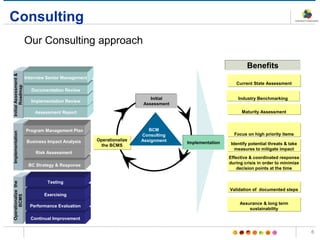
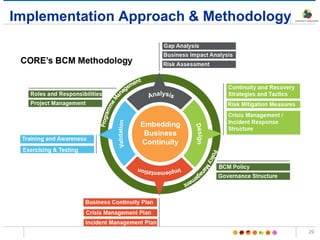
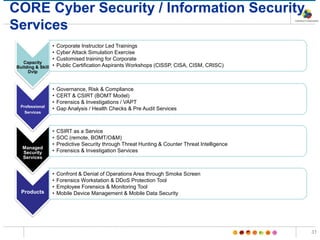
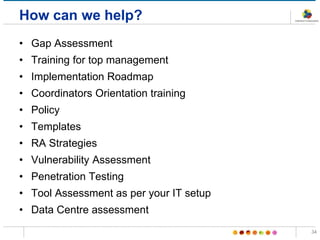
The document outlines the BCM framework and consulting services presented at the 8th ME Business & IT Resilience Summit, emphasizing the importance of business continuity management (BCM) and crisis management for member organizations affiliated with SAMA in Saudi Arabia. It details the requirements for implementing BCM practices, roles and responsibilities, necessary training courses, and strategies for crisis and disaster recovery. The framework aims to ensure effective response to disruptions, continuous improvement, and senior management accountability in maintaining operational resilience.