This document provides an overview of software configuration management (SCM) using IBM Rational ClearCase and ClearQuest products. It discusses SCM strategies for version control, configuration management, process management, and problem tracking. The document also maps IBM Rational products to SCM areas and provides terminology for ClearCase and ClearQuest concepts. Overall, the document aims to help readers understand SCM and how to plan an SCM solution using ClearCase and ClearQuest.


































































































































































































![A natural divider is also how we assemble (build) the finished application. If we
can develop, build, test, and deliver a subsystem as one component, then that is
probably a good candidate for a project of its own. Refer to “Projects versus
streams” on page 178 for more insight.
UCM infrastructure
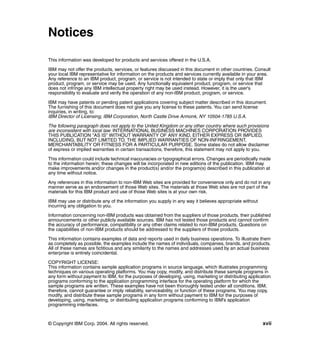
The complete ClearCase-ClearQuest UCM implementation might look like
Figure 10-19.
Notice that we include the MultiSite shipping servers, which will be discussed in
Part 5, “Implementing distributed UCM with MultiSite” on page 233.
database
server for CQ
(Windows/Unix) Unix
clients
Windows
CC + CQ
clients
CC + CQ internal firewall
CQ server(s)
(Windows/Unix)
exernal firewall
CQ web client
remote
client
CQ/MS
(email,
shipping
web for
server
CQ CQ)
[CC/MS (Windows)
administration
shipping
client
server]
(Windows)
(Unix) remote client
(UCM:
connected /
CC/MS server disconnected)
(Windows/Unix)
external
license CQ WEB server change
server mail request
(Windows/Solaris)
server submitter
(email or
CC WEB server web)
(Windows/Solaris)
Figure 10-19 UCM infrastructure
Notice that the site installation disk space provider for neither ClearCase nor
ClearQuest is shown in Figure 10-19.
Chapter 10. Implementing UCM 191](https://image.slidesharecdn.com/sg246399-120219010012-phpapp02/85/Sg246399-217-320.jpg)




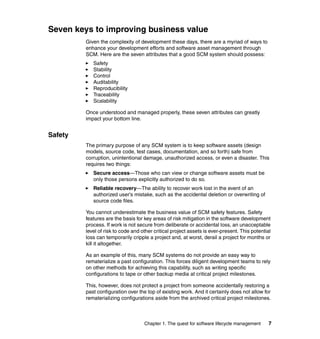
![Table 10-10 ClearCase installation
Screen Selection/Entry
Welcome to the Setup Wizard Click Next.
Deployment Method Select Desktop installation from CD
image.
Click Next.
Client/Server Select Install server and client software.
Click Next.
Welcome to the Setup Wizard Click Next.
Product Warnings Make sure you have closed all other
applications and stop virus protection.
Click Next.
License Agreement Select I accept, click Next.
Destination Folder Accept default, click Next.
Custom Setup Click Next.
Configure Rational ClearCase Select Service Account from left-hand
pane.
Service Account Field Selection/Entry
Account Domain None (Local Workstation)
Server Process clearcase_albd
Password <type in a password>
Confirm password <re-enter password>
ClearCase clearcase
Administration Group
Select Registry and Mail from left-hand
pane.
Message “Specifying no domain will mean Click Yes.
that you can only use ClearCase on this
one workstation [...]
Are you sure this is what you want to do?
Chapter 10. Implementing UCM 197](https://image.slidesharecdn.com/sg246399-120219010012-phpapp02/85/Sg246399-223-320.jpg)



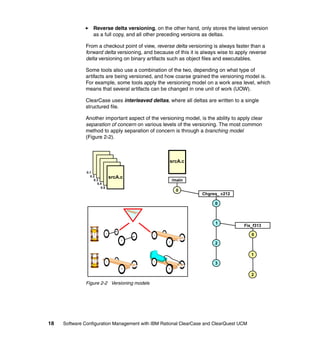
![Step 3—Create a UCM project
The next step is to create a UCM project.
As the ClearCase Administrator, or possibly the project lead, follow the steps in
Table 10-11 to create your first UCM project, gizmo_1.0.
Table 10-11 Creating a UCM project through Project Explorer
Step Description
Start ClearCase Project Start → Program Files → Rational Software → Rational
Explorer ClearCase → Project Explorer
Create a projects folder Select File → New → Folder and name the folder
Projects.
Create a UCM project Select the newly created Projects folder.
Select Projects → New → Project.
New Project—Step 1
Name the project gizmo_1.0
Click Next.
New Project—Step 2 Question Would you like to seed this project [...] ?
Select No.
Click Next.
Chapter 10. Implementing UCM 201](https://image.slidesharecdn.com/sg246399-120219010012-phpapp02/85/Sg246399-227-320.jpg)












































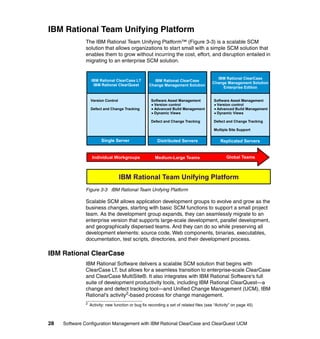
![Using MultiSite for disaster recovery
Consider the regional CM configuration defined in Figure 12-9. The circles
represent individual sites, the triangles represent project sets—defined programs
that may span multiple projects and multiple VOB/dbsets:
Sites share some project work with one or more sites, but there is also a good
bit of work that is local to the site.
In addition, site s4 is working on a number of programs with China and Japan.
Replication among sites is done every 15 to 30 minutes.
A
B
s1
A
B
s5 I
J
s2 C
D
C
D
C
D s3
s4 K
E
H
project
X sets [to asia]
Figure 12-9 Sample regional CM sites with some MultiSite
Chapter 12. Planning for distributed development using MultiSite 255](https://image.slidesharecdn.com/sg246399-120219010012-phpapp02/85/Sg246399-281-320.jpg)
![What happens if the database for project set C is lost at s2 due to a hardware
failure? The hardware is repaired and data is restored from backup (which may
be up to 24 hours old.)
Then a special MultiSite replication mode, called restorereplica, is invoked. The
restorereplica function queries the replica family for up-to-date information. Data
is recovered to its last replication. If data is replicated every 15 minutes, only 15
minutes of data is at risk for loss.
This is a great feature. What about project set K? It is not replicated, so the latest
backup is the best restore that occurred. It may be worth replicating it to another
site just to get the recover option that MultiSite provides.
Using a dedicated disaster recovery site (DR site)
Figure 12-10 shows an example of defining a site just for disaster recovery
purposes. All sites replicate to the DR site at whatever rate your recover
tolerance is set at. Every fifteen minutes is common; some sites replicate every
five minutes.
A ... J
Database
CQ A
VOB Shipping
Server Server B
Server
s1
DR Site
A
B
s5 I
J
s2 C
D
C
D
C
D s3
s4 K
E
H
project
X sets [to asia]
Figure 12-10 Establishing a regional disaster recovery site using MultiSite
256 Software Configuration Management with IBM Rational ClearCase and ClearQuest UCM](https://image.slidesharecdn.com/sg246399-120219010012-phpapp02/85/Sg246399-282-320.jpg)