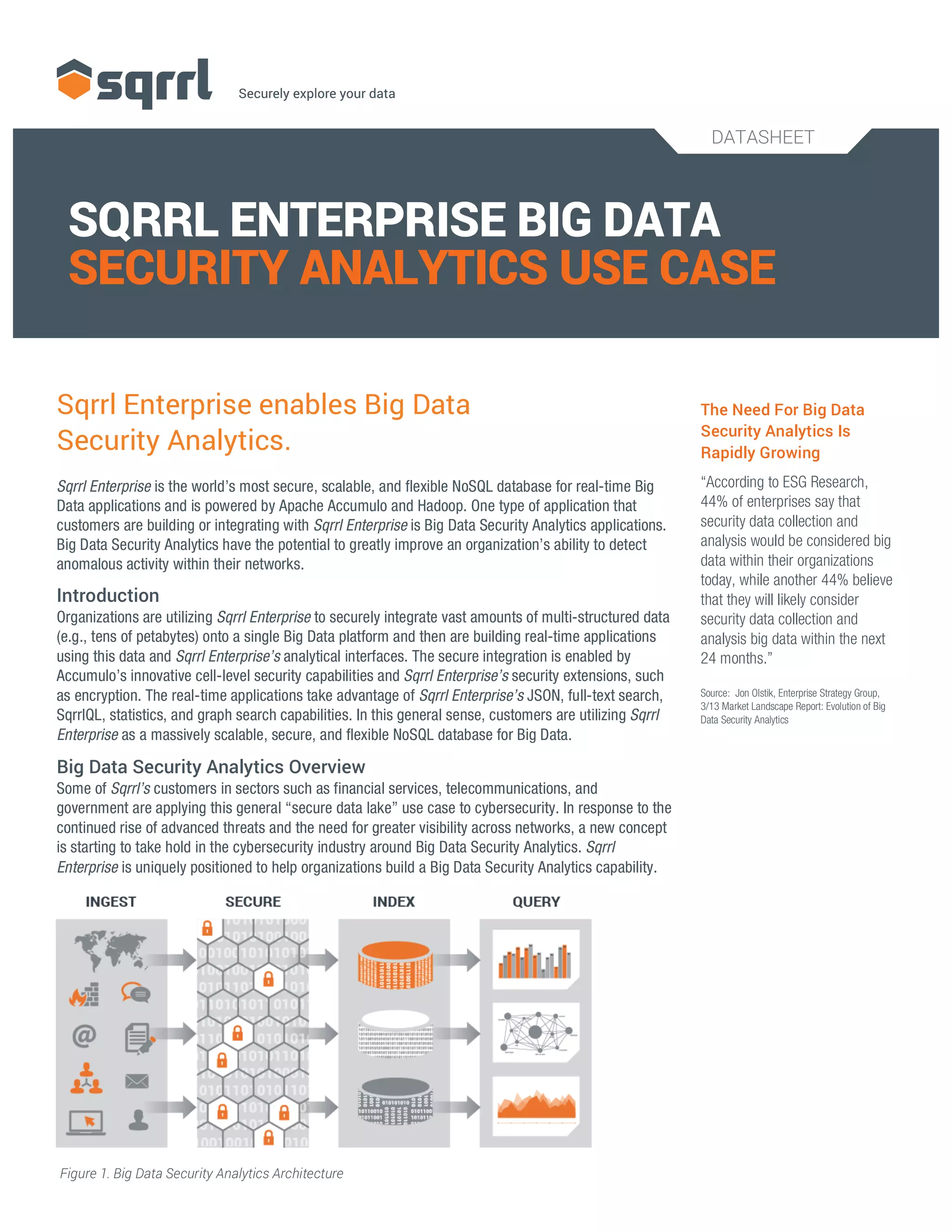
Sqrrl Enterprise offers a secure, scalable NoSQL database designed for real-time big data security analytics applications, enabling organizations to analyze vast amounts of multi-structured data for detecting anomalous activities. It provides advantages over traditional SIEM tools, such as greater scalability, flexibility in data sources, and lower costs, thereby supporting the analysis of cybersecurity data in real-time. As the demand for big data security analytics rises, Sqrrl is uniquely positioned to help organizations build effective security analytics capabilities.