Recommended
PPS
Records Creation And Maintenance
PPTX
Policy, formulation, implementation and evaluation
PPTX
5 major social institutions
PDF
Socio economic empowerment of rural women through icts
PDF
PDF
PDF
ഭൂതലവിശകലനം ഭൂപടങ്ങളിലൂടെ
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PPT
SS I CHAPTER 1 SELF EVALUATION EXAM X CLASS
PPT
X CLASS SSII CHAPTER 1 SELF EVALUATION
PDF
Social science english medium notes 2016
PPT
PDF
ഇന്ത്യ സാമ്പത്തിക ഭൂമിശാസ്ത്രം
PDF
ODP
PDF
PDF
PPT
PDF
PDF
PDF
PDF
Africa booprakrithi-rivers
PPTX
PDF
Kila training Material - മഹാത്മാ ഗാന്ധി ദേശീയ ഗ്രാമീണ തൊഴിലുറപ്പ് പദ്ധതി- MG...
More Related Content
PPS
Records Creation And Maintenance
PPTX
Policy, formulation, implementation and evaluation
PPTX
5 major social institutions
PDF
Socio economic empowerment of rural women through icts
PDF
PDF
PDF
ഭൂതലവിശകലനം ഭൂപടങ്ങളിലൂടെ
PDF
Viewers also liked
PDF
PDF
PDF
PDF
PDF
PDF
PPT
SS I CHAPTER 1 SELF EVALUATION EXAM X CLASS
PPT
X CLASS SSII CHAPTER 1 SELF EVALUATION
PDF
Social science english medium notes 2016
PPT
PDF
ഇന്ത്യ സാമ്പത്തിക ഭൂമിശാസ്ത്രം
PDF
ODP
PDF
PDF
PPT
PDF
PDF
PDF
PDF
Africa booprakrithi-rivers
Similar to ദേശീയ വരുമാനം
PPTX
PDF
Kila training Material - മഹാത്മാ ഗാന്ധി ദേശീയ ഗ്രാമീണ തൊഴിലുറപ്പ് പദ്ധതി- MG...
PDF
PDF
Kerala House to the house less - LIFE MISSION pHASE 3 - REHABILITATION OF TH...
PDF
E book - The Economics of Freedom (Malayalam Translation)
PDF
Old age pension Kerala Guidelines - James adhikaram doc
PDF
Natural Rubber and Irregularities
PDF
Jamabandhi Inspection- Guidelines
PPTX
Employment and labour topic for ldc.pptx
PDF
PDF
Kerala Government Daily wages rate 2019 uploaded by james Adhikaram kottayam
PDF
Haritha karma sena - Green army in kerala -Go20200812 26710. www.jamesadhikar...
PDF
Income tax notes 2018-19 uploaded by T james Joseph Adhikarthil kottayam
PDF
Sevana Jalakam - All you want to know from a panchayath office - James Joseph...
PDF
The Science of Money (In Malayalam)
More from iqbal muhammed
PDF
PDF
PDF
PDF
PDF
11 economic planning in india
PDF
PDF
9 from magatha to thaneswar
PDF
8 towards the gangetic plain(1)
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
PDF
2.ഭൂമിശാസ്ത്രത്തിലെ നൂതന സങ്കേതങ്ങള്
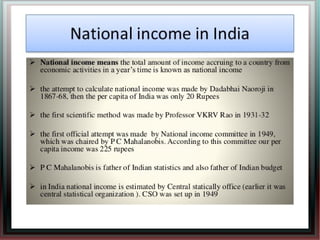
ദേശീയ വരുമാനം 1. 6. േദശീയ വരുമാനം
ഒരു രാജയം ഒരു വർഷം ഉലാദിപികുന
സാധനങളുേടയും േസവനങളുേടയും ആെക മൂലയം
പണതിൽ പതിപാദികുനതാണ് േദശീയ വരുമാനം
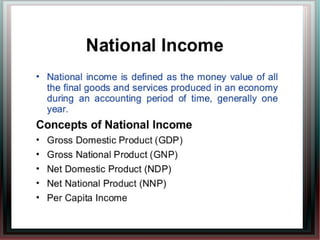
േദശീയ വരുമാനവുമായി ബനെപട ആശയങളാണ് അറേദശീയ
ഉലനം പതിശീർഷവരുമാനം എനിവ.
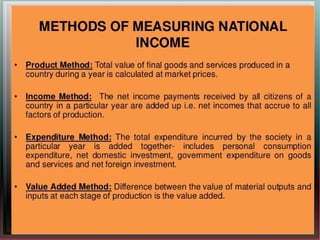
േദശീയ വരുമാനം കണകാകുനതിനുള 3 രീതികളാണ്
ഉലാദന രീതി വരുമാന രീതി െചലവു രീതി
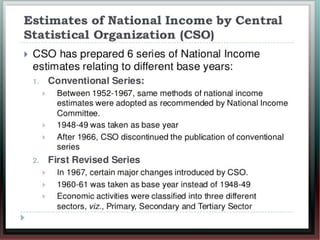
ഇനയയിൽ േകന സിതിവിവര സംഘടനയാണ് (CSO)
േദശീയ വരുമാനം കണകാകുകയും പസിദീകരികുകയും
െചയുനത്.
രാജയം ൈകവരിച സാമതികവളർച മനസിലാകുനതിനും
താരതമയം െചയുനതിനും േദശീയവരുമാന കണകുകൾ
സഹായികുനു.
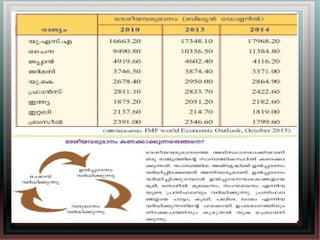
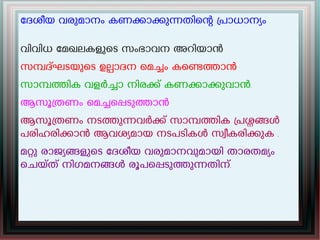
12. േദശീയ വരുമാനം കണകാകുനതിെന പാധാനയം
വിവിധ േമഖലകളുെട സംഭാവന അറിയാൻ
സമദഘടയുെട ഉലാദന െമചം കെണതാൻ
സാമതിക വളർചാ നിരക് കണകാകുവാൻ.
ആസൂതണം െമചെപടുതാൻ
ആസൂതണം നടതുനവർക് സാമതിക പശങൾ
പരിഹരികാൻ ആവശയമായ നടപടികൾ സവീകരികുക .
മറു രാജയങളുെട േദശീയ വരുമാനവുമായി താരതമയം
െചയത് നിഗമനങൾ രൂപെപടുതുനതിന്.
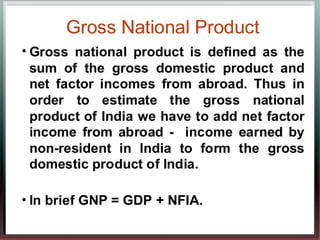
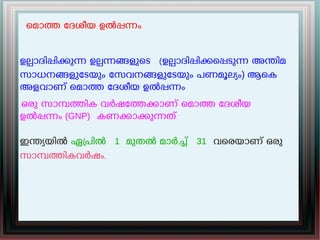
13. െമാത േദശീയ ഉൽപനം.
ഉലാദിപികുന ഉലനങളുെട (ഉലാദിപികെപടുന അനിമ
സാധനങളുേടയും േസവനങളുേടയും പണമൂലയം) ആെക
അളവാണ് െമാത േദശീയ ഉൽപനം
.ഒരു സാമതിക വർഷേതകാണ് െമാത േദശീയ
ഉൽപനം (GNP) കണകാകുനത്.
ഇനയയിൽ ഏപിൽ 1 മുതൽ മാർച് 31 വെരയാണ് ഒരു
സാമതികവർഷം.
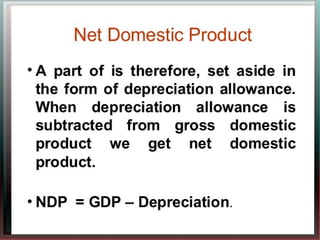
14. െമാത ആഭയനര ഉൽപനം
ഒരു സാമതിക വർഷതിൽ രാജയതിെന
ആഭയനര അതിർതികുളിൽ
ഉലാദിപികെപടുന സാധനങളുേടയും
േസവനങളുേടയും ആെക പണമൂലയമാണ്
െമാത ആഭയനര ഉൽപനം
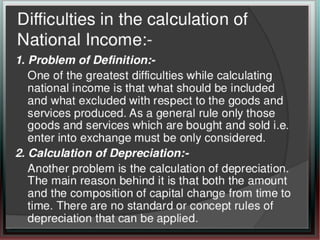
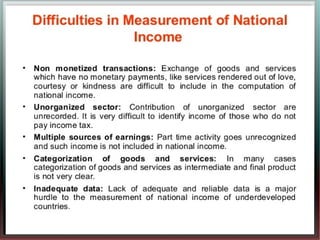
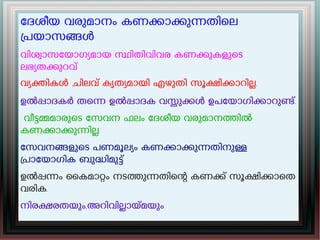
18. േദശീയ വരുമാനം കണകാകുനതിെല
പയാസങൾ
വിശവാസേയാഗയമായ സിതിവിവര കണകുകളുെട
ലഭയതകുറവ്
വയകികൾ ചിലവ് കൃതയമായി എഴുതി സൂകികാറില.
ഉൽപാദകർ തെന ഉൽപാദക വസുകൾ ഉപേയാഗികാറുണ്.
വീടമമാരുെട േസവന ഫലം േദശീയ വരുമാനതിൽ
കണകാകുനില.
േസവനങളുെട പണമൂലയം കണകാകുനതിനുള
പാേയാഗിക ബുദിമുട്
ഉൽപനം ൈകമാറം നടതുനതിെന കണക് സൂകികാെത
വരിക.
നിരകരതയും,അറിവിലായമയും
19.