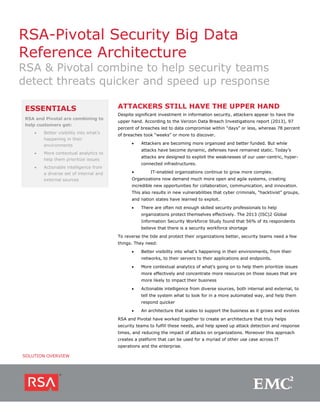
RSA-Pivotal Security Big Data Reference Architecture
•
0 likes•1,114 views
E
EMCThis paper talks about how customers can use RSA and Pivotal to get better visibility into their environments, more context to help them prioritize issues, and actionable intelligence from a diverse set of sources
Report
Share
Report
Share
Download to read offline
Recommended
Enterprise Security and User Behavior Analytics

Splunk Enterprise Security 4.5 provides security information and event management (SIEM) and a security intelligence platform. It includes features like adaptive response to extend analytics-driven decisions and automation, and glass tables to enhance visual analytics. Glass tables allow security teams to create custom visualizations that reflect their workflows and gain visibility across their security ecosystem. The update also includes improvements to detection, investigation, and response times through automation and correlation searches.
SplunkLive! Customer Presentation – HCA

- Currently they ingest over 2 billion events per day into Splunk and use it for security, performance, and infrastructure monitoring across many teams, but plan to expand analytics through machine learning, threat intelligence integration, and focus on more proactive security logs.
User and entity behavior analytics: building an effective solution

This presentation provides an overview of UEBA space and gives insights into the core components of an effective solution, such as relevant Threat and Attack Scenarios, Data Sources, and various Analytic techniques. This was presented during ISSA-UK chapter meeting.
November 2013 HUG: Cyber Security with Hadoop

Narus provides cybersecurity analytics and solutions to help customers gain visibility into their network traffic and security threats. Their technology fuses network, semantic, and user data to provide comprehensive security insights. Key challenges include increasing data volumes and diversity of network deployments. Narus addresses these with an integrated analytics platform that uses machine learning to extract metadata and detect anomalies in real-time and over long periods of stored data. Their hybrid approach leverages both Hadoop/Hbase and relational databases for scalable analytics and business intelligence.
Novetta Cyber Analytics Product Brochure Final_Web_4.20.2015

Novetta Cyber Analytics is an advanced network traffic analytics solution that provides security analysts with comprehensive and near real-time visibility of network traffic. It collects and processes packet capture data from sensors across the network. It allows analysts to run queries against metadata representing petabytes of network traffic and receive answers within seconds. This enables rapid alert triage, incident response, and network hunting. It substantially increases the efficiency and effectiveness of security teams.
UEBA

IntroSpect User and Entity Behavior Analytics (UEBA) uses AI-based machine learning to spot changes in user behavior that often indicate inside attacks that have evaded perimeter defenses. Security teams are armed with insights into malicious, compromised or negligent users, systems and devices – cutting off the threat before it does damage.
Sqrrl Enterprise: Big Data Security Analytics Use Case

Organizations are utilizing Sqrrl Enterprise to securely integrate vast amounts of multi-structured data (e.g., tens of petabytes) onto a single Big Data platform and then are building real-time applications using this data and Sqrrl Enterprise’s analytical interfaces. The secure integration is enabled by Accumulo’s innovative cell-level security capabilities and Sqrrl Enterprise’s security extensions, such as encryption.
Enterprise Security featuring UBA

This document provides an overview of Splunk Enterprise Security and User Behavior Analytics (UBA). It discusses the evolving threat landscape and how Splunk has been recognized as a leader in security information and event management. The document outlines Splunk's analytics-driven security capabilities for threat detection, investigation, and response. It also describes new features for reducing storage costs, enhancing investigations, extending analytics with automation, and improving threat detection with UBA. The document promotes a quick UBA demo and mentions happy hour.
Recommended
Enterprise Security and User Behavior Analytics

Splunk Enterprise Security 4.5 provides security information and event management (SIEM) and a security intelligence platform. It includes features like adaptive response to extend analytics-driven decisions and automation, and glass tables to enhance visual analytics. Glass tables allow security teams to create custom visualizations that reflect their workflows and gain visibility across their security ecosystem. The update also includes improvements to detection, investigation, and response times through automation and correlation searches.
SplunkLive! Customer Presentation – HCA

- Currently they ingest over 2 billion events per day into Splunk and use it for security, performance, and infrastructure monitoring across many teams, but plan to expand analytics through machine learning, threat intelligence integration, and focus on more proactive security logs.
User and entity behavior analytics: building an effective solution

This presentation provides an overview of UEBA space and gives insights into the core components of an effective solution, such as relevant Threat and Attack Scenarios, Data Sources, and various Analytic techniques. This was presented during ISSA-UK chapter meeting.
November 2013 HUG: Cyber Security with Hadoop

Narus provides cybersecurity analytics and solutions to help customers gain visibility into their network traffic and security threats. Their technology fuses network, semantic, and user data to provide comprehensive security insights. Key challenges include increasing data volumes and diversity of network deployments. Narus addresses these with an integrated analytics platform that uses machine learning to extract metadata and detect anomalies in real-time and over long periods of stored data. Their hybrid approach leverages both Hadoop/Hbase and relational databases for scalable analytics and business intelligence.
Novetta Cyber Analytics Product Brochure Final_Web_4.20.2015

Novetta Cyber Analytics is an advanced network traffic analytics solution that provides security analysts with comprehensive and near real-time visibility of network traffic. It collects and processes packet capture data from sensors across the network. It allows analysts to run queries against metadata representing petabytes of network traffic and receive answers within seconds. This enables rapid alert triage, incident response, and network hunting. It substantially increases the efficiency and effectiveness of security teams.
UEBA

IntroSpect User and Entity Behavior Analytics (UEBA) uses AI-based machine learning to spot changes in user behavior that often indicate inside attacks that have evaded perimeter defenses. Security teams are armed with insights into malicious, compromised or negligent users, systems and devices – cutting off the threat before it does damage.
Sqrrl Enterprise: Big Data Security Analytics Use Case

Organizations are utilizing Sqrrl Enterprise to securely integrate vast amounts of multi-structured data (e.g., tens of petabytes) onto a single Big Data platform and then are building real-time applications using this data and Sqrrl Enterprise’s analytical interfaces. The secure integration is enabled by Accumulo’s innovative cell-level security capabilities and Sqrrl Enterprise’s security extensions, such as encryption.
Enterprise Security featuring UBA

This document provides an overview of Splunk Enterprise Security and User Behavior Analytics (UBA). It discusses the evolving threat landscape and how Splunk has been recognized as a leader in security information and event management. The document outlines Splunk's analytics-driven security capabilities for threat detection, investigation, and response. It also describes new features for reducing storage costs, enhancing investigations, extending analytics with automation, and improving threat detection with UBA. The document promotes a quick UBA demo and mentions happy hour.
Getting Started with Splunk Enterprise Hands-On

Here’s your chance to get hands-on with Splunk for the first time! Bring your laptop, and we’ll go through a simple install of Splunk. Then we’ll load some sample data, and see Splunk in action. At the end of this session you’ll have a hands-on understanding of the pieces that make up the Splunk Platform, how it works, and how it fits in the landscape of Big Data. We’ll share practical examples that differentiate Splunk while demonstrating how to gain quick time to value.
HP ArcSight Demonstrating ROI For a SIEM Solution

This document discusses how SIEM technology can provide a return on investment through cost savings and avoidance. It provides examples from various organizations that implemented SIEM solutions. These organizations were able to reduce costs through automating security tasks, preventing infrastructure expansion, avoiding compliance penalties, and reducing losses. The examples show organizations achieving payback periods ranging from less than a week to 6 months. The document concludes that SIEM benefits far outweigh acquisition costs, with expenses usually paid off within a few weeks or months through hard cost savings and soft benefits like improved security awareness.
Document fingerprinting in Microsoft 365 Compliance

Built directly from the documentation! https://docs.microsoft.com/en-us/microsoft-365/compliance/document-fingerprinting?view=o365-worldwide
Hands-On Security Breakout Session- Disrupting the Kill Chain

The document discusses a security investigation demo using Splunk software to disrupt the cyber kill chain. It begins with detecting threat intelligence related events across multiple data sources for a specific IP address. Further investigation using endpoint data from Microsoft Sysmon reveals network connections and process information. This traces the suspicious activity back through parent processes to identify a vulnerable PDF reader application exploited by opening a weaponized file delivered via email phishing. Additional context from web logs shows the file was obtained through a brute force attack on the company's website. The investigation is then able to connect events across various data sources to fully map out the adversary's actions.
Splunk Ninjas: New Features and Search Dojo

In addition to seeing the latest features in Splunk Enterprise, learn some of the top commands that will solve most search and analytics needs. Ninja’s can use these blindfolded. New features will be demonstrated in the following areas: TCO and Performance Improvements, Platform Management and New Interactive Visualizations.
Applying Auto-Data Classification Techniques for Large Data Sets

In the current data security landscape, large volumes of data are being created across the enterprise. Manual techniques to inventory and classify data makes it a tedious and expensive activity. To create a time and cost effective implementation of security and access controls, it becomes key to automate the data classification process.
(Source: RSA USA 2016-San Francisco)
Operational Security Intelligence Breakout Session

This document discusses operationalizing security intelligence through Splunk. It begins with an overview of security intelligence and what it aims to provide organizations. It then discusses requirements for security intelligence like risk-based analytics, context and intelligence, and connecting data and people. The presentation includes two demos of Splunk capabilities for security use cases. It promotes attending future tech talks and Splunk conferences to learn more.
Splunk Discovery: Warsaw 2018 - Getting Data In

Presented at Splunk Discovery Warsaw 2018:
What Data can Splunk Ingest?
How to Ingest Data
Apps and Add-ons
Demo
Using Splunk for Information Security

This document provides an overview of a presentation on security monitoring and analytics using Splunk. The presentation covers using Splunk Enterprise for security operations like alert management and incident response. It also covers using Splunk User Behavior Analytics to detect anomalies and threats using machine learning. The presentation highlights new features in Splunk Enterprise Security 4.1 like prioritizing investigations and expanded threat intelligence, and new features in Splunk UBA 2.2 like enhanced security analytics and custom threat modeling. It demonstrates integrating UBA results into the Splunk Enterprise Security workflow for faster investigation of advanced threats.
Splunk Enterprise for InfoSec Hands-On Breakout Session

This document outlines an agenda for a Splunk Enterprise for InfoSec Hands-On training session covering web attacks, lateral movement, and DNS exfiltration. The introductory section provides an overview of Splunk and how it can be used to collect, store, and analyze machine data. Examples of SQL injection detection techniques and analyzing network traffic to detect lateral movement are discussed. DNS exfiltration is also covered, including using entropy calculations and subdomain analysis to identify potential exfiltration in DNS query logs.
Splunk for Enterprise Security featuring User Behavior Analytics

This session will review Splunk’s two premium solutions - Splunk Enterprise Security (ES) is Splunk's award-winning security intelligence solution that brings immediate value for continuous monitoring across SOC and incident response environments. Splunk UBA is a new technology that applies unsupervised machine learning and data science to solving one of the biggest problems in information security today: insider threat. You’ll learn how Splunk UBA works in tandem with ES, or third-party data sources, to bring significant automated analytical power to your SOC and Incident Response teams.
Splunking configfiles 20211208_daniel_wilson

Splunk SF Bay Area Usergroup meeting December 8, 2021: Splunking config files, presentation by Daniel Wilson
ExtraHop Splunk datasheet

Combine your wire data with machine data for complete IT Operational Intelligence.
Learn more at https://www.extrahop.com.
Cloudera Federal Forum 2014: EzBake, the DoDIIS App Engine

General Manager of 42Six, a CSC Company, Matt Carroll, shares EzBake - a secure apps engine for DoDIIS.
Threat Hunting with Elastic at SpectorOps: Welcome to HELK

This document provides an overview and agenda for the Elastic Tour 2018 conference. It introduces the speaker, Cyb3rWard0g, and outlines their background and expertise in threat hunting. The agenda covers topics like threat hunting techniques and data, the role of threat hunters, integrating threat hunting with SIEMs, and pre-hunt activities. It also introduces HELK, an open source project that extends the Elastic Stack with advanced analytics capabilities to empower threat hunters. Key components of HELK include Apache Spark, Elasticsearch, and Jupyter notebooks. The document discusses how these tools can help with tasks like threat modeling, data analysis, and developing threat hunting playbooks. It concludes by discussing potential future directions for the HELK
Fluency - Next Generation Incident Response Utilizing Big Data Analytics Over...

Fluency’s vision empowers decisions through a holistic view of the network, fusing the ability to monitor traffic with SIEM-like capability. Fluency provides clarity & measurable value by leveraging Big Data & Packet Monitoring to provide more information, not less; additionally Fluency is open & integrates with existing deployed security solutions protecting investments made while providing measurable, complementary value & an extremely quick ROI from the day implemented.
****Fluency In The Press:
- RSA Selected as 1 of 9 Most Innovative Security Products of 2015 (Only Breach Offering Selected) - 04/15
- CRN Selected #6 of the 10 Coolest Security Startups of 2015 - 07/15
- CRN Selected as 1 of the Top 25 Disrupters (Across all IT Disciplines) of 2015 - 08/15
SplunkLive! Munich 2018: Data Onboarding Overview

Presented at SplunkLive! Munich 2018:
- Splunk Data Collection Architecture
- Apps & Technology Add-ons
- Demons / Examples
- Best Practices
- Resources
Getting Started with Splunk Breakout Session

Splunk is a software platform that allows users to search, monitor, and analyze machine-generated big data for security, IT and business intelligence. It collects data from sources like servers, networks, sensors and applications. Splunk can scale from analyzing data from a single computer to very large enterprises handling terabytes of data per day. It provides real-time operational intelligence through universal data ingestion, schema-on-the-fly indexing, and an intuitive search process.
Clinical and Business Analytics - HIMSS 2015

By passively analyzing your wire data, ExtraHop provides deep visibility into HL7 messages, Citrix performance, EHR behavior, ICD-10 conversion, and more.
Proactive monitoring and remediation
Optimization and continuous improvement
Pervasive security monitoring and compliance
Clinical and operations analytics
End-to-End Security Analytics with the Elastic Stack

Interested in staying ahead of the adversary in a shifting security landscape? Learn how to create a centralized security analytics platform with the speed and scale you need for ad hoc analysis during threat detection and hunting exercises.
Power View from the Data Visualisation Perspective

Speaker: Jen Stirrup
Download SQL Server 2012: http://www.microsoft.com/sqlserver/en/us/get-sql-server/try-it.aspx
More Related Content
What's hot
Getting Started with Splunk Enterprise Hands-On

Here’s your chance to get hands-on with Splunk for the first time! Bring your laptop, and we’ll go through a simple install of Splunk. Then we’ll load some sample data, and see Splunk in action. At the end of this session you’ll have a hands-on understanding of the pieces that make up the Splunk Platform, how it works, and how it fits in the landscape of Big Data. We’ll share practical examples that differentiate Splunk while demonstrating how to gain quick time to value.
HP ArcSight Demonstrating ROI For a SIEM Solution

This document discusses how SIEM technology can provide a return on investment through cost savings and avoidance. It provides examples from various organizations that implemented SIEM solutions. These organizations were able to reduce costs through automating security tasks, preventing infrastructure expansion, avoiding compliance penalties, and reducing losses. The examples show organizations achieving payback periods ranging from less than a week to 6 months. The document concludes that SIEM benefits far outweigh acquisition costs, with expenses usually paid off within a few weeks or months through hard cost savings and soft benefits like improved security awareness.
Document fingerprinting in Microsoft 365 Compliance

Built directly from the documentation! https://docs.microsoft.com/en-us/microsoft-365/compliance/document-fingerprinting?view=o365-worldwide
Hands-On Security Breakout Session- Disrupting the Kill Chain

The document discusses a security investigation demo using Splunk software to disrupt the cyber kill chain. It begins with detecting threat intelligence related events across multiple data sources for a specific IP address. Further investigation using endpoint data from Microsoft Sysmon reveals network connections and process information. This traces the suspicious activity back through parent processes to identify a vulnerable PDF reader application exploited by opening a weaponized file delivered via email phishing. Additional context from web logs shows the file was obtained through a brute force attack on the company's website. The investigation is then able to connect events across various data sources to fully map out the adversary's actions.
Splunk Ninjas: New Features and Search Dojo

In addition to seeing the latest features in Splunk Enterprise, learn some of the top commands that will solve most search and analytics needs. Ninja’s can use these blindfolded. New features will be demonstrated in the following areas: TCO and Performance Improvements, Platform Management and New Interactive Visualizations.
Applying Auto-Data Classification Techniques for Large Data Sets

In the current data security landscape, large volumes of data are being created across the enterprise. Manual techniques to inventory and classify data makes it a tedious and expensive activity. To create a time and cost effective implementation of security and access controls, it becomes key to automate the data classification process.
(Source: RSA USA 2016-San Francisco)
Operational Security Intelligence Breakout Session

This document discusses operationalizing security intelligence through Splunk. It begins with an overview of security intelligence and what it aims to provide organizations. It then discusses requirements for security intelligence like risk-based analytics, context and intelligence, and connecting data and people. The presentation includes two demos of Splunk capabilities for security use cases. It promotes attending future tech talks and Splunk conferences to learn more.
Splunk Discovery: Warsaw 2018 - Getting Data In

Presented at Splunk Discovery Warsaw 2018:
What Data can Splunk Ingest?
How to Ingest Data
Apps and Add-ons
Demo
Using Splunk for Information Security

This document provides an overview of a presentation on security monitoring and analytics using Splunk. The presentation covers using Splunk Enterprise for security operations like alert management and incident response. It also covers using Splunk User Behavior Analytics to detect anomalies and threats using machine learning. The presentation highlights new features in Splunk Enterprise Security 4.1 like prioritizing investigations and expanded threat intelligence, and new features in Splunk UBA 2.2 like enhanced security analytics and custom threat modeling. It demonstrates integrating UBA results into the Splunk Enterprise Security workflow for faster investigation of advanced threats.
Splunk Enterprise for InfoSec Hands-On Breakout Session

This document outlines an agenda for a Splunk Enterprise for InfoSec Hands-On training session covering web attacks, lateral movement, and DNS exfiltration. The introductory section provides an overview of Splunk and how it can be used to collect, store, and analyze machine data. Examples of SQL injection detection techniques and analyzing network traffic to detect lateral movement are discussed. DNS exfiltration is also covered, including using entropy calculations and subdomain analysis to identify potential exfiltration in DNS query logs.
Splunk for Enterprise Security featuring User Behavior Analytics

This session will review Splunk’s two premium solutions - Splunk Enterprise Security (ES) is Splunk's award-winning security intelligence solution that brings immediate value for continuous monitoring across SOC and incident response environments. Splunk UBA is a new technology that applies unsupervised machine learning and data science to solving one of the biggest problems in information security today: insider threat. You’ll learn how Splunk UBA works in tandem with ES, or third-party data sources, to bring significant automated analytical power to your SOC and Incident Response teams.
Splunking configfiles 20211208_daniel_wilson

Splunk SF Bay Area Usergroup meeting December 8, 2021: Splunking config files, presentation by Daniel Wilson
ExtraHop Splunk datasheet

Combine your wire data with machine data for complete IT Operational Intelligence.
Learn more at https://www.extrahop.com.
Cloudera Federal Forum 2014: EzBake, the DoDIIS App Engine

General Manager of 42Six, a CSC Company, Matt Carroll, shares EzBake - a secure apps engine for DoDIIS.
Threat Hunting with Elastic at SpectorOps: Welcome to HELK

This document provides an overview and agenda for the Elastic Tour 2018 conference. It introduces the speaker, Cyb3rWard0g, and outlines their background and expertise in threat hunting. The agenda covers topics like threat hunting techniques and data, the role of threat hunters, integrating threat hunting with SIEMs, and pre-hunt activities. It also introduces HELK, an open source project that extends the Elastic Stack with advanced analytics capabilities to empower threat hunters. Key components of HELK include Apache Spark, Elasticsearch, and Jupyter notebooks. The document discusses how these tools can help with tasks like threat modeling, data analysis, and developing threat hunting playbooks. It concludes by discussing potential future directions for the HELK
Fluency - Next Generation Incident Response Utilizing Big Data Analytics Over...

Fluency’s vision empowers decisions through a holistic view of the network, fusing the ability to monitor traffic with SIEM-like capability. Fluency provides clarity & measurable value by leveraging Big Data & Packet Monitoring to provide more information, not less; additionally Fluency is open & integrates with existing deployed security solutions protecting investments made while providing measurable, complementary value & an extremely quick ROI from the day implemented.
****Fluency In The Press:
- RSA Selected as 1 of 9 Most Innovative Security Products of 2015 (Only Breach Offering Selected) - 04/15
- CRN Selected #6 of the 10 Coolest Security Startups of 2015 - 07/15
- CRN Selected as 1 of the Top 25 Disrupters (Across all IT Disciplines) of 2015 - 08/15
SplunkLive! Munich 2018: Data Onboarding Overview

Presented at SplunkLive! Munich 2018:
- Splunk Data Collection Architecture
- Apps & Technology Add-ons
- Demons / Examples
- Best Practices
- Resources
Getting Started with Splunk Breakout Session

Splunk is a software platform that allows users to search, monitor, and analyze machine-generated big data for security, IT and business intelligence. It collects data from sources like servers, networks, sensors and applications. Splunk can scale from analyzing data from a single computer to very large enterprises handling terabytes of data per day. It provides real-time operational intelligence through universal data ingestion, schema-on-the-fly indexing, and an intuitive search process.
Clinical and Business Analytics - HIMSS 2015

By passively analyzing your wire data, ExtraHop provides deep visibility into HL7 messages, Citrix performance, EHR behavior, ICD-10 conversion, and more.
Proactive monitoring and remediation
Optimization and continuous improvement
Pervasive security monitoring and compliance
Clinical and operations analytics
End-to-End Security Analytics with the Elastic Stack

Interested in staying ahead of the adversary in a shifting security landscape? Learn how to create a centralized security analytics platform with the speed and scale you need for ad hoc analysis during threat detection and hunting exercises.
What's hot (20)
Document fingerprinting in Microsoft 365 Compliance

Document fingerprinting in Microsoft 365 Compliance
Hands-On Security Breakout Session- Disrupting the Kill Chain

Hands-On Security Breakout Session- Disrupting the Kill Chain
Applying Auto-Data Classification Techniques for Large Data Sets

Applying Auto-Data Classification Techniques for Large Data Sets
Operational Security Intelligence Breakout Session

Operational Security Intelligence Breakout Session
Splunk Enterprise for InfoSec Hands-On Breakout Session

Splunk Enterprise for InfoSec Hands-On Breakout Session
Splunk for Enterprise Security featuring User Behavior Analytics

Splunk for Enterprise Security featuring User Behavior Analytics
Cloudera Federal Forum 2014: EzBake, the DoDIIS App Engine

Cloudera Federal Forum 2014: EzBake, the DoDIIS App Engine
Threat Hunting with Elastic at SpectorOps: Welcome to HELK

Threat Hunting with Elastic at SpectorOps: Welcome to HELK
Fluency - Next Generation Incident Response Utilizing Big Data Analytics Over...

Fluency - Next Generation Incident Response Utilizing Big Data Analytics Over...
End-to-End Security Analytics with the Elastic Stack

End-to-End Security Analytics with the Elastic Stack
Viewers also liked
Power View from the Data Visualisation Perspective

Speaker: Jen Stirrup
Download SQL Server 2012: http://www.microsoft.com/sqlserver/en/us/get-sql-server/try-it.aspx
5 tips for_getting_a_job_interview_next_week ppt

Career Confidential presents 5 tips for Getting a Job Interview Next Week.
www.careerconfidential.com
The Evolution of IP Storage and Its Impact on the Network

- The document discusses the evolution of IP storage networks and their impact on enterprise networks. It argues that as data growth and server virtualization increase pressure on networks, dedicated IP storage networks can provide better performance, availability and manageability compared to consolidating IP storage onto general enterprise networks.
- It provides examples of customers who saw benefits such as improved scalability, efficiency and issue resolution by separating their IP storage networks and allowing their storage teams to manage the dedicated storage networking infrastructure. Isolating the storage network traffic helped provide more predictable performance for mission-critical workloads.
Block political vs physical maps

This document discusses different types of maps and their purposes. Political maps show human-made features like cities, roads, and borders. Physical maps show natural features not made by humans, like rivers, lakes, mountains, and oceans. The document provides examples of jobs that would use each type of map, like a hiker wanting a physical map of Colorado or a driver wanting a political map to get to Utah. It also gives map-reading exercises asking students to identify locations, borders, oceans, and other geographic features using an atlas.
Converged Data Center: FCoE, iSCSI and the Future of Storage Networking

From ( EMCWorld 2011 ) : This session explores the opportunities and challenges of using a single network to support both storage and networking. The Fibre Channel over Ethernet (FCoE) and iSCSI (SCSI over TCP/IP) protocols offer two approaches for supporting storage over Ethernet. Standards, technologies and deployment scenarios for both protocols are covered, along with the future of storage networking technology.
Transforming Expectations for Treat-Intelligence Sharing

Gain insight into a new approach to information-sharing processes for threat intelligence which ensures that data distribution is relevant, actionable, and automated.
RSA Security Briefs provide executives and practitioners with essential guidance on today’s most pressing information-security risks and opportunities. Each Brief is created by a select response team of security and technology experts who mobilize across companies to share specialized knowledge on a critical emerging topic. Offering both big-picture insight and practical technology advice, these papers are vital reading for today’s forward-thinking security leaders.
รวมไอเดียแบบบ้านชั้นเดียว

ไอเดียสร้างบ้านสำหรับท่านที่กำลังมองหาไอเดียแบบบ้านชั้นเดียว หลากหลายสไตล์ เพื่อเป็นแนวทางในการการออกแบบและการตกแต่ง
psychology of old age

The document discusses various aspects of aging including biological, psychological, and social factors. Biologically, aging is characterized by gradual decline in functioning of body systems due to factors like cellular damage and reduced organ function. Psychologically, late adulthood involves developmental tasks like accepting loss and retirement while maintaining interests. Socially, aging can involve changes like loss of social connections, discrimination against older adults, and economic and living situation adjustments. Maintaining well-being involves addressing reversible causes of mental health issues and continuing social engagement for older adults.
Underground city of_derinkuyu

The document summarizes the discovery and features of the underground city of Derinkuyu in Turkey. In 1963, a local resident discovered a hidden room behind a wall in his house, which led to the discovery of the extensive underground city. Archaeologists have since uncovered 20 levels that could house up to 10,000 people and provided refuge from frequent invasions. Key features included stone doors to block passages, ventilation wells, stables, dining rooms, a church, and connections to other underground cities. The underground city provided an advanced shelter system for inhabitants over different periods.
Tues treaty of versailles

This document provides information about the end of World War 1 and the Treaty of Versailles through a series of passages and images:
1) US troops provided fresh reinforcements for the Allied forces in 1918, helping them break through German lines during the decisive "Hundred Days Offensive." An armistice ended the war on November 11, 1918.
2) World leaders from the US, France, Britain, and Italy met secretly at the Palace of Versailles in 1919 to negotiate a peace treaty. The Treaty of Versailles placed blame on Germany, took territory, and imposed heavy reparations. It also created the League of Nations.
3) The treaty negatively impacted Germany by stripping it of land and imposing a large
Formulario agenda telefonica

Este documento contiene la agenda telefónica de 35 contactos con sus respectivos nombres, números de identificación, números telefónicos, ciudades y tipo de contacto (familiar, personal o profesional).
Make your presentations stick (3)

In this third tutorial we take a look at another technique to connect with the audience, through carefully crafted story telling.
Changing the Security Monitoring Status Quo

This solution overview discusses solving Security Information and Event Management (SIEM) challenges with RSA Security Analytics, which enables security analysts to be effective in protecting an organization’s digital assets and IT systems.
Viewers also liked (15)
Power View from the Data Visualisation Perspective

Power View from the Data Visualisation Perspective
The Evolution of IP Storage and Its Impact on the Network

The Evolution of IP Storage and Its Impact on the Network
Converged Data Center: FCoE, iSCSI and the Future of Storage Networking

Converged Data Center: FCoE, iSCSI and the Future of Storage Networking
Transforming Expectations for Treat-Intelligence Sharing

Transforming Expectations for Treat-Intelligence Sharing
Similar to RSA-Pivotal Security Big Data Reference Architecture
(ENT211) Migrating the US Government to the Cloud | AWS re:Invent 2014

This document discusses a platform called EzBake that was created to help a US government customer modernize their systems and better analyze large amounts of data. EzBake provides tools to easily develop and deploy applications, integrate and analyze data from various sources, and implement security controls. It improved the customer's ability to share data and applications across many teams and networks, decreased development times from 6-8 months to 3-4 weeks, and reduced costs while increasing capabilities.
QRadar, ArcSight and Splunk 

The document provides a review and comparison of the QRadar, ArcSight, and Splunk SIEM platforms. It summarizes their key capabilities and components. For each solution, it outlines strengths such as integrated monitoring, analytics features, and scalability. It also notes weaknesses such as complexity, customization limitations, and high data volume licensing costs. The comparison finds QRadar well-suited for smaller deployments, ArcSight for medium-large organizations, and notes Splunk's log collection strengths but limited out-of-the-box correlations compared to competitors. Gartner assessments for each platform cover visibility trends, deployment challenges, and roadmap monitoring advice.
Preparing for the Cybersecurity Renaissance

We are in the midst of a fundamental shift in the way in which organizations protect themselves from the modern adversary.
Traditional rules based cybersecurity applications of the past are not able to protect organizations in the new mobile, social, and hyper-connected world they now operate within. However, the convergence of big data technology, analytic advancements, and a variety of other factors have sparked a cybersecurity renaissance that will forever change the way in which organizations protect themselves.
Join Rocky DeStefano, Cloudera's Cybersecurity subject matter expert, as he explores how modern organizations are protecting themselves from more frequent, sophisticated attacks.
During this webinar you will learn about:
The current challenges cybersecurity professionals are facing today
How big data technologies are extending the capabilities of cybersecurity applications
Cloudera customers that are future proofing their cybersecurity posture with Cloudera’s next generation data and analytics management system
FireEye: Seamless Visibility and Detection for the Cloud

This document summarizes a presentation about securing data on AWS. It discusses how AWS can provide more security than on-premises environments through automated logging and monitoring, simplified access controls, and built-in encryption. It also outlines how AWS and customers share responsibility for security, with AWS managing the security of the cloud infrastructure and customers defining access and encryption controls for their applications and data. The presentation then demonstrates FireEye's Threat Analytics Platform for providing cloud-based threat detection, investigation, and response capabilities tailored for AWS environments.
SplunkLive! London - Splunk App for Stream & MINT Breakout

The document discusses new features in Splunk's App for Stream and Splunk MINT. It introduces the Splunk App for Stream, which enables real-time insights into private, public and hybrid cloud infrastructures through efficient wire data capture. It also discusses Splunk for Mobile Intelligence (MINT), which provides mobile analytics capabilities. The document promotes these products as enhancing operational intelligence through efficient and cloud-ready wire data collection.
Biznet Gio Presentation - Database Security

This document provides information on database security. It discusses how database security protects confidentiality, integrity and availability of databases. It also discusses the importance of database security to prevent data loss or compromise. Some of the largest data breaches in 2018 are summarized, including breaches of Aadhaar and Facebook that exposed over 1 billion and 87 million records respectively. Common attack vectors and frameworks for implementing database security are referenced. Finally, the document outlines a methodology for implementing proven database security practices around inventory, testing, compliance, eliminating vulnerabilities, enforcing least privileges, monitoring for anomalies, data protection, backup plans, and responding to incidents.
Azure Sentinel Jan 2021 overview deck 

Azure Sentinel is a cloud-native security information event management (SIEM) and security orchestration automated response (SOAR) solution. It collects data from across an organization, uses built-in analytics and threat intelligence to detect threats, enables investigation of incidents with AI, and automates responses. Azure Sentinel provides visibility across users, devices, applications, and infrastructure both on-premises and in multiple clouds. It detects previously unknown threats, minimizes false positives, and allows hunting for suspicious activities at scale. Responses can be automated through built-in orchestration of common tasks. Azure Sentinel has no infrastructure setup or maintenance costs and scales automatically with unlimited compute and storage resources.
S4x20 Forescout Presentation 

Asset owners today want to understand how investments made in people, process, or technology are progressing the maturity of their ICS security programs to validate those investments. Whether asset owners are spending one dollar, one million dollars, or one hour of their time, understanding which investments are actually improving the overall ICS security posture and reducing risk is essential to determine where to spend valuable (and sometimes limited) resources.
The NIST Cybersecurity Framework helps asset owners measure security control maturity in both IT and OT domains, and can be useful to help understand whether certain ICS security investments are working or not. This talk will break down all five NIST CSF functions and dive into specific forward thinking use cases used to help jumpstart many of Forescout's industry leading customers.
Overall Security Process Review CISC 6621Agend.docx

Overall Security Process Review
CISC 662
1
Agenda
Review of the following technologies and current products:
SIEM
CASB
EDR (Enterprise Detection and Response)
NGFW (Next Generation Firewalls)
Threat Intelligence
Summary of Term
SANS Technology Institute - Candidate for Master of Science Degree
What is a SIEM?
SIEM - Security Information Event Management
Logging and Event Aggregation
Network (router,switch,firewall,etc)
System (Server,workstation,etc)
Application (Web, DB )
Correlation Engine
2+ related events = higher alarm (1+1=3)
3
At first glance SIEM's appliances and software look like an event aggregator. While a SIEM has the advantage of aggregating logs what puts them apart from the event aggregator market are the correlation engines.
The correlation engines allow the ability to uncover threats/attacks across multiple related events which by themselves would not be a cause for alarm.
SIEM
4
What is a SIEM?
5
Security information and event management (SIEM) is the technology that can tie all your systems together and give you a comprehensive view of IT security.
IT security is typically a patchwork of technologies – firewalls, intrusion prevention, endpoint protection, threat intelligence and the like – that work together to protect an organization’s network and data from hackers and other threats. Tying all those disparate systems together is another challenge, however, and that’s where SIEM can help.
SIEM systems manage and make sense of security logs from all kinds of devices and carry out a range of functions, including spotting threats, preventing breaches before they occur, detecting breaches, and providing forensic information to determine how a security incident occurred as well as its possible impact.
Using SIEM
How do SIEM Products help the following Security concerns?
Countermeasures to detect attempts to infect internal system
Identification of infected systems trying to exfiltrate information
Mitigation of the impact of infected systems
Detection of outbound sensitive information ( DLP)
6
These questions are a core part of a companies overall security architecture. If a SIEM isn't providing answers or solutions to these questions what is it doing?
If you aren't using your SIEM to solve issues like these it may just be an expensive log aggregator/collection system sitting in your network collecting dust.
SIEM Advantages
Correlation of data from multiple systems and from different events detecting security and operational conditions
Anomaly detection by using a baseline of events over time to find deviations from expected or normal behavior
Comprehensive view into an environment based on event types, protocols, log sources, etc
APT (advanced persistent threat) protection through detection of protocol and application anomalies
Prioritization based on risk of threat to assets, staff can triage the most vulnerable targets
Alerting and monitoring on events of interest to escalate pri ...
Cloudera federal summit

EzBake is a secure application engine for DoDIIS that provides an integrated platform for building applications. It allows developers to focus on application logic while leveraging distributed frameworks for data ingestion, storage, querying and elastic deployment. The platform uses open source components like Frack for streaming data, common services for reusable logic, datasets for standardized data access, and OpenShift for deployment. Security is built into all components. EzBake aims to reduce costs by consolidating functionality and enabling data and resource sharing across applications. Future enhancements include distributed querying with Impala and integration with Apache Spark and Titan graph.
SAIP-Intelligence-Brochure

The SAIP platform collects data from multiple sources, enriches it with real-world context, and identifies connections between unrelated events to disseminate actionable intelligence to stakeholders. It transforms big data into usable intelligence by prioritizing new information and enabling proactive response to emerging threats. SAIP combines internal and external structured or unstructured data and applies advanced analytics to help identify security risks and gain a comprehensive view of existing threats.
Cisco_Big_Data_Webinar_At-A-Glance_ABSOLUTE_FINAL_VERSION

Analytics solutions are needed to generate insights from data located everywhere and help address challenges around scaling, integrating data, and generating real-time insights. Leading analytics providers like Splunk, SAP, Platfora, and SAS rely on Cisco infrastructure to power their solutions and deliver outcomes for customers. Cisco offers an analytics-ready infrastructure and Cisco Data Virtualization to process analytics from data centers to the edge and support customers' analytics journeys.
Building the High Speed Cybersecurity Data Pipeline Using Apache NiFi

This document discusses using Apache NiFi to build a high-speed cyber security data pipeline. It outlines the challenges of ingesting, transforming, and routing large volumes of security data from various sources to stakeholders like security operations centers, data scientists, and executives. It proposes using NiFi as a centralized data gateway to ingest data from multiple sources using a single entry point, transform the data according to destination needs, and reliably deliver the data while avoiding issues like network traffic and data duplication. The document provides an example NiFi flow and discusses metrics from processing over 20 billion events through 100+ production flows and 1000+ transformations.
10 Criteria for Evaluating NPB, Security Architect Edition

Top Ten Criteria for Evaluation a Network Packet Broker (aka Network Visibility) Solution, Security Architect Edition
Segmentation on azure platform

The document discusses network segmentation strategies on the Azure platform. It outlines several segmentation options on Azure including subscriptions, virtual networks, network security groups, application security groups, and Azure Firewall. It recommends segmenting based on principles such as splitting workstations from servers, grouping by physical location, separating production and non-production workloads, and isolating high risk or sensitive assets. The hub-spoke architecture is presented as a common topology for implementing segmentation on Azure with shared services in the hub and isolated workloads in spokes.
Cisco NGFW AMP

The Cisco Firepower Management Center provides centralized management of Cisco network security solutions such as firewalls, intrusion prevention, and advanced malware protection. It collects extensive network intelligence, analyzes vulnerabilities, and provides policy recommendations. The Management Center offers unified policy management, superior threat intelligence, application visibility and control, and reporting/dashboards. It is available as a physical or virtual appliance and supports various Cisco security products.
Splunk

Splunk is a time-series data platform that handles the three V's of data (volume, velocity, and variety) very well. It collects, indexes, and allows searching and analysis of data. Splunk can collect data from files, directories, network ports, programs/scripts, and databases. It breaks data down into searchable events and builds a high-performance index. This allows users to search, manipulate, and visualize data in reports, charts, and dashboards. Splunk can analyze structured, unstructured, and multistructured data from various sources like logs, networks, clicks, and more.
Soc security-analytics

Big data security product of Leo TechnoSoft is designed to provides software solutions on big data and analyze it in real time.
Presentacion de solucion cloud de navegacion segura

Solucion de seguridad de navegacion WEb con controles dobre trafico http y https, ademas de DLP y control de amenazas, CASB
Splunk MINT for Mobile Intelligence and Splunk App for Stream for Enhanced Op...

Learn what is new in Splunk App for Stream and how it can help you utilize wire/network data analytics to proactively resolve applications and IT operational issues and to efficiently analyze security threats in real-time, across your cloud and on-premises infrastructures. Additionally, you will learn about Splunk MINT, which allows you to gain operational intelligence on the availability, performance, and usage of your mobile apps. You’ll learn how to instrument your mobile apps for operational insight, and how you can build the dashboards, alerts, and searches you need to gain real-time insight on your mobile apps.
Similar to RSA-Pivotal Security Big Data Reference Architecture (20)
(ENT211) Migrating the US Government to the Cloud | AWS re:Invent 2014

(ENT211) Migrating the US Government to the Cloud | AWS re:Invent 2014
FireEye: Seamless Visibility and Detection for the Cloud

FireEye: Seamless Visibility and Detection for the Cloud
SplunkLive! London - Splunk App for Stream & MINT Breakout

SplunkLive! London - Splunk App for Stream & MINT Breakout
Overall Security Process Review CISC 6621Agend.docx

Overall Security Process Review CISC 6621Agend.docx
Cisco_Big_Data_Webinar_At-A-Glance_ABSOLUTE_FINAL_VERSION

Cisco_Big_Data_Webinar_At-A-Glance_ABSOLUTE_FINAL_VERSION
Building the High Speed Cybersecurity Data Pipeline Using Apache NiFi

Building the High Speed Cybersecurity Data Pipeline Using Apache NiFi
10 Criteria for Evaluating NPB, Security Architect Edition

10 Criteria for Evaluating NPB, Security Architect Edition
Presentacion de solucion cloud de navegacion segura

Presentacion de solucion cloud de navegacion segura
Splunk MINT for Mobile Intelligence and Splunk App for Stream for Enhanced Op...

Splunk MINT for Mobile Intelligence and Splunk App for Stream for Enhanced Op...
More from EMC
INDUSTRY-LEADING TECHNOLOGY FOR LONG TERM RETENTION OF BACKUPS IN THE CLOUD

CloudBoost is a cloud-enabling solution from EMC
Facilitates secure, automatic, efficient data transfer to private and public clouds for Long-Term Retention (LTR) of backups. Seamlessly extends existing data protection solutions to elastic, resilient, scale-out cloud storage
Cloud Foundry Summit Berlin Keynote 

Building a Cloud Foundry Dojo: A Model For Open Source Communities presented by Brian Gallagher, EMC Corporation
EMC GLOBAL DATA PROTECTION INDEX 

KEY FINDINGS & RESULTS FOR AMERICAS - GLOBALLY, ENTERPRISES ARE LOSING AS MUCH AS $1.7 TRILLION THROUGH DATA LOSS AND UNPLANNED DOWNTIME
Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO

With EMC XtremIO all-flash array, improve
1) your competitive agility with real-time analytics & development
2) your infrastructure agility with elastic provisioning for performance & capacity
3) your TCO with 50% lower capex and opex and double the storage lifecycle.
• Citrix & EMC XtremIO: Better Together
• XtremIO Design Fundamentals for VDI
• Citrix XenDesktop & XtremIO
-- Image Management & Storage
-- Demonstrations
-- XtremIO XenDesktop Integration
Citrix ready-webinar-xtremio

EMC XtremIO and Citrix XenDesktop provide an optimized virtual desktop infrastructure solution. XtremIO's all-flash storage delivers high performance, scalability, and predictable low latency required for large VDI deployments. Its agile copy services and data reduction features help reduce storage costs. Joint demonstrations showed XtremIO supporting thousands of desktops with sub-millisecond response times during boot storms and login storms. A unique plug-in streamlines the automated deployment and management of large XenDesktop environments using XtremIO's advanced capabilities.
EMC FORUM RESEARCH GLOBAL RESULTS - 10,451 RESPONSES ACROSS 33 COUNTRIES 

Explore findings from the EMC Forum IT Study and learn how cloud computing, social, mobile, and big data megatrends are shaping IT as a business driver globally.
EMC with Mirantis Openstack

Reference architecture with MIRANTIS OPENSTACK PLATFORM.The changes that are going on in IT with disruptions from technology, business and culture and so IT to solve the issues has to change from moving from traditional models to broker provider model.
Modern infrastructure for business data lake

This document summarizes a presentation about scale-out converged solutions for analytics. The presentation covers the history of analytic infrastructure, why scale-out converged solutions are beneficial, an analytic workflow enabled by EMC Isilon storage and Hadoop, test results showing performance benefits, customer use cases, and next steps. It includes an agenda, diagrams demonstrating analytic workflows, performance comparisons, and descriptions of enterprise features provided by using EMC Isilon with Hadoop.
Force Cyber Criminals to Shop Elsewhere

The document discusses identity and access management challenges for retailers. It outlines security concerns retailers face, including the need to protect customer data and payment card information from cyber criminals. It then describes specific identity challenges retailers deal with related to compliance, access governance, and managing identity lifecycles. The document proposes using RSA Identity Management and Governance solutions to help retailers with access reviews, governing access through policies, and keeping compliant with regulations. Use cases are provided showing how IMG can help with challenges like point of sale monitoring, unowned accounts, seasonal workers, and operational issues.
Pivotal : Moments in Container History 

Container-based technology has experienced a recent revival and is becoming adopted at an explosive rate. For those that are new to the conversation, containers offer a way to virtualize an operating system. This virtualization isolates processes, providing limited visibility and resource utilization to each, such that the processes appear to be running on separate machines. In short, allowing more applications to run on a single machine. Here is a brief timeline of key moments in container history.
Data Lake Protection - A Technical Review

This white paper provides an overview of EMC's data protection solutions for the data lake - an active repository to manage varied and complex Big Data workloads
Mobile E-commerce: Friend or Foe

This infographic highlights key stats and messages from the analyst report from J.Gold Associates that addresses the growing economic impact of mobile cybercrime and fraud.
Virtualization Myths Infographic 

Virtualization does not have to be expensive, cause downtime, or require specialized skills. In fact, virtualization can reduce hardware and energy costs by up to 50% and 80% respectively, accelerate provisioning time from weeks to hours, and improve average uptime and business response times. With proper training and resources, virtualization can be easier to manage than physical environments and save over $3,000 per year for each virtualized server workload through server consolidation.
Intelligence-Driven GRC for Security

An Intelligence Driven GRC model provides organizations with comprehensive visibility and context across their digital assets, processes, and relationships. It enables prioritization of risks based on their potential business impact and streamlines remediation. By collecting and analyzing data in real time, an Intelligence Driven GRC strategy reveals insights into critical risks and compliance issues and facilitates coordinated responses across security, risk management, and compliance functions.
The Trust Paradox: Access Management and Trust in an Insecure Age

This white paper discusses the results of a CIO UK survey on a“Trust Paradox,” defined as employees and business partners being both the weakest link in an organization’s security as well as trusted agents in achieving the company’s goals.
EMC Technology Day - SRM University 2015

Emory's 2015 Technology Day conference brought together faculty, staff and students to discuss innovative uses of technology in teaching and research. Attendees learned about new tools and platforms through hands-on workshops and presentations by Emory experts. The conference highlighted how technology is enhancing collaboration and creativity across Emory's campus.
Data Science and Big Data Analytics Book from EMC Education Services

This document provides information about data science and big data analytics. It discusses discovering, analyzing, visualizing and presenting data as key activities for data scientists. It also provides a website for further information on a book covering the tools and methods used by data scientists.
Using EMC Symmetrix Storage in VMware vSphere Environments

This EMC Engineering TechBook describes how the VMware vSphere platform works with EMC Symmetrix storage systems and software technologies.
Using EMC VNX storage with VMware vSphereTechBook

This document provides an overview of using EMC VNX storage with VMware vSphere. It covers topics such as VNX technology and management tools, installing vSphere on VNX, configuring storage access, provisioning storage, cloning virtual machines, backup and recovery options, data replication solutions, data migration, and monitoring. Configuration steps and best practices are also discussed.
More from EMC (20)
INDUSTRY-LEADING TECHNOLOGY FOR LONG TERM RETENTION OF BACKUPS IN THE CLOUD

INDUSTRY-LEADING TECHNOLOGY FOR LONG TERM RETENTION OF BACKUPS IN THE CLOUD
Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO

Transforming Desktop Virtualization with Citrix XenDesktop and EMC XtremIO
EMC FORUM RESEARCH GLOBAL RESULTS - 10,451 RESPONSES ACROSS 33 COUNTRIES 

EMC FORUM RESEARCH GLOBAL RESULTS - 10,451 RESPONSES ACROSS 33 COUNTRIES
The Trust Paradox: Access Management and Trust in an Insecure Age

The Trust Paradox: Access Management and Trust in an Insecure Age
Data Science and Big Data Analytics Book from EMC Education Services

Data Science and Big Data Analytics Book from EMC Education Services
Using EMC Symmetrix Storage in VMware vSphere Environments

Using EMC Symmetrix Storage in VMware vSphere Environments
Recently uploaded
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-und-domino-lizenzkostenreduzierung-in-der-welt-von-dlau/
DLAU und die Lizenzen nach dem CCB- und CCX-Modell sind für viele in der HCL-Community seit letztem Jahr ein heißes Thema. Als Notes- oder Domino-Kunde haben Sie vielleicht mit unerwartet hohen Benutzerzahlen und Lizenzgebühren zu kämpfen. Sie fragen sich vielleicht, wie diese neue Art der Lizenzierung funktioniert und welchen Nutzen sie Ihnen bringt. Vor allem wollen Sie sicherlich Ihr Budget einhalten und Kosten sparen, wo immer möglich. Das verstehen wir und wir möchten Ihnen dabei helfen!
Wir erklären Ihnen, wie Sie häufige Konfigurationsprobleme lösen können, die dazu führen können, dass mehr Benutzer gezählt werden als nötig, und wie Sie überflüssige oder ungenutzte Konten identifizieren und entfernen können, um Geld zu sparen. Es gibt auch einige Ansätze, die zu unnötigen Ausgaben führen können, z. B. wenn ein Personendokument anstelle eines Mail-Ins für geteilte Mailboxen verwendet wird. Wir zeigen Ihnen solche Fälle und deren Lösungen. Und natürlich erklären wir Ihnen das neue Lizenzmodell.
Nehmen Sie an diesem Webinar teil, bei dem HCL-Ambassador Marc Thomas und Gastredner Franz Walder Ihnen diese neue Welt näherbringen. Es vermittelt Ihnen die Tools und das Know-how, um den Überblick zu bewahren. Sie werden in der Lage sein, Ihre Kosten durch eine optimierte Domino-Konfiguration zu reduzieren und auch in Zukunft gering zu halten.
Diese Themen werden behandelt
- Reduzierung der Lizenzkosten durch Auffinden und Beheben von Fehlkonfigurationen und überflüssigen Konten
- Wie funktionieren CCB- und CCX-Lizenzen wirklich?
- Verstehen des DLAU-Tools und wie man es am besten nutzt
- Tipps für häufige Problembereiche, wie z. B. Team-Postfächer, Funktions-/Testbenutzer usw.
- Praxisbeispiele und Best Practices zum sofortigen Umsetzen
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
“I’m still / I’m still / Chaining from the Block”

“An Outlook of the Ongoing and Future Relationship between Blockchain Technologies and Process-aware Information Systems.” Invited talk at the joint workshop on Blockchain for Information Systems (BC4IS) and Blockchain for Trusted Data Sharing (B4TDS), co-located with with the 36th International Conference on Advanced Information Systems Engineering (CAiSE), 3 June 2024, Limassol, Cyprus.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
UiPath Test Automation using UiPath Test Suite series, part 6

Welcome to UiPath Test Automation using UiPath Test Suite series part 6. In this session, we will cover Test Automation with generative AI and Open AI.
UiPath Test Automation with generative AI and Open AI webinar offers an in-depth exploration of leveraging cutting-edge technologies for test automation within the UiPath platform. Attendees will delve into the integration of generative AI, a test automation solution, with Open AI advanced natural language processing capabilities.
Throughout the session, participants will discover how this synergy empowers testers to automate repetitive tasks, enhance testing accuracy, and expedite the software testing life cycle. Topics covered include the seamless integration process, practical use cases, and the benefits of harnessing AI-driven automation for UiPath testing initiatives. By attending this webinar, testers, and automation professionals can gain valuable insights into harnessing the power of AI to optimize their test automation workflows within the UiPath ecosystem, ultimately driving efficiency and quality in software development processes.
What will you get from this session?
1. Insights into integrating generative AI.
2. Understanding how this integration enhances test automation within the UiPath platform
3. Practical demonstrations
4. Exploration of real-world use cases illustrating the benefits of AI-driven test automation for UiPath
Topics covered:
What is generative AI
Test Automation with generative AI and Open AI.
UiPath integration with generative AI
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
Full-RAG: A modern architecture for hyper-personalization

Mike Del Balso, CEO & Co-Founder at Tecton, presents "Full RAG," a novel approach to AI recommendation systems, aiming to push beyond the limitations of traditional models through a deep integration of contextual insights and real-time data, leveraging the Retrieval-Augmented Generation architecture. This talk will outline Full RAG's potential to significantly enhance personalization, address engineering challenges such as data management and model training, and introduce data enrichment with reranking as a key solution. Attendees will gain crucial insights into the importance of hyperpersonalization in AI, the capabilities of Full RAG for advanced personalization, and strategies for managing complex data integrations for deploying cutting-edge AI solutions.
Microsoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
Recently uploaded (20)
HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU

HCL Notes und Domino Lizenzkostenreduzierung in der Welt von DLAU
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
UiPath Test Automation using UiPath Test Suite series, part 6

UiPath Test Automation using UiPath Test Suite series, part 6
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
Full-RAG: A modern architecture for hyper-personalization

Full-RAG: A modern architecture for hyper-personalization
RSA-Pivotal Security Big Data Reference Architecture
- 1. RSA-Pivotal Security Big Data Reference Architecture RSA & Pivotal combine to help security teams detect threats quicker and speed up response ESSENTIALS RSA and Pivotal are combining to help customers get: • Better visibility into what’s happening in their environments • Actionable intelligence from a diverse set of internal and external sources Despite significant investment in information security, attackers appear to have the upper hand. According to the Verizon Data Breach Investigations report (2013), 97 percent of breaches led to data compromise within “days” or less, whereas 78 percent of breaches took “weeks” or more to discover. • Attackers are becoming more organized and better funded. But while attacks have become dynamic, defenses have remained static. Today’s More contextual analytics to help them prioritize issues • ATTACKERS STILL HAVE THE UPPER HAND attacks are designed to exploit the weaknesses of our user-centric, hyperconnected infrastructures. • IT-enabled organizations continue to grow more complex. Organizations now demand much more open and agile systems, creating incredible new opportunities for collaboration, communication, and innovation. This also results in new vulnerabilities that cyber criminals, “hacktivist” groups, and nation states have learned to exploit. • There are often not enough skilled security professionals to help organizations protect themselves effectively. The 2013 (ISC)2 Global Information Security Workforce Study found that 56% of its respondents believe that there is a security workforce shortage To reverse the tide and protect their organizations better, security teams need a few things. They need: • Better visibility into what’s happening in their environments, from their networks, to their servers to their applications and endpoints. • More contextual analytics of what’s going on to help them prioritize issues more effectively and concentrate more resources on those issues that are more likely to impact their business • Actionable intelligence from diverse sources, both internal and external, to tell the system what to look for in a more automated way, and help them respond quicker • An architecture that scales to support the business as it grows and evolves RSA and Pivotal have worked together to create an architecture that truly helps security teams to fulfill these needs, and help speed up attack detection and response times, and reducing the impact of attacks on organizations. Moreover this approach creates a platform that can be used for a myriad of other use case across IT operations and the enterprise. SOLUTION OVERVIEW
- 2. VISIBILITY IS THE FOUNDATION FOR SUPERIOR ANALYTICS RSA and Pivotal provide unparalleled visibility into user and system activity across the IT environment. RSA Security Analytics provides a collection infrastructure that can provides full visibility into • Network Activity by performing full packet capture, session reconstruction and analysis of packet data • Log Data by collecting log and event data from devices and applications that support business and IT activity. Collection occurs through the deployment of “decoder” devices topographically close of the systems generating the data, either through a span port or tap (in the case of packets) or through common system protocols including syslog, SNMP, ODBC or proprietary protocols. RSA Security Analytics also integrates with systems that collect contextual information like • Asset data – this includes the collection of technical configuration data, as well as business context like what business processes the system supports, or the criticality of the system • Vulnerability data – data which can add additional context to an investigation (e.g. when the system was last scanned and what vulnerabilities were present) or to help prioritize response to attacks on vulnerable systems • Identity data – additional contextual information about the user, their location, their job function and the privileges they have. RSA Security Analytics enriches the log and network data it captures with this contextual information to aid in the “downstream” processing of that data, either in the detection or investigation of threats Fig 1. Security Analytics High Level Architecture
- 3. ANALYTICS THROUGHOUT THE INFORMATION LIFECYCLE STREAMLINE DETECTION AND INVESTIGATION RSA and Pivotal combine to provide numerous types of analytics, needed to spot threats at different times in the information lifecycle. The three main types of analytics provided are: • Capture time analytics – to identify interesting characteristics of data right at the time of capture. This includes: o Basic characteristics – e.g. source IP, destination IP, username, log action, etc. o Interesting characteristics – e.g. such use of encryption, executable files, administrative users, administrative commands o Indicators of compromise – e.g. known bad IPs, known bad protocols, watchlist users Security Analytics creates “metadata” out of these interesting characteristics that can be used for further analytics or to facilitate investigations • Streaming analytics – to analyze metadata in real time to spot concurrent sessions or actions happening over a short time window that might be an indicator of a threat. This metadata could be log-based, network-based or from another contextual source. Examples include: o Basic SIEM-like correlation rules: like 5 failed logons followed by a successful logon o Compound indicators of compromise: like a user downloading suspect JavaScript at around the same time as an encrypted session to a blacklisted country o Hybrid log & network rules: like malformed traffic bound for a host at around the same time as encrypted traffic to a blacklisted country Streaming analytics can be based on combinations of events or deviations from a “baseline” normal count of a piece of metadata. Streaming analytics appliances need not be deployed right at the point of data collection, but can be deployed in parallel throughout the environment for enhanced scalability. • Batch analytics – to identify “low and slow” type attacks, and patterns that occur over extended periods of time. Batch analytics is performed by the RSA Security Analytics Warehouse, which has Pivotal HD at its core. Pivotal uses proven Hadoop and other Big Data technologies, and the Pivotal Data Science Labs team to enable different analytic techniques including: o Rules based pattern matching o Cluster analysis o Anomaly detection o Machine learning Batch analytics and these advanced methods facilitate use cases such as malicious domain detection, beaconing host detection, and anomalous user behavior detection. In addition, RSA Security Analytics provides a log archiving capability to allow organizations to satisfy retention and reporting requirements, but store the data in a cost-effective manner
- 4. ANALYTIC METHODS COMBINE TO FACILITATE ADVANCED SOC ACTIONS Threat analysts need a combination of capture time, stream and batch analytics to detect and investigate a full range of threats. Each of these methods combine to support a number of workstreams common in a security operations center, like: • Visualizing heat maps of issues across an organization by business unit or profile • Profiling systems or devices for indicators of risk • Prioritizing alerts when a particular critical business asset or user exhibits multiple suspicious characteristics over a week-long period • Providing investigative context after an alert gets triggered to determine the cause or impact of an issue, e.g. if the user downloaded an executable prior to the alert, or the IP accessed a critical asset after triggering the alert In addition, using Pivotal and Hadoop, and the Pivotal Data Science Labs team offers the potential to add additional capabilities like: • Predictive modeling – using visibility and context to predict where issues are likely to occur • Analyst feedback loops – allowing analysts to provide feedback whether they think a particular alert warrants follow-up, and allowing the system to learn that for future alerts DISTRIBUTED ARCHITECTURE ALLOWS FOR ENTERPRISE SCALABILITY AND DEPLOYMENT Many systems have claimed to offer this functionality, but have failed. This is because older architecture using old database technologies and proprietary data stores don’t work. More analytical compute power than ever is needed to analyze the data, but this needs to be provided cost effectively. Pivotal and RSA have teamed up to create a Security Analytics platform that provides an architecture that deploys components throughout the environment in order to provide superior scalability and deployability, and the ability to deploy the platform in a modular way to suit an organization’s unique use cases. • Collection and Capture-Time Analytics get deployed close to where the activity occurs. This allows the system to scale across locations more effectively. This also minimizes the impact on WAN connections, since the system can be configured to transfer only metadata, not raw data across these connections. • Streaming Analytics and Archiving get deployed centrally or in a federated way. Architects can decide to deploy the system in a more central way, or in a federated way. This gives maximum flexibility to take into account compliance regulations around cross-border data transfer requirements or network constraints. • Batch Analytics gets deployed in a Hadoop cluster that takes advantage of the resilient nature of a Hadoop distributed computing environment • SOCs operate where the best talent resides. With this architecture, the Security Operations Center can access the data and perform analytics from anywhere across the organization. A sample multi-location architecture diagram is included below.
- 5. Fig 2. Sample deployment for Security Analytics and Pivotal PIVOTAL EXPANDS USES OF COLLECTED DATA ACROSS IT AND ENTERPRISE USE CASES The combined Pivotal and RSA platform allows IT organizations to gain greater value from the data collected through the use of the collected data for non-security use cases. The open architecture gives IT organizations flexibility to leverage Hadoop tools, or Pivotal tools like HAWQ and Spring XD to develop applications and analytics for adjacent use cases like: • Capacity planning • Mean-time-to-repair analysis • Downtime impact analysis • Shadow IT detection Moreover, outside of security and IT operations, there are a myriad of options for incorporating security into a wider Enterprise Data Lake allowing the data to be used for uses such as customer experience monitoring and billing. This allows customers to gain much wider benefit across their organization from their investment in Pivotal and RSA.
- 6. BENEFITS OF RSA-PIVOTAL APPROACH The joint RSA-Pivotal offering provides customers with: • Reduced risk of compromise by using the latest analytic and detection techniques and threat intelligence to aid in the detection, investigation and response to security incidents • Reduced deployment risk and quicker time to value through proven, validated architecture for collection, analytics of data that produces actionable intelligence at enterprise scale • Less reliance on Data Science expertise to leverage cutting edge analytic techniques • Take better advantage of existing security expertise by adding analytic firepower • Enterprise-wide benefits as collected data integrates with the Enterprise data lake CONTACT US To learn more about how EMC products, services, and solutions can help solve your business and IT challenges, contact your local representative or authorized reseller— or visit us at www.emc.com. EMC2, EMC, the EMC logo, RSA are registered trademarks or trademarks of EMC Corporation in the United States and other countries. VMware is a registered trademark or trademark of VMware, Inc., in the United States and other jurisdictions. © Copyright 2014 EMC Corporation. All rights reserved. Published in the USA. 02/14 Solution Overview H12878 EMC believes the information in this document is accurate as of its publication date. The information is subject to change without notice.