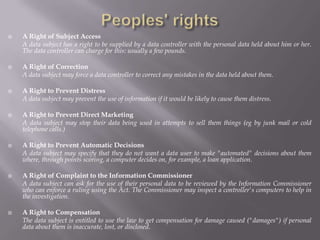
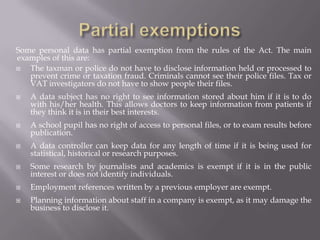
The Data Protection Act 1998 establishes rules for how personal data can be collected and used. It requires organizations that store personal data to register with the Information Commissioner and only collect data for specified purposes. The Act gives data subjects rights to access and correct their data and restricts processing and transfer of sensitive personal data. It establishes eight principles for data controllers around security, relevance, accuracy, and lawful processing and transfer of personal data. Some personal data processing is exempt from the Act for reasons such as national security or medical research.