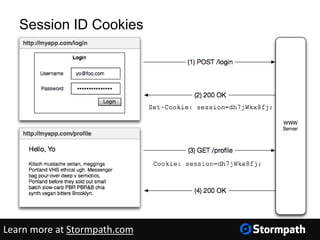
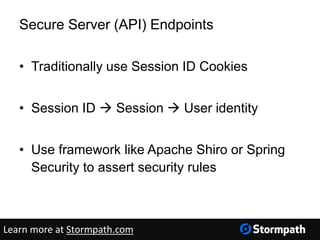
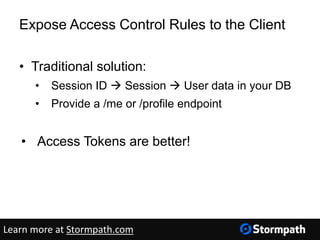
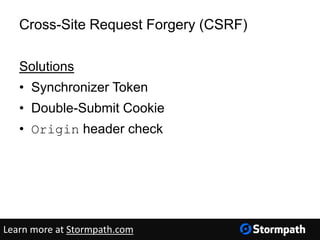
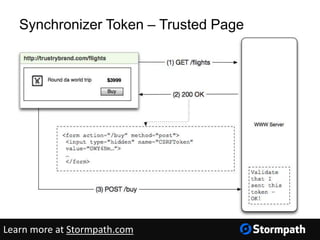
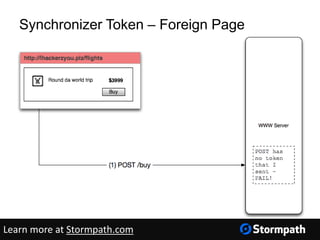
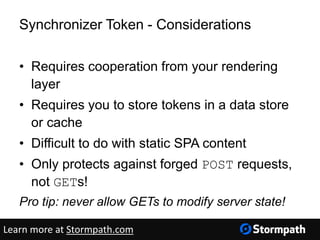
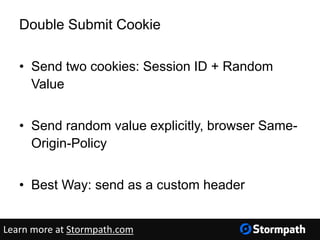
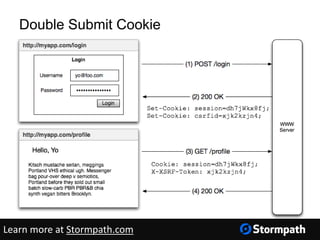
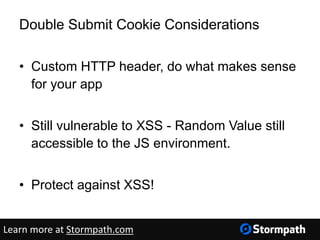
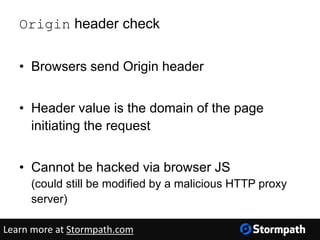
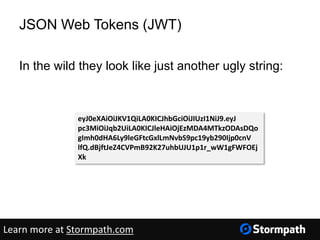
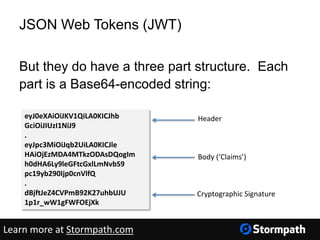
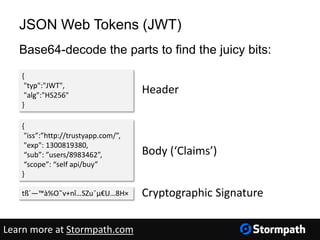
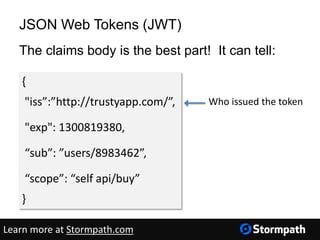
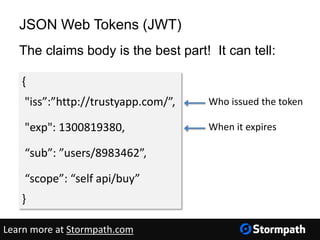
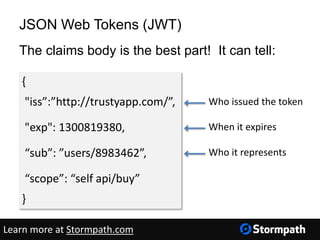
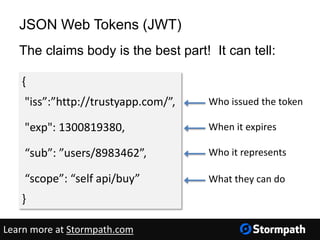
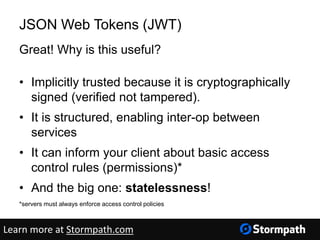
The document discusses securing web applications through token authentication, emphasizing its advantages over traditional session ID-based methods. It outlines various security concerns, such as cross-site scripting (XSS) and cross-site request forgery (CSRF), and presents JSON Web Tokens (JWT) as a reliable authentication mechanism. The document also provides practical implementation details and resources for developers utilizing token authentication in their applications.


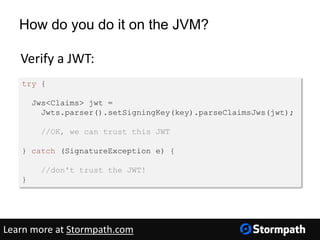
![How do you do it on the JVM?
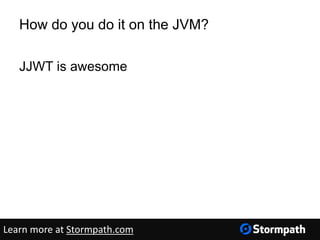
import io.jsonwebtoken.Jwts;
import io.jsonwebtoken.SignatureAlgorithm;
byte[] key = getSignatureKey();
String jwt =
Jwts.builder().setIssuer(“http://trustyapp.com/”)
.setSubject(“users/1300819380”)
.setExpiration(expirationDate)
.put(“scope”, “self api/buy”)
.signWith(SignatureAlgorithm.HS256,key)
.compact();
Create a JWT:
Learn more at Stormpath.com](https://image.slidesharecdn.com/tokenauthentication-150721011243-lva1-app6892/85/Token-Authentication-for-Java-Applications-48-320.jpg)