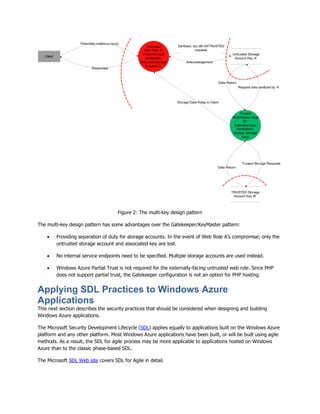
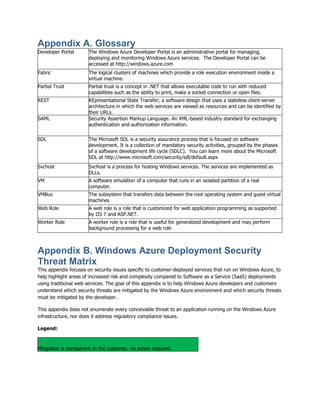
This document provides guidelines for developing secure applications on the Windows Azure platform, emphasizing the importance of identity management, access control, and awareness of specific security threats. It outlines best practices for leveraging Azure platform services and tools while addressing challenges unique to cloud-based environments. The intended audience includes software designers, architects, developers, and testers seeking to create robust and secure cloud applications.