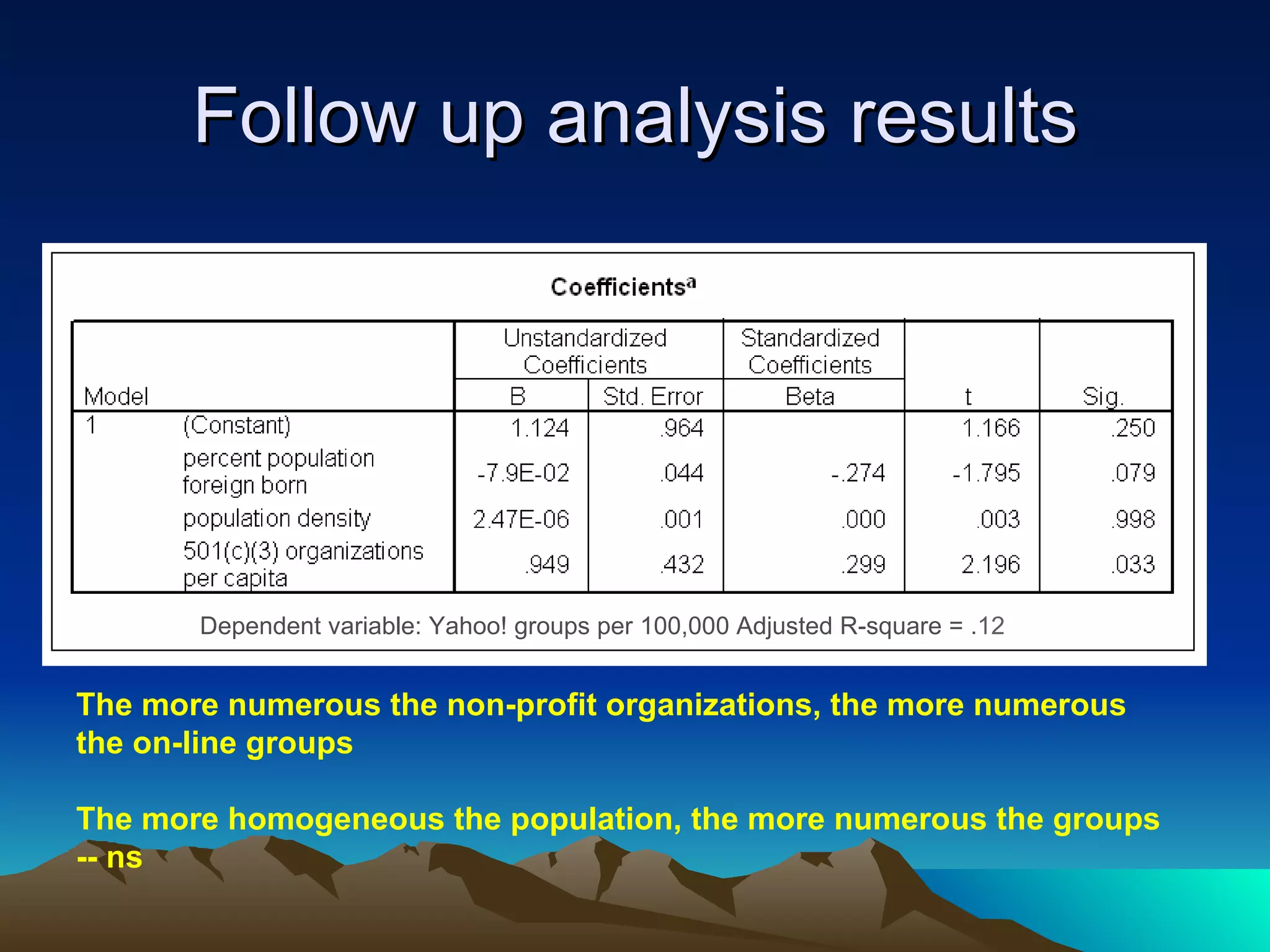
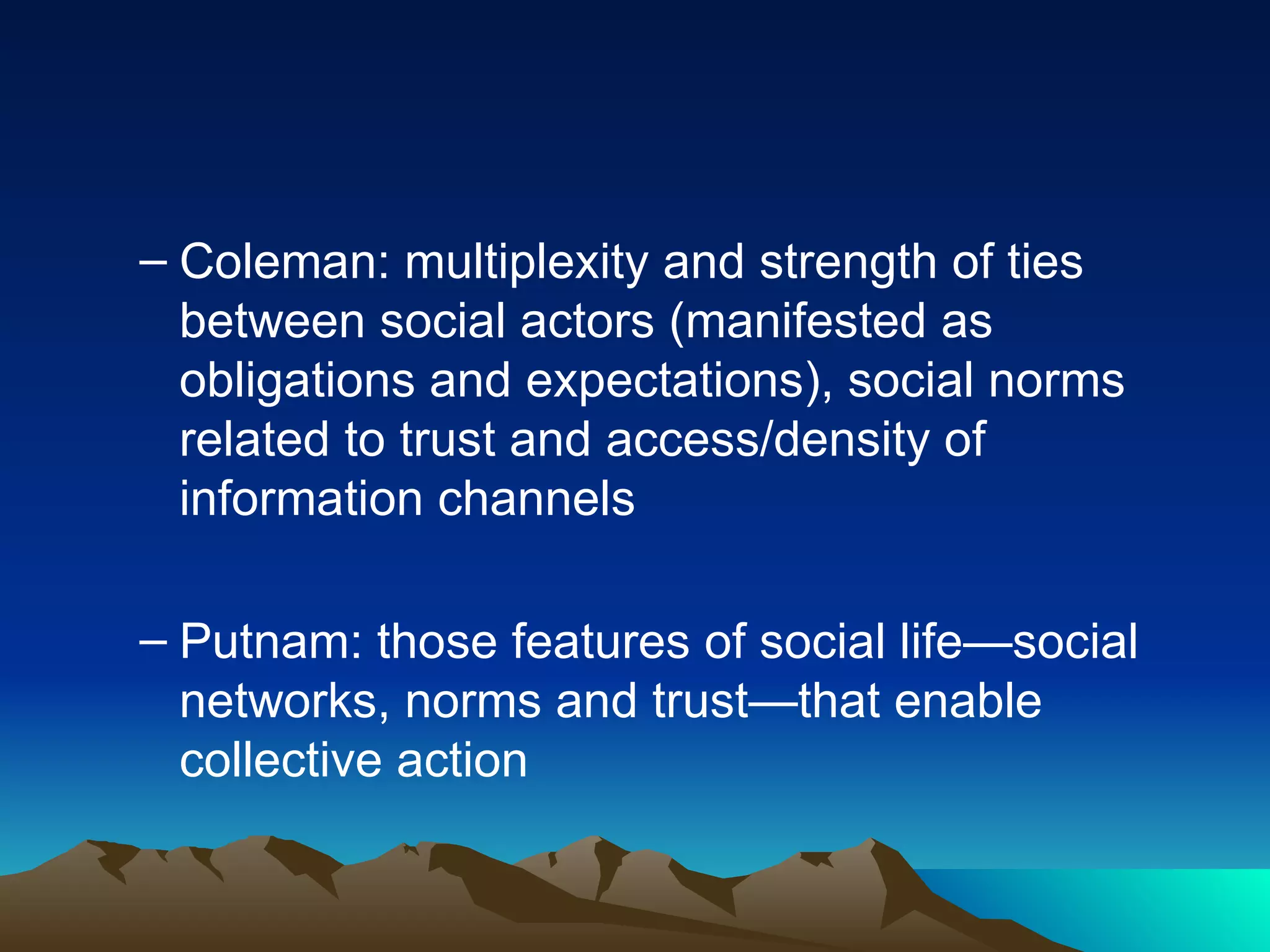
The document discusses how social capital theory can help explain the social effects of the Internet. It argues that individuals and communities with higher levels of social capital, as measured by factors like generalized reciprocity and social ties, will be more socially active online as well as offline. Empirical evidence from studies in Los Angeles and of U.S. states supports this, finding those with more offline social connections and belonging were more likely to make online friends or participate in online groups. The document calls for more research examining social capital and online activity over time and across different communities.