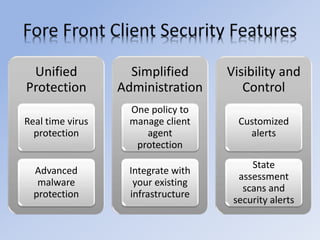
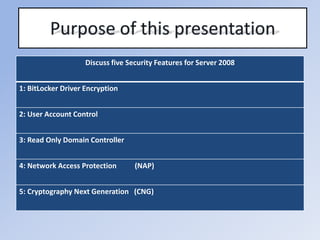
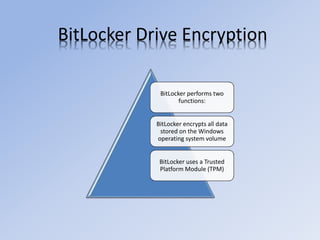
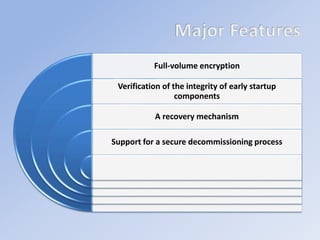
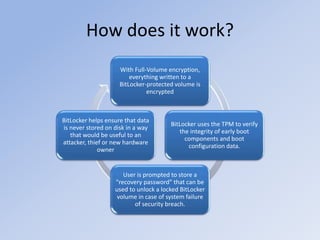
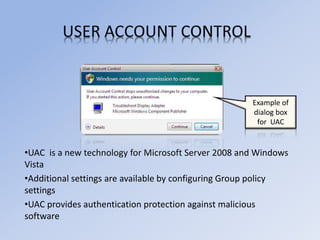
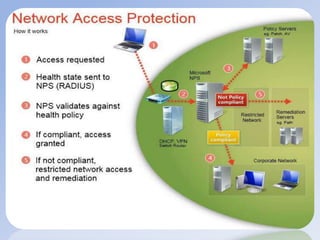
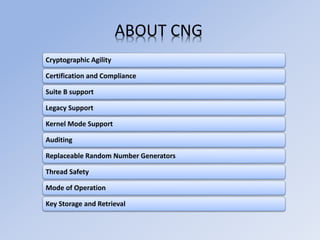
Unified malware protection for business desktops, laptops and server operating systems that provides unified protection, simplified administration and visibility and control. Key features include real-time virus protection, advanced malware protection, one policy to manage client agent protection across systems, customized alerts and security assessments. The document discusses security features for Server 2008 such as BitLocker drive encryption, user account control, read-only domain controllers, network access protection and cryptography next generation.