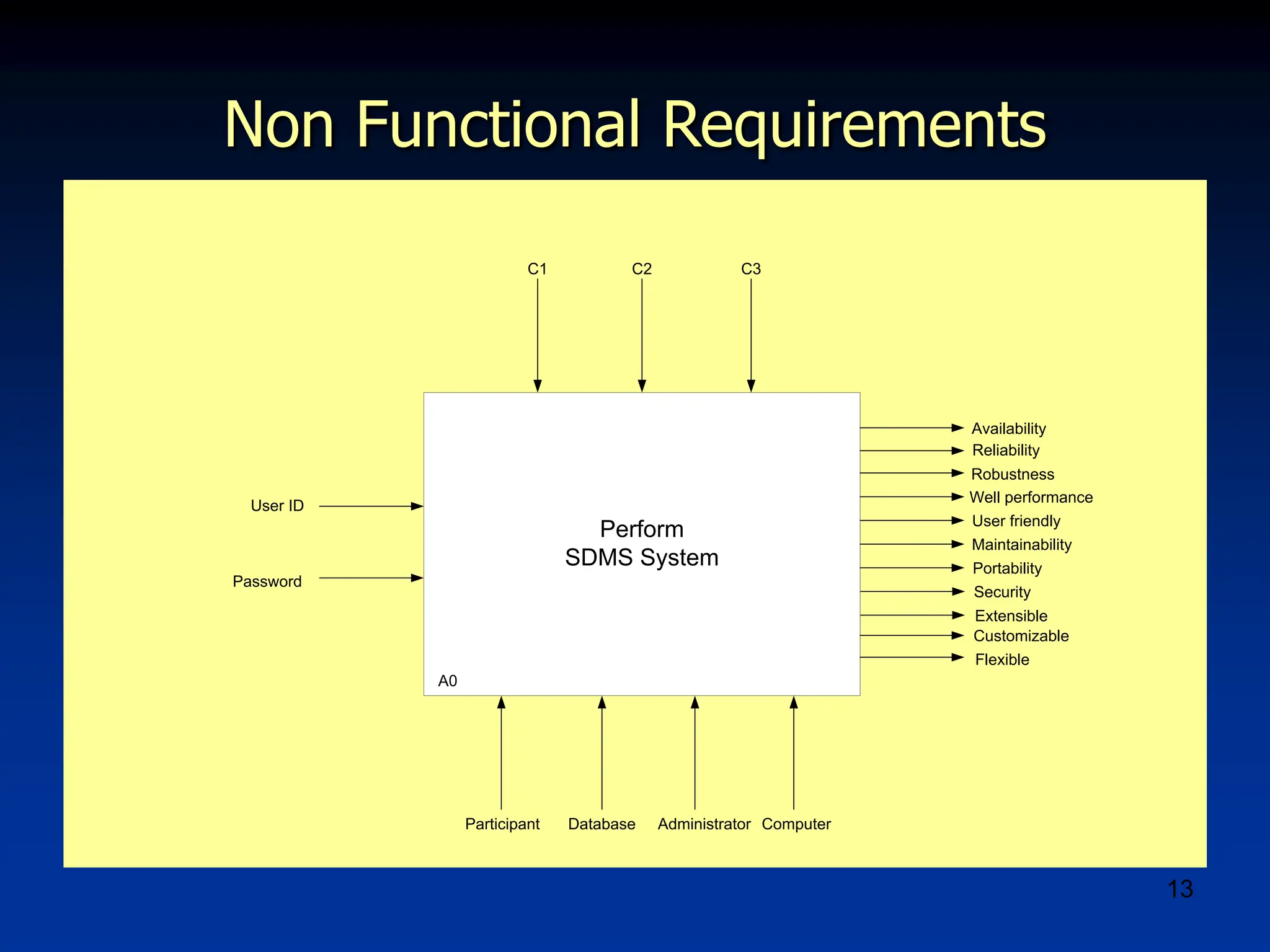
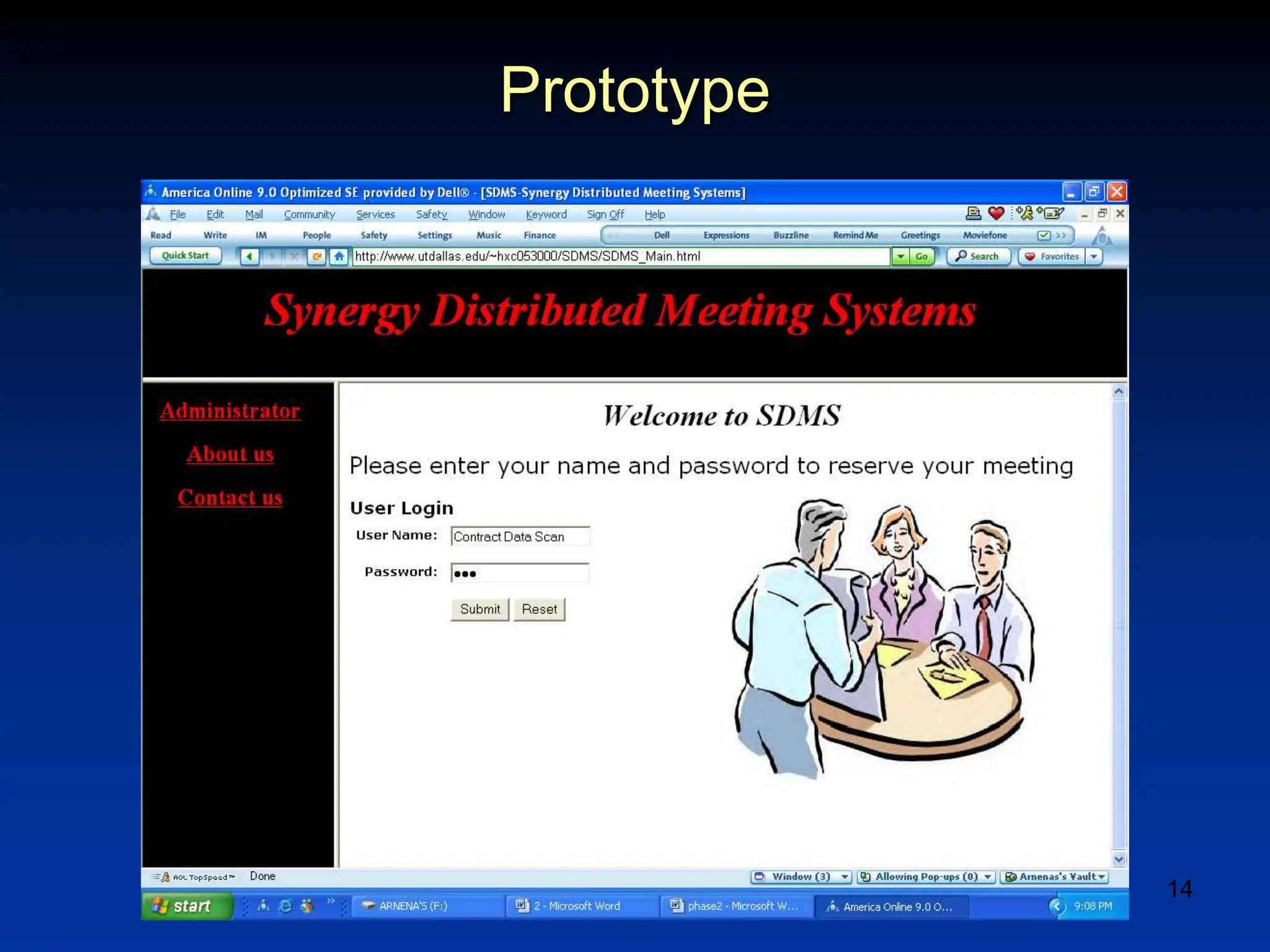
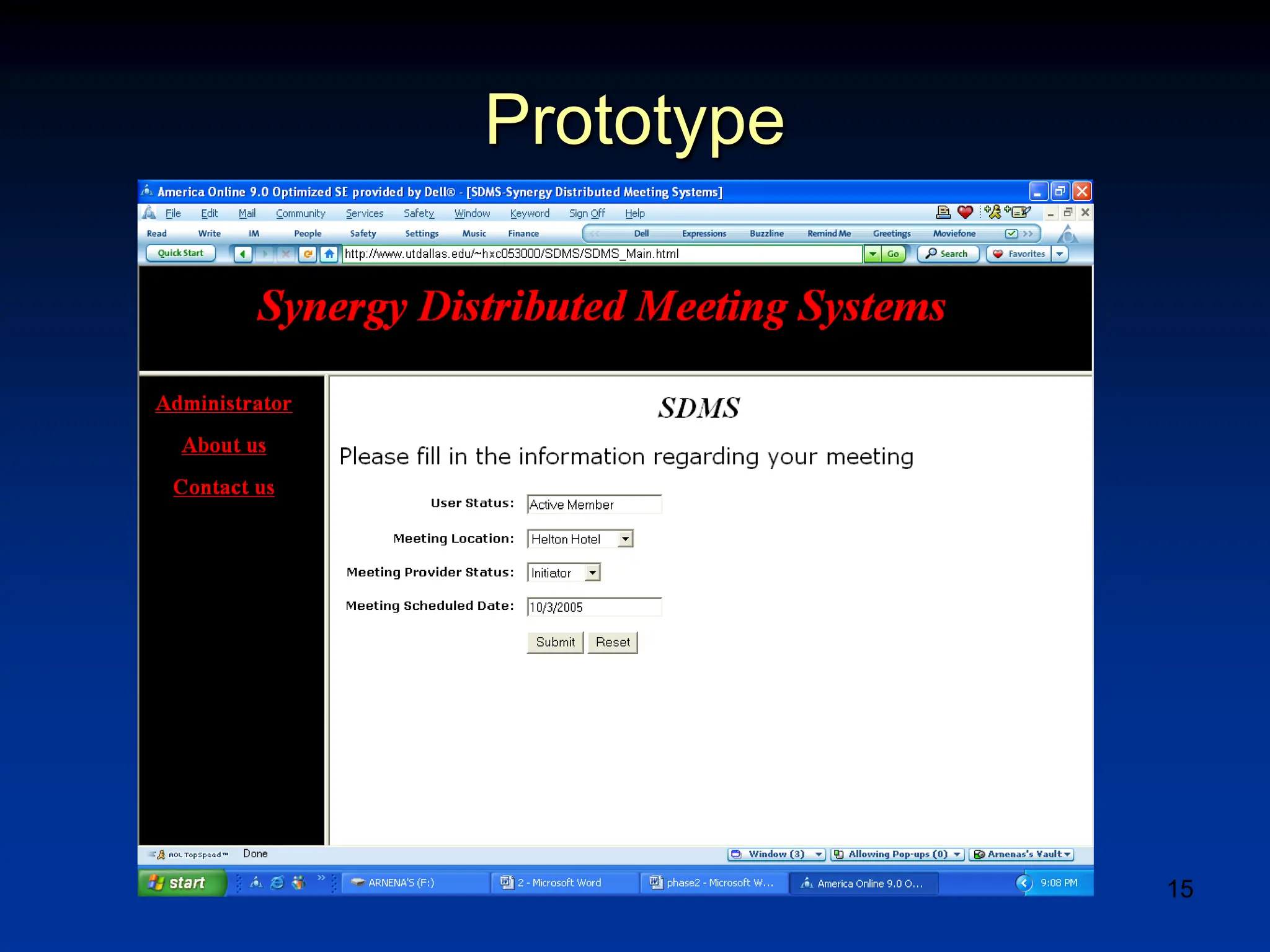
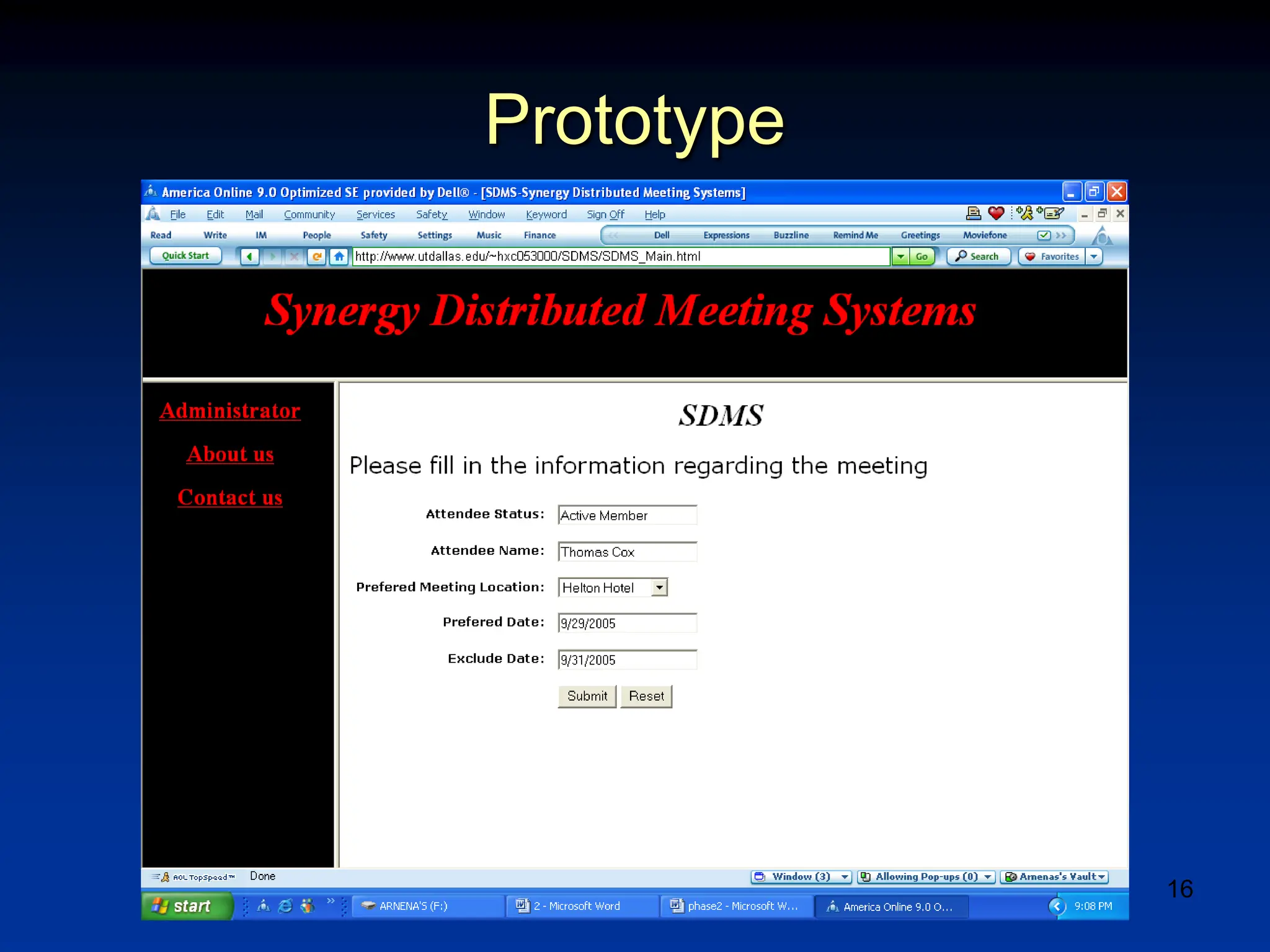
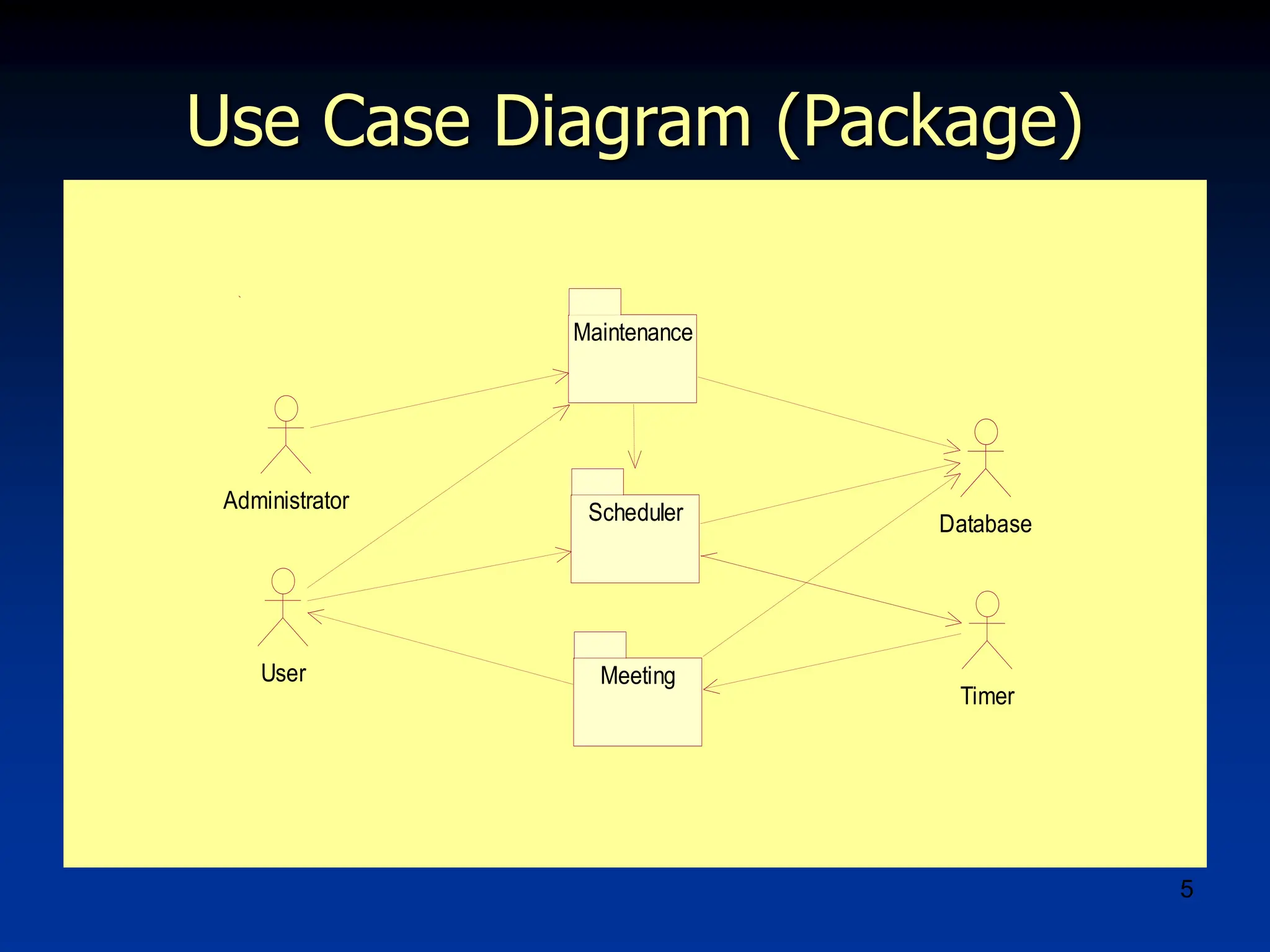
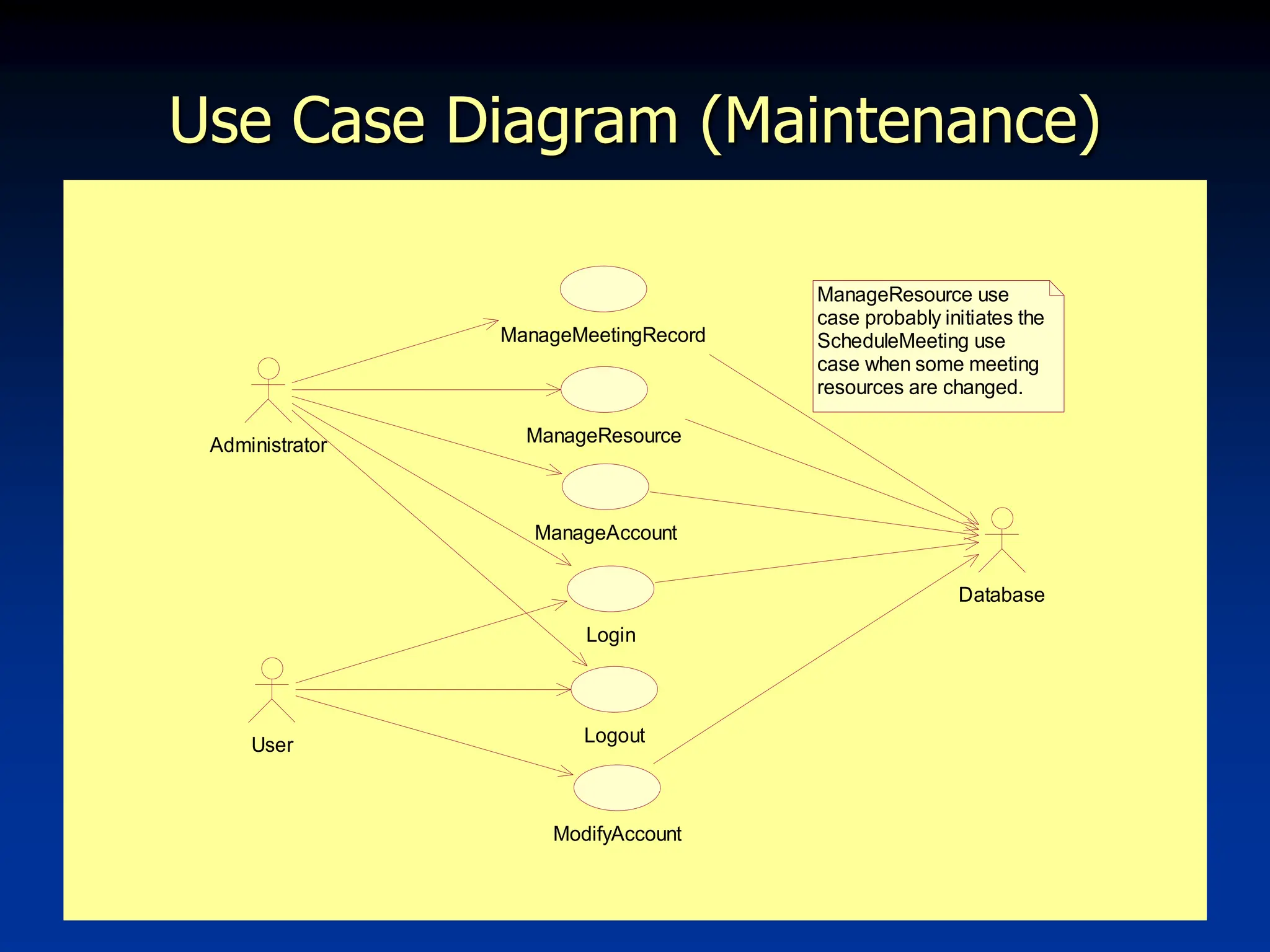
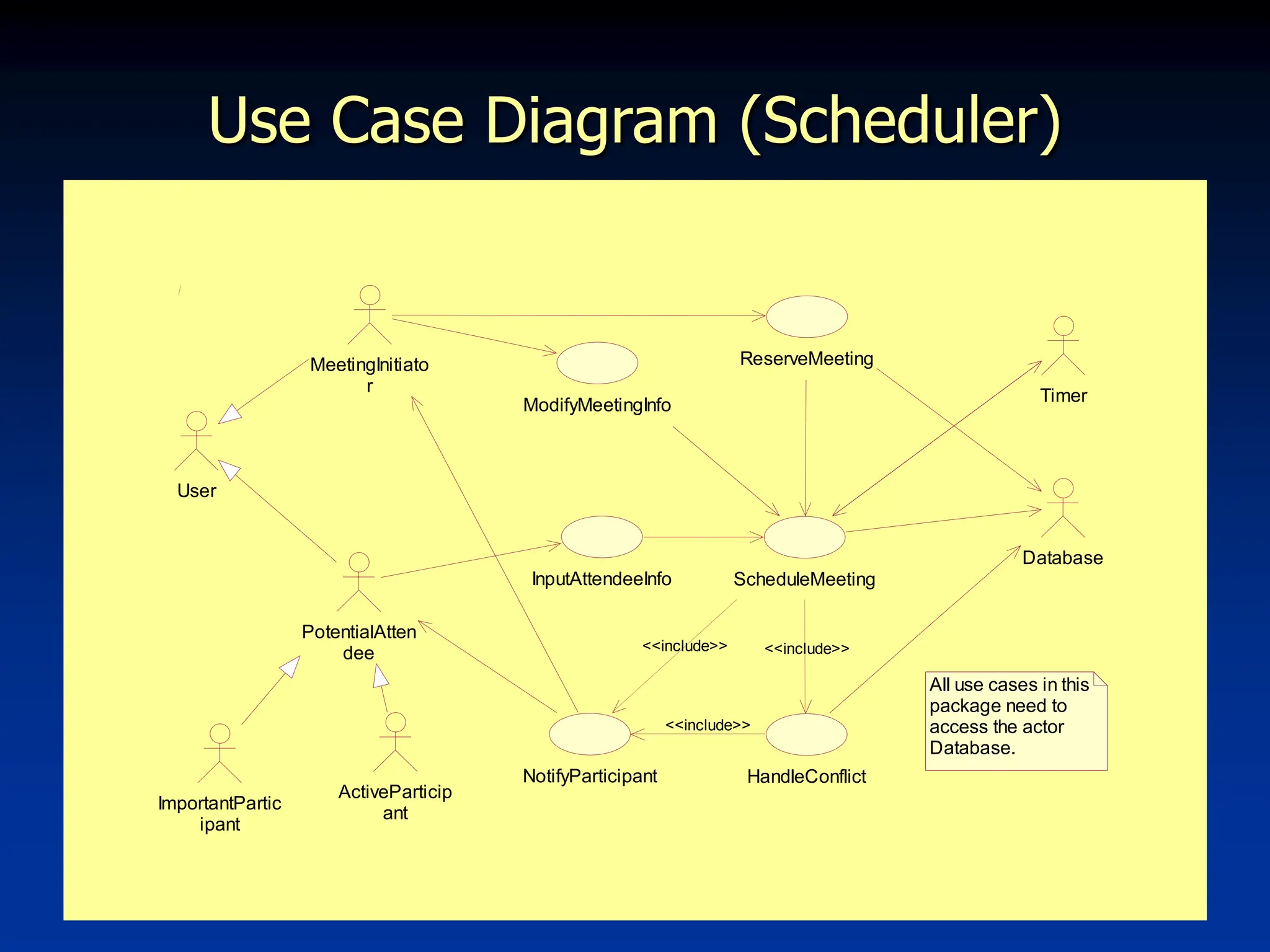
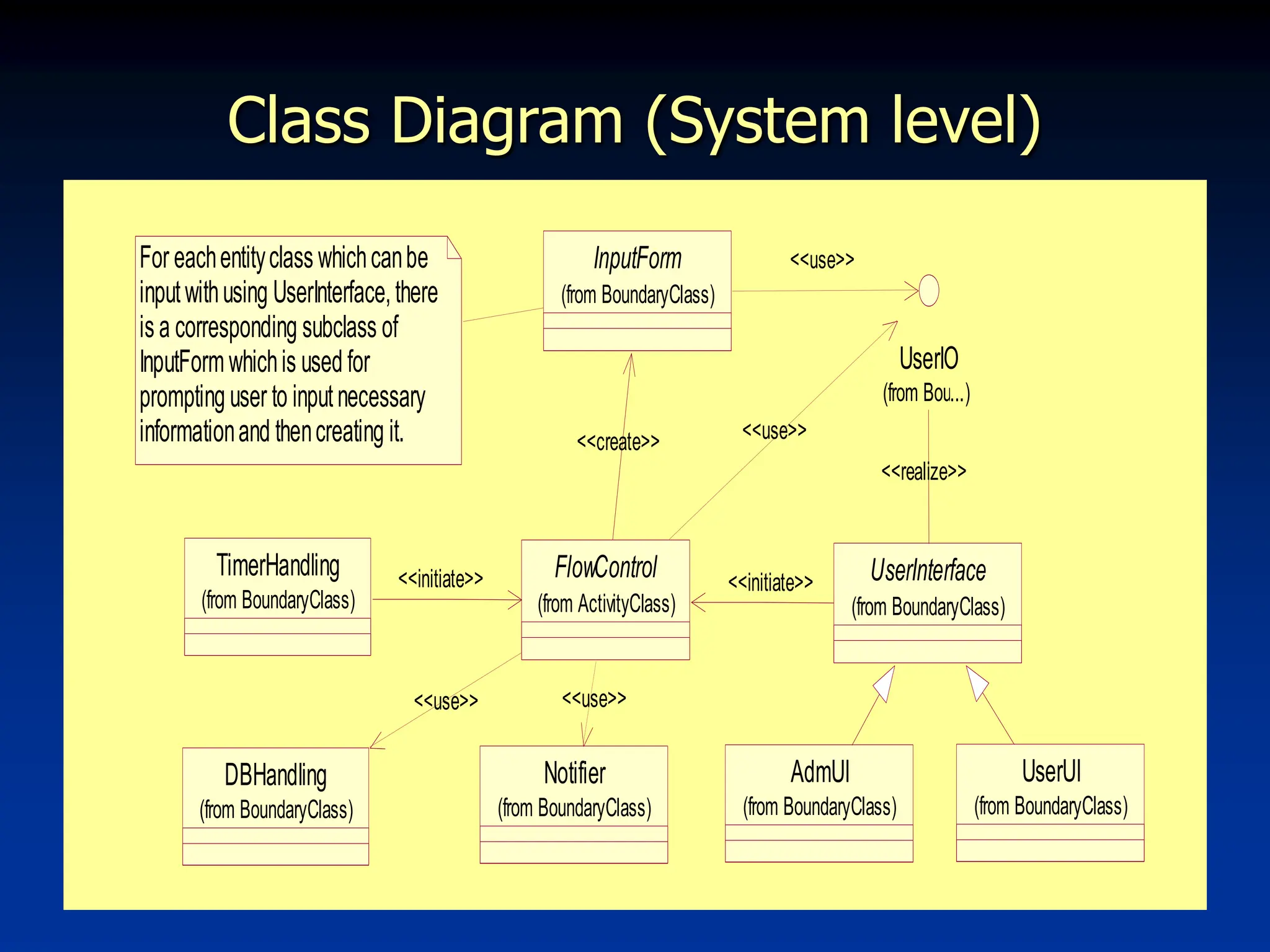
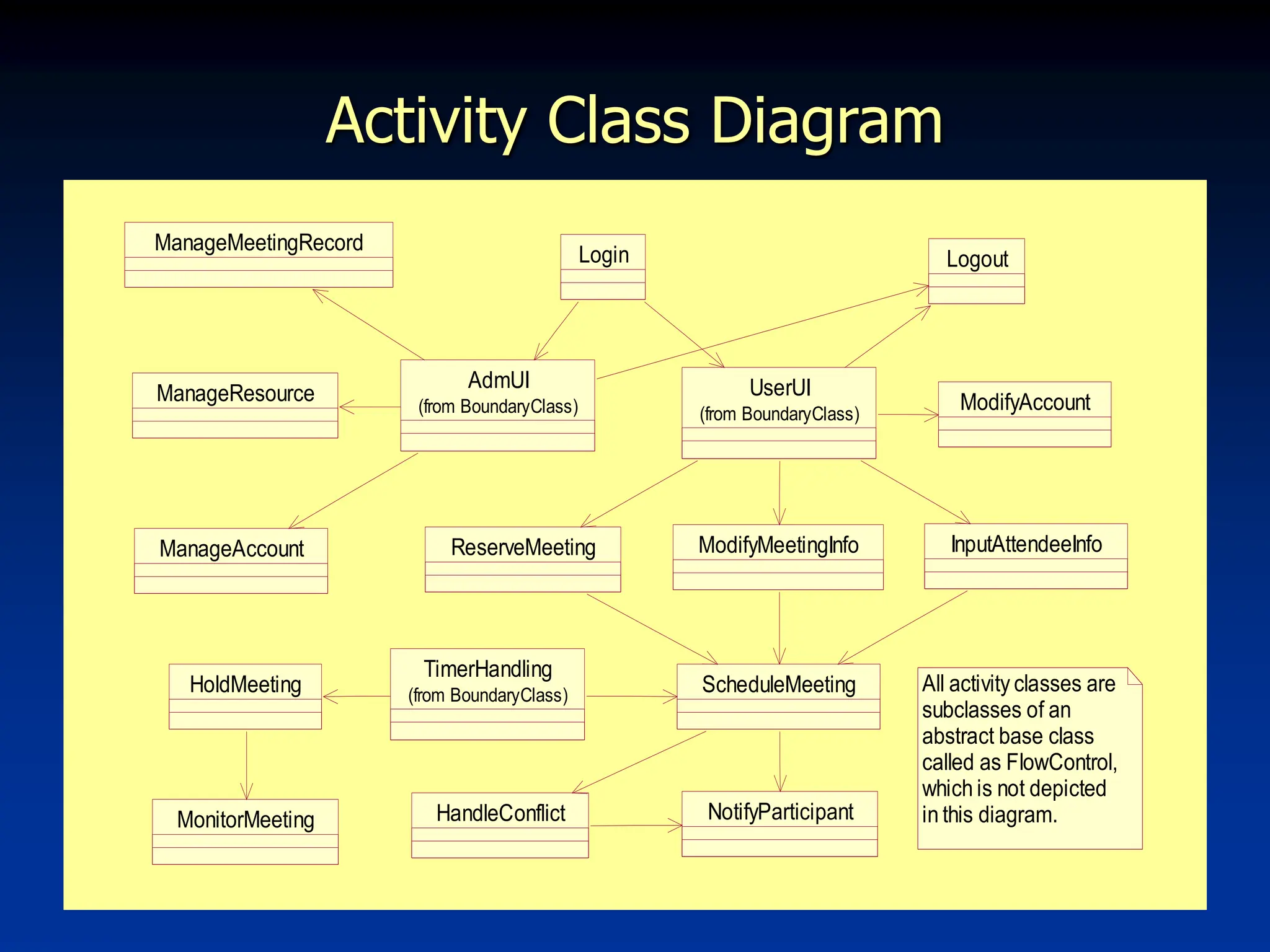
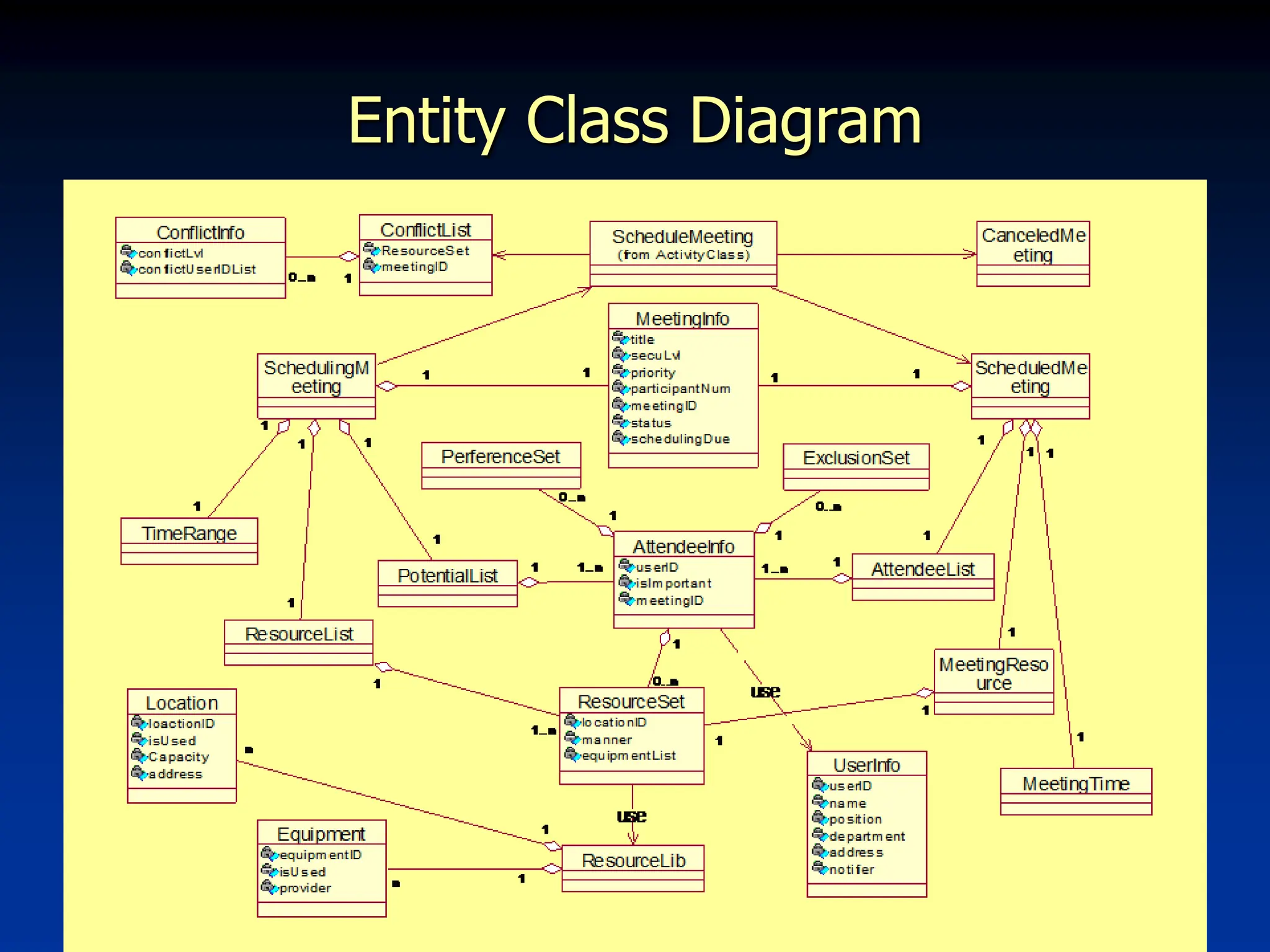
The document presents a project for an online meeting scheduling system called Synergy Distributed Meeting Scheduler (SDMS), aimed at facilitating scheduling between business partners. It includes detailed diagrams such as use case diagrams, activity class diagrams, and entity class diagrams that outline system functionality, user interactions, and system architecture. Additionally, the document addresses non-functional requirements and provides prototypes of the system.
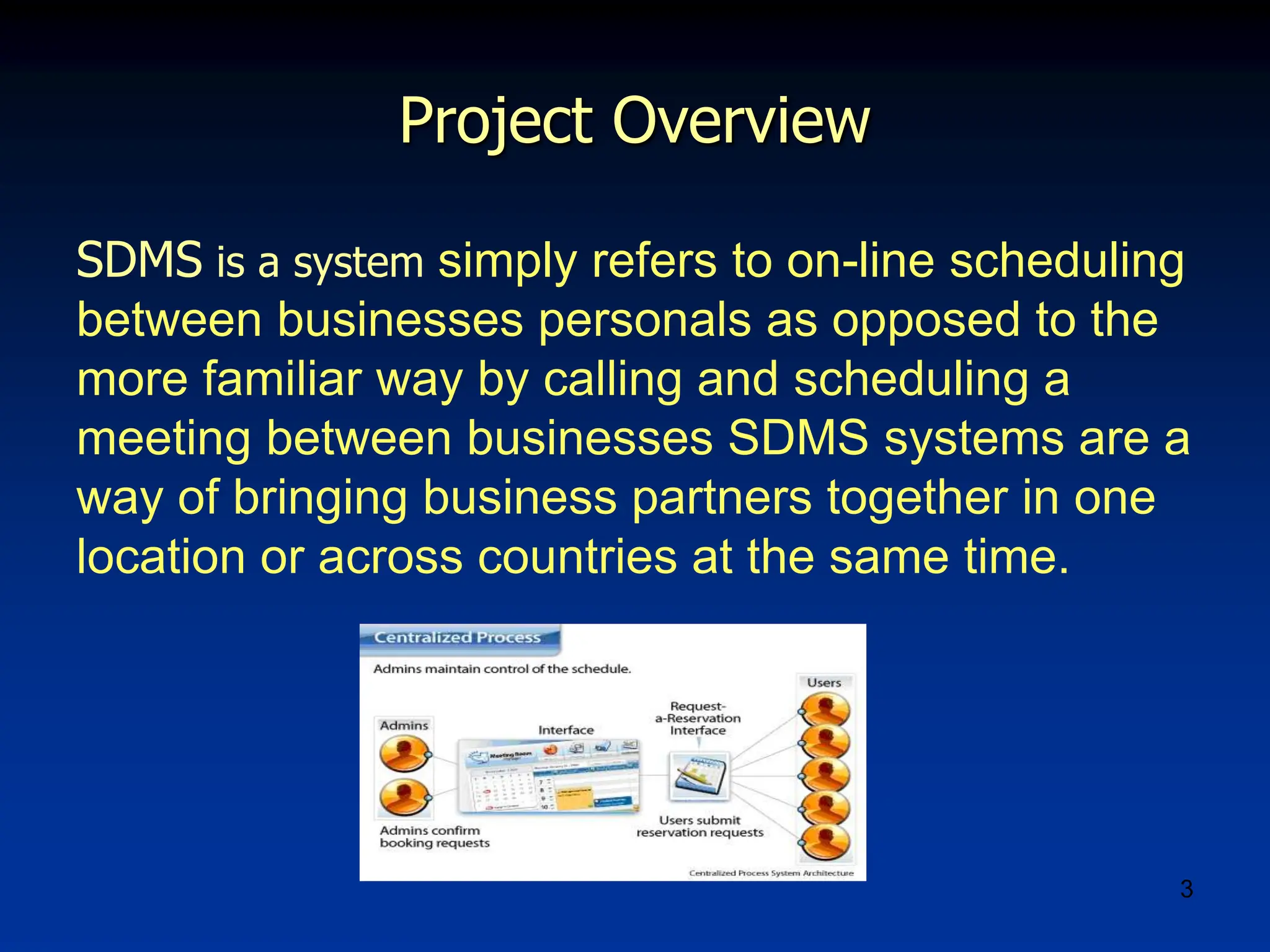
![12
Statechart
Diagram
Initiate System
Wait Input
Event
Terminate System
Ready
Maintain Database
do/ Show adm menu
Hold Meeting
do/ HoldMeeting
do/ MonitorMeeting
Main User Interface
do/ Show user menu
ManageMeet
ingRecord
ManageRe
source
Manage
Account
ModifyAc
count
Initiator User Interface
do/ Show initiator menu
Attendee User Interface
do/ Show attendee menu
Reserve
Meeting
Schedule Meeting
Notify Participant
Handle
Conflict
Schedule
Meeting
Cancel
Meeting
Schedule
Complete
Save Meetinf
Record Upper Menu
Input Attendee
Information
[Using-Resource changed]
[ Select Reserve ]
Modify Meeting
Information
[ Select Modify ]
Notify Participant
Handle
Conflict
Schedule
Meeting
[Conflict occurs]
Need New Info
[ Need Info ]
Cancel
Meeting
[Time out]
Schedule
Complete
[Success]
Save Meetinf
Record
[ Select Modify ]
[ Select Initiator ]
[ Select Attendee ]
Logout
Show
Result
[Others]
Meeting ends
[ Select Record ]
[ Select Resource ]
[ Select Account ]
Logout
Upper Menu
[ Logined ]
[ Unlogined ]
Shut down
[ Timer event for starting meeting ]
[ Administrator Login ]
[ User Login ]
[ Timer event for scheduling meeting ]](https://image.slidesharecdn.com/sdms-240517081256-d81c6602/75/sdms-electric-power-generation-system-report-on-engg-12-2048.jpg)