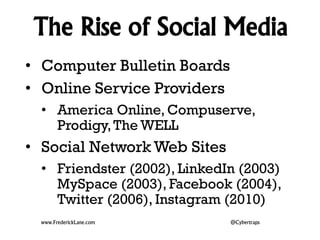
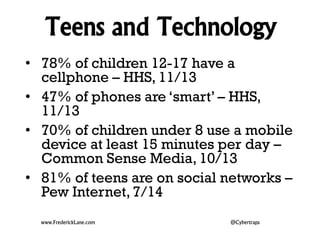
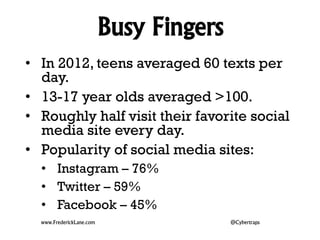
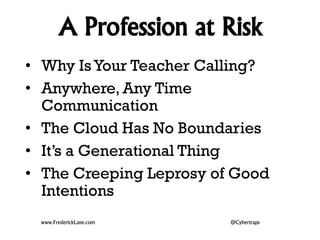
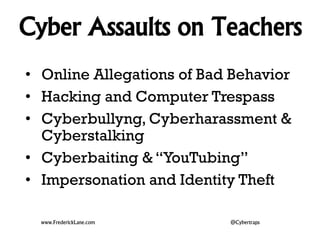
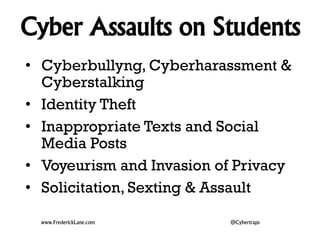
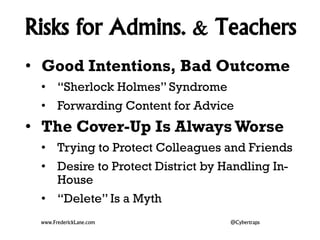
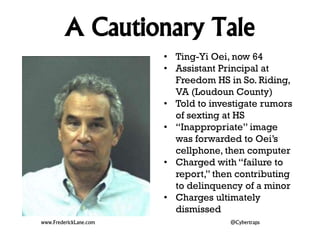
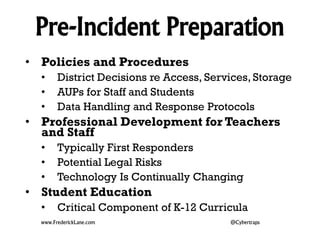
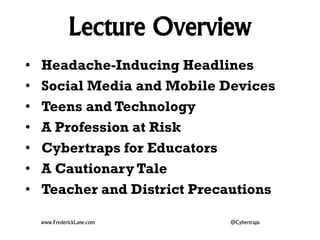
The document discusses the impact of technology on education, focusing on the risks associated with social media and mobile devices for both teenagers and educators. It highlights alarming incidents of inappropriate behavior between teachers and students facilitated by technology, while also emphasizing the need for proactive measures and policies to mitigate these risks. Key recommendations include educating both educators and students about cyber ethics and implementing clear district policies.
![Headache-Inducing Headlines
• 10/19/14 – Teacher is accused of using Kik to send
naked photos of herself to three students and
having sex with one of them in her classroom [LA]
• 9/24/14 -- Student who had affair with teacher
reveals how his life was ruined after she seduced
him on Facebook [TX]
• 9/24/14 -- Married teacher, 38, whose wife is
pregnant with their fourth child ‘took 15-year-old
student's virginity after luring her over Twitter’ [PA]
• 9/15/14 -- HIV-positive teacher uses Grindr to hook
up with 15-year-old [TX]
• 9/4/14 -- Teacher Admits He Sent Dick Pic
Snapchats to Underage Students [WI]
www.FrederickLane.com @Cybertraps](https://image.slidesharecdn.com/2014-11-06textingtweetingteensandteachers-141106133108-conversion-gate01/85/Texting-Tweeting-Teens-and-Teachers-4-320.jpg)