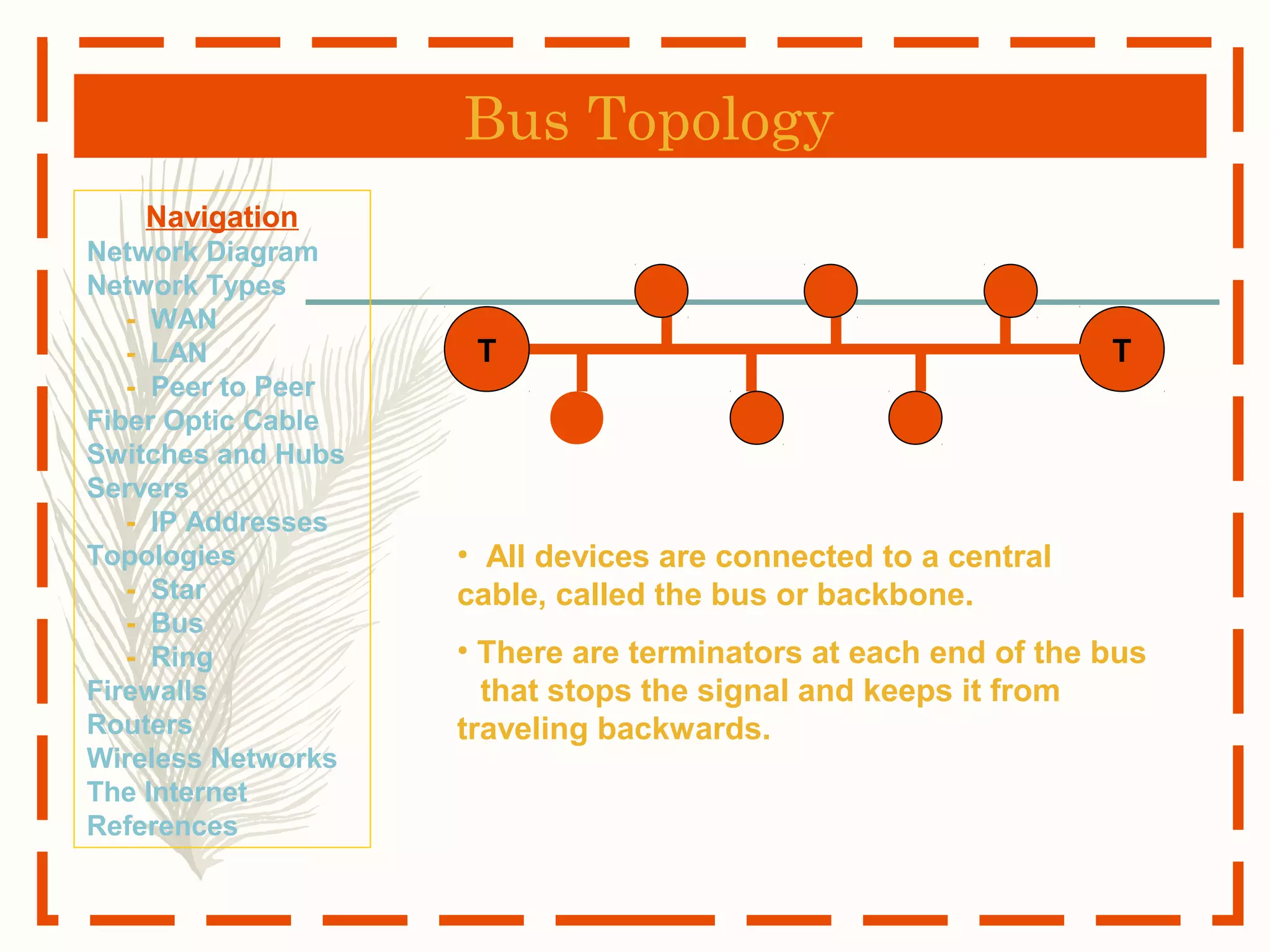
The document provides an overview of basic computer networking concepts, defining a computer network and describing different types of networks including WAN, LAN, and peer-to-peer. It also explains key components of networks such as switches, routers, servers, and topologies including star, bus and ring configurations. The document aims to introduce readers to fundamental networking topics in a clear and straightforward manner.

![The Computer Network
What is a Computer Network
net·work: [net-wurk] – noun, a system containing any
combination of computers, computer terminals, printers,
audio or visual display devices, or telephones
interconnected by telecommunication equipment or
cables: used to transmit or receive information.](https://image.slidesharecdn.com/thebasicsofcomputernetworking-171209234340/75/The-basics-of-computer-networking-3-2048.jpg)