- Internet penetration has grown to over half of the world's population by 2018, with global internet speeds continuing to rise.
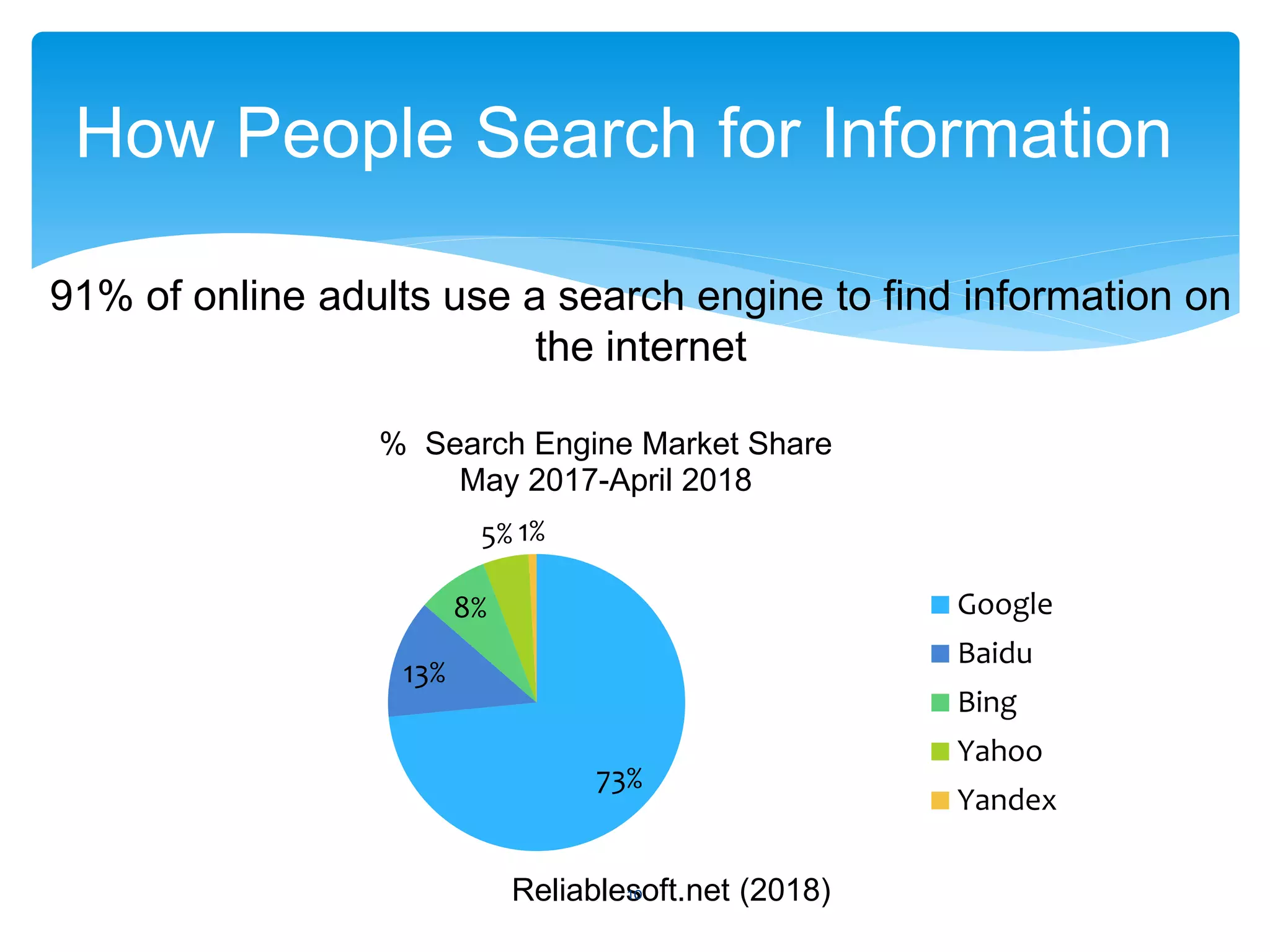
- Google is the dominant search engine, and consumers use it for transactional, informational, or navigational queries.
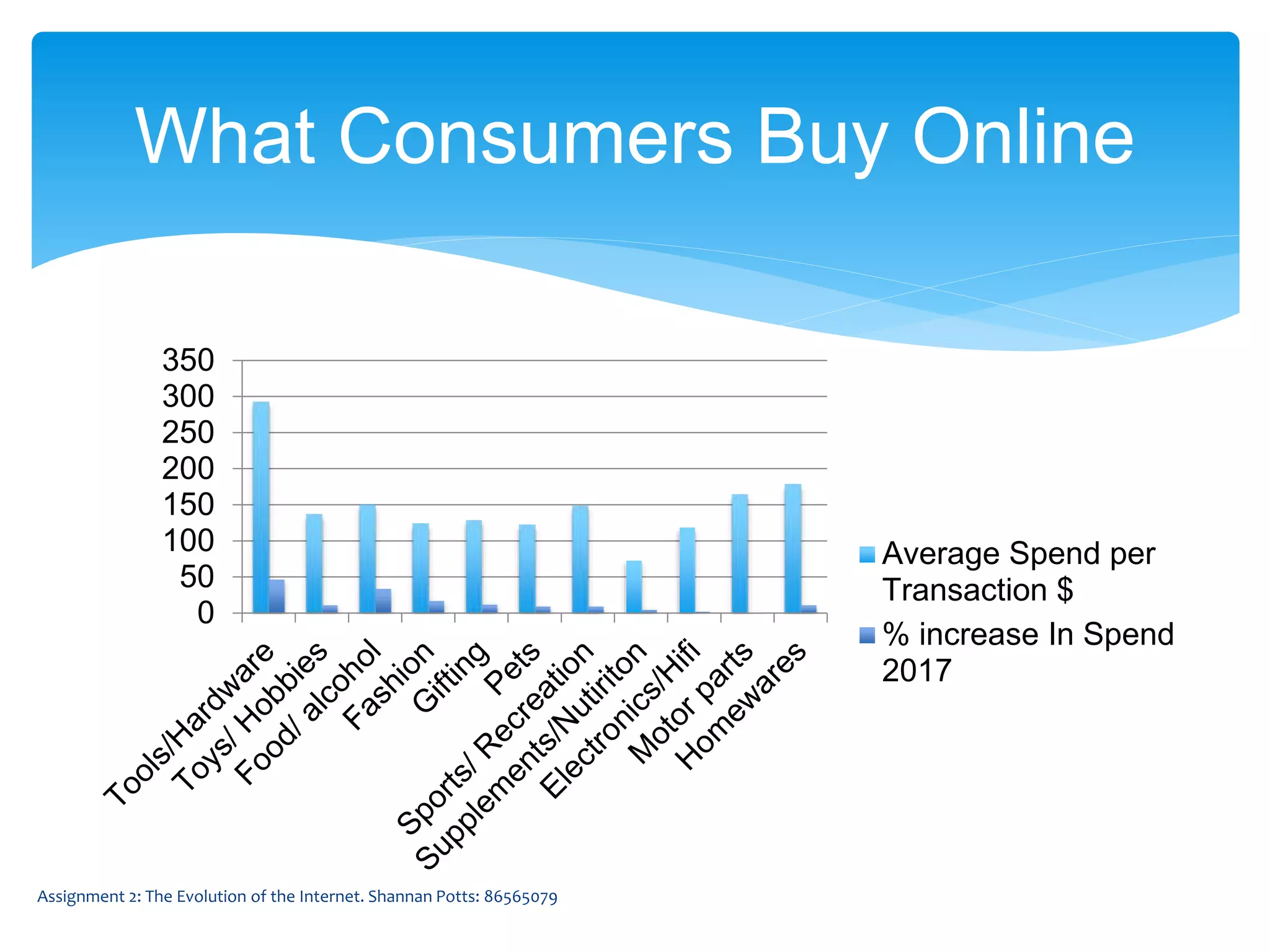
- In Australia, online spending is highest for tools/hardware and fashion sees the most yearly increase.
- The number of hours individuals spend watching online video has increased in recent years, with smartphones a common viewing device.