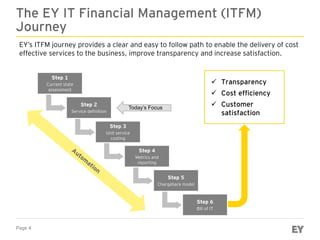
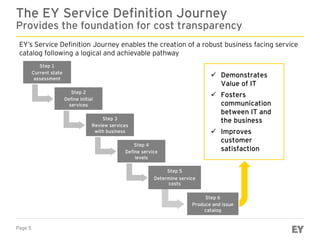
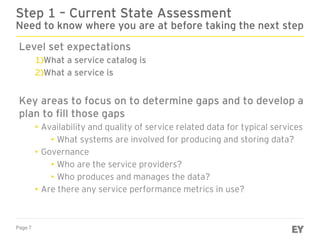
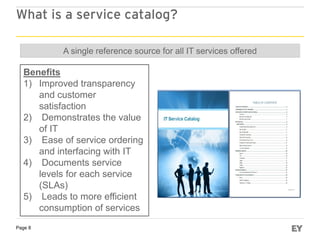
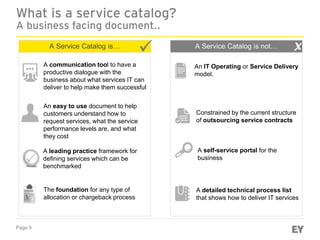
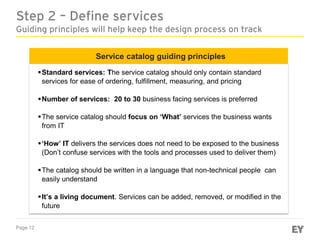
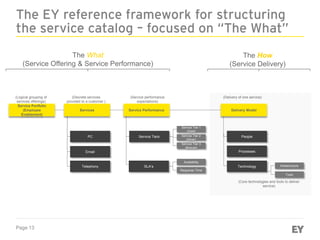
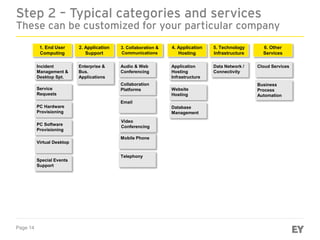
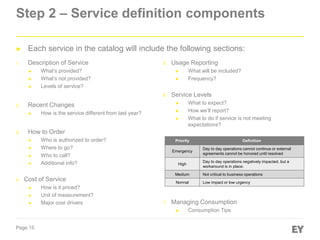
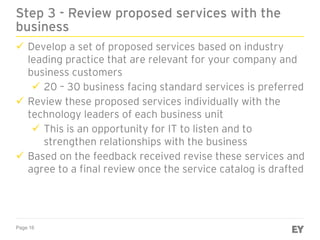
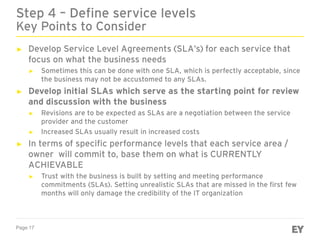
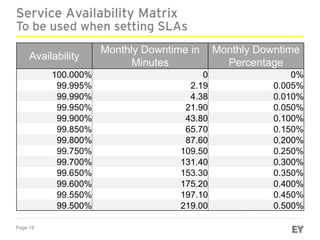
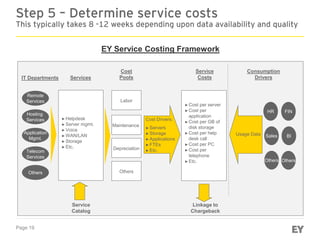
The document discusses the EY IT Financial Management (ITFM) service definition journey. The journey provides a framework to define IT services in a way that is transparent to business customers. It involves 6 steps: 1) assessing the current state, 2) defining initial services, 3) reviewing services with business stakeholders, 4) defining service levels, 5) determining service costs, and 6) producing and issuing a service catalog. The service catalog establishes a common language for communication between IT and business leaders and improves customer satisfaction. It forms the foundation for cost transparency and a potential chargeback model.