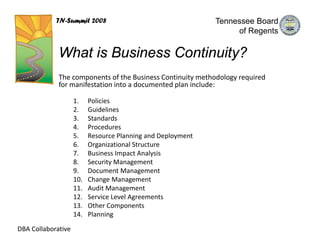
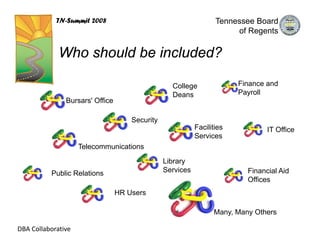
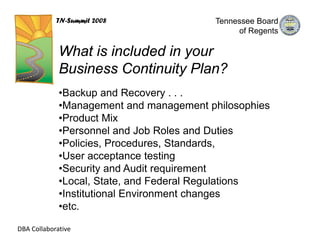
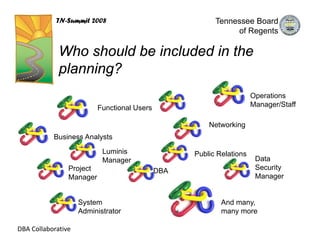
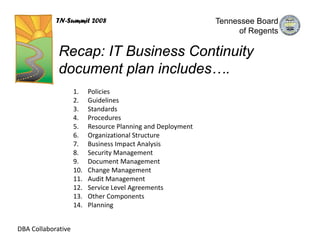
The document discusses business continuity planning and how it differs from disaster recovery. Business continuity involves maintaining critical business functions through daily activities and ensuring recoverability, while disaster recovery is a subset that deals with functions after a disaster. An effective business continuity plan considers factors like policies, procedures, staffing changes, regulatory changes, and technology changes to ensure normal business operations. Both IT and business units need continuity plans that address issues beyond backup and recovery.