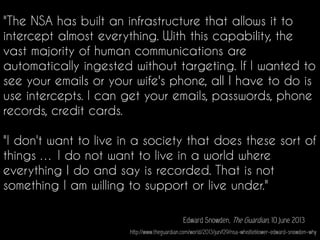
The document discusses Edward Snowden's views on mass surveillance by the NSA. It quotes Snowden as saying that the NSA has built an infrastructure that allows it to intercept almost all communications and that the vast majority of human communications are automatically ingested without targeting. Snowden expresses his unwillingness to live in a society where everything he does and says is recorded.



![“[W]hen we engage in democratic
argument, the point of the activity is
critically to reflect on our preferences,
to question them, to challenge them,
to enlarge them, to improve them.”
- Michael Sandel
Source: http://www.bbc.co.uk/programmes/b00lb6bt](https://image.slidesharecdn.com/thedigitaldivideinthepost-snowdenera-160106213349/85/The-digital-divide-in-the-post-Snowden-era-13-320.jpg)






![“It seems like the media was just
led around by the nose by law
enforcement. [They are] taking
advantage of a crisis where
encryption hasn’t proven to have
a role. It’s leading us in a less safe
direction at a time when the world
needs systems that are more
secure.”
Fung, B. (2015). If government surveillance expands after Paris, the media will be partly to blame. The Washington Post.
Retrieved from: washingtonpost.com/news/the-switch/wp/2015/11/19/if-government-surveillance-expands-after-paris-
the-press-will-be-partly-to-blame/
Paris | Flickr - Photo Sharing! : taken from - https://www.flickr.com/photos/gwpfae/13326359683
Author: MacPepper https://creativecommons.org/licenses/by-nc-sa/2.0/](https://image.slidesharecdn.com/thedigitaldivideinthepost-snowdenera-160106213349/85/The-digital-divide-in-the-post-Snowden-era-38-320.jpg)





![Good morning:) | Flickr - Photo Sharing! : taken from - https://www.flickr.com/photos/124374841@N05/21263365286/
Author: Amber inhim https://creativecommons.org/licenses/by-nc-sa/2.0/
[Source: http://www.theguardian.com/technology/2015/nov/24/google-can-
unlock-android-devices-remotely-if-phone-unencrypted]](https://image.slidesharecdn.com/thedigitaldivideinthepost-snowdenera-160106213349/85/The-digital-divide-in-the-post-Snowden-era-63-320.jpg)