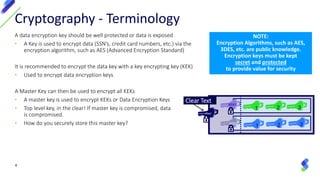
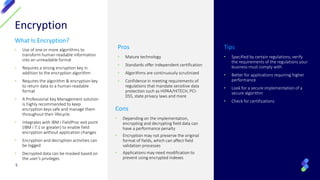
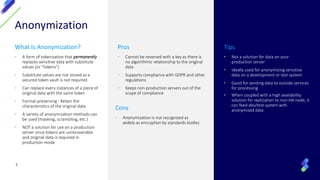
The document outlines methods for protecting sensitive data through encryption, tokenization, and anonymization, emphasizing the importance of preventing data breaches and maintaining customer trust. It discusses the differences and advantages of each method, regulatory requirements for data protection, and best practices for implementation, including the need for secure key management. Finally, it highlights how Syncsort offers various services and tools to assist organizations in ensuring their data security and compliance.