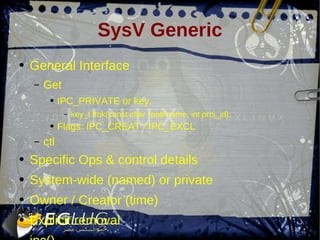
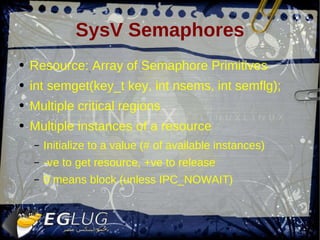
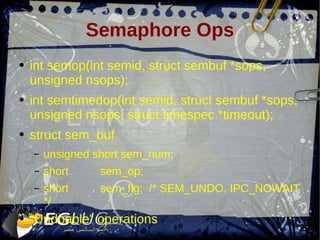
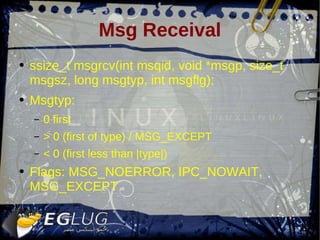
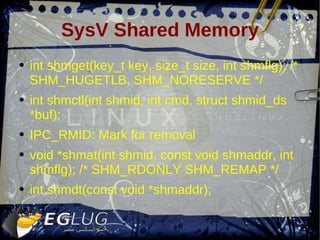
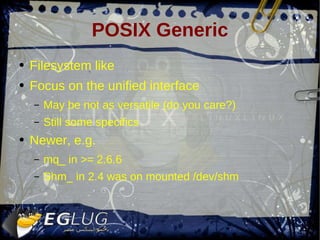
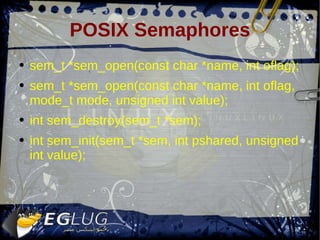
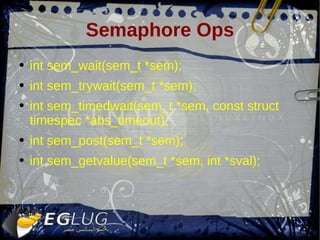
The document discusses various inter-process communication (IPC) mechanisms for Linux system programming, including pipes, FIFOs, System V IPC mechanisms like semaphores, messages and shared memory, and POSIX IPC analogs. It provides details on how to implement and use these different IPC primitives, as well as code examples for shared memory allocation and synchronization using POSIX semaphores.
![Pipes Characteristics: Single reader – single writer (uni-diriectional) File descriptors (unnamed) POSIX and Linux restrictions Pipefs SIGPIPE: No readers PAGE_SIZE max (blocking write!!) int pipe(int pipefd[2]); int dup2(int oldfd, int newfd);](https://image.slidesharecdn.com/session13-090315114107-phpapp02/85/Sysprog-13-4-320.jpg)
![struct job *jp; struct nodelist *lp; int pipelen; int prevfd; int pip[2]; prevfd = -1; for (lp = n->npipe.cmdlist; lp; lp = lp->next) { ... pip[1] = -1; if (lp->next) { if (pipe(pip) < 0) { ... } } if (forkshell(jp, lp->n, n->npipe.pipe_backgnd) == 0) { ... if (pip[1] >= 0) { close(pip[0]); } if (prevfd > 0) { dup2(prevfd, 0); close(prevfd); } if (pip[1] > 1) { dup2(pip[1], 1); close(pip[1]); } /* Execute */ /* never returns */ } if (prevfd >= 0) close(prevfd); prevfd = pip[0]; close(pip[1]); }](https://image.slidesharecdn.com/session13-090315114107-phpapp02/85/Sysprog-13-5-320.jpg)

![SysV Messages int msgget(key_t key, int msgflg); int msgctl(int msqid, int cmd, struct msqid_ds *buf); IPC_RMID, IPC_SET int msgsnd(int msqid, const void msgp, size_t msgsz, int msgflg); struct msgbuf { long mtype; /* > 0 */ char mtext[1]; }](https://image.slidesharecdn.com/session13-090315114107-phpapp02/85/Sysprog-13-11-320.jpg)

![POSIX shm example int pa_shm_create_rw(pa_shm *m, size_t size, int shared, mode_t mode) { char fn[32]; int fd = -1; struct shm_marker *marker; pa_random(&m->id, sizeof(m->id)); segment_name(fn, sizeof(fn), m->id); if ((fd = shm_open(fn, O_RDWR|O_CREAT|O_EXCL, mode & 0444)) < 0) { ... } m->size = size + PA_ALIGN(sizeof(struct shm_marker)); if (ftruncate(fd, m->size) < 0) { ... } if ((m->ptr = mmap(NULL, m->size, PROT_READ|PROT_WRITE, MAP_SHARED, fd, 0)) == MAP_FAILED) { ... } marker = (struct shm_marker*) ((uint8_t*) m->ptr + m->size - PA_ALIGN(sizeof(struct shm_marker))); pa_atomic_store(&marker->pid, (int) getpid()); pa_atomic_store(&marker->marker, SHM_MARKER); ... m->do_unlink = 1; } void pa_shm_free(pa_shm *m) { ... if (munmap(m->ptr, m->size) < 0) pa_log("munmap() failed: %s", pa_cstrerror(errno)); if (m->do_unlink) { char fn[32]; segment_name(fn, sizeof(fn), m->id); if (shm_unlink(fn) < 0) pa_log(" shm_unlink(%s) failed: %s", fn, pa_cstrerror(errno)); } ... memset(m, 0, sizeof(*m)); } struct shm_marker { pa_atomic_t marker; /* 0xbeefcafe */ pa_atomic_t pid; void *_reserverd1; void *_reserverd2; void *_reserverd3; void *_reserverd4; }; static char *segment_name(char *fn, size_t l, unsigned id) { pa_snprintf(fn, l, "/pulse-shm-%u", id); return fn; }](https://image.slidesharecdn.com/session13-090315114107-phpapp02/85/Sysprog-13-22-320.jpg)
