Stop flirting with disaster! Prepare your business for unforeseen disasters.
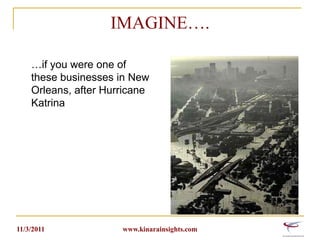
- 1. IMAGINE…. …if you were one of these businesses in New Orleans, after Hurricane Katrina 11/3/2011 www.kinarainsights.com
- 2. Even closer to home… Springfield MA June 1, 2011 tornado 11/3/2011 www.kinarainsights.com
- 3. STOP FLIRTING WITH DISASTER! BE PREPARED. Sameer Sule Business Technology Consultant KINARA | INSIGHTS
- 4. Objectives Understand the importance of having a disaster recovery plan for a business as relates to its computer systems, applications and data. Reduce Business Downtime-Technologies currently available to SMBs 11/3/2011 www.kinarainsights.com
- 5. 2011: Year of Disasters in Massachusetts October 29th Snowstorm: More than 600,000 people without power. Outage likely to last a few days. Springfield Tornado : June 1, 2011 Hurricane Irene: > 500,000 people lost power. Some for as long as a week. Earthquake January blizzard Millions in damages and lost business 11/3/2011 www.kinarainsights.com
- 6. October 29th Snow Storm According to National Grid: 671,594 customers or 28 percent of the state’s 2.4 million electric customers lost power By late Oct 31st, 459,809 customers were still without power Harvard :100 percent were without power Wrentham: 93 percent in the dark Foxboro:91 percent powerless Andover: 74 percent unplugged 11/3/2011 www.kinarainsights.com
- 7. Eye Opener “A Company that experiences a computer outage lasting more than 10 days will never fully recover financially. 50 percent will be out of business within five years.” 70 percent of small firms that experience a major data loss go out of business within a year. Companies that aren’t able to resume operations within ten days (of a disaster hit) are not likely to survive. Of those businesses that experience a disaster and have no emergency plan, 43 percent never reopen; of those that do reopen, only 29 percent are still operating two years later. SCORE: Counselors to America’s Small Businesses 11/3/2011 www.kinarainsights.com
- 8. More Eye Openers 15-40% businesses fail following a natural or man-made disaster* 35% SMBs have a comprehensive disaster recovery plan** 94% small business owners believe a disaster could seriously disrupt their business within the next two years*** 51% Americans have experienced at least one emergency situation involving lost utilities for at least 3 days, evacuation from their home or office, loss of communications with family members or had to provide first aid to others**** *Insurance Information Institute, **Gartner, ***American Red Cross and FedEx Small Business Survey, 2007, ****American Red Cross/Harris Poll Survey, 2009. 11/3/2011 www.kinarainsights.com
- 9. Most common business disruptive events Power outage Internet outage Server crash Viruses, hacks and breaches Location based issues like building evacuation due to fire, hazardous spill, burst pipes, theft etc 11/3/2011 www.kinarainsights.com
- 10. What is the actual cost in $$$$$$ to your business if you were down for a day? 11/3/2011 www.kinarainsights.com
- 11. Median cost of downtime Small business: $3000 per day Medium size business: $23,000 per day Symantec 2011 SMB Disaster Preparedness Survey - Global: January 2011 11/3/2011 www.kinarainsights.com
- 12. Real cost of business downtime Loss in labor Loss in revenue Loss in service All are cascade effects. Total loss total is larger than you think. 11/3/2011 www.kinarainsights.com
- 13. SMB Data on Disaster Preparedness Despite warnings, most SMBs are still not prepared for disaster 50% don’t have a BDR plan in place 41% never thought about putting a plan in place Symantec 2011 SMB Disaster Preparedness Survey - Global: January 2011 11/3/2011 www.kinarainsights.com
- 14. SMB Data on Disaster Preparedness SMBs are at risk - 40% said disaster recovery is not a priority - <50% of SMBs back up their data weekly or more frequently - 23% back up data daily Symantec 2011 SMB Disaster Preparedness Survey - Global: January 2011 11/3/2011 www.kinarainsights.com
- 15. SMB Data on Disaster Preparedness SMBs do not act until it is too late - 50% of SMBs that implemented a BDR plan did so after experiencing an outage and/or data loss - 28% actually tested their recovery plan Symantec 2011 SMB Disaster Preparedness Survey - Global: January 2011 11/3/2011 www.kinarainsights.com
- 16. Business Continuity Planning Describes the processes and procedures an organization puts in place to ensure that essential functions can continue during and after a disaster. Seeks to prevent interruption of mission-critical services, and to re-establish full functioning as swiftly and smoothly as possible. 11/3/2011 www.kinarainsights.com
- 17. Disaster Recovery Planning The processes, policies and procedures related to preparing for recovery or continuation of technology infrastructure critical to an organization after a disruptive event Subset of business continuity that focuses on the IT or technology systems that support business functions. 11/3/2011 www.kinarainsights.com
- 18. Assess your business risk What types of emergencies have you experienced in in the past? What could result from a process or system failure? What threats does your business location have? Will you be affected if your neighbor is hit by a disaster? 11/3/2011 www.kinarainsights.com
- 19. BDR: Common SMB Mistakes Lack of: A formal written BDR plan Offsite data protection Policy on data retention Testing of restores/DR plan on a regular basis Ensuring critical data protection Focus on recovery Designated accountable BDR person 11/3/2011 www.kinarainsights.com
- 20. Backup and Disaster Recovery (BDR) Planning Backup Backup with no recovery planning is pointless Disaster Recovery Recovery without backup is impossible 11/3/2011 www.kinarainsights.com
- 21. Backup What should be backed up? What type of backup? What is the backup frequency? 11/3/2011 www.kinarainsights.com
- 22. Backup Build multiple layers of backup for greater reliability and faster restores Local RAID based backup, off-site tapes, or cloud based storage Technology deployed should meet your data backup and recovery needs 11/3/2011 www.kinarainsights.com
- 23. Backup: Points to consider How long can your business run without critical data available to your employees, clients, partners etc? What data is extremely important in order to get back up and running after an unforeseen disruptive event? What type of backup solution (local/ offsite cloud based) do you need to address your needs? What level of data backup (files, whole image) do you need and what is the backup frequency? Which desktops/laptops/mobile devices need to be backed up? 11/3/2011 www.kinarainsights.com
- 24. Disaster Recovery No Plan= No recovery Disaster Recovery without proper planning is a recipe for disaster 11/3/2011 www.kinarainsights.com
- 25. Recovery Planning During the recovery process, what is the order in which systems, applications and data will be brought back on line? How are your employees going to access the applications and data in the event that the regular work location cannot be accessed? 11/3/2011 www.kinarainsights.com
- 26. RTO and RPO RTO (Recovery Time Objective) The maximum tolerable duration of time that a computer system, network or application can be down after a failure or the length of time it takes to restore the system. RPO Disaster occurrence R T O time RPO (Recovery Point Objective) Is the age of files or state of data that must be recovered from backup storage for normal operations to resume if a computer system, network or application goes down. The RPO is expressed backward in time (that is, into the past) from the instant at which the failure occurs, 11/3/2011 www.kinarainsights.com
- 27. Cloud Based BDR Systems Automatic backup Secure and offsite Easy to access and restore Faster recovery Reduced downtime Competitive pricing 11/3/2011 www.kinarainsights.com
- 28. Virtualization and Reduced Downtime Backup image of physical server to the cloud Can launch a virtual machine in the cloud Allows technicians to fix the physical server while regular business is run from the virtual server Allows server migrations to be carried out in the cloud Test upgrades/patches in cloud before production deployment 11/3/2011 www.kinarainsights.com
- 29. BDR Solutions Turnkey solutions: for a monthly fee providing everything from power, technology, mobile offices and connectivity Software providers: cloud based BDR solutions, each with its own value proposition 11/3/2011 www.kinarainsights.com
- 30. What to expect from your BDR vendor Experience with required federal and state compliance and regulatory requirements for your industry Strong encryption methods RTOs and RPOs planning with skilled engineers Redundancy of data over 2 geographically dispersed data centers 11/3/2011 www.kinarainsights.com
- 31. What to expect..continued Designated point of contact (engineer) who knows your BDR plan and can monitor and respond immediately to any emergencies Vendor technology should be scalable and flexible to your company needs Service and support References 11/3/2011 www.kinarainsights.com
- 32. Prevention is always better than cure Be Proactive Use Remote Monitoring and Management (RMM) services to ensure that your server and workstations are running properly, updated, backed up daily, and protected from viruses with latest definitions Keep inventory of all your IT systems up-to-date Keep system passwords and contact info of important personnel readily available in case of emergency 11/3/2011 www.kinarainsights.com
- 33. BDR Plan: Bare minimum Designate a BDR person/team Details of your computing environment: description of what you own, its location, date purchased, warranty information, number of licenses Contact info for your hardware and software vendors User names and Passwords for critical systems Different channels of communication: phone, email, text, social media 11/3/2011 www.kinarainsights.com
- 34. Real World Examples River Valley Community Federal CU: Camden, Arkansas During initial test of recovery plan, they collected all critical info, such as technical information for server configuration, data recovery steps, setup information, etc. Found that simple phone numbers for key contacts at data backup locations were missing Updated their printed plan and online repository of key contact data Small Business Administration 11/3/2011 www.kinarainsights.com
- 35. Real World Examples A Desaur & Co. ( accounting company) was using a tape-based solution when the server failure occurred in April 2007. The tape restore failed entirely because its IT support company had not carried out trial data restores, which would have revealed that the backups were not working. After an expensive and time costly hard disk data restore, only 80% of the data was able to be restored. Permanently lost valuable data. Now employ a cloud based backup and recovery software, which also backs up laptops when connected to the network and can immediately begin remotely restoring all of the data to the systems if the server fails. 11/3/2011 www.kinarainsights.com
- 36. Real World Examples 400‐Person Call Center: Nashville, Tennessee Building located in floodplain, extensive planning was made to help alleviate risk Took steps to elevate IT equipment storage, establish redundant facilities, and institute a fail-safe phone system. During 2010 Nashville floods, entire facility was lost Chose to recover locally in mobile offices rather than lay off or transfer employees 11/3/2011 www.kinarainsights.com
- 37. BDR PLAN IT IMPLEMENT IT TEST IT REGULARLY DON’T LEAVE YOUR BUSINESS TO CHANCE!! 11/3/2011 www.kinarainsights.com
- 38. THANK YOU CONTACT Sameer Sule Healthcare Technology Consultant Author: “Protecting Electronic Health Information: A Practical Approach to Patient Data Security in Your Healthcare Practice” Amazon: http://www.amazon.com/author/sameersule Blog: http://www.kinarainsights.com/blog.html Linkedin: http://www.linkedin.com/pub/sameer-sule/7/b1b/511 Twitter:@sameersule 10/1/2013 www.kinarainsights.com 40
