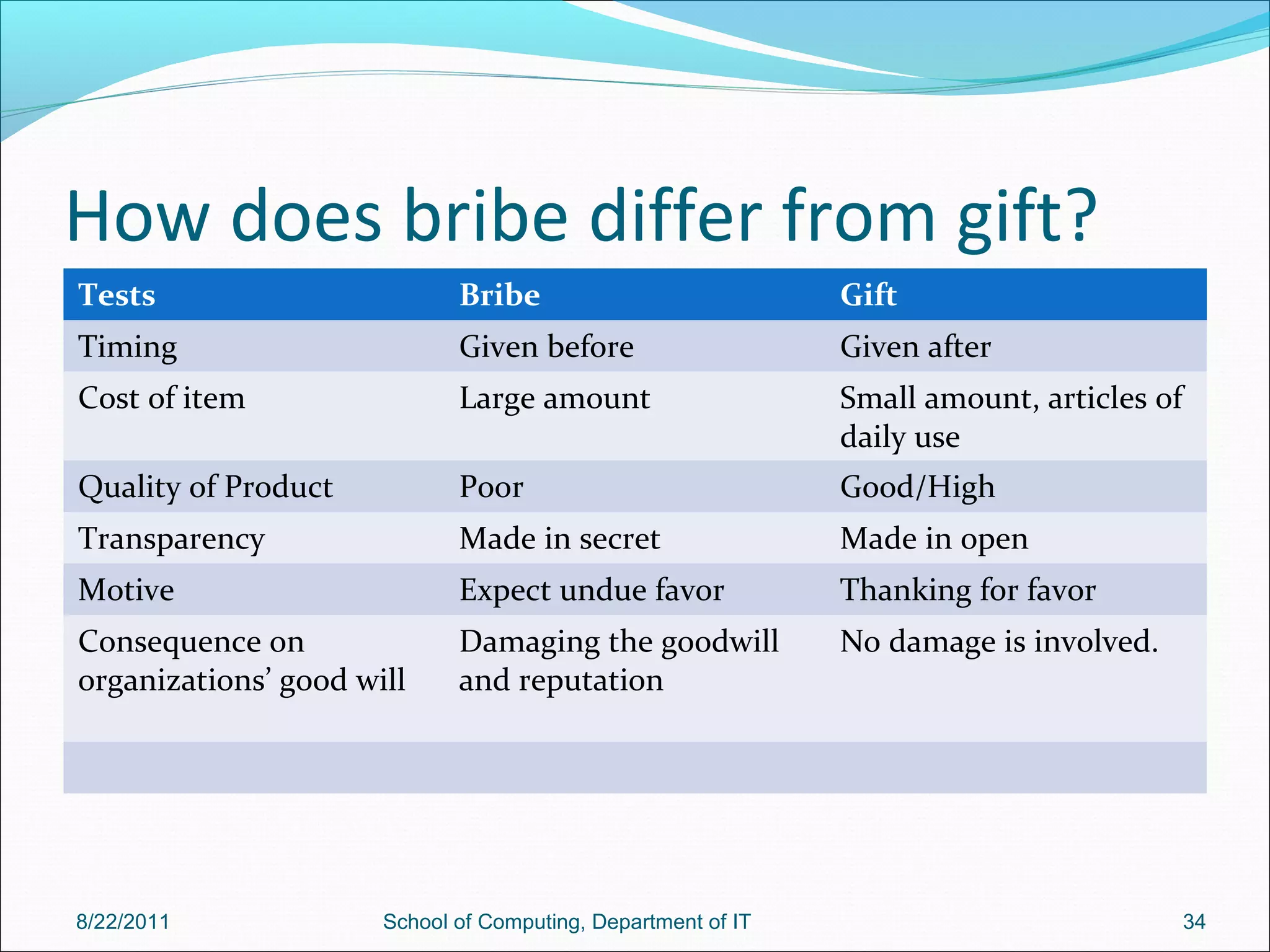
The document discusses various ethical responsibilities and issues faced by professionals, particularly engineers, including collegiality, loyalty, authority, confidentiality, and conflicts of interest. It emphasizes that engineers have a paramount obligation to public safety and welfare, which supersedes loyalty to employers in case of conflict. Additionally, it discusses the implications of collective bargaining, occupational crime, and the moral rights of engineers within their professional roles.