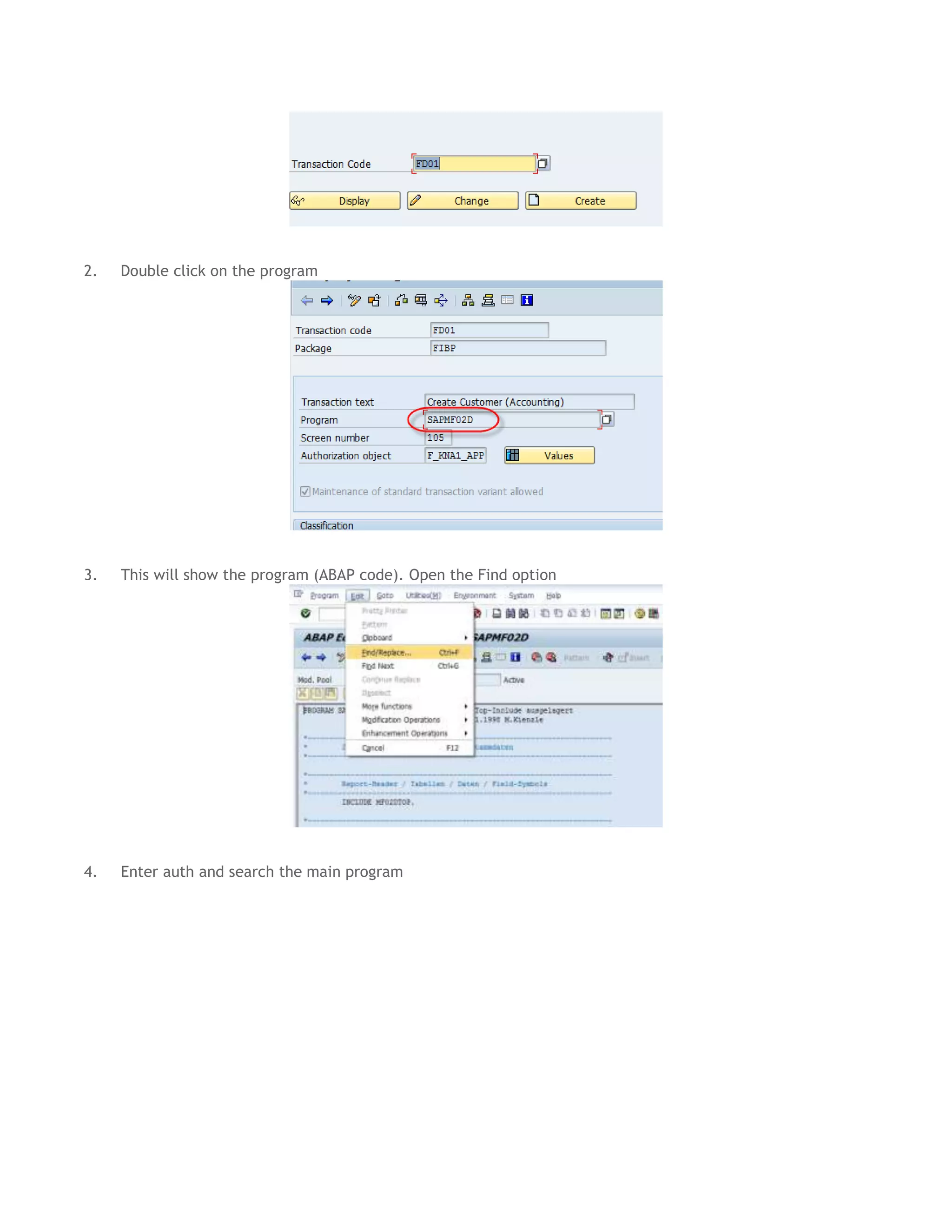
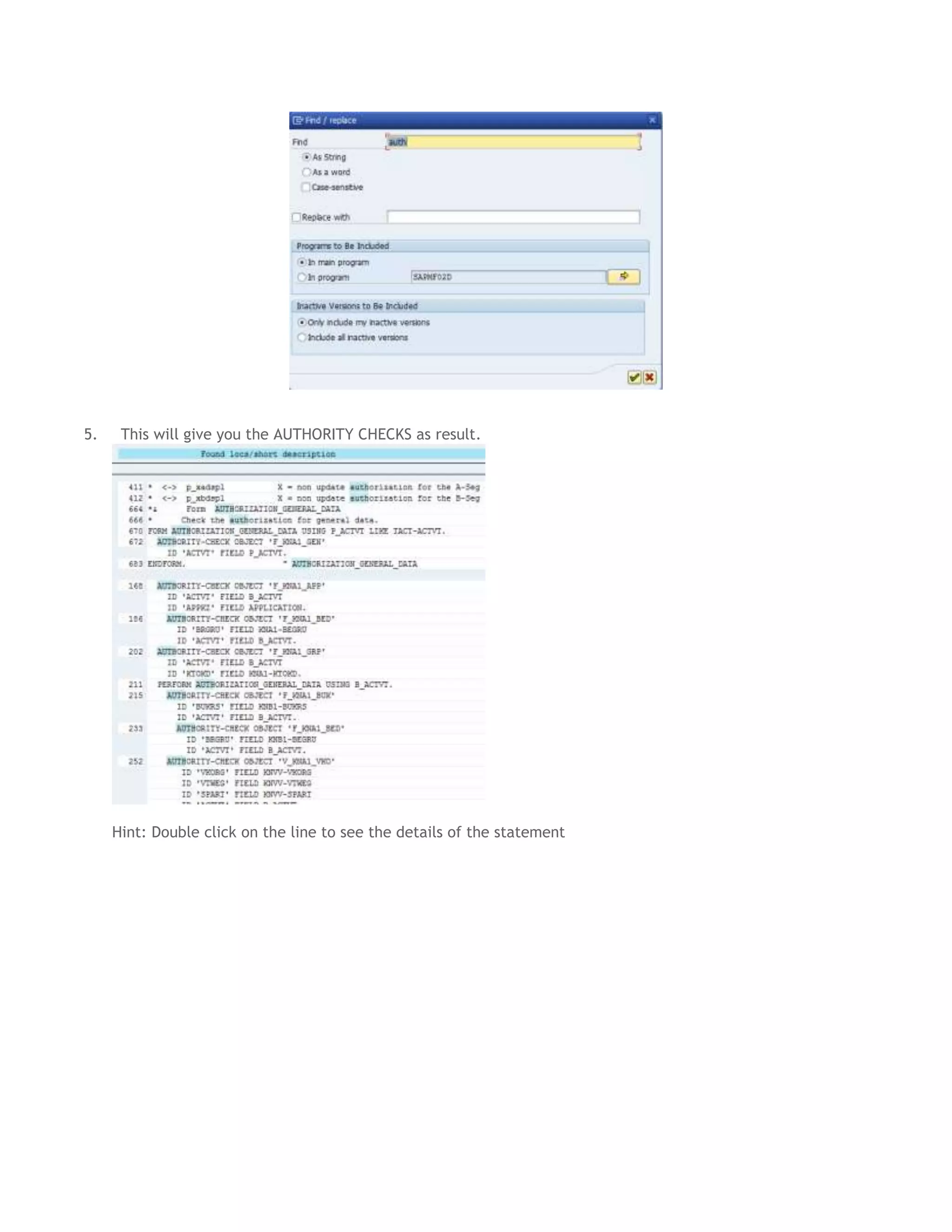
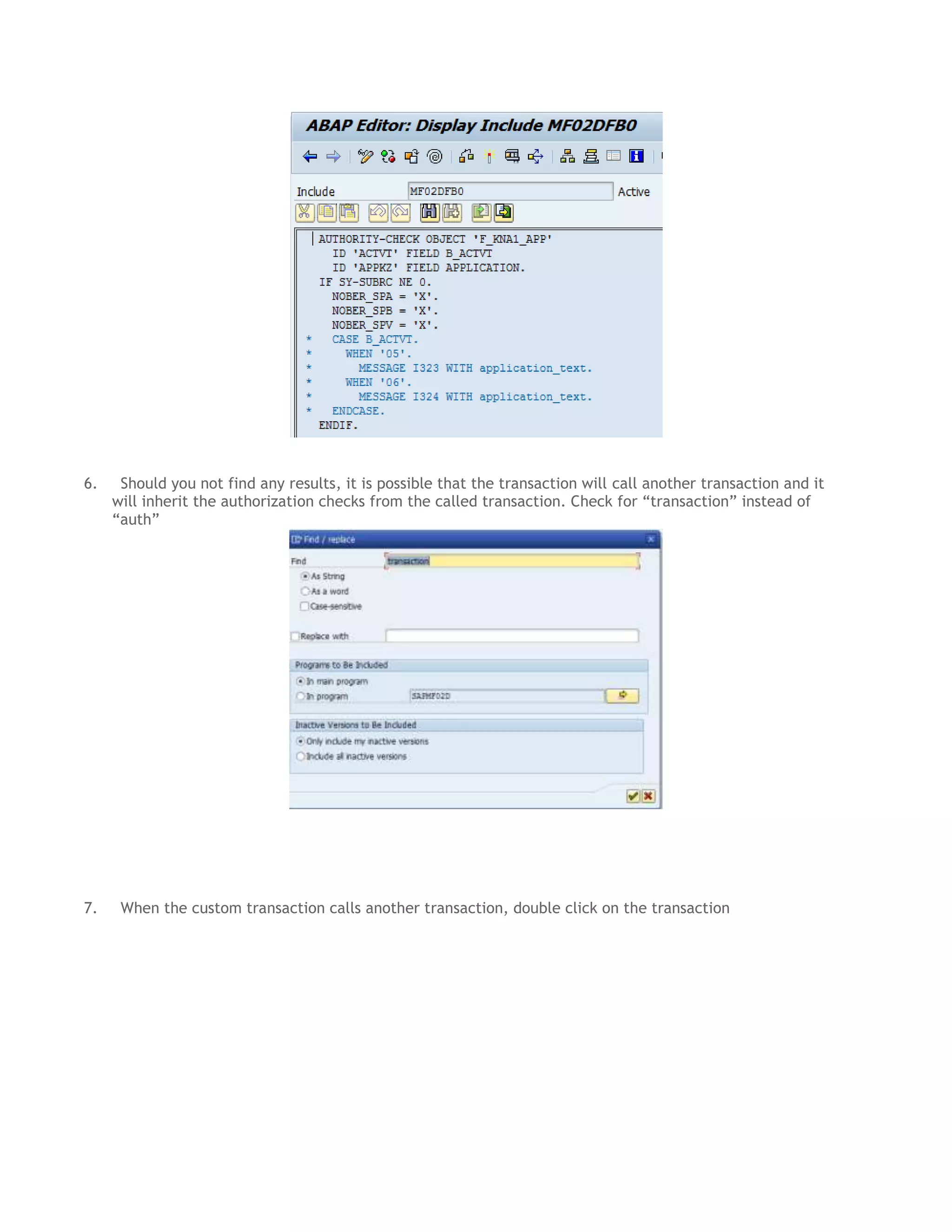
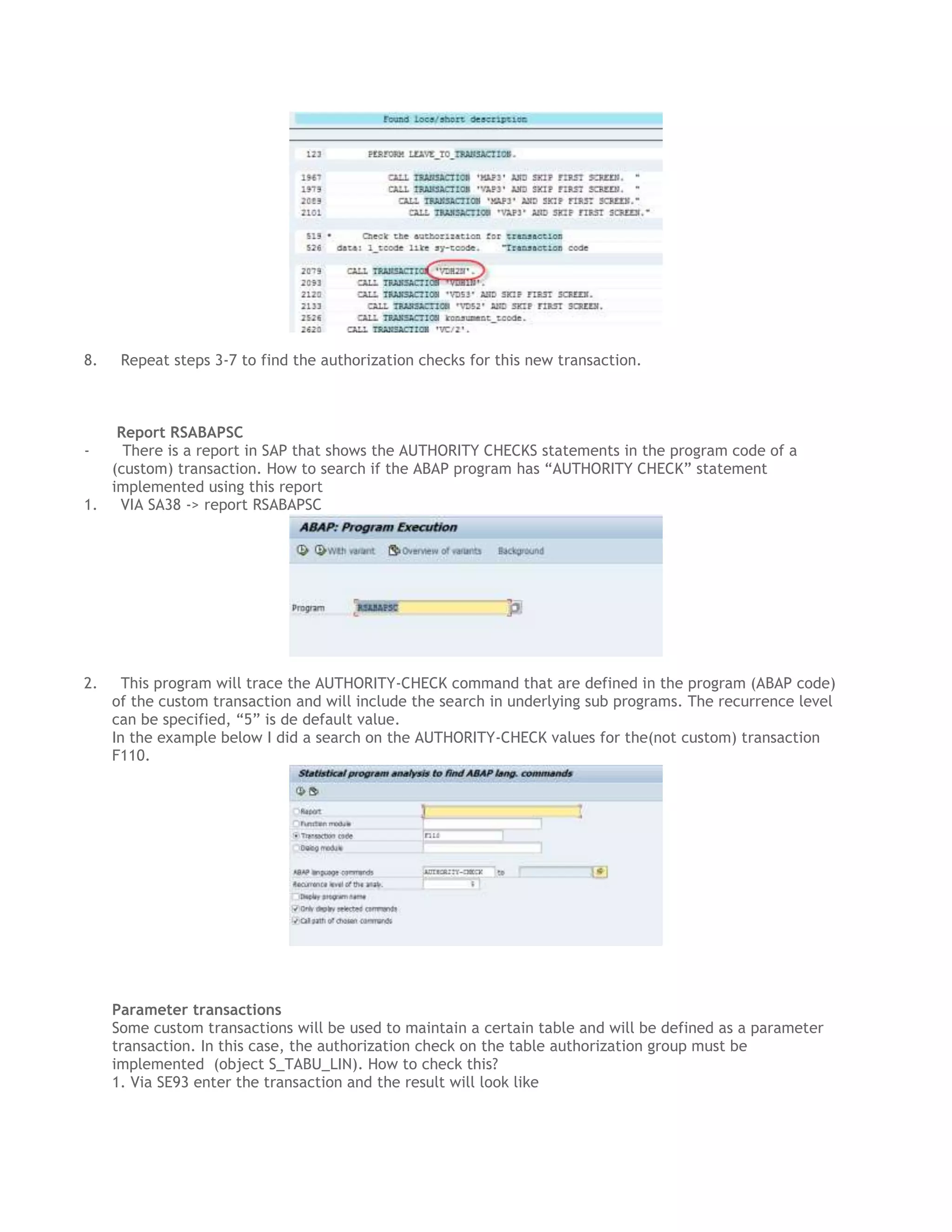
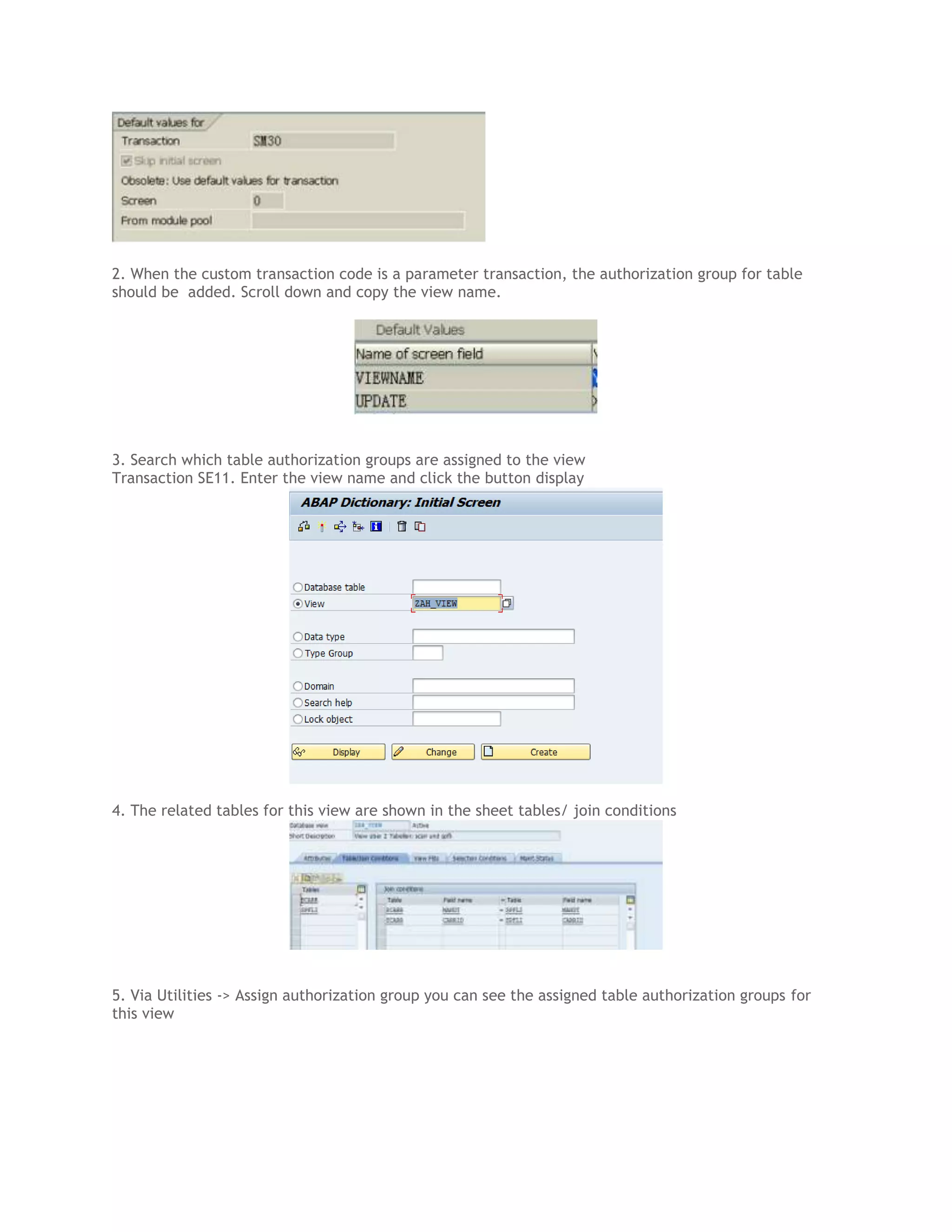
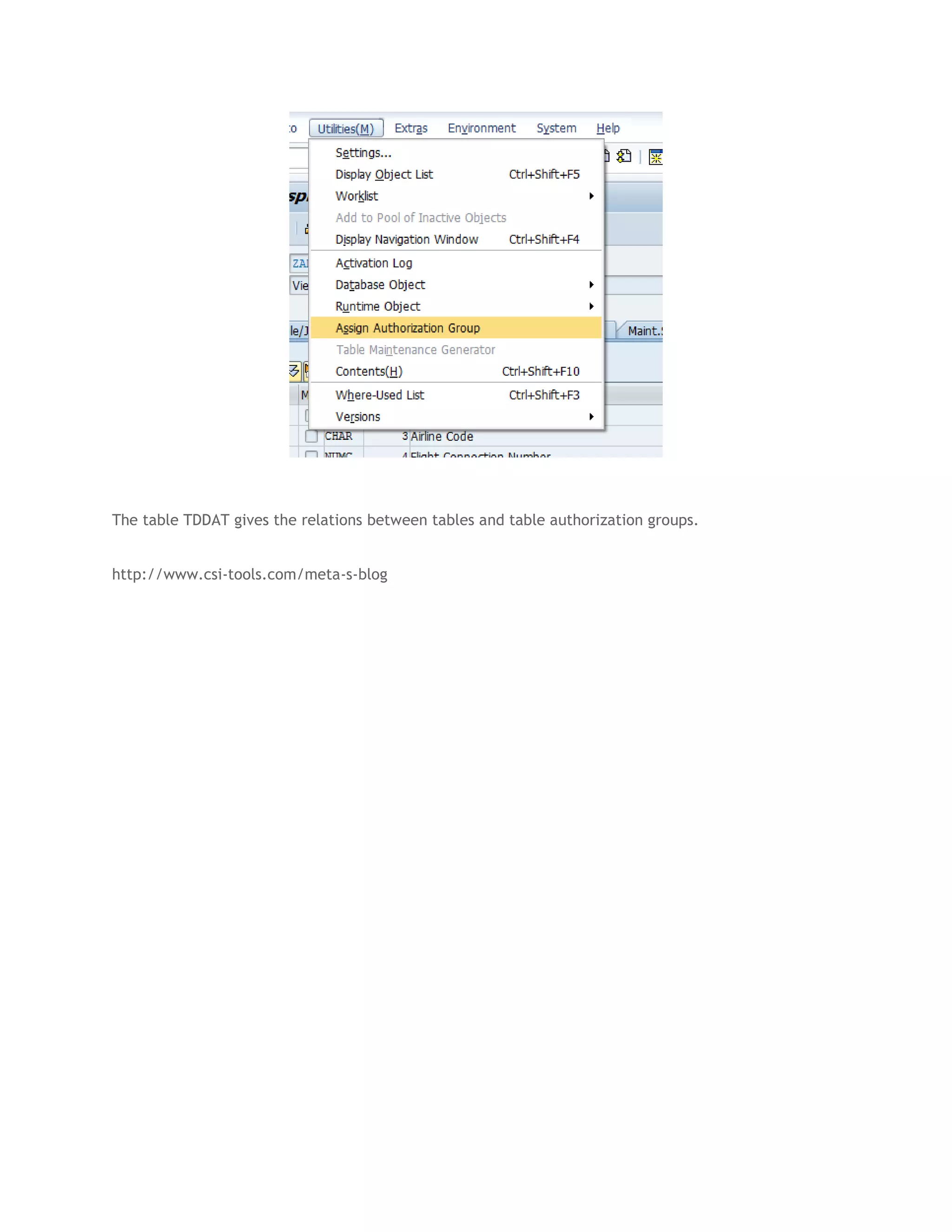
This document discusses how to identify authorization checks for custom transactions in SAP systems in order to include critical custom transactions in the rule set for authorization auditing. It provides instructions for searching the transaction table (TSTC) to find custom transactions, checking transaction programs for AUTHORITY CHECK statements using transaction SE93 or report RSABAPSC, and identifying table authorization groups for parameter transactions by analyzing transaction views. The goal is to fine tune the GRC filter set to include checks for relevant custom transactions.