This document provides information on various SAP security concepts and configuration steps, including:
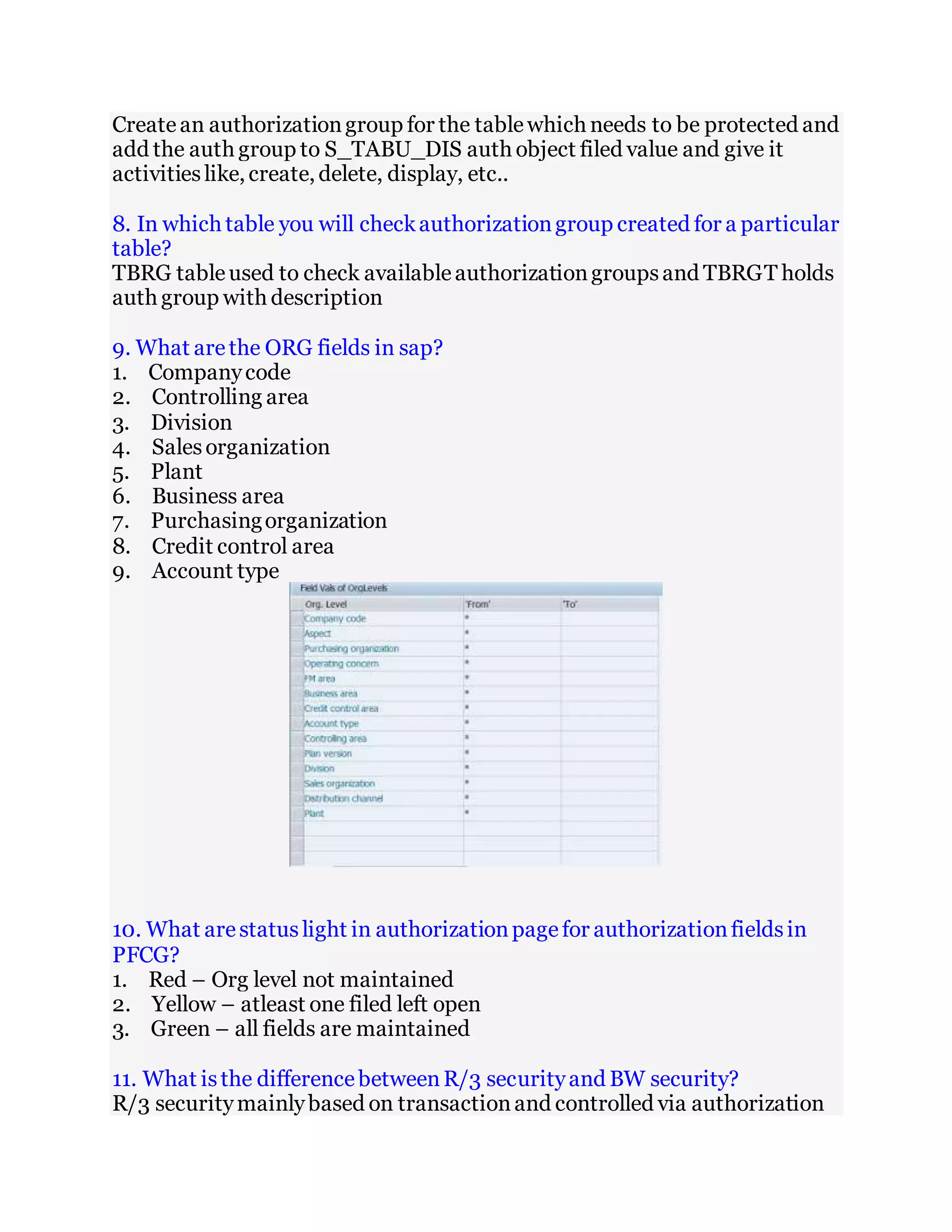
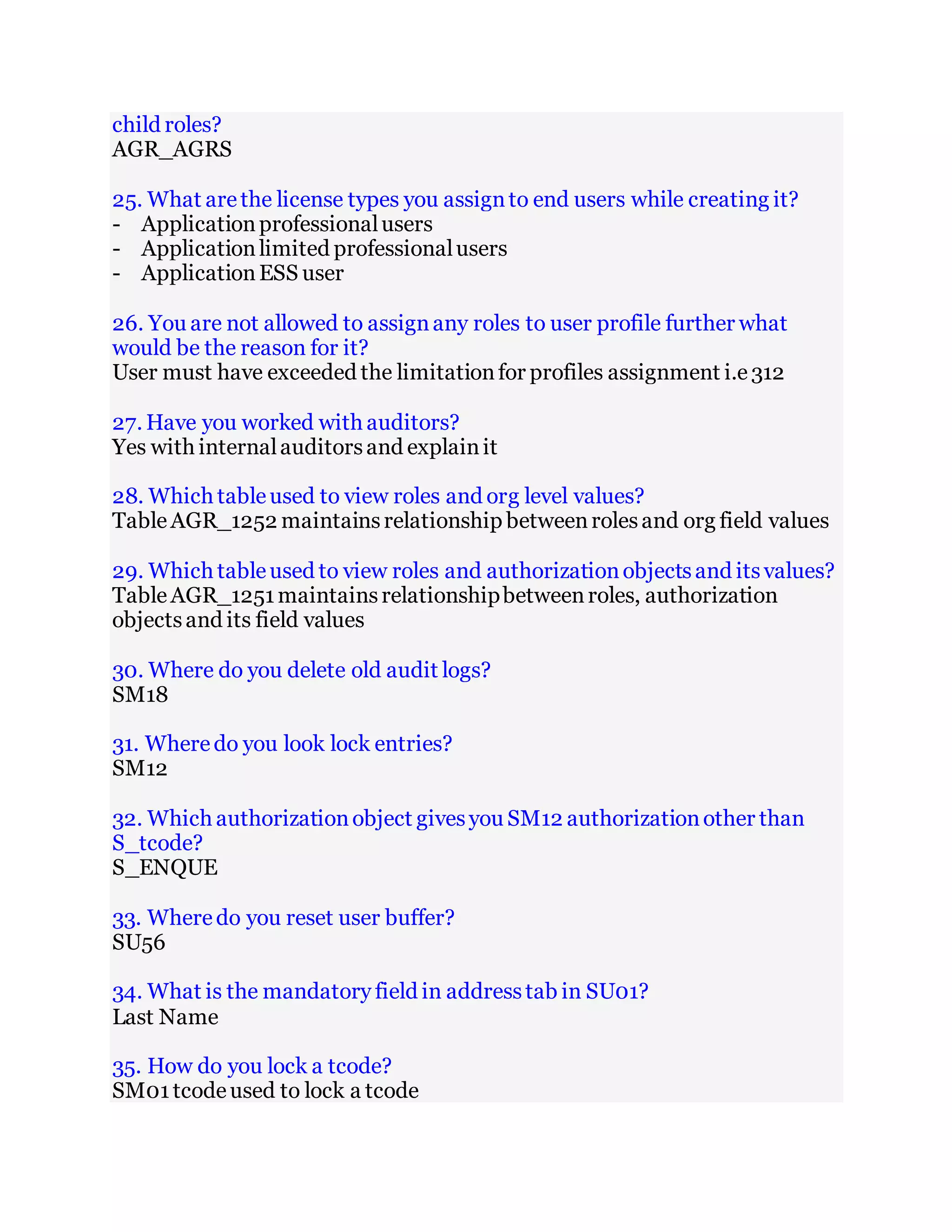
1. How to create reference user types, authorization objects, organizational fields, extract user emails, check role relationships, create authorization groups, restrict table access, check authorization groups and fields.
2. The differences between R/3 and BW security models and key authorization objects for BW queries.
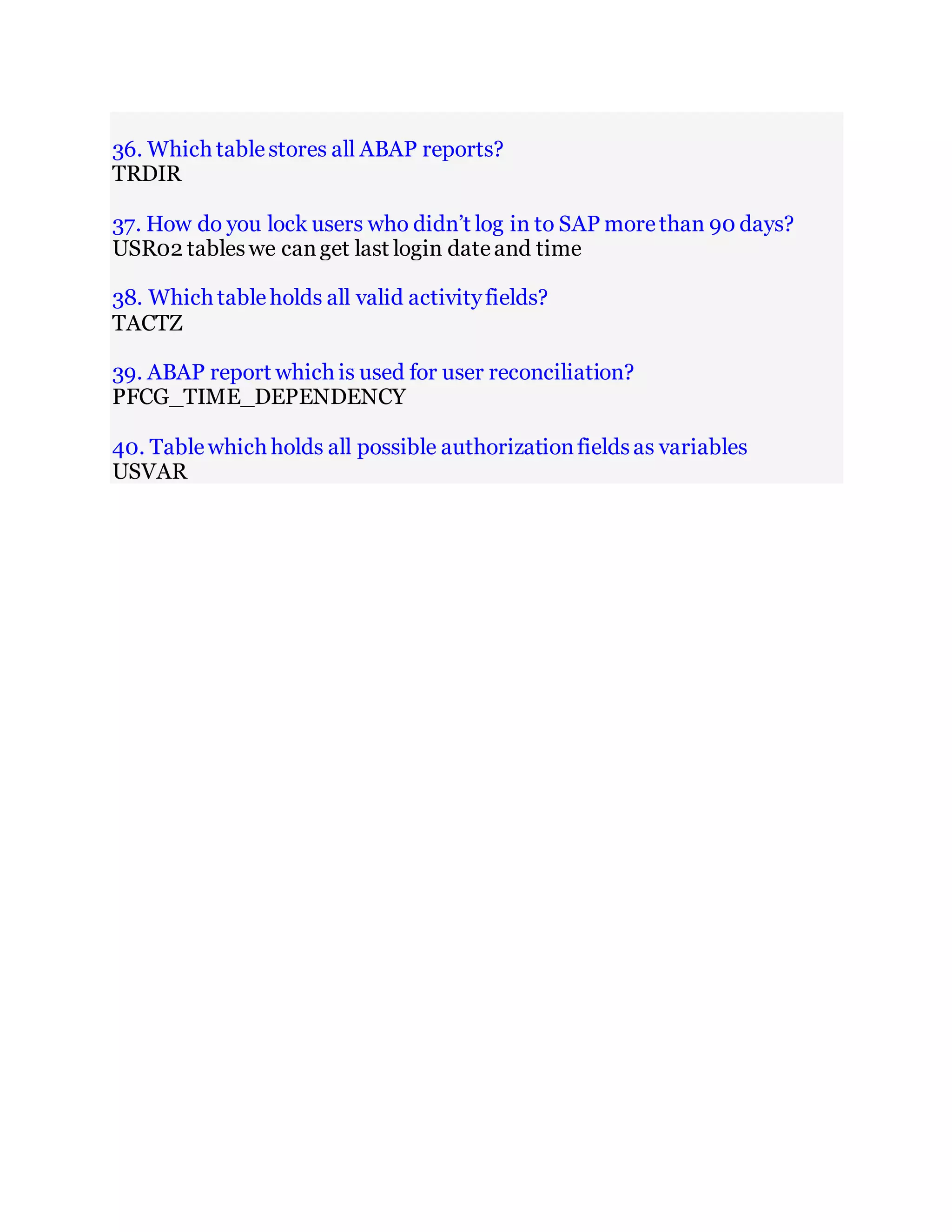
3. How to create custom transactions, transport requests, background jobs, work with auditors, delete old logs, lock users, and reconcile users.
4. The tables that store role assignments, transaction authorizations, ABAP reports, activity fields, and authorization fields.