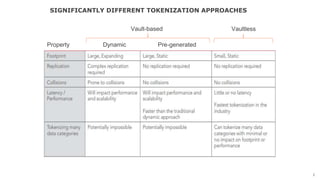
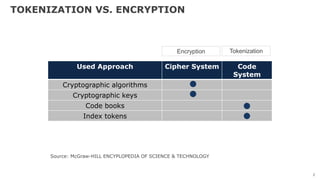
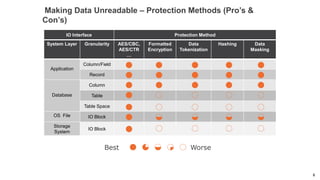
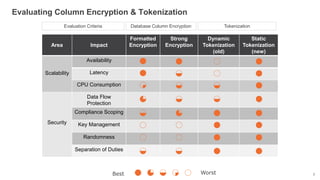
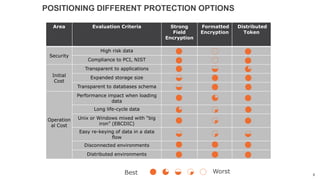
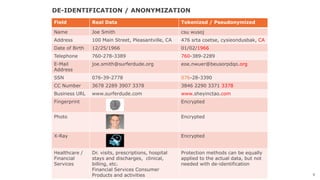
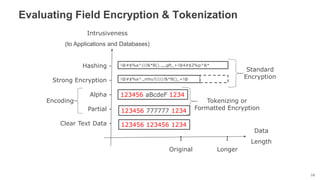
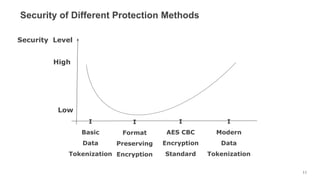
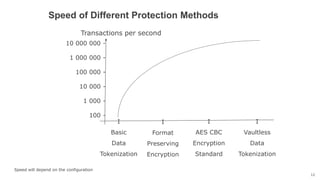
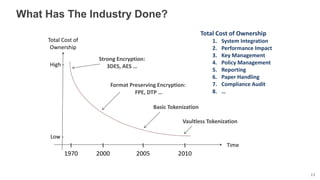
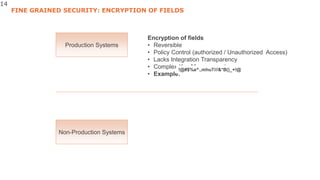
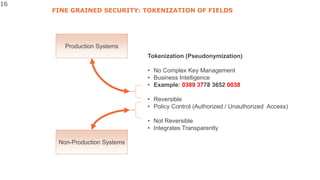
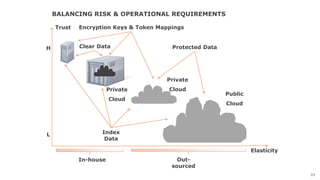
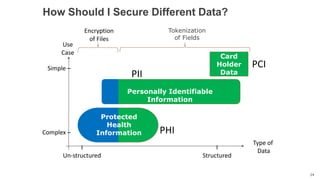
The document discusses various data protection methods including tokenization, encryption, and their implementation in compliance with security standards like PCI DSS and NIST. It evaluates different approaches based on criteria such as performance, security, and total cost of ownership, while emphasizing the need for adaptable protection methods as security requirements evolve. The document also highlights the importance of integrating these security measures in both production and non-production environments for maintaining data confidentiality and integrity.