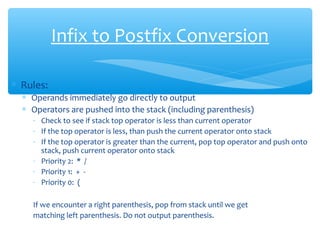
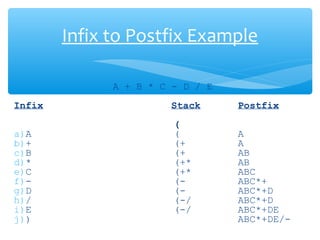
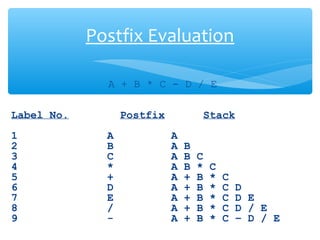
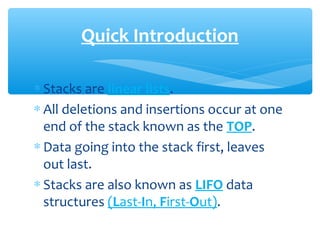
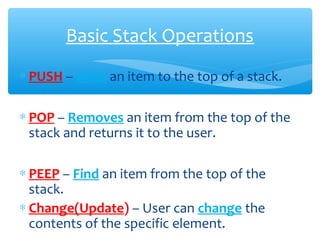
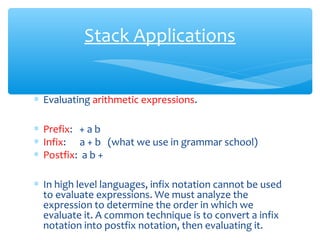
The document provides a comprehensive overview of stack data structures, including their last-in, first-out (LIFO) behavior and basic operations such as push, pop, peep, and change. It discusses applications of stacks in reversing data, converting decimal to binary, and evaluating arithmetic expressions through infix to postfix conversion. The document also includes pseudocode for implementing stack operations and examples demonstrating their use.



![PUSH Algorithm
PUSH(S, Top, x)
Step 1: [Check For Stack Overflow]
if Top >= N
then write("Stack Overflow")
Exit
Step 2: [Increment Top pointer By
Value One]
Top Top +1
Step 3: [Perform Insertion]
s[Top] X
Step 4: [Finished]
Exit
N
Top 0](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-8-320.jpg)
![PUSH Algorithm
PUSH(S, Top, x)
Step 1: [Check For Stack Overflow]
if Top >= N
then write("Stack Overflow")
Exit
Step 2: [Increment Top pointer By
Value One]
Top Top +1
Step 3: [Perform Insertion]
s[Top] X
Step 4: [Finished]
Exit
N
Top A](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-9-320.jpg)
![PUSH Algorithm
PUSH(S, Top, x)
Step 1: [Check For Stack Overflow]
if Top >= N
then write("Stack Overflow")
Exit
Step 2: [Increment Top pointer By
Value One]
Top Top +1
Step 3: [Perform Insertion]
s[Top] X
Step 4: [Finished]
Exit
N
Top
A
B](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-10-320.jpg)
![PUSH Algorithm
PUSH(S, Top, x)
Step 1: [Check For Stack Overflow]
if Top >= N
then write("Stack Overflow")
Exit
Step 2: [Increment Top pointer By
Value One]
Top Top +1
Step 3: [Perform Insertion]
s[Top] X
Step 4: [Finished]
Exit
N
A
B
Top C](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-11-320.jpg)
![PUSH Algorithm
PUSH(S, Top, x)
Step 1: [Check For Stack Overflow]
if Top >= N
then write("Stack Overflow")
Exit
Step 2: [Increment Top pointer By
Value One]
Top Top +1
Step 3: [Perform Insertion]
s[Top] X
Step 4: [Finished]
Exit
N
Top
A
B
C
D](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-12-320.jpg)
![PUSH Algorithm
PUSH(S, Top, x)
Step 1: [Check For Stack Overflow]
if Top >= N
then write("Stack Overflow")
Exit
Step 2: [Increment Top pointer By
Value One]
Top Top +1
Step 3: [Perform Insertion]
s[Top] X
Step 4: [Finished]
Exit
N
Top
A
B
C
D
Stack Overflow](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-13-320.jpg)
![POP Algorithm
N
Top
A
B
C
D
POP(S , Top)
Step 1: [Check For Stack Underflow Or
Check Whether Stack Is Empty]
if (Top = 0) OR (Top = -1)
then write("Stack Underflow")
Exit
Step 2: [Decrement Top pointer /
Remove The Top Information]
Value S[Top]
Top Top - 1
Step 3: [Return From Top Element Of The
Stack]
Write(value)
Step 4: [Finished]
Exit](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-15-320.jpg)
![POP Algorithm
N
A
B
C
POP(S , Top)
Step 1: [Check For Stack Underflow Or
Check Whether Stack Is Empty]
if (Top = 0) OR (Top = -1)
then write("Stack Underflow")
Exit
Step 2: [Decrement Top pointer /
Remove The Top Information]
Value S[Top]
Top Top - 1
Step 3: [Return From Top Element Of The
Stack]
Write(value)
Step 4: [Finished]
Exit
Top ](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-16-320.jpg)
![POP Algorithm
N
A
B
POP(S , Top)
Step 1: [Check For Stack Underflow Or
Check Whether Stack Is Empty]
if (Top = 0) OR (Top = -1)
then write("Stack Underflow")
Exit
Step 2: [Decrement Top pointer /
Remove The Top Information]
Value S[Top]
Top Top - 1
Step 3: [Return From Top Element Of The
Stack]
Write(value)
Step 4: [Finished]
Exit
Top ](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-17-320.jpg)
![POP Algorithm
N
A
POP(S , Top)
Step 1: [Check For Stack Underflow Or
Check Whether Stack Is Empty]
if (Top = 0) OR (Top = -1)
then write("Stack Underflow")
Exit
Step 2: [Decrement Top pointer /
Remove The Top Information]
Value S[Top]
Top Top - 1
Step 3: [Return From Top Element Of The
Stack]
Write(value)
Step 4: [Finished]
Exit
Top ](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-18-320.jpg)
![POP Algorithm
N
POP(S , Top)
Step 1: [Check For Stack Underflow Or
Check Whether Stack Is Empty]
if (Top = 0) OR (Top = -1)
then write("Stack Underflow")
Exit
Step 2: [Decrement Top pointer /
Remove The Top Information]
Value S[Top]
Top Top - 1
Step 3: [Return From Top Element Of The
Stack]
Write(value)
Step 4: [Finished]
ExitTop 0](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-19-320.jpg)
![POP Algorithm
N
POP(S , Top)
Step 1: [Check For Stack Underflow Or
Check Whether Stack Is Empty]
if (Top = 0) OR (Top = -1)
then write("Stack Underflow")
Exit
Step 2: [Decrement Top pointer /
Remove The Top Information]
Value S[Top]
Top Top - 1
Step 3: [Return From Top Element Of The
Stack]
Write(value)
Step 4: [Finished]
ExitTop 0
Stack Underflow](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-20-320.jpg)

![PEEP Algorithm
N
Top
A
B
C
D
PEEP(S, Top, i)
Step 1: [Check For Stack Underflow]
if (Top - i + 1) <= 0
then write("Stack Underflow")
Exit
Step 2: [Return The ith Element From
The Top Of The Stack]
X S(Top - i + 1)
Step 3: [Finished]
Exit
Top D](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-22-320.jpg)

![CHANGE Algorithm
N
Top
A
B
C
D
CHANGE(S, Top, X, i)
Step 1: [Check For Stack Underflow]
if (Top - i + 1) < 0
then write("Stack Underflow")
Exit
Step 2: [Change The Element Value
From The Top Of The Stack]
S(Top - i + 1) X
Step 3: [Finished]
Exit](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-24-320.jpg)
![CHANGE Algorithm
N
Top
A
B
C
D1
CHANGE(S, Top, X, i)
Step 1: [Check For Stack Underflow]
if (Top - i + 1) < 0
then write("Stack Underflow")
Exit
Step 2: [Change The Element Value
From The Top Of The Stack]
S(Top - i + 1) X
Step 3: [Finished]
Exit](https://image.slidesharecdn.com/divyeshstack-150708071225-lva1-app6892/85/Stack-Operation-In-Data-Structure-25-320.jpg)