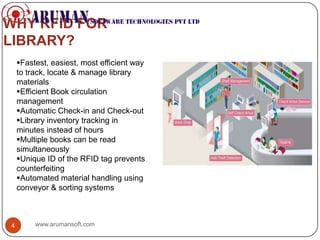
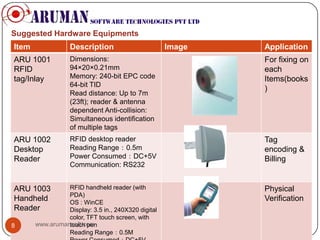
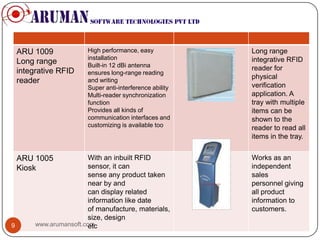
The document discusses the implementation of RFID technology in libraries to enhance management efficiency and improve patron experience by automating book handling processes. Key benefits include faster inventory management, reduced circulation operation times, enhanced security, and better patron services through self-checkout systems and easy item tracking. It also lists suggested RFID hardware solutions to facilitate these functions.