Tiet48 cac truong hop dong dang cua tam giac vuong
•Download as PPT, PDF•
0 likes•410 views
Report
Share
Report
Share
Recommended
Scacchi: tattiche di base.

Il documento si rivolge a chi già conosce le regole degli scacchi e i movimenti dei pezzi e si propone di esporre alcune tattiche di base che si possono applicare ai vari pezzi durante una partita.
Recommended
Scacchi: tattiche di base.

Il documento si rivolge a chi già conosce le regole degli scacchi e i movimenti dei pezzi e si propone di esporre alcune tattiche di base che si possono applicare ai vari pezzi durante una partita.
Improving System Security and User Privacy in Secure Electronic Transaction (...

With the advancement of internets, user’s transaction is at ease, timely manner and effective wise through online payment method, so also cybercriminals become increasingly more prompt in areas like e-commerce sites, financial institutions, payment processes and other online transactions. Therefore the need for the system security and privacy became the central issues for the acceptance of online payment methods in particular and growth of the Internet market in general. Using SET as an open encryption and security specification designed to protect credit card transaction on the internet. This paper proposes a new approach for increasing security by avoiding privacy violation using Public Key Infrastructure, X.509 certificate and Format Preservation encryption method, the credit card number is encrypted using public key algorithm and re-encrypted using Format preservation Encryption algorithm and finally stored in the X.509 version 3 certificate private extensions. This technique can be used to improve the security of the user credit card information against card fraud or the compromise of data associated with the account.
Energy Storage Management in Grid Connected Solar Photovoltaic System

The penetration of renewable sources in the power system network in the power system has been increasing in the recent years. One of the solutions being proposed to improve the reliability and performance of these systems is to integrate energy storage device into the power system network. This paper discusses the modeling of photo voltaic and status of the storage device such as lead acid battery for better energy management in the system. The energy management for the grid connected system was performed by the dynamic switching process.
Evento PIM - Novità QGis 2.8: database e mappe online / webgis

GIS open source per la pianificazione territoriale
More Related Content
Viewers also liked
Improving System Security and User Privacy in Secure Electronic Transaction (...

With the advancement of internets, user’s transaction is at ease, timely manner and effective wise through online payment method, so also cybercriminals become increasingly more prompt in areas like e-commerce sites, financial institutions, payment processes and other online transactions. Therefore the need for the system security and privacy became the central issues for the acceptance of online payment methods in particular and growth of the Internet market in general. Using SET as an open encryption and security specification designed to protect credit card transaction on the internet. This paper proposes a new approach for increasing security by avoiding privacy violation using Public Key Infrastructure, X.509 certificate and Format Preservation encryption method, the credit card number is encrypted using public key algorithm and re-encrypted using Format preservation Encryption algorithm and finally stored in the X.509 version 3 certificate private extensions. This technique can be used to improve the security of the user credit card information against card fraud or the compromise of data associated with the account.
Energy Storage Management in Grid Connected Solar Photovoltaic System

The penetration of renewable sources in the power system network in the power system has been increasing in the recent years. One of the solutions being proposed to improve the reliability and performance of these systems is to integrate energy storage device into the power system network. This paper discusses the modeling of photo voltaic and status of the storage device such as lead acid battery for better energy management in the system. The energy management for the grid connected system was performed by the dynamic switching process.
Evento PIM - Novità QGis 2.8: database e mappe online / webgis

GIS open source per la pianificazione territoriale
Viewers also liked (13)
Improving System Security and User Privacy in Secure Electronic Transaction (...

Improving System Security and User Privacy in Secure Electronic Transaction (...
Energy Storage Management in Grid Connected Solar Photovoltaic System

Energy Storage Management in Grid Connected Solar Photovoltaic System
Evento PIM - Novità QGis 2.8: database e mappe online / webgis

Evento PIM - Novità QGis 2.8: database e mappe online / webgis
Similar to Tiet48 cac truong hop dong dang cua tam giac vuong
200 bài toán nâng cao ôn tập lớp 2 | iHoc.me - Tài liệu toán tiểu học

200 bài toán nâng cao ôn tập lớp 2 file word sẽ giúp các thầy cô và các em học sinh luyện tập các bài toán nâng cao dễ dàng hơn.
Tải về máy tài liệu 200 bai toan nang cao on tap lop 2 tại địa chỉ:
http://ihoc.me/200-bai-toan-nang-cao-lop-2/
Similar to Tiet48 cac truong hop dong dang cua tam giac vuong (20)
285 cau trac nghiem dao dong dieu hoa cllx co dap an1.2724

285 cau trac nghiem dao dong dieu hoa cllx co dap an1.2724
200 bài toán nâng cao ôn tập lớp 2 | iHoc.me - Tài liệu toán tiểu học

200 bài toán nâng cao ôn tập lớp 2 | iHoc.me - Tài liệu toán tiểu học
More from Hoa Phượng
More from Hoa Phượng (20)
Tiet 2 bai 1- hoc hat- bai tieng chuong va ngon co. bai doc them- am nhac o...

Tiet 2 bai 1- hoc hat- bai tieng chuong va ngon co. bai doc them- am nhac o...
Bai 10 luc ke phep do luc trong luong va khoi luong

Bai 10 luc ke phep do luc trong luong va khoi luong
Tiet48 cac truong hop dong dang cua tam giac vuong
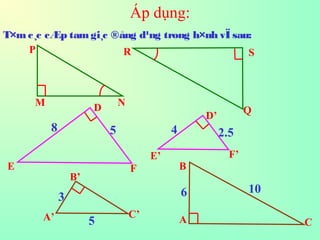
- 1. Áp dụng: T×m c¸c cÆp tamgi¸c ®ång d¹ng trong h×nh vÏ sau: A B C B’ A’ C’ E’ F’ D’ D FE N Q SR M P 8 5 4 2.5 3 5 6 10
- 2. Áp dụng: T×m c¸c cÆp tamgi¸c ®ång d¹ng trong h×nh vÏ sau: A B C B’ A’ C’ E’ F’ D’ D FE N Q SR M P 8 5 4 2.5 3 5 6 10
- 3. TiÕt 48: C¸c trêng hîp ®ång d¹ng cña tamgi¸c vu«ng
- 4. Hai tamgi¸c vu«ng ®ång d¹ng víi nhauHai tamgi¸c vu«ng ®ång d¹ng víi nhau nÕu tho¶ m·n :nÕu tho¶ m·n : a)Tamgi¸c vu«ng nµy cã mét gãc nhän b»ng gãc nhän cña tamgi¸c vu«ng kia. b) Tamgi¸c vu«ng nµy cã hai c¹nhgãc vu«ngtû lÖ víi haic¹nhgãc vu«ng cña tamgi¸c vu«ng kia.
- 5. A CB A’ B’ C’M N Tamgi¸c A’B’C’ vµ tamgi¸c ABC cã: ' '''' ;90ˆ'ˆ 0 BC CB AB BA AA === )(''''' '''' cgvchCBAAMNCBMN BC CB BC MN AB BA BC MN AB AM −∆=∆⇒=⇒ ==⇒= Suy ra: ABC A’B’C’. Trªn tia AB®Æt AM=A’B’ qua MvÏ ®êng th¼ng MN//BC . Ta cã AMN ABC nªn: C¸ch 2
- 6. Bµi 1: Cho ABC A’B’C’ (k=3/5) . BiÕt AHvµ A’H’ lµ hai ®êng cao cña tamgi¸c ABC vµ tamgi¸c A’B’C’. BiÕt AH=6. TÝnh A’H’. A B C A’ B’ C’ H H’ ⇒ ABH A’B’H’(g.g) 5 3 '''' ==⇒ BA AB HA AH 10'' 5 3 '' 6 =⇒= HA HA
- 7. A B CD 6 9 4 Bµi 2: a) T×m cÆp tamgi¸c ®ång d¹ng cã trong h×nh vÏ sau. b) TÝnh tû sè diÖn tÝch cña hai tam gi¸c ABDvµ tam gi¸c BDC.
- 8. Bµi 3: a)T×mc¸c tamgi¸c ®ång d¹ng cã trong h×nh vÏ sau: 2 A BC H M N 6 b)NÕu diÖn tÝch tam gi¸c CMN b»ng 24 th× diÖn tÝch tamgi¸c ABC lµ bao nhiªu? 2 cm
- 9. §Þnh lý 1: NÕu c¹nh huyÒn vµ mét c¹nh gãc vu«ng cña tam gi¸c vu«ng nµy tû lÖ víi c¹nh huyÒn vµ mét c¹nh gãc vu«ng cña tam gi¸c vu«ng kia th× hai tam gi¸c vu«ng ®ã ®ång d¹ng. §Þnh lý 2: Tû sè hai ®êng cao t¬ng øng cña hai tam gi¸c ®ång d¹ng b»ng tû sè ®ång d¹ng. §Þnh lý 3: Tû sè diÖn tÝch cña hai tam gi¸c ®ång d¹ng b»ng b×nh ph¬ng tû sè ®ång d¹ng.
- 10. Híng dÉn vÒ nhµ - Häc thuéc c¸c trêng hîp ®ång d¹ng cña tam gi¸c vu«ng. - Häc thuéc 2 ®Þnh lý vÒ tû sè ®êng cao vµ tû sè diÖn tÝch cña hai tam gi¸c ®ång d¹ng. - Lµm c¸c bµi tËp 46, 47, 48, 49 (SGK).