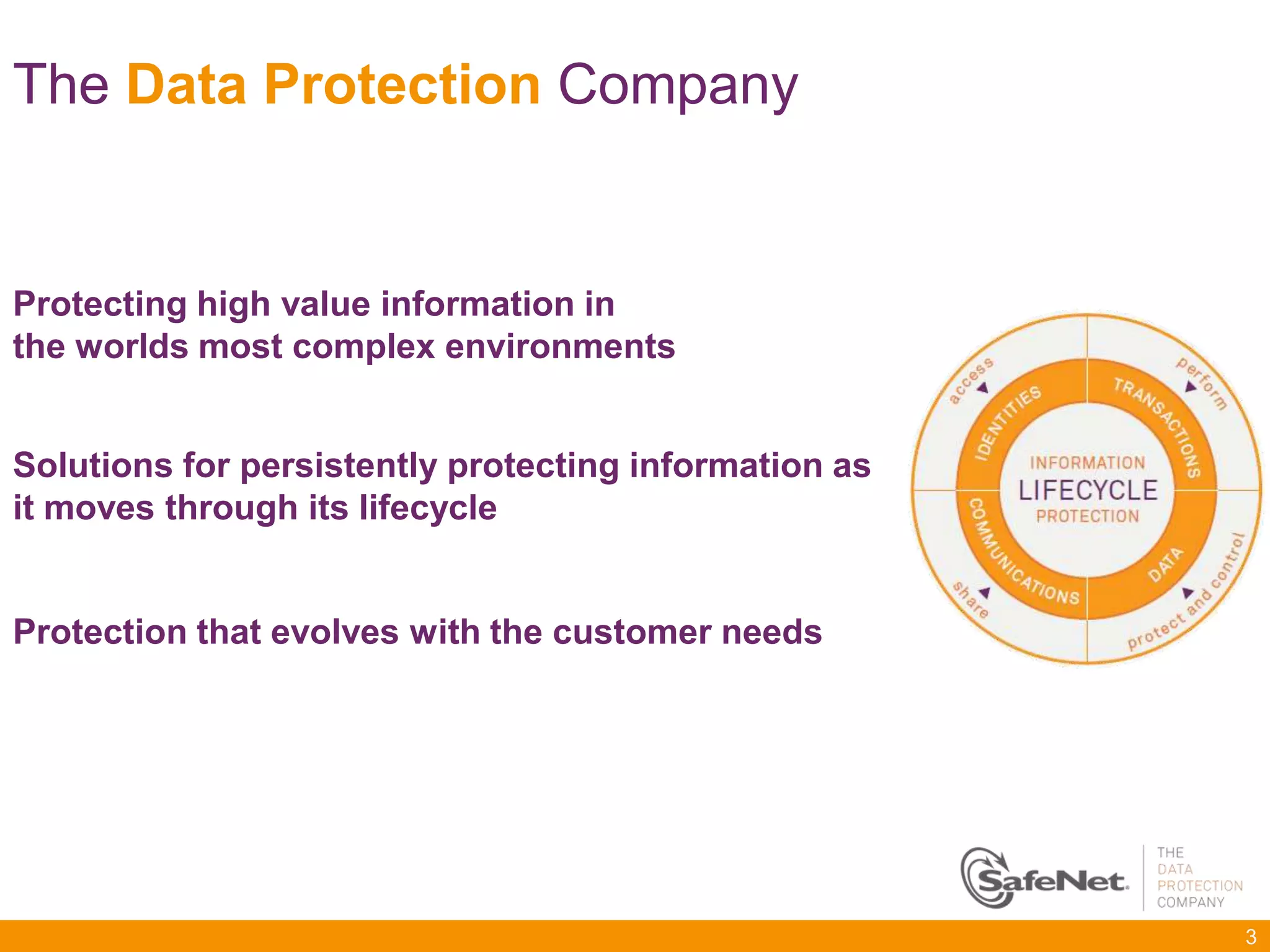
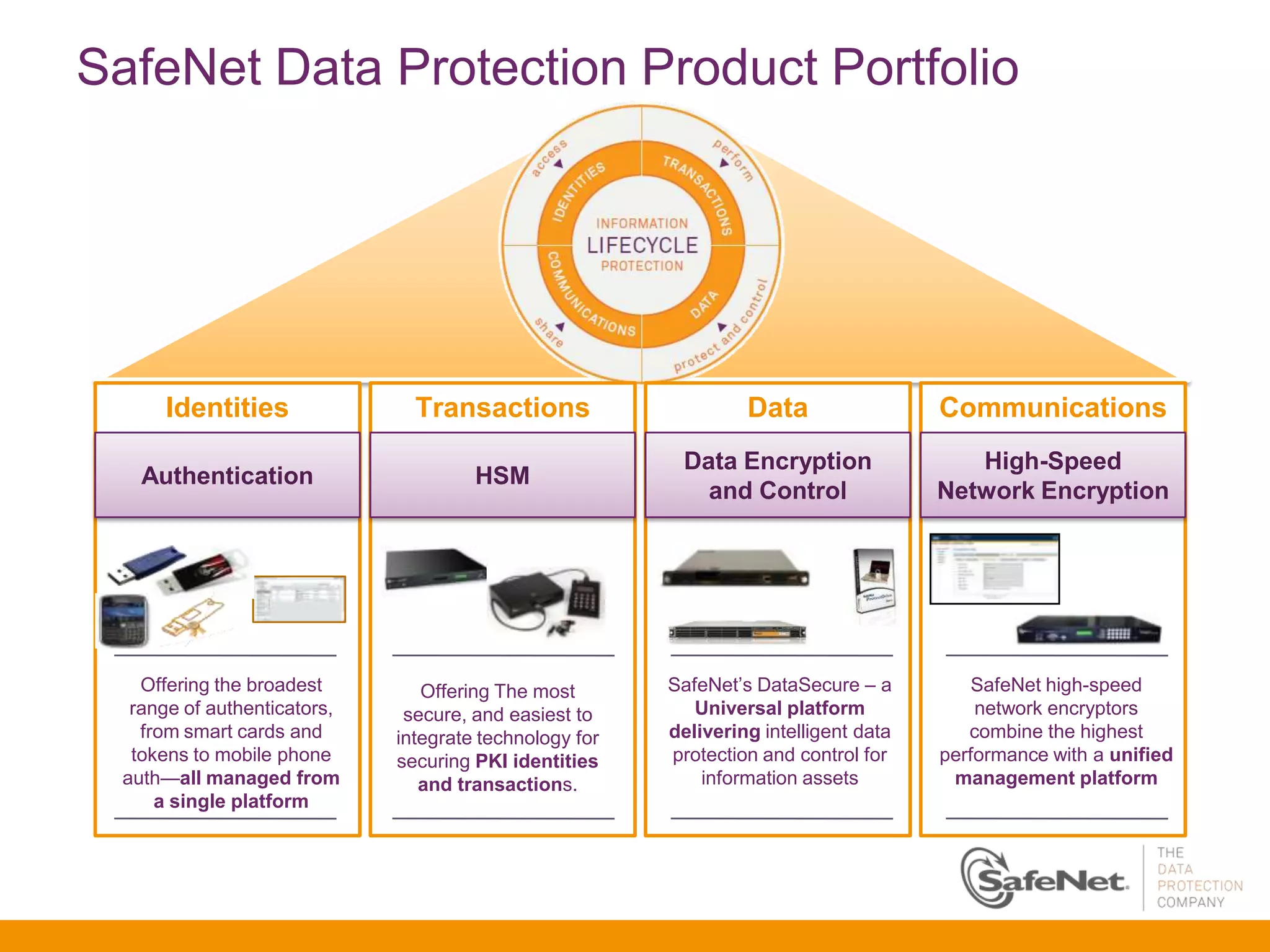
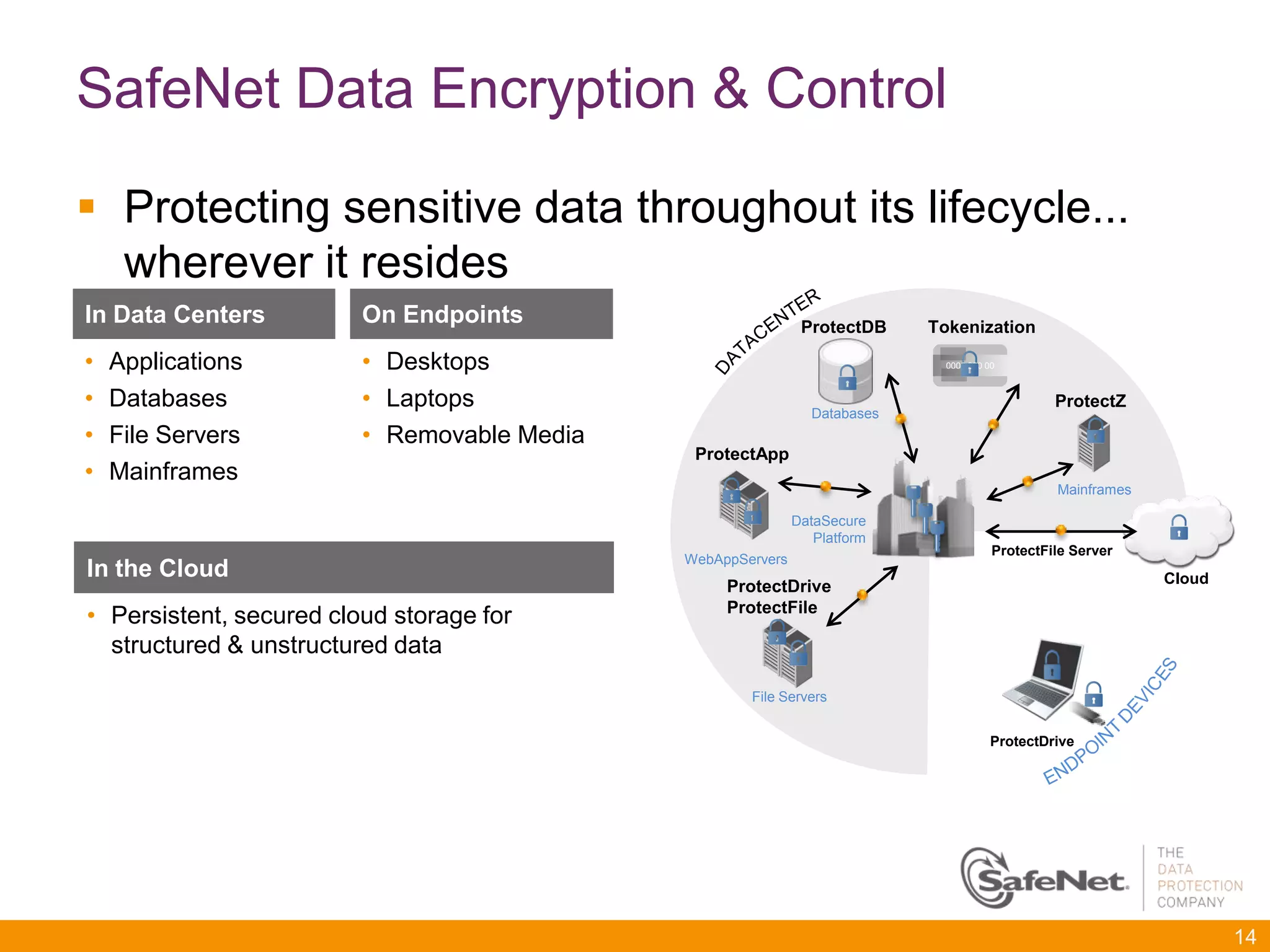
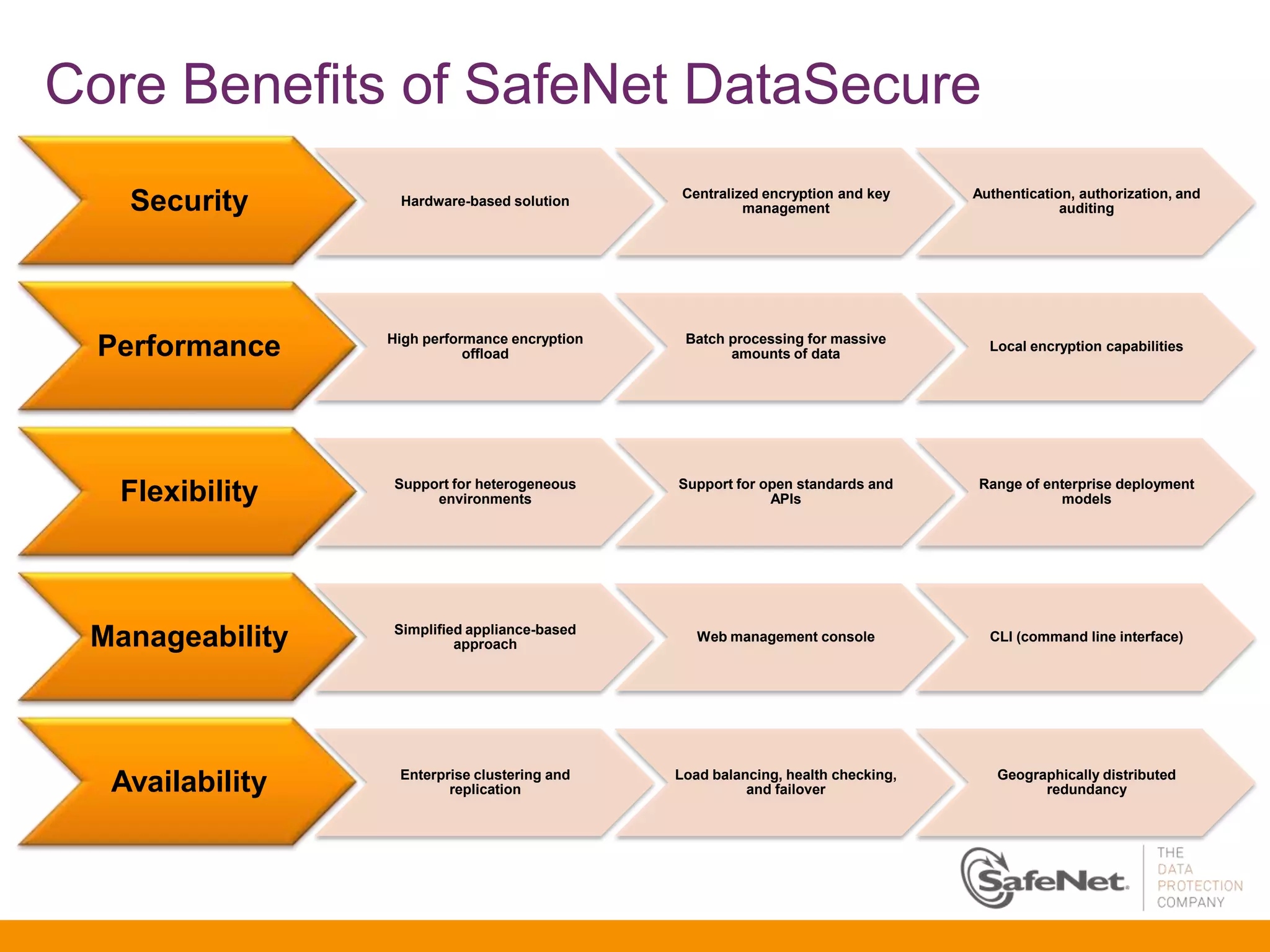
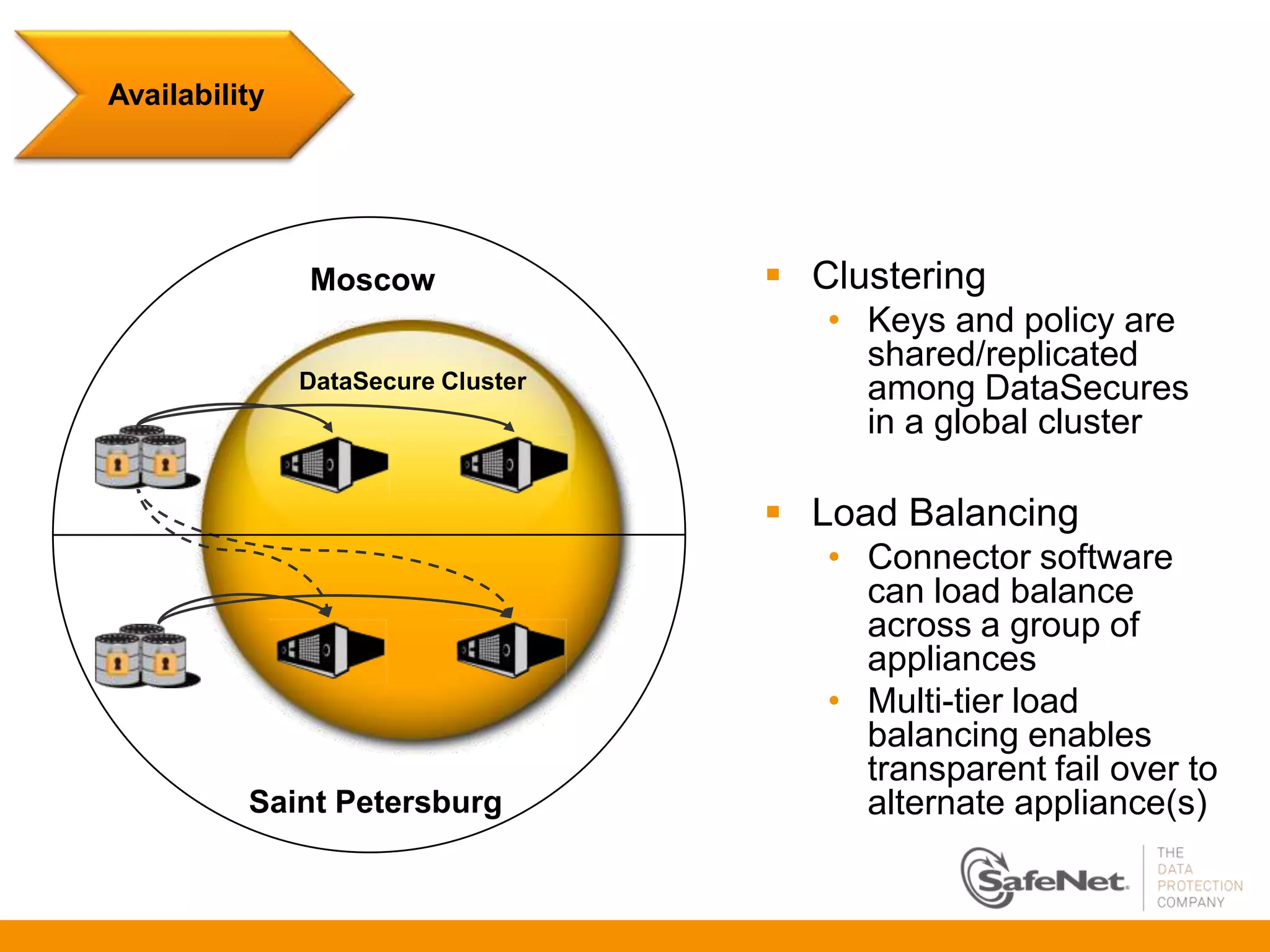
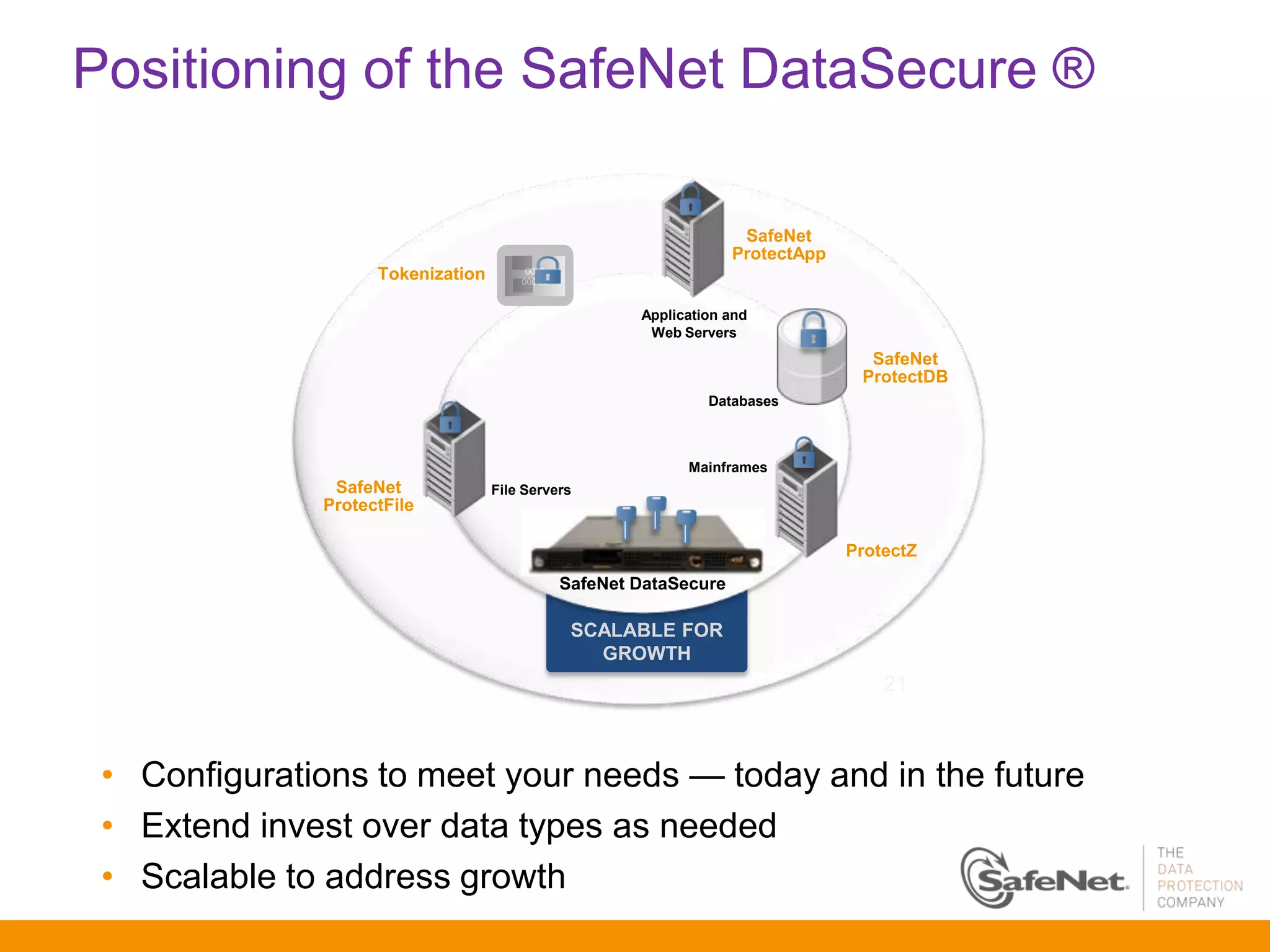
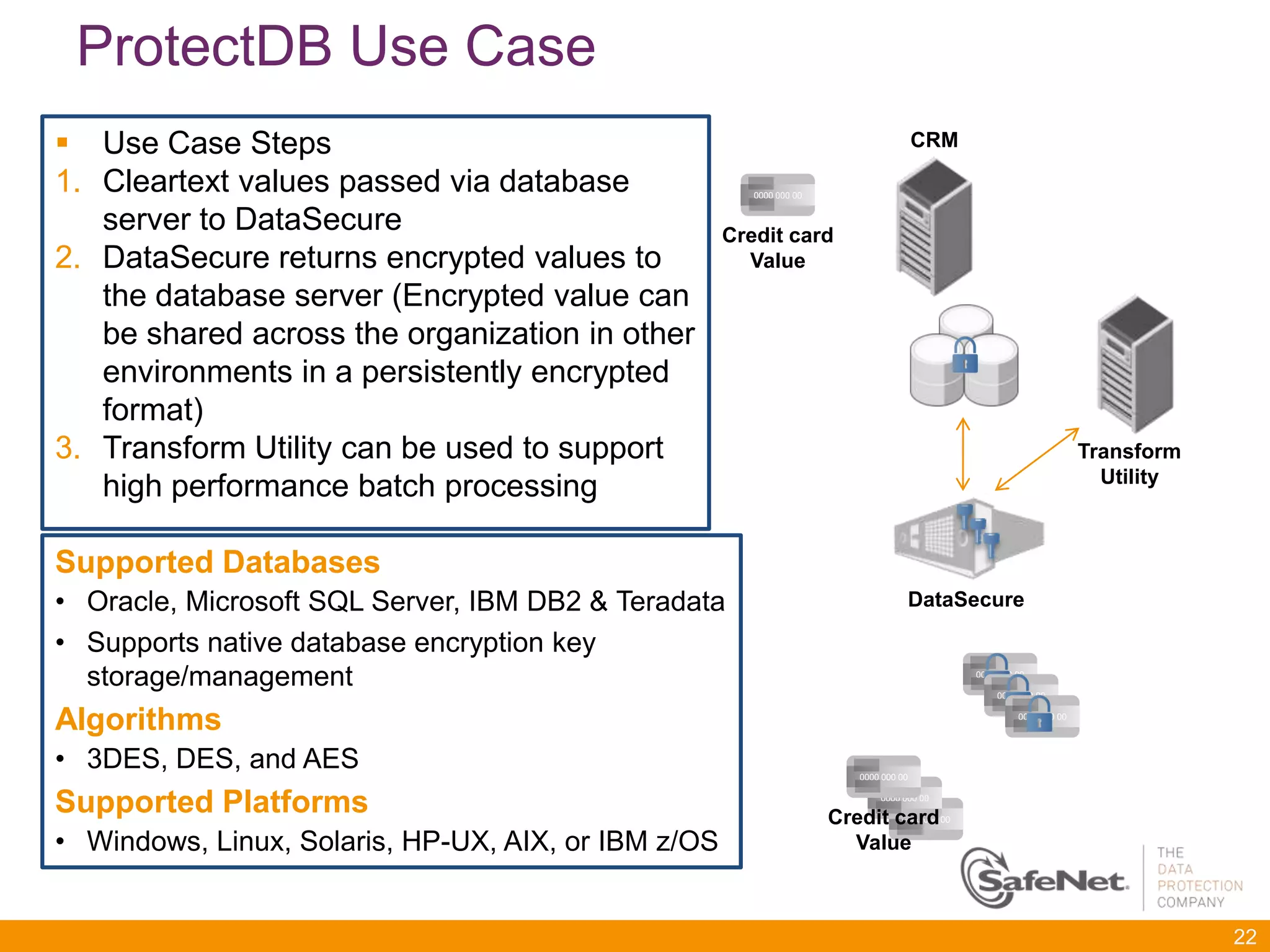
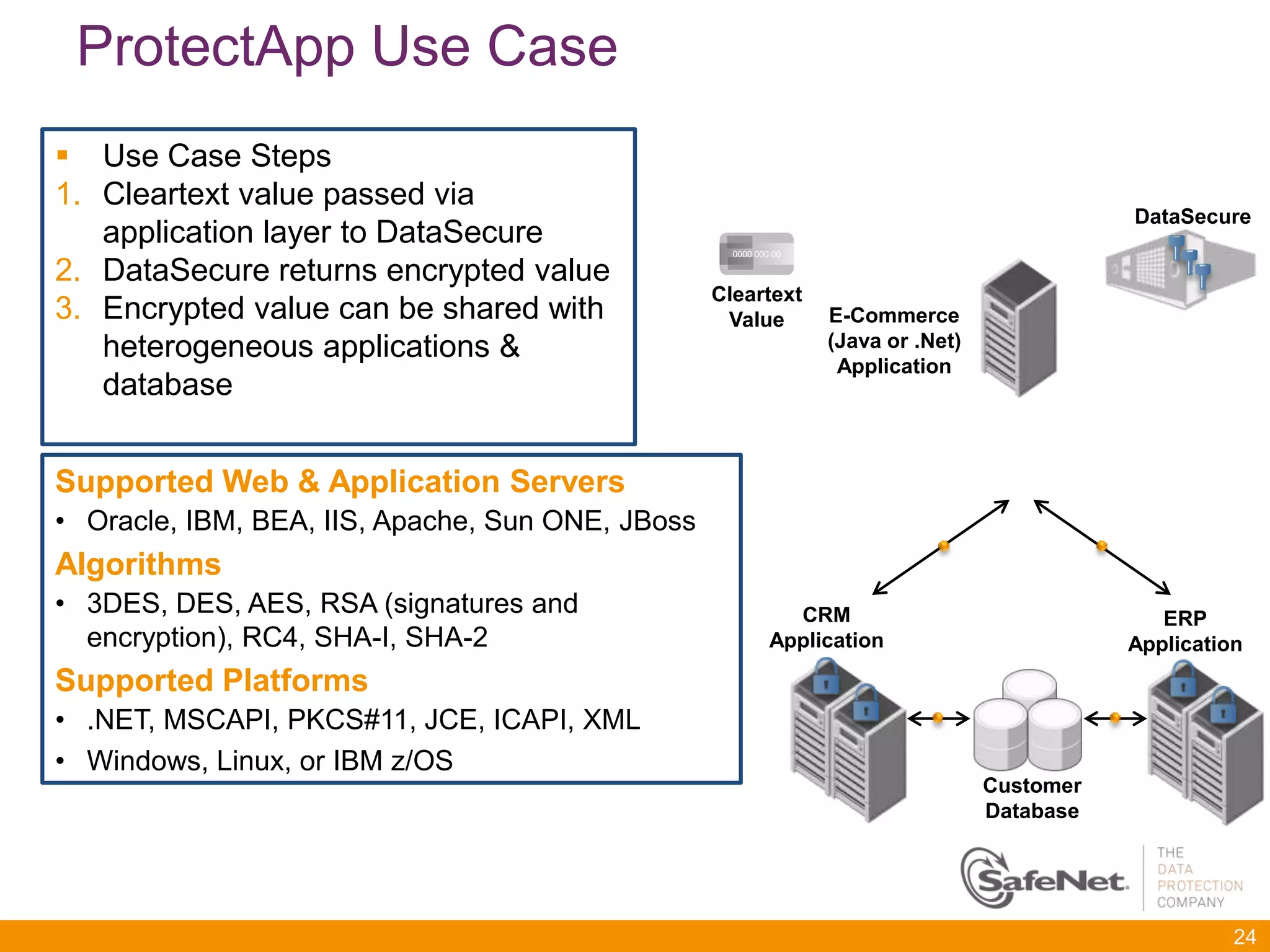
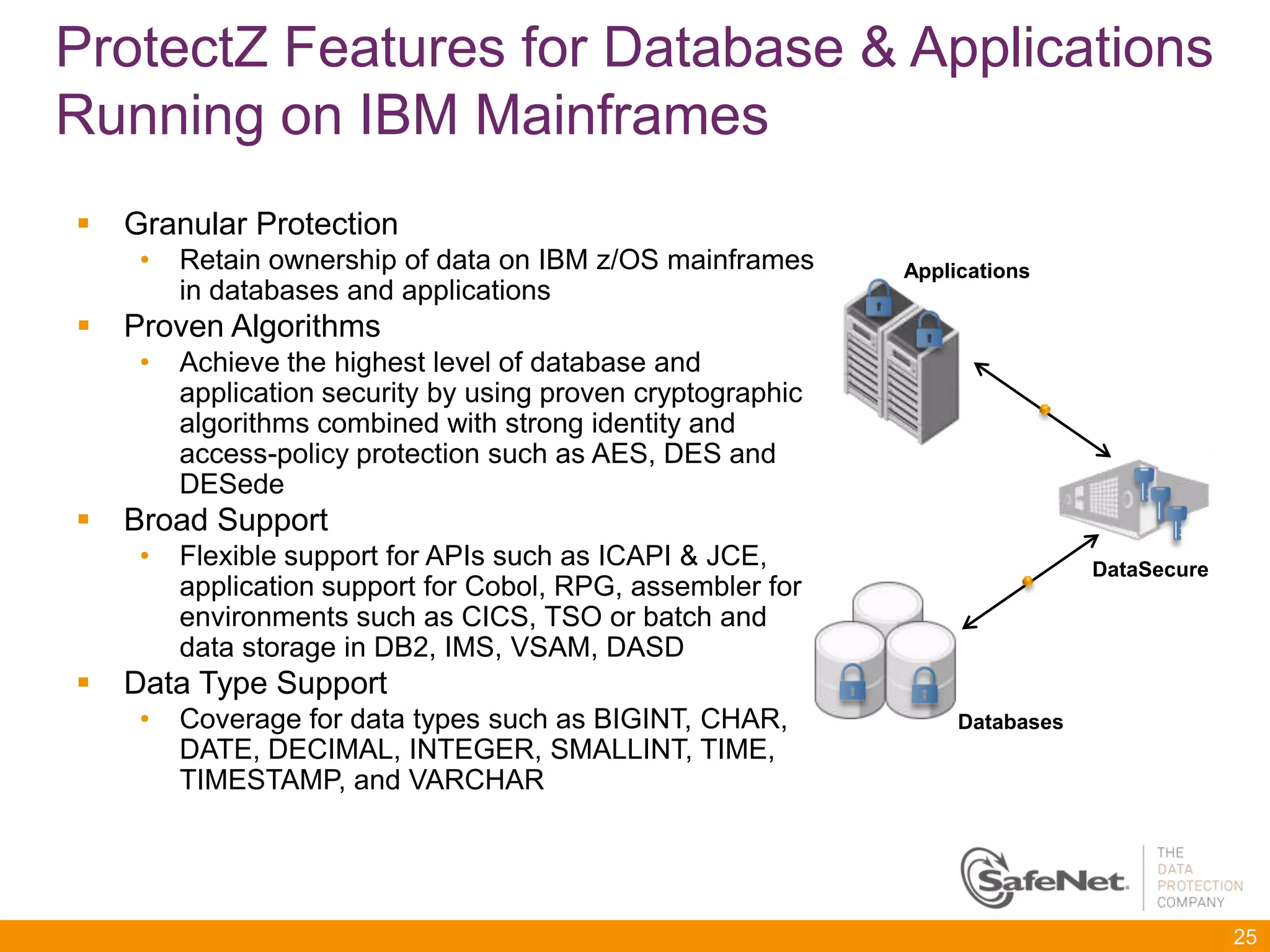
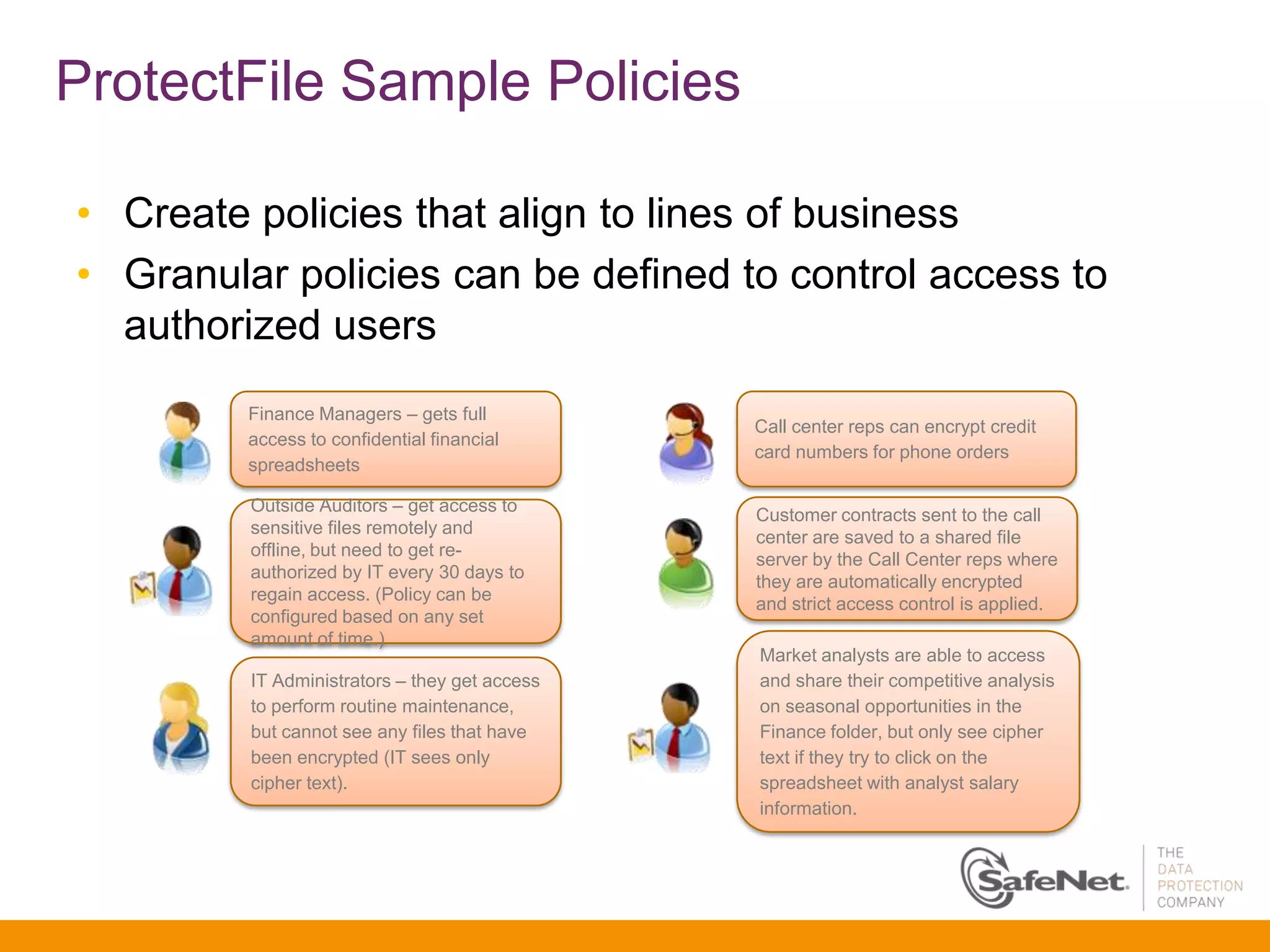
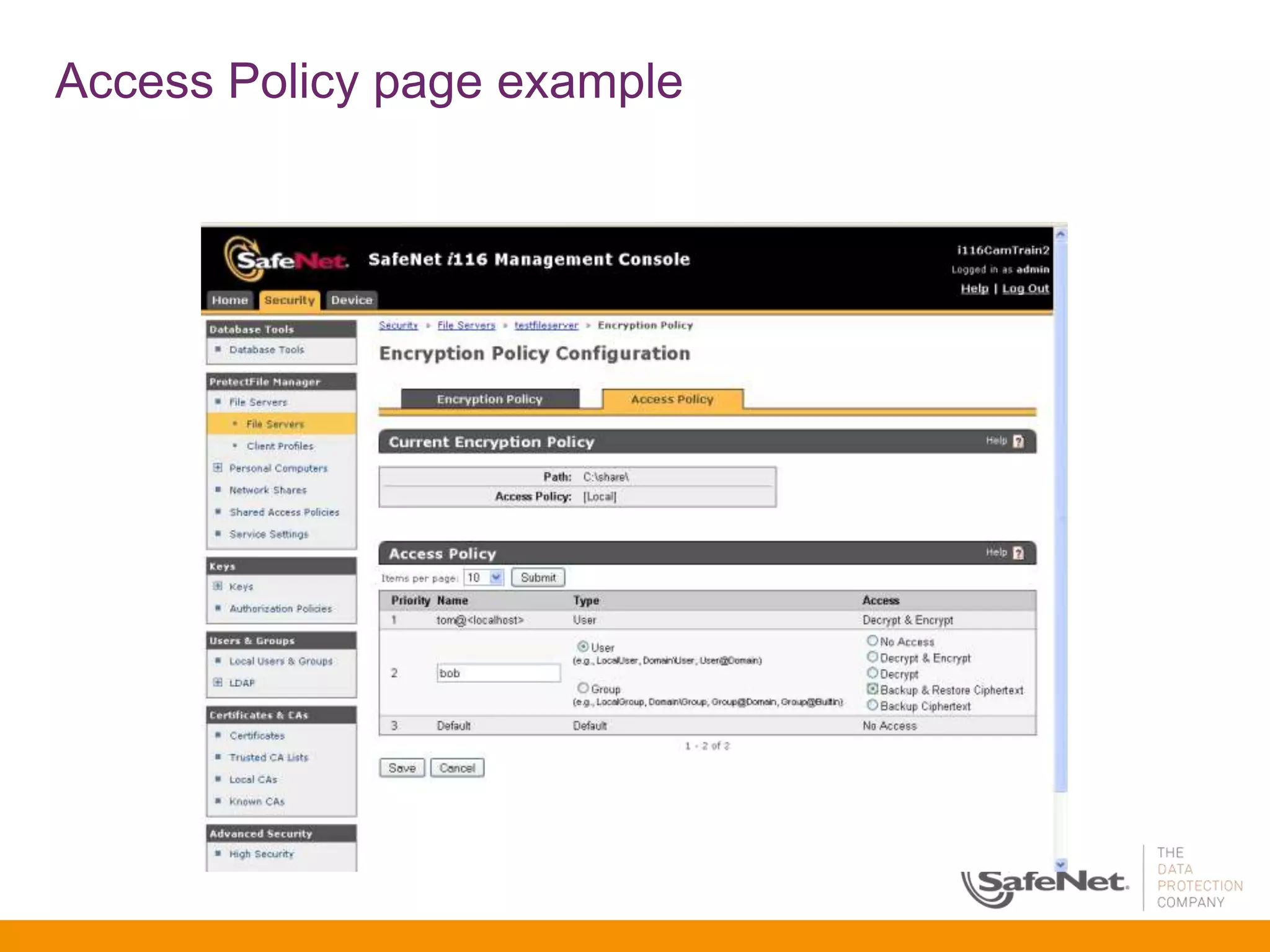
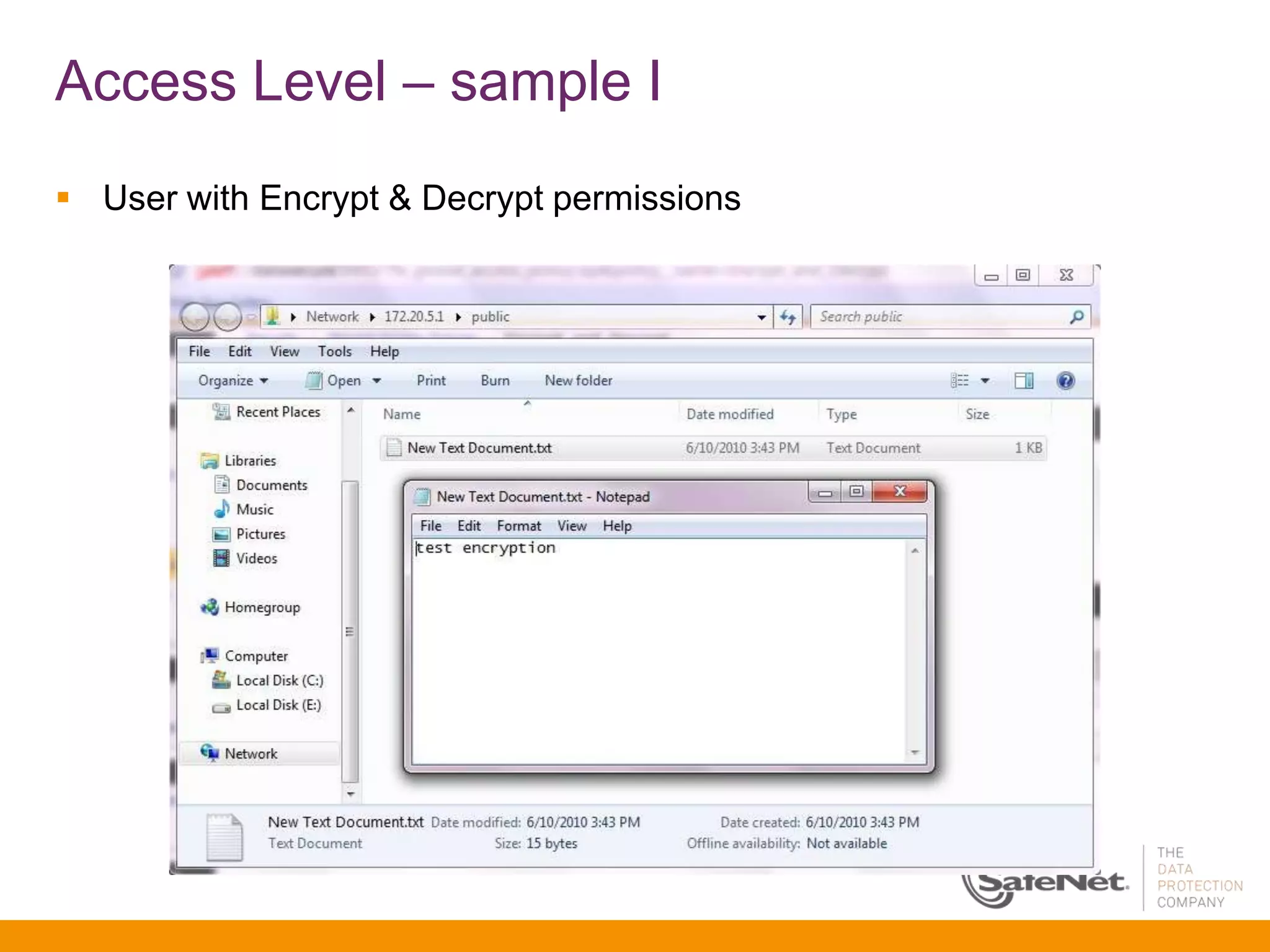
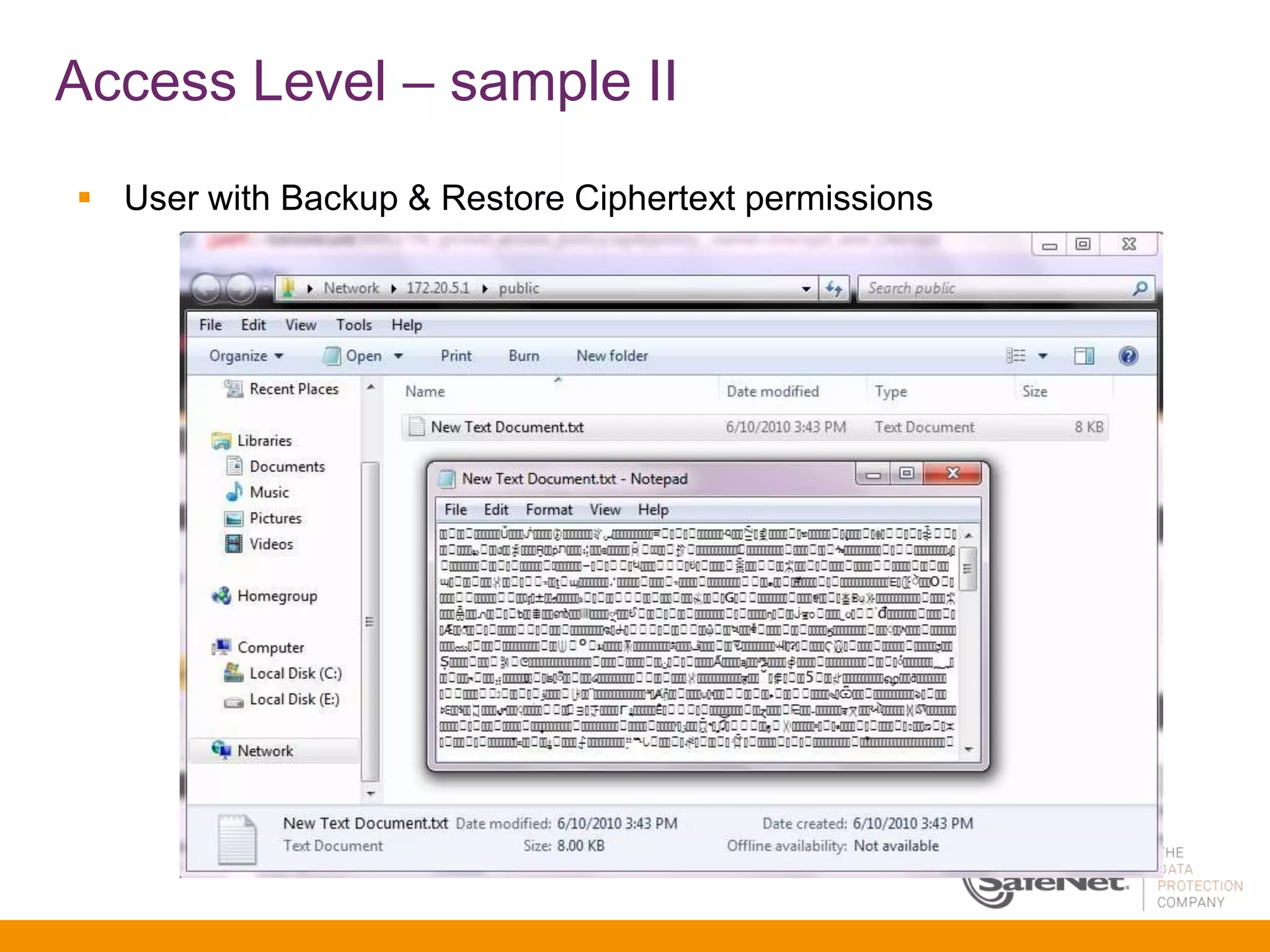
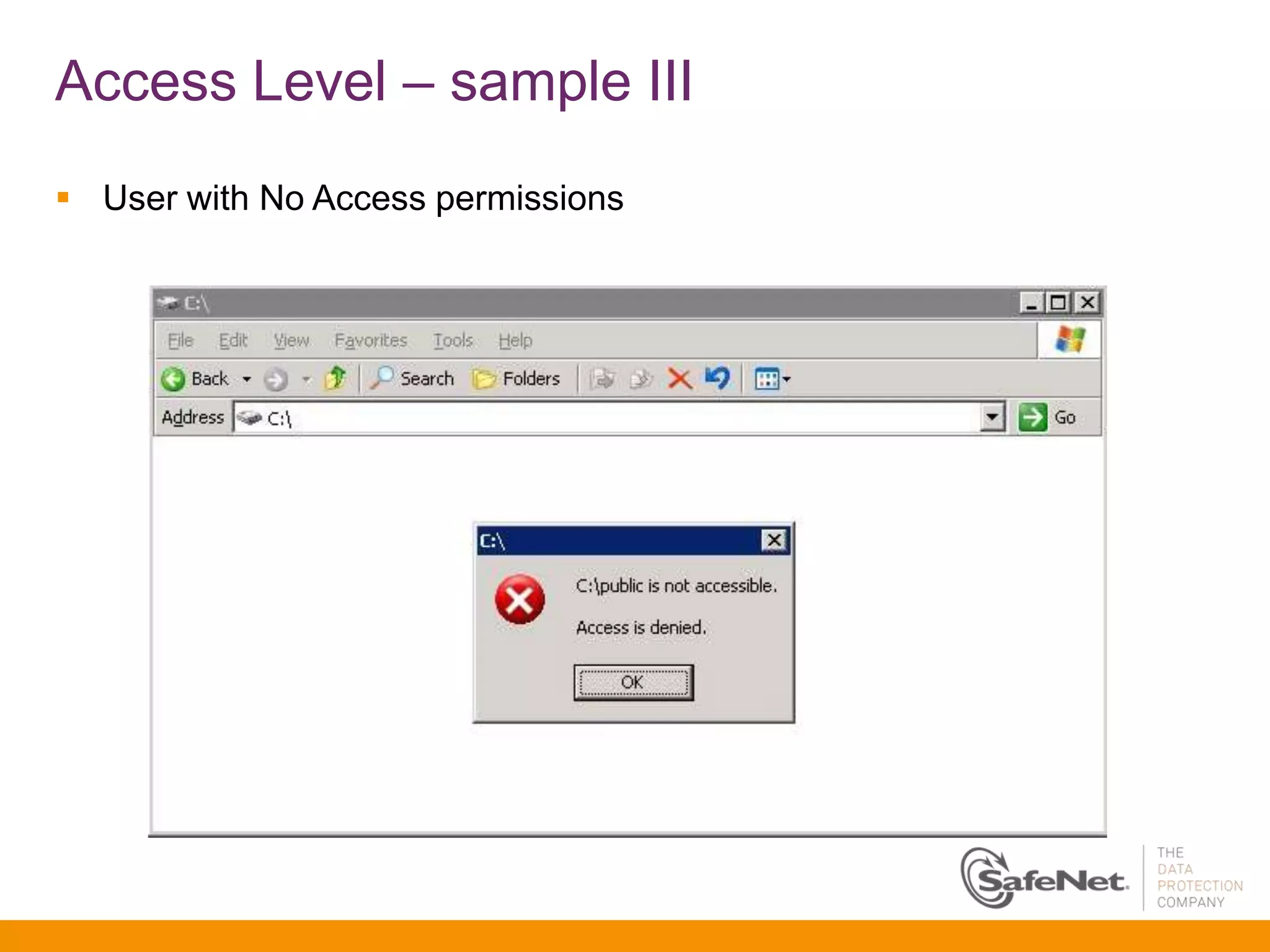
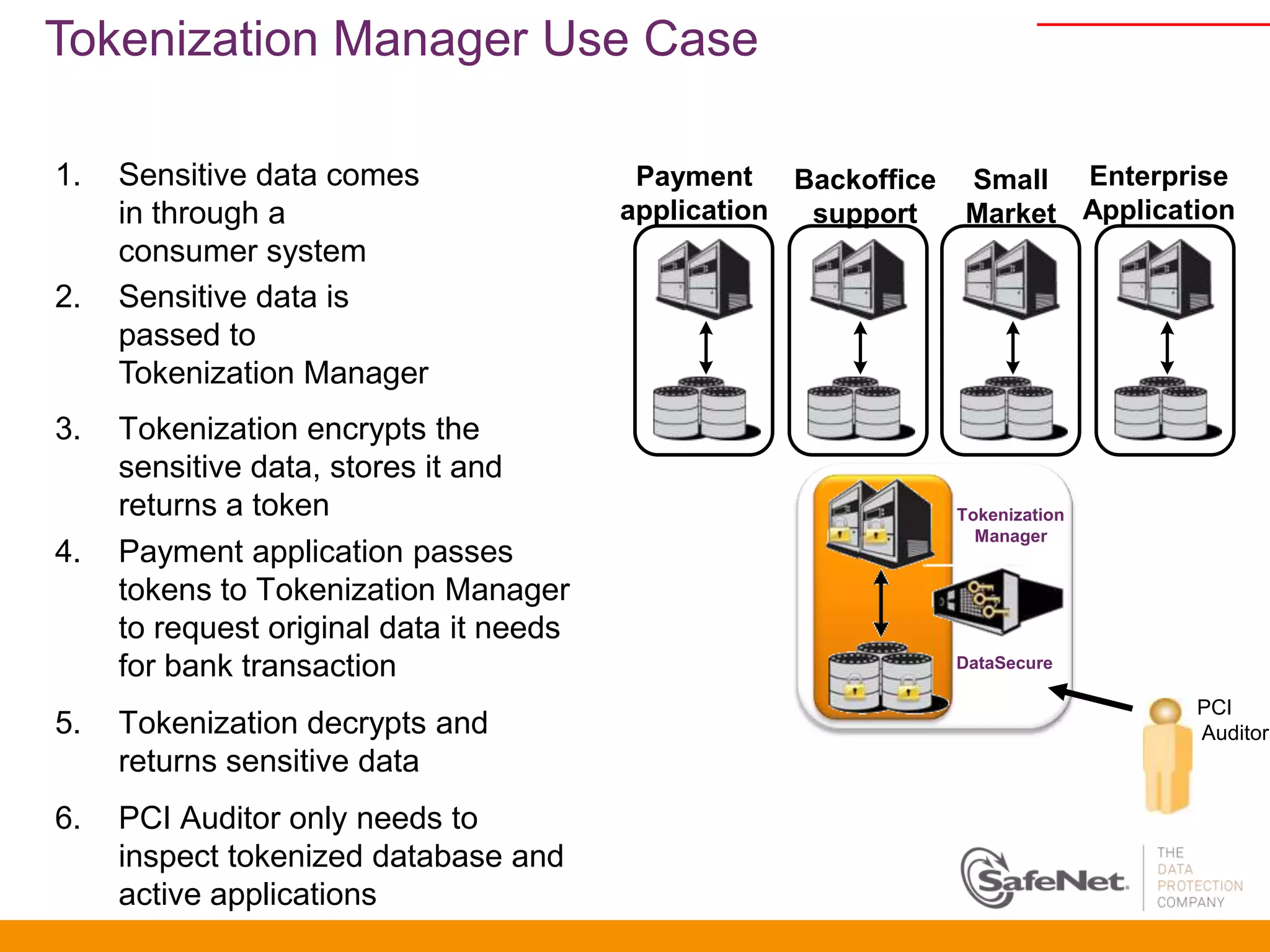
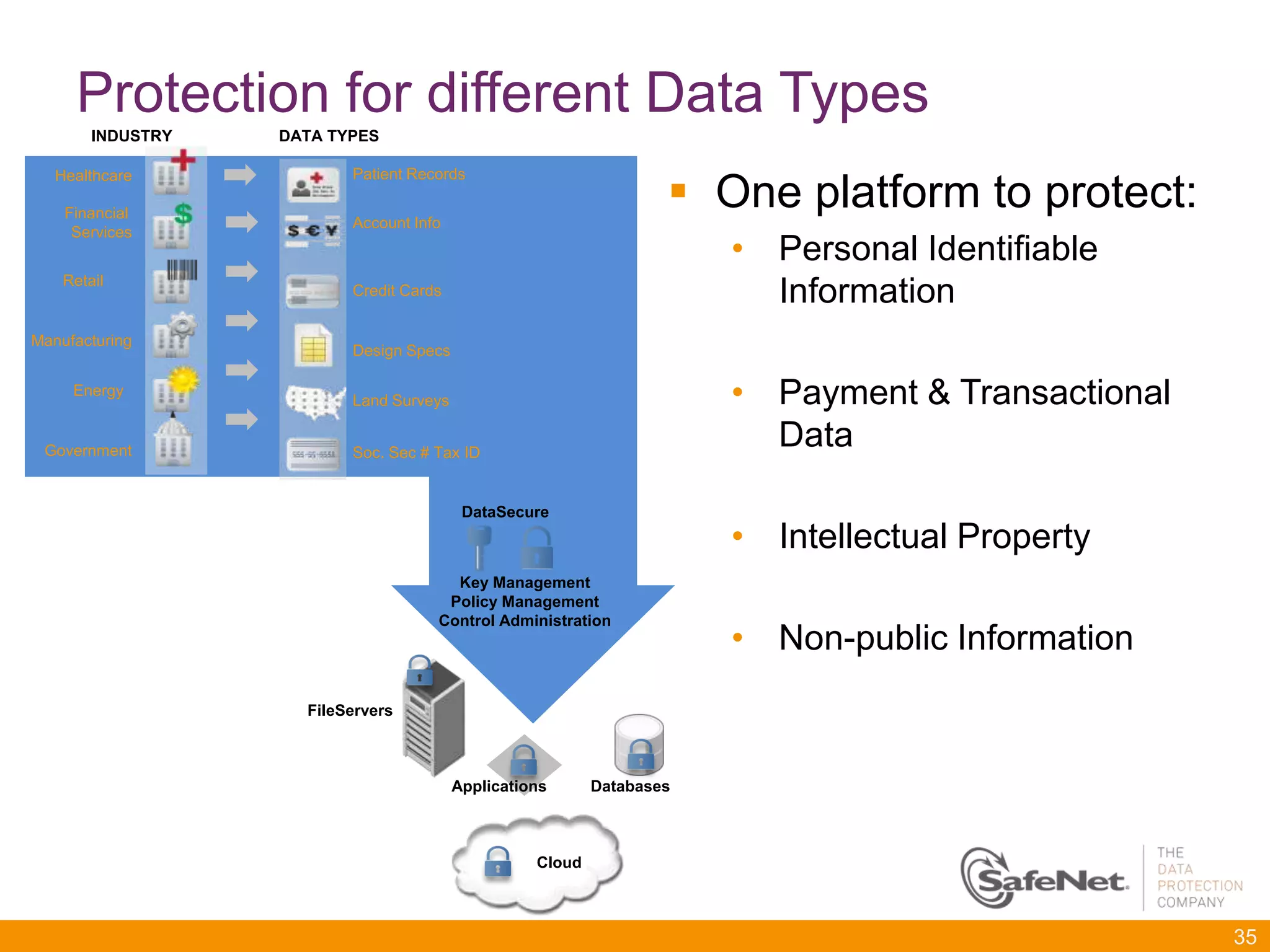
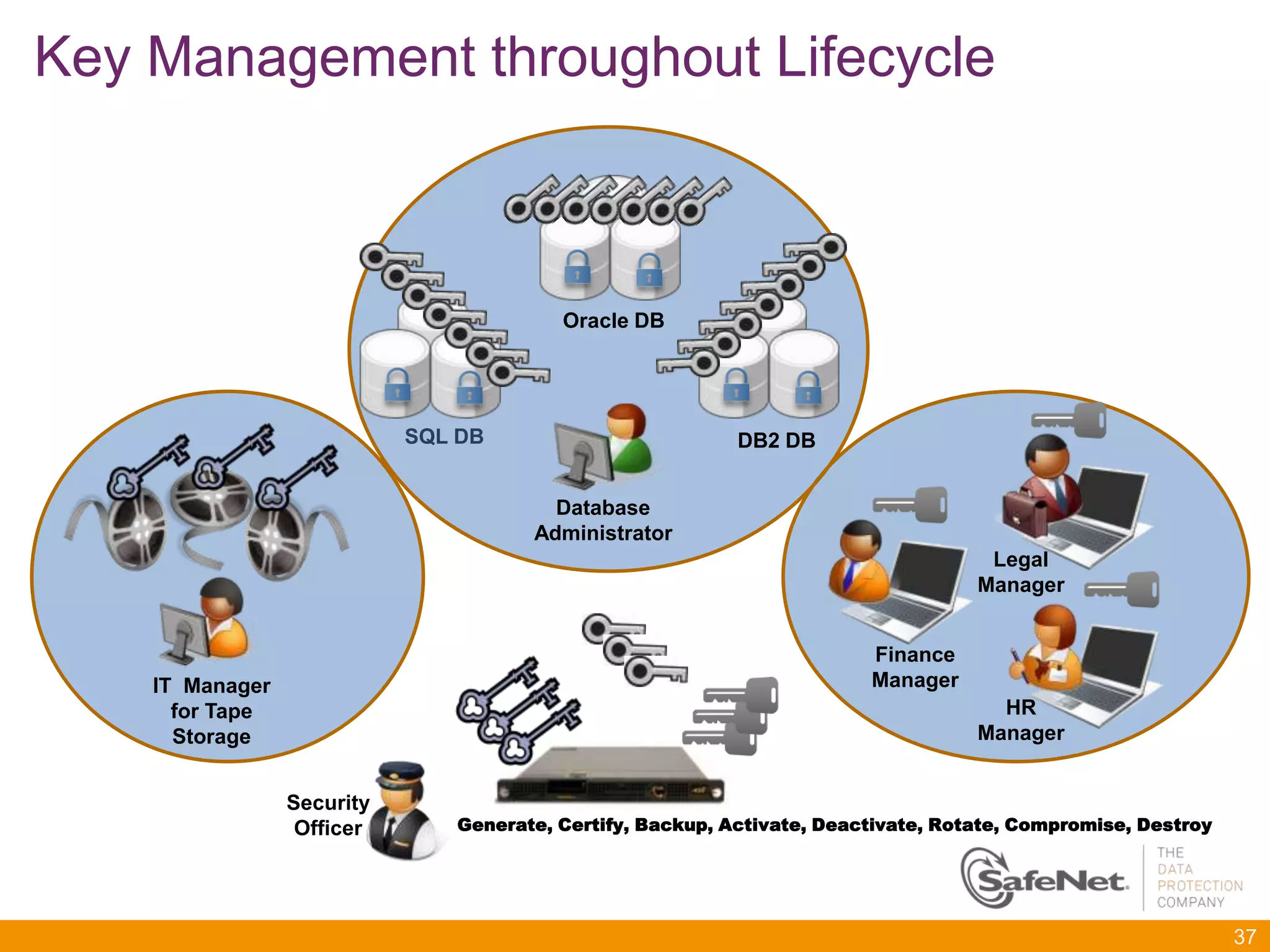
The document discusses SafeNet's DataSecure platform for protecting information through its lifecycle. DataSecure provides a universal platform for intelligent data protection and control over information assets. It delivers solutions for persistently protecting information as it moves through its lifecycle and evolves with customer needs.