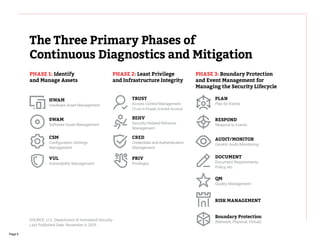
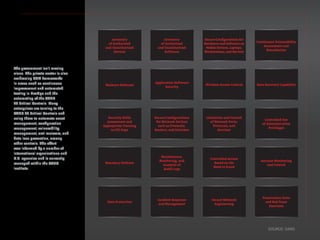
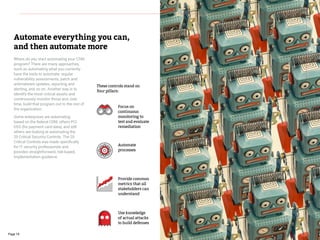
The document discusses the need for continuous security monitoring in modern IT environments. It argues that traditional, periodic security assessments are no longer sufficient given how quickly technology and threats are evolving. Continuous security monitoring allows organizations to adapt security as quickly as their infrastructure and applications change. The document recommends starting with established frameworks like NIST SP 800-137 or the SANS 20 critical security controls and implementing tools and processes for asset management, configuration management, vulnerability management, access control, and incident response. This represents a shift from compliance-driven security to an automated, ongoing approach.