e Descrizioni (parte seconda)
Ogni Use Case deve avere una breve descrizione.
Per evitare ridondanze è possibile usare la struttura delle User Stories per descrivere
lo Use Case.
Il [nome attore] vuole [obiettivo del caso d'uso] in modo tale che [motivo per cui
vuole raggiungere tale obiettivo].
Lo use case derivato potrebbe essere:
L’Utente della WebMail vuole potersi loggarsi alla piattaforma per poter leggere le
sue Mail
4
By Stefano Trojani – All rights reserved](https://image.slidesharecdn.com/usecaseefficaci-131029094922-phpapp02/85/Agile-Testing-Come-Scrivere-Use-Case-4-320.jpg)