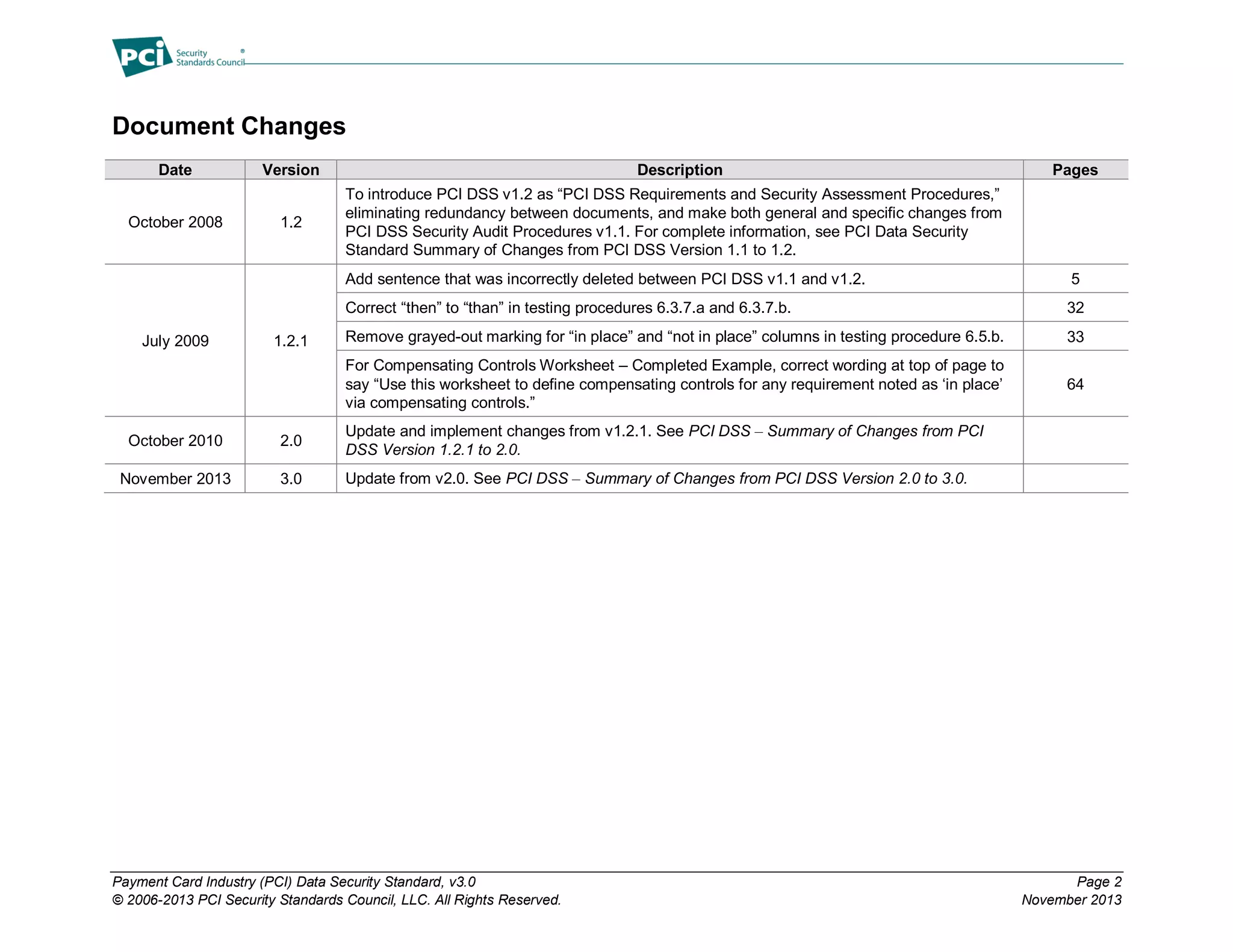
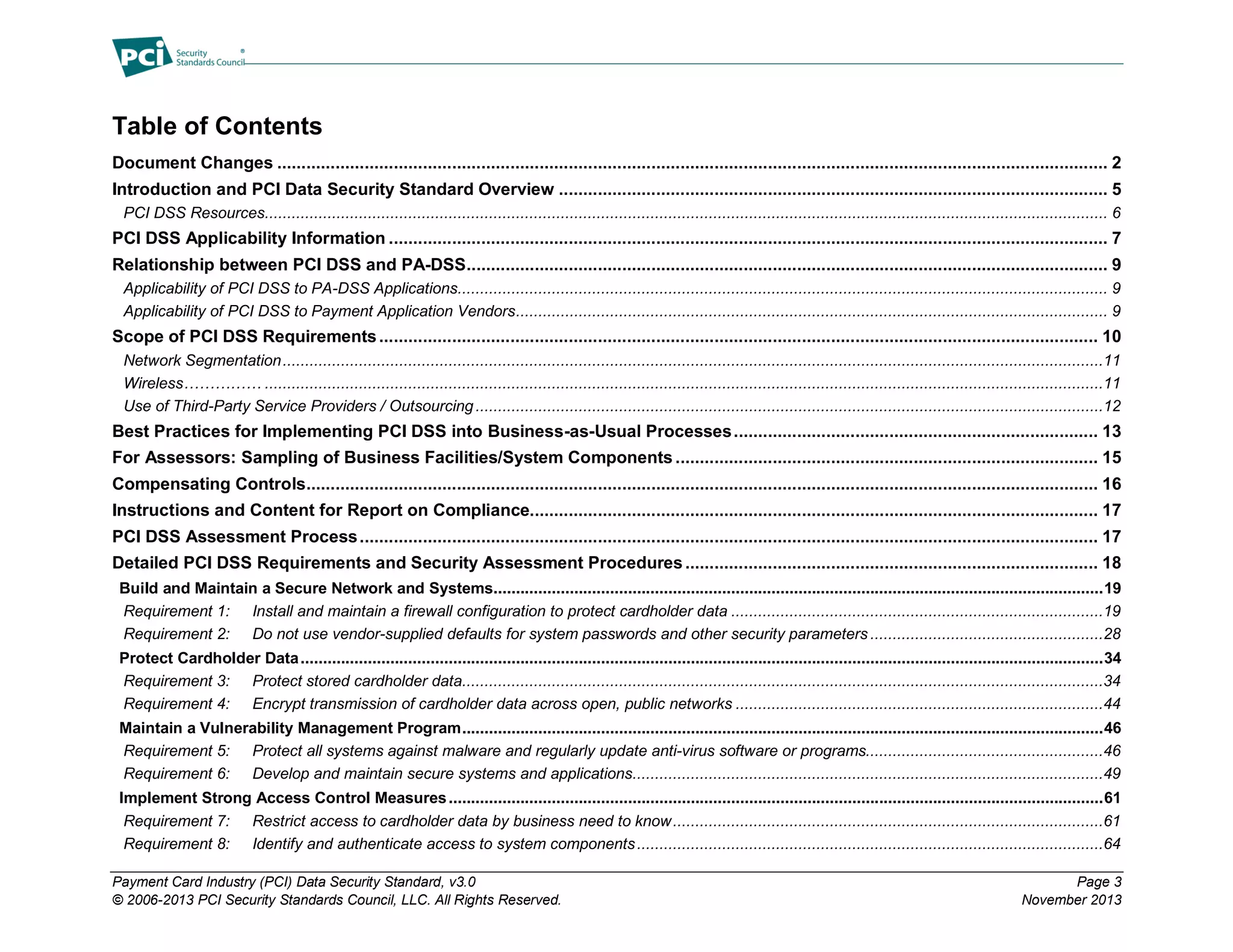
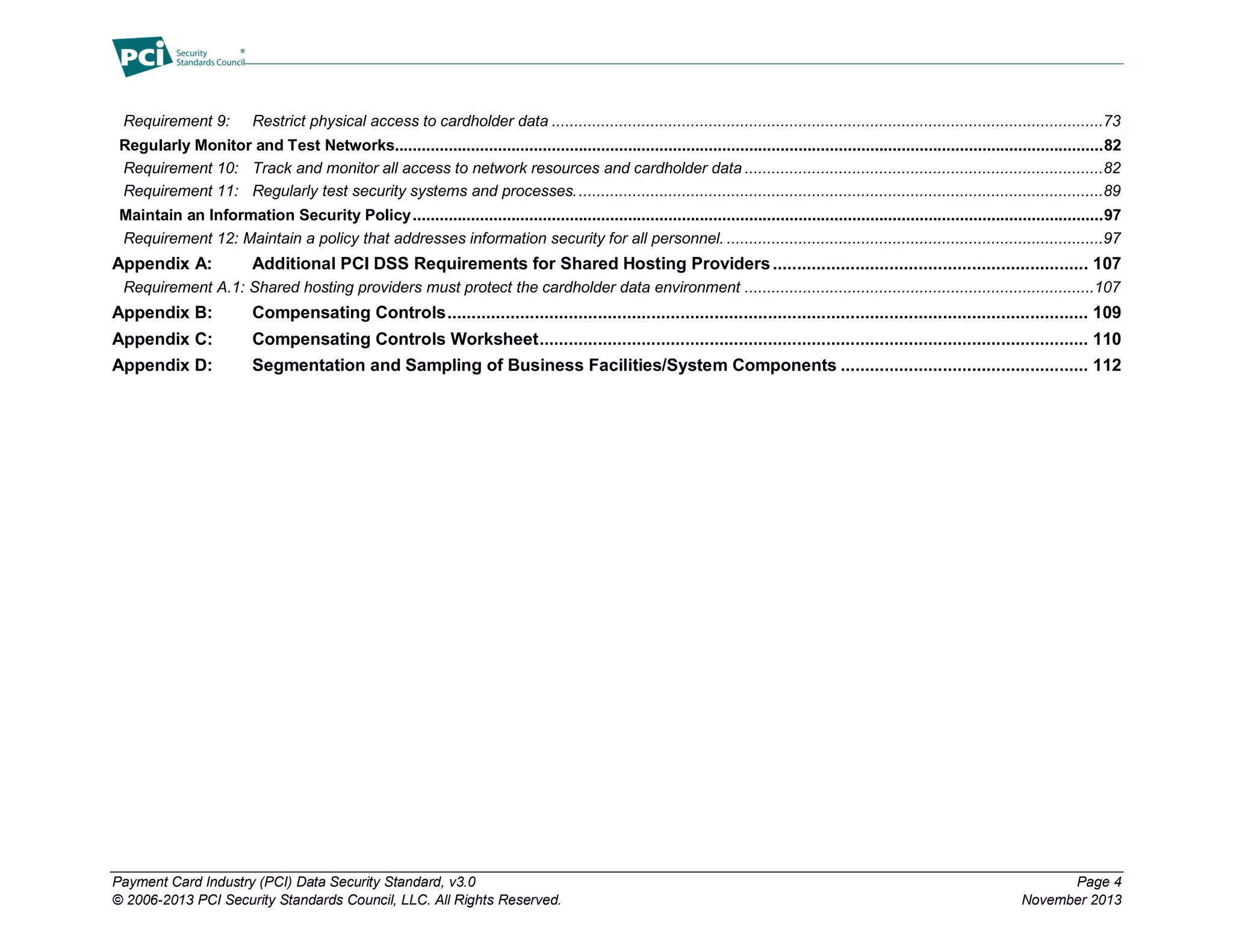
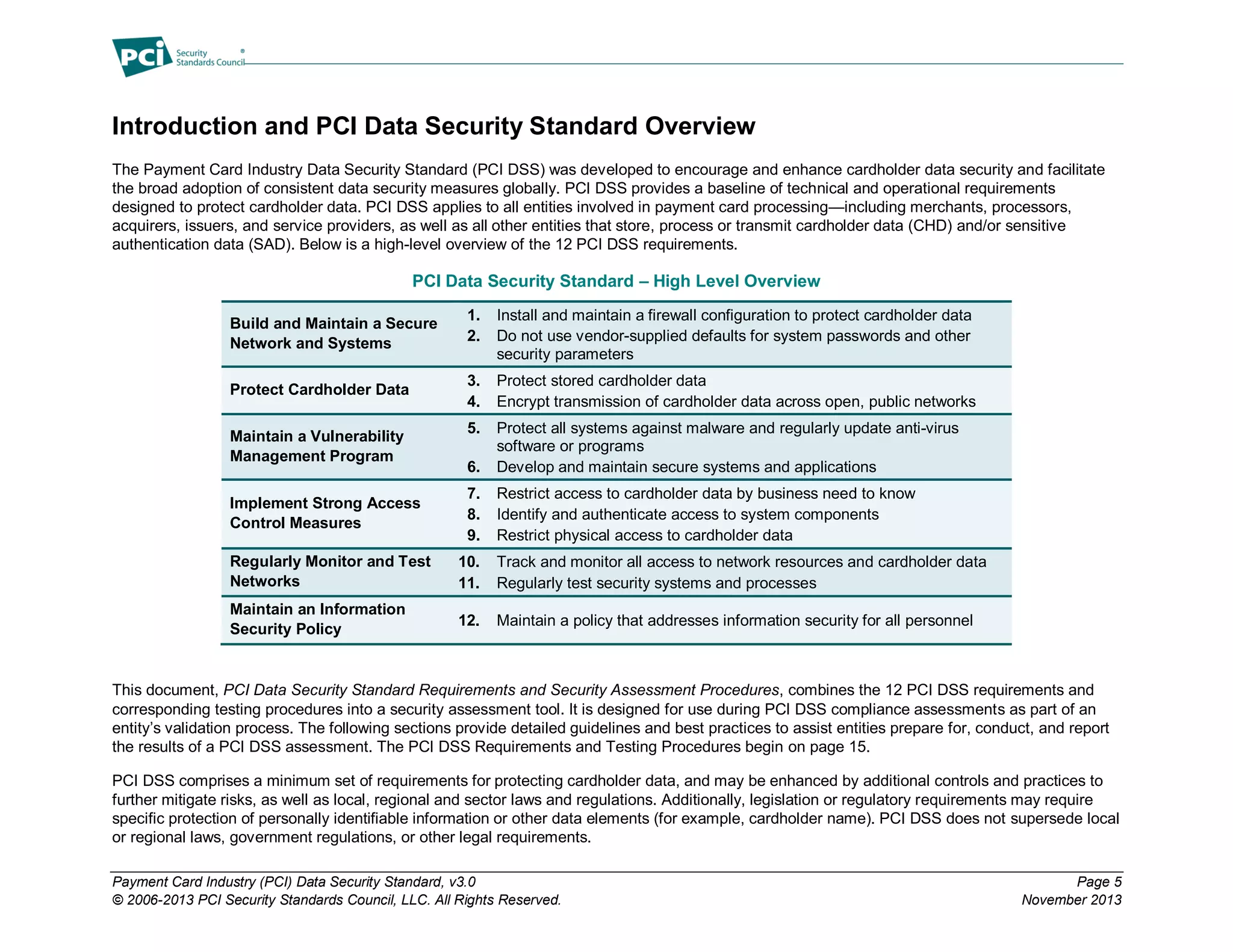
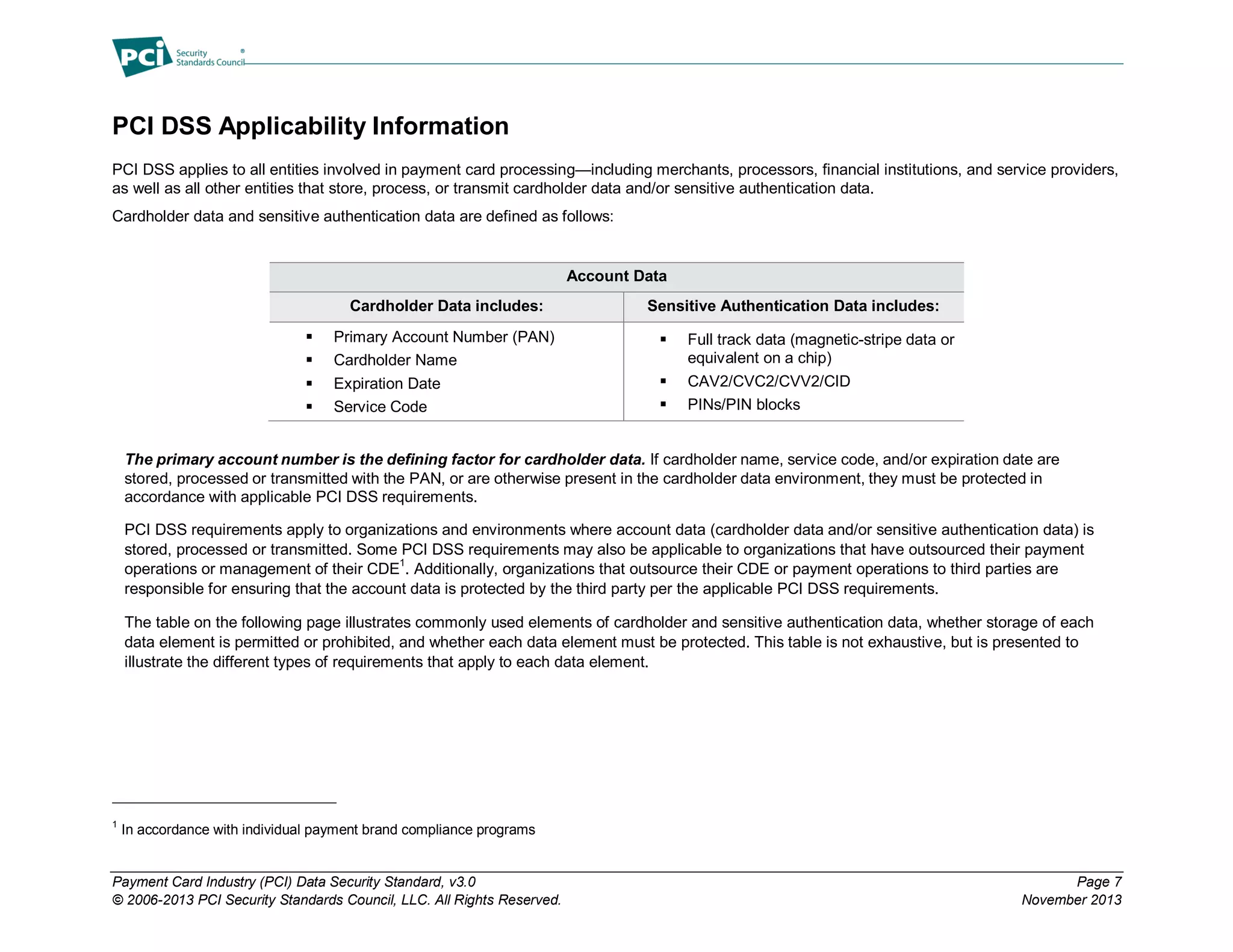
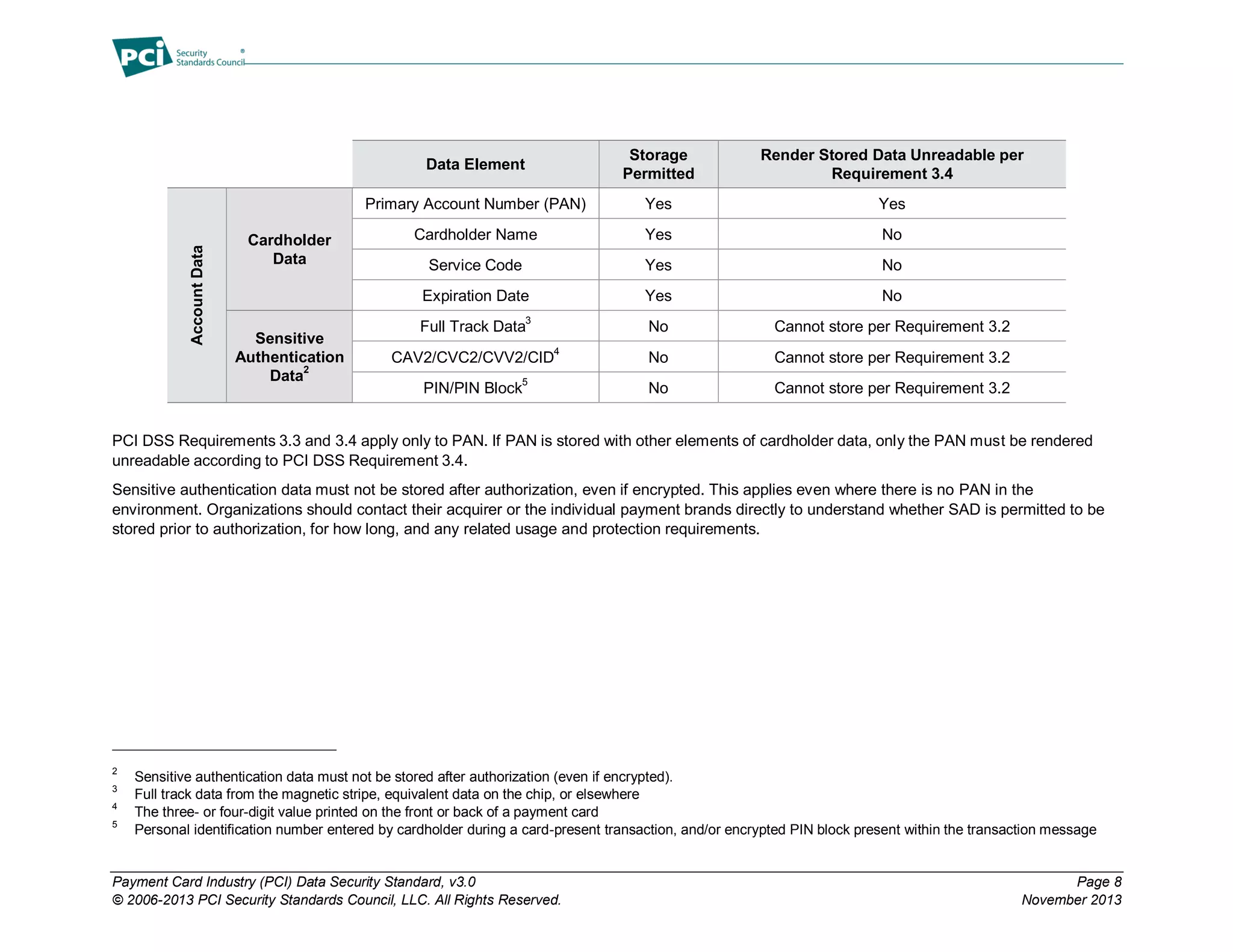
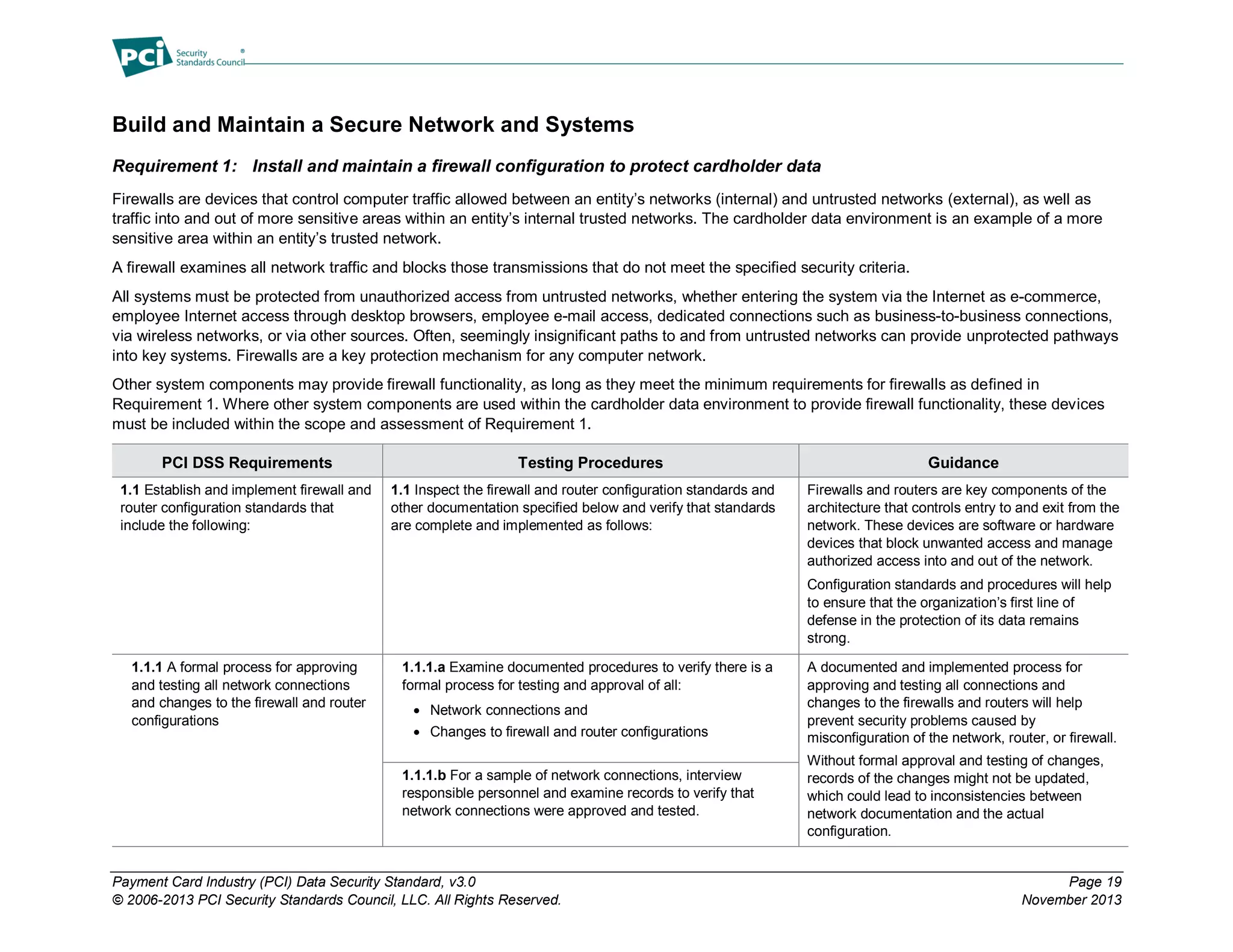
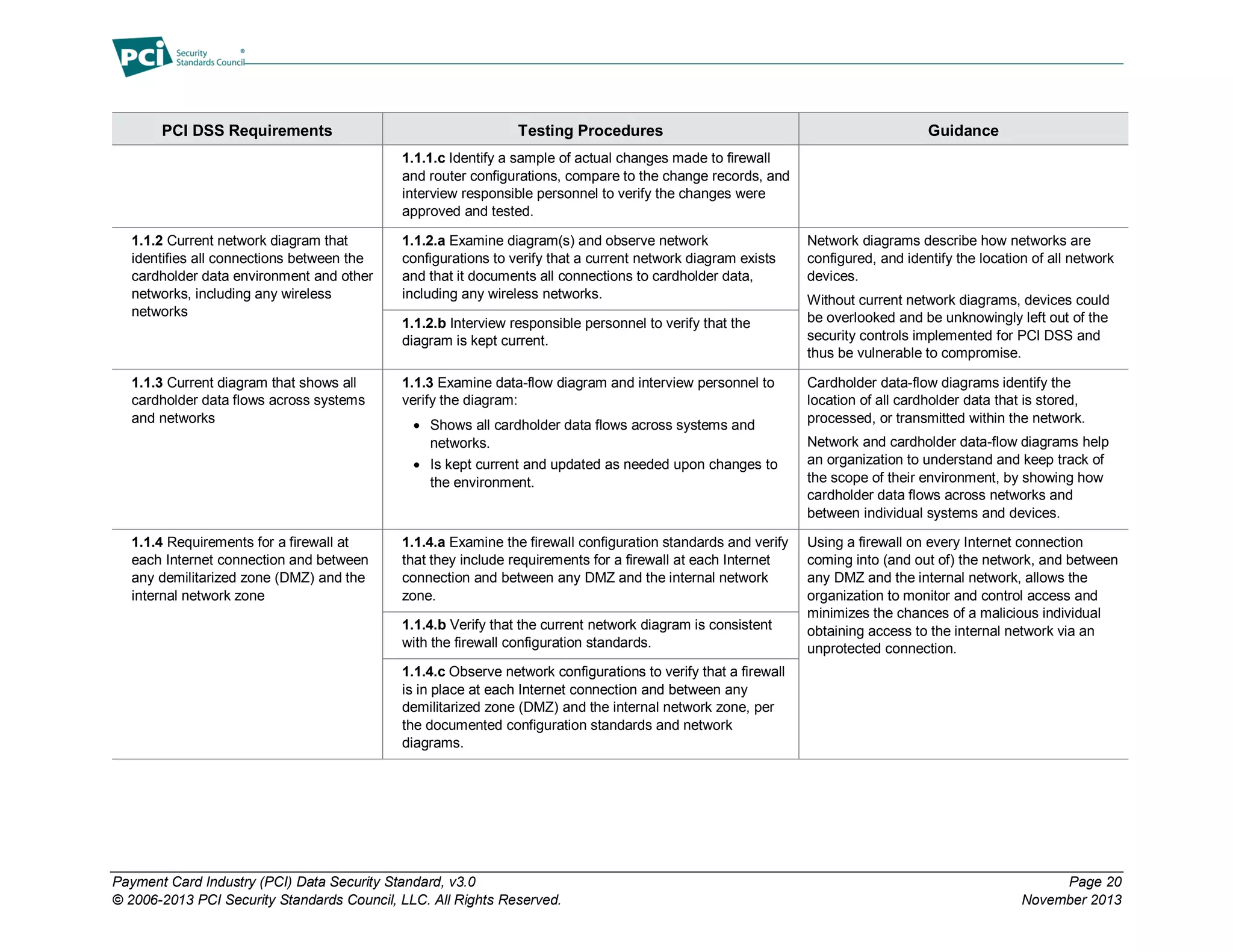
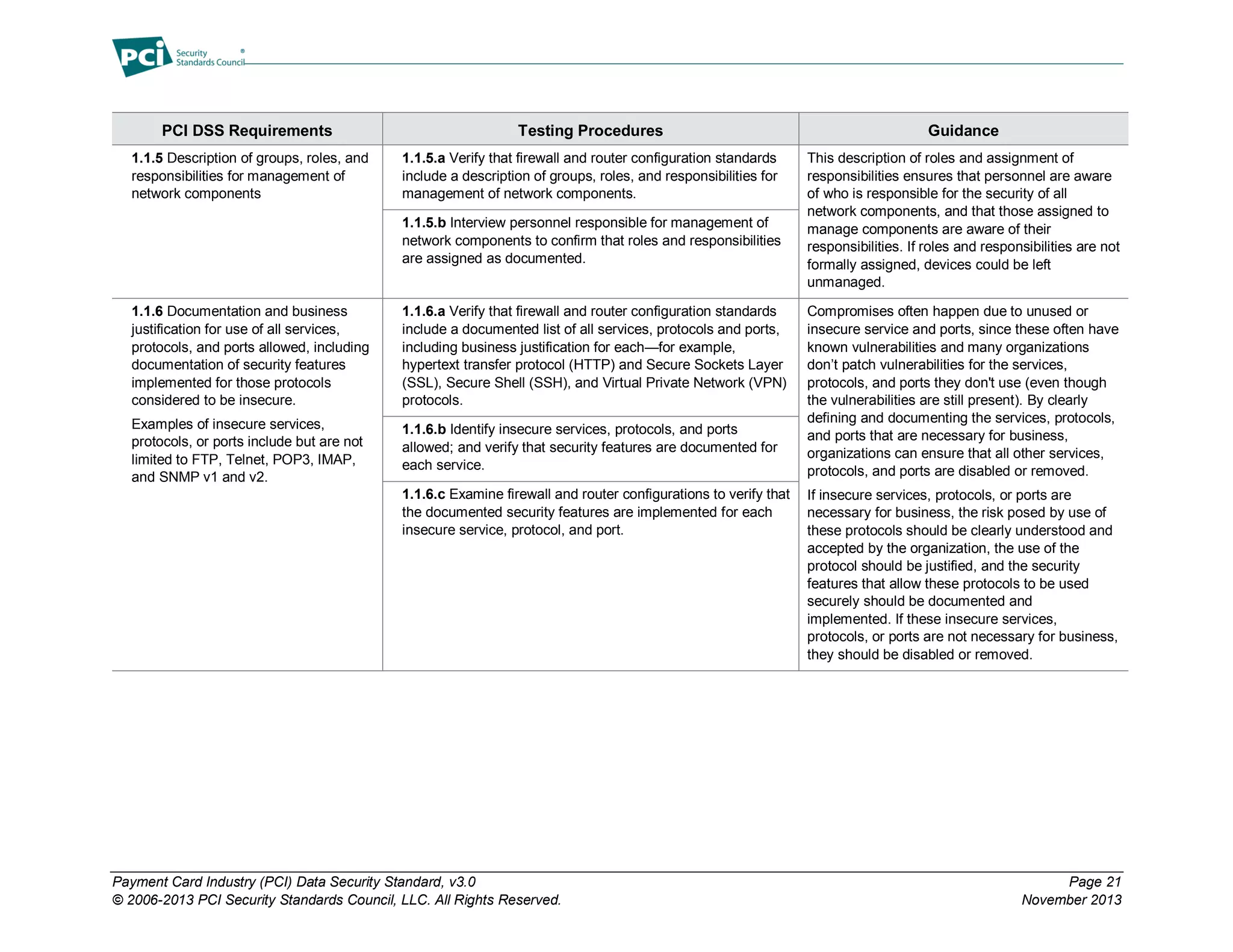
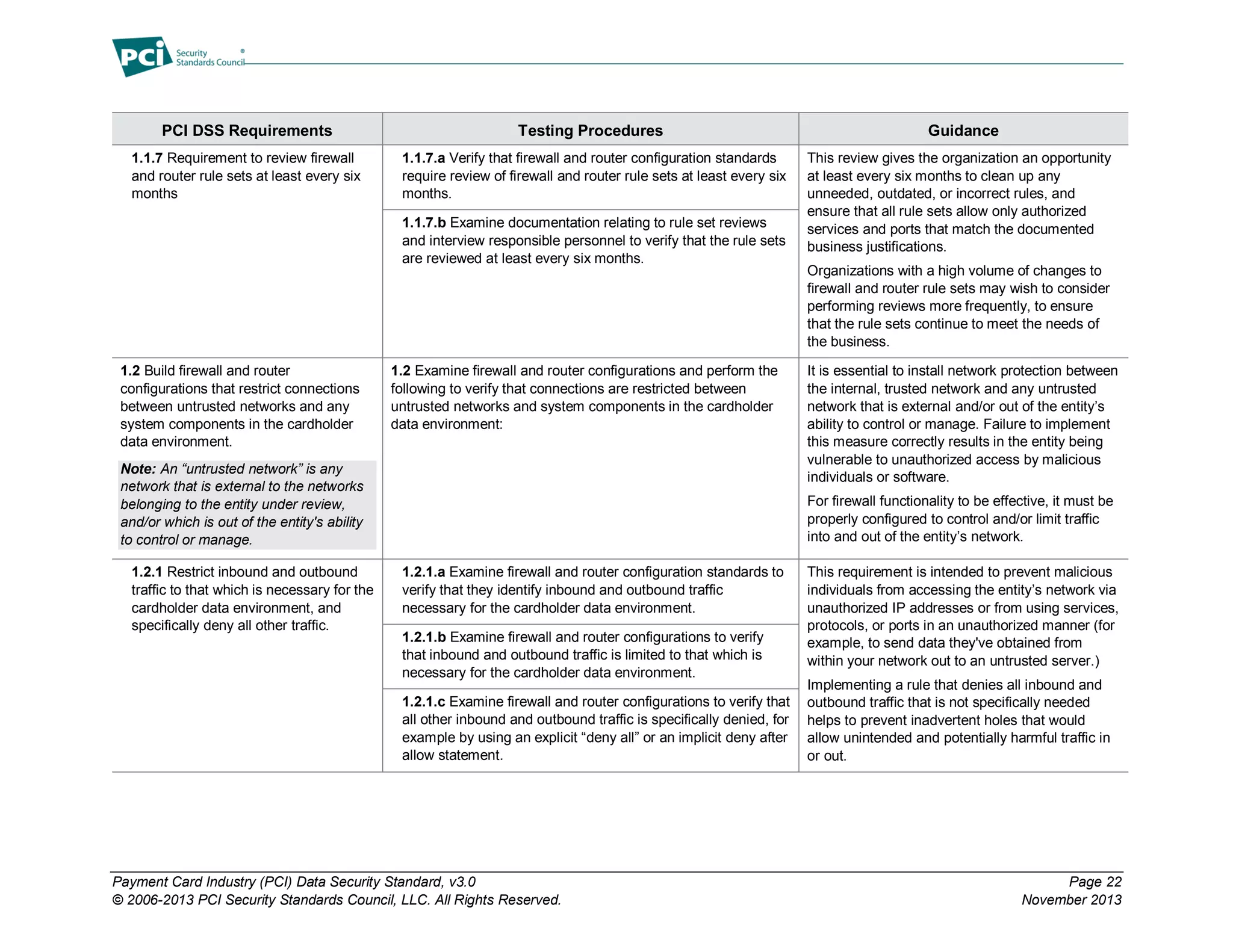
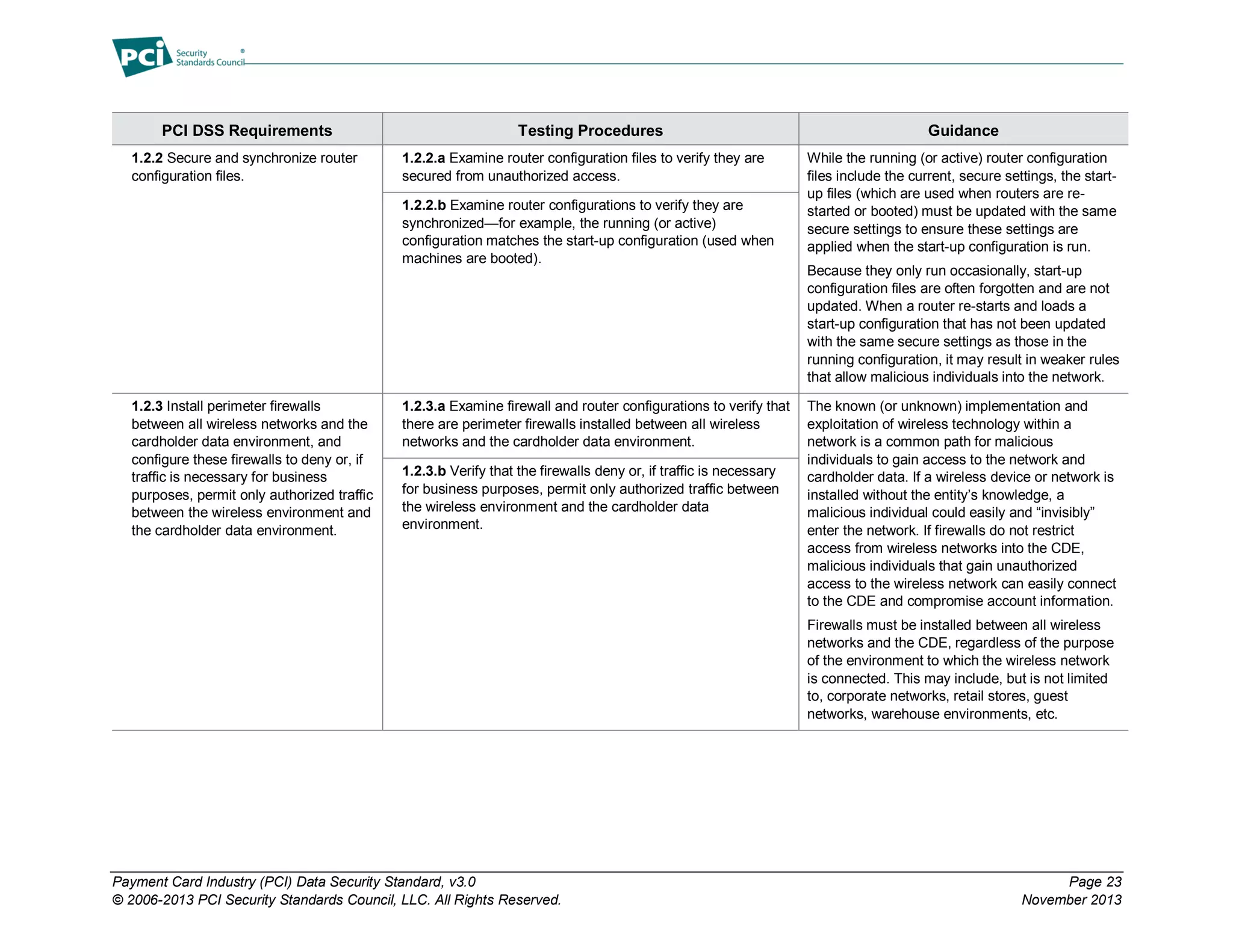
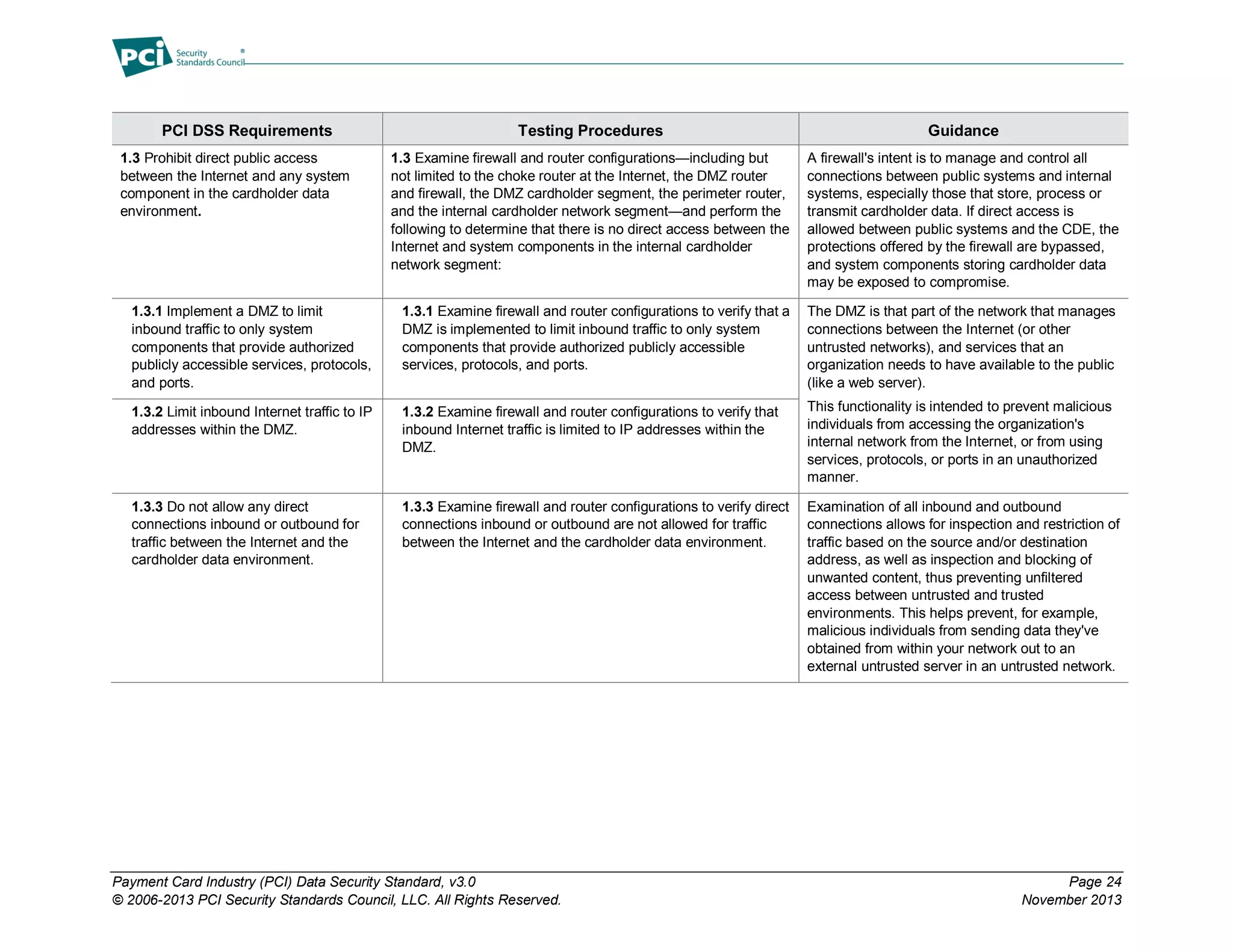
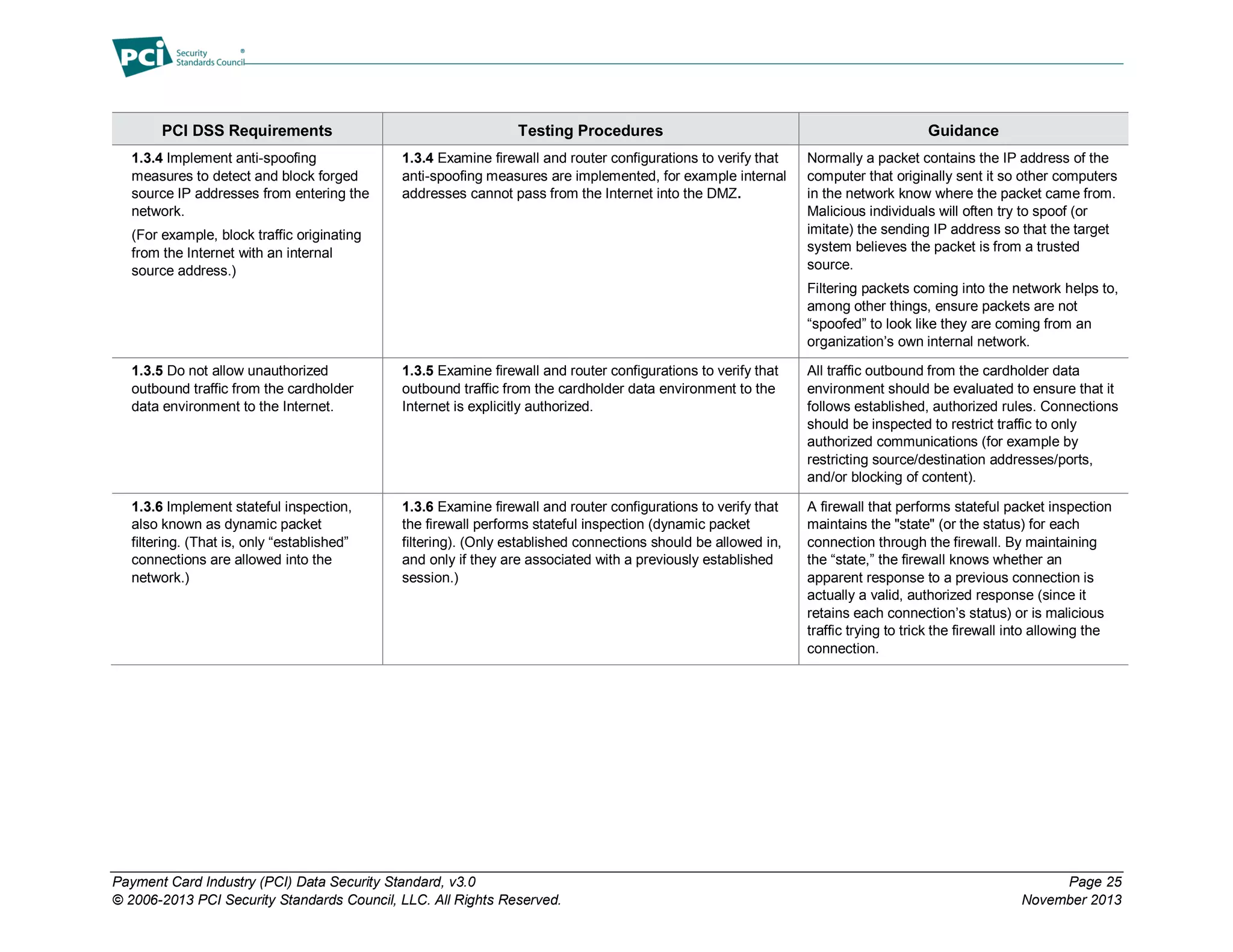
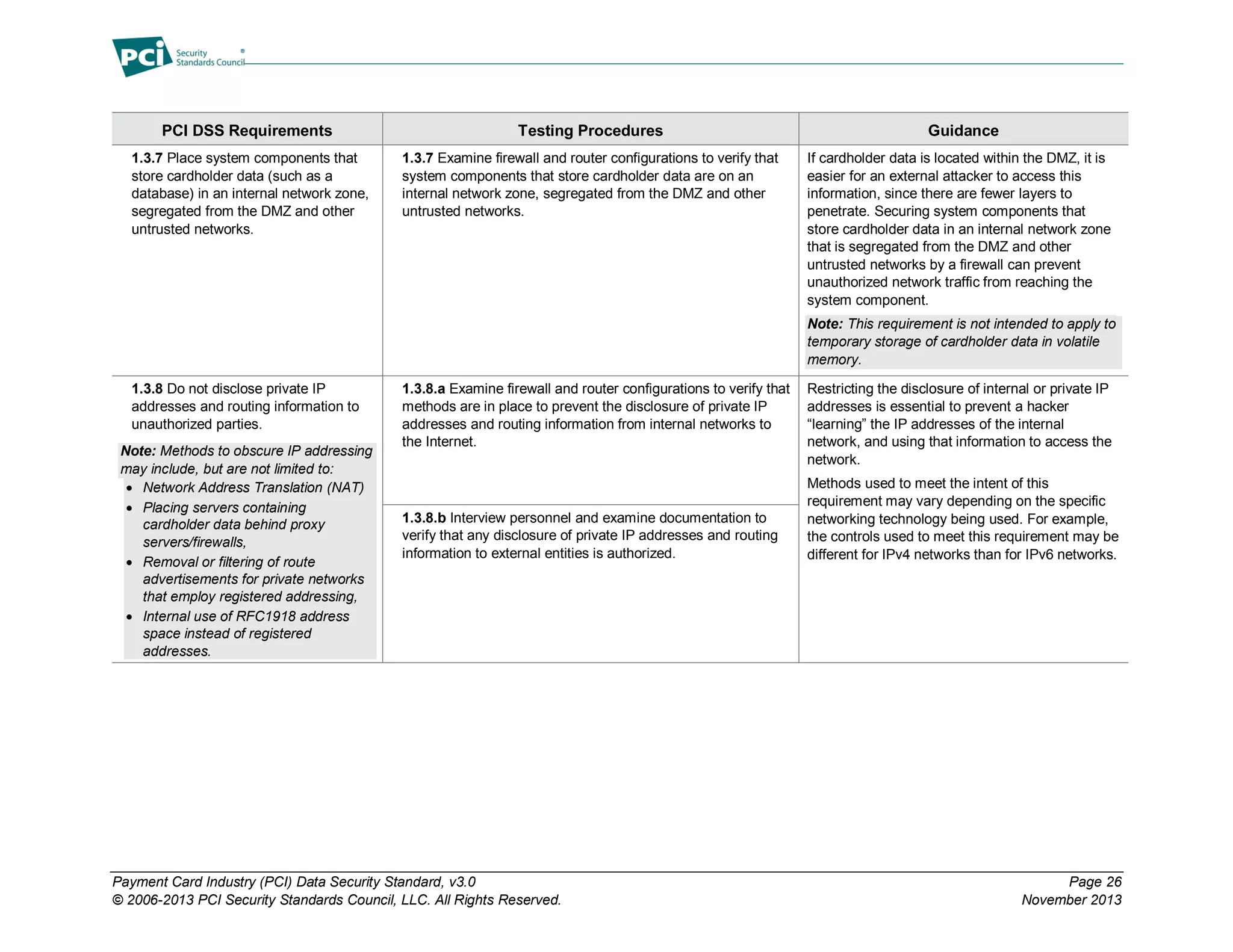
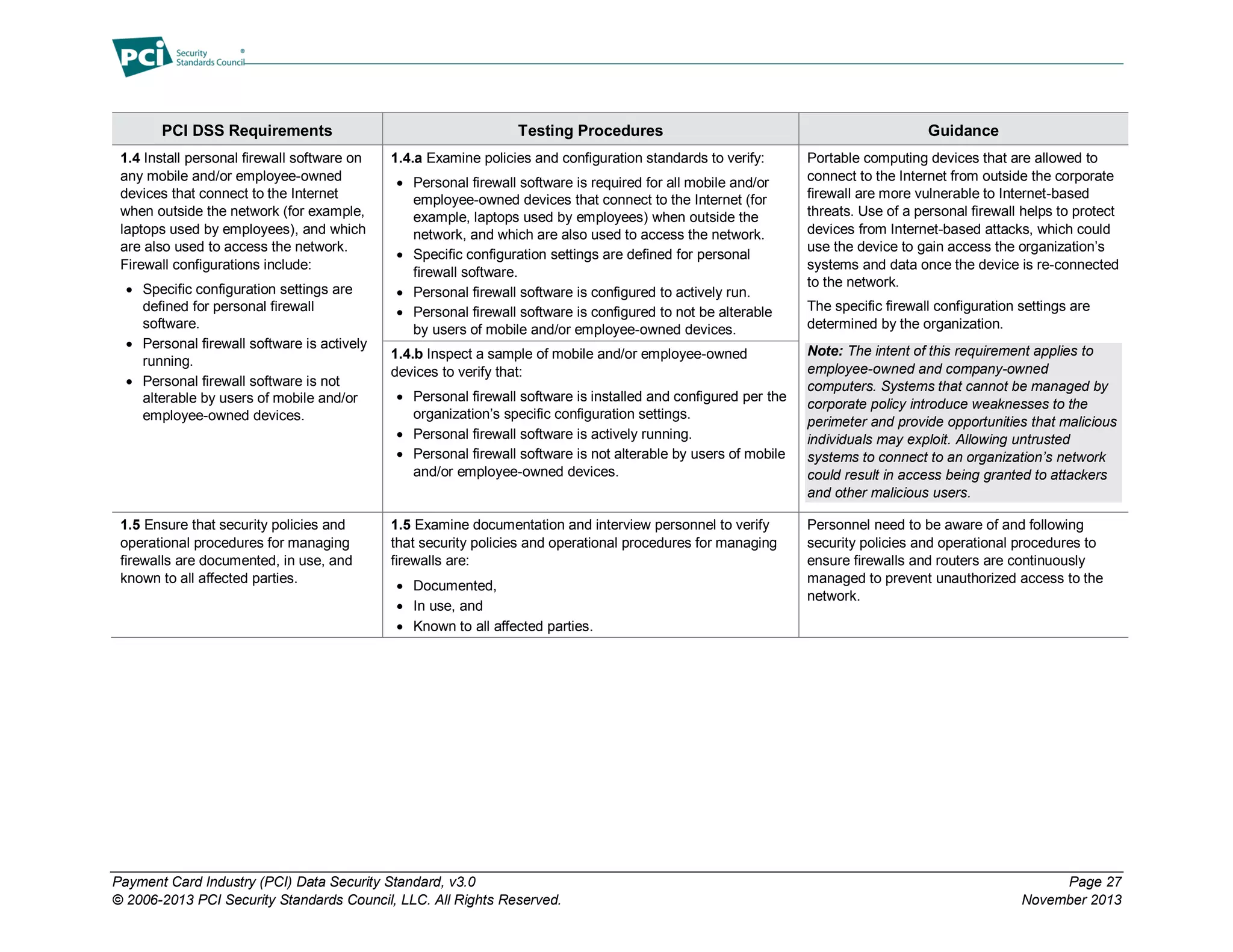
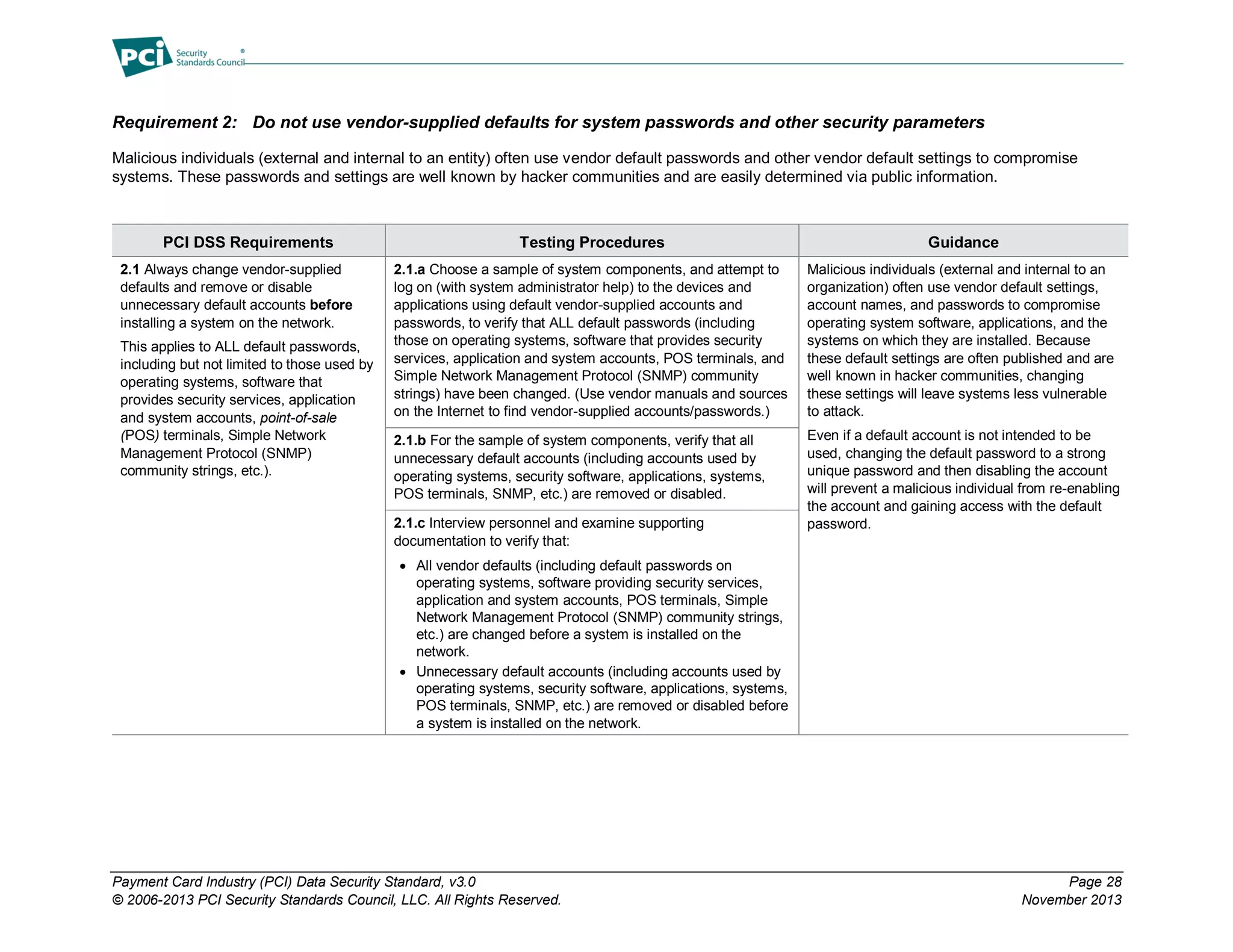
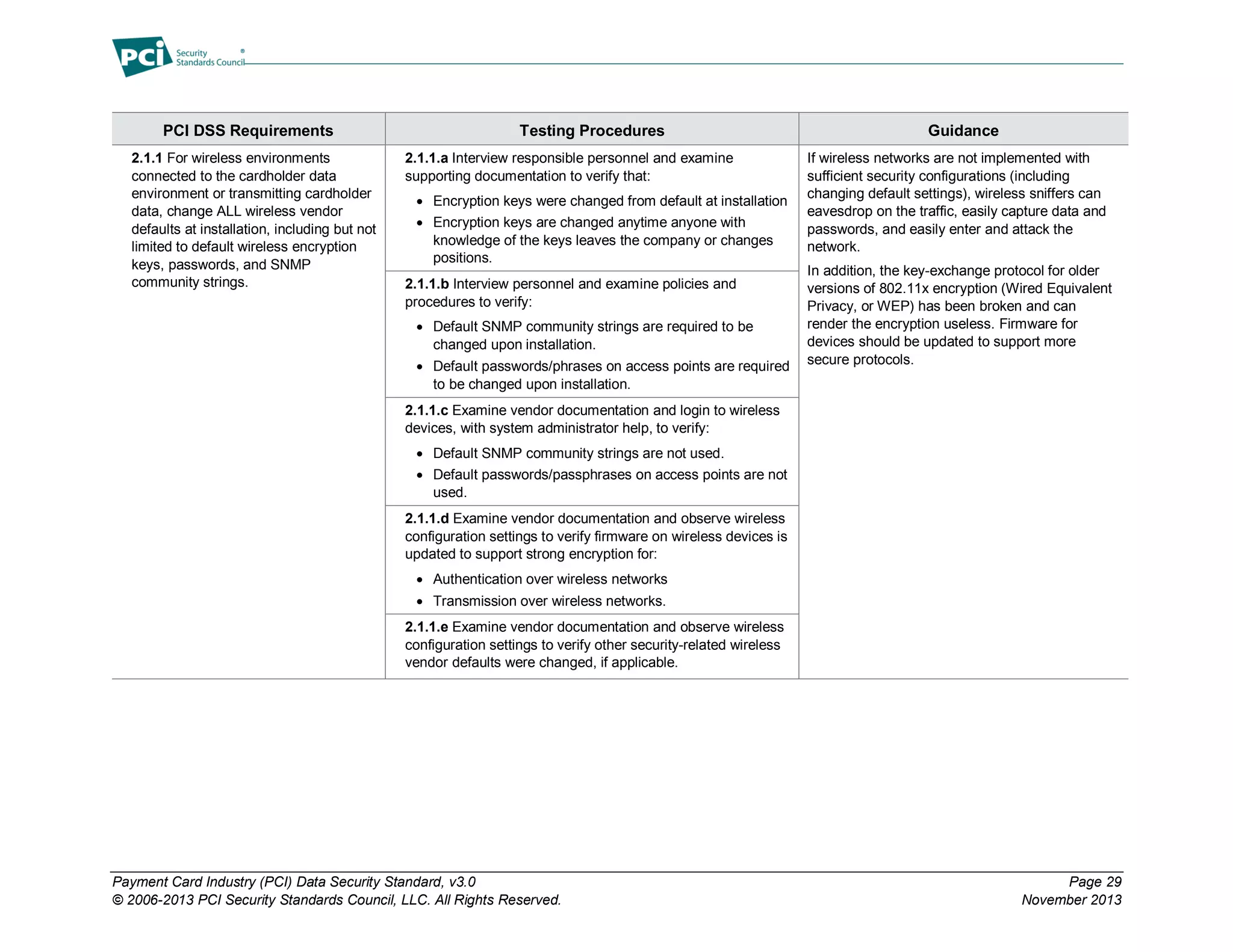
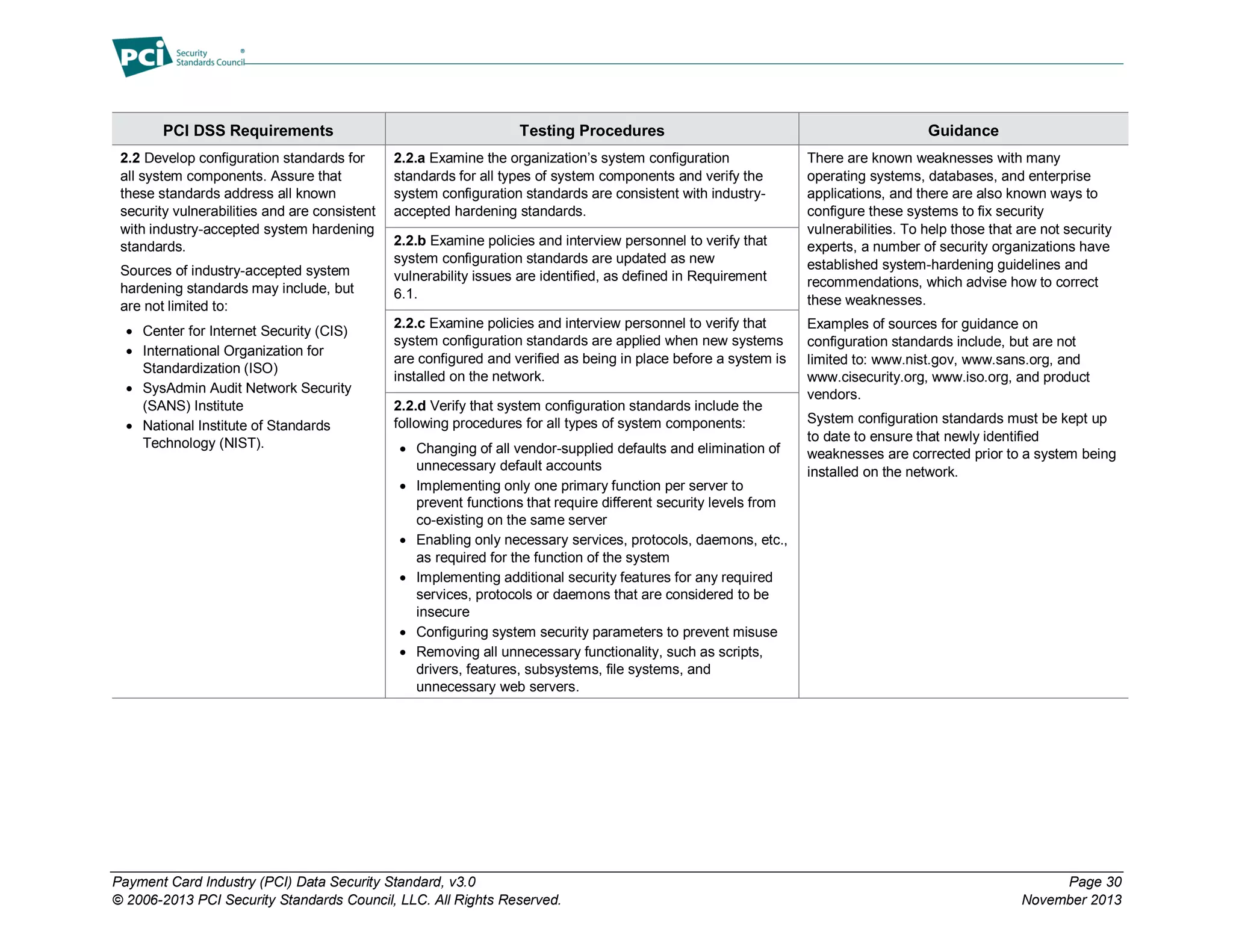
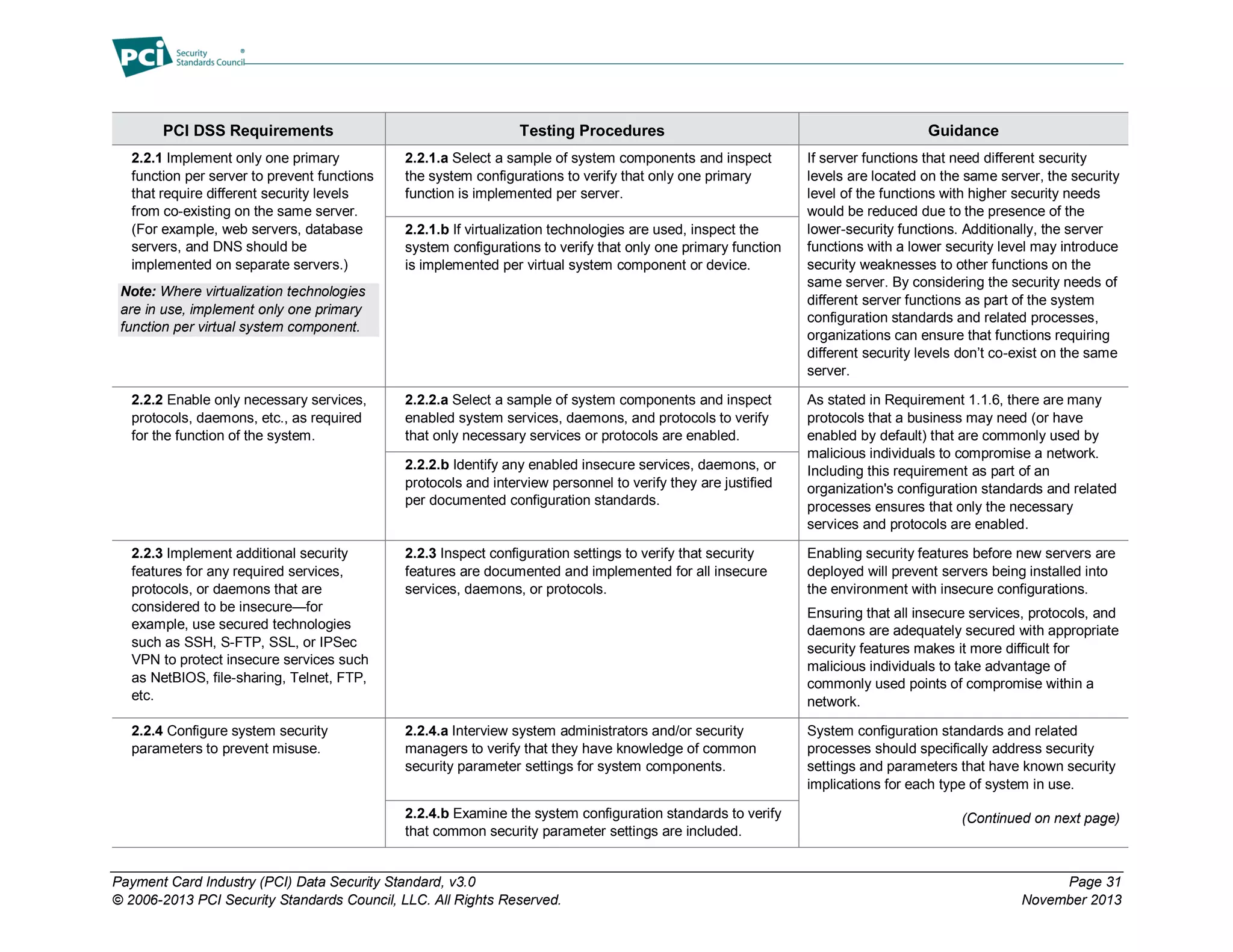
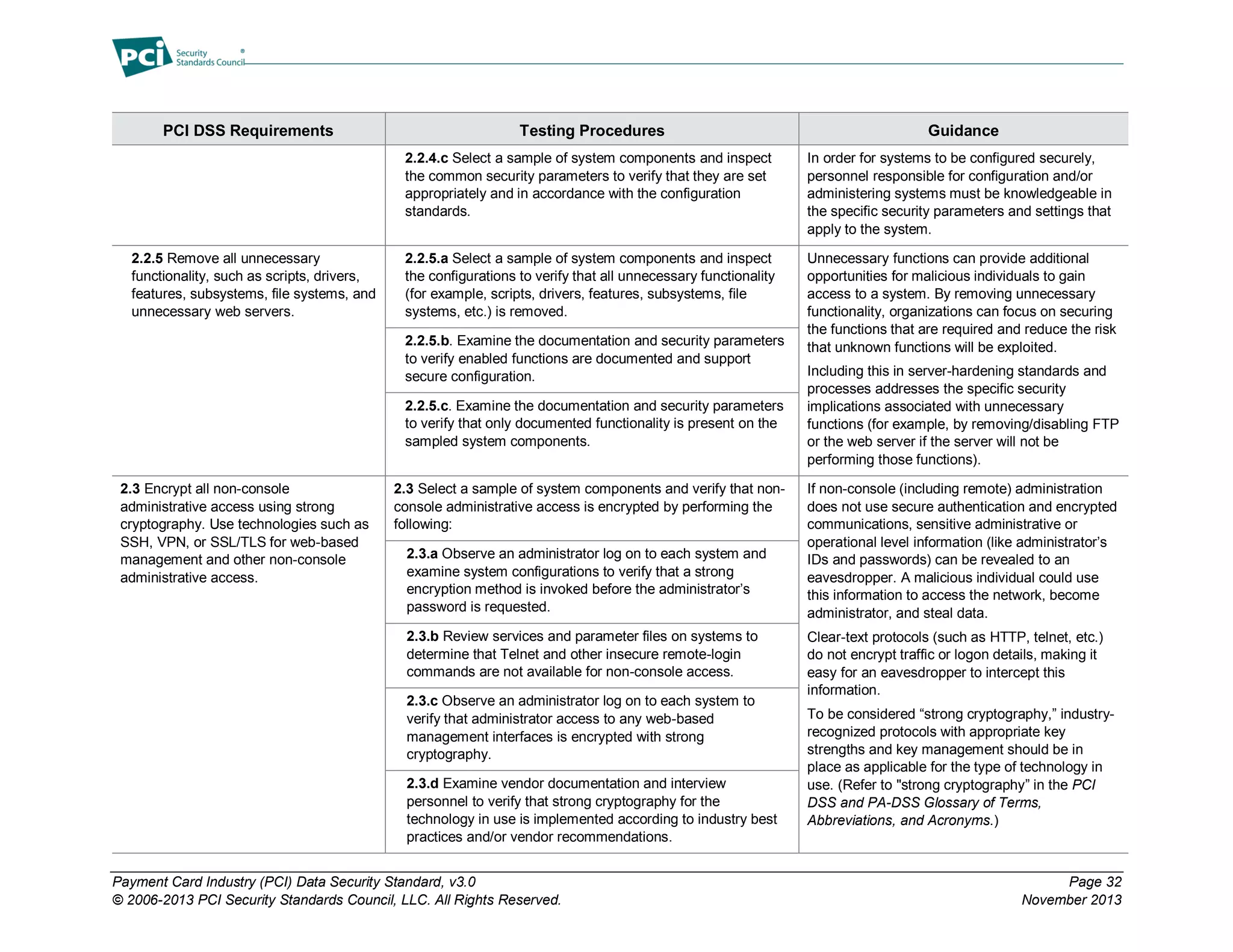
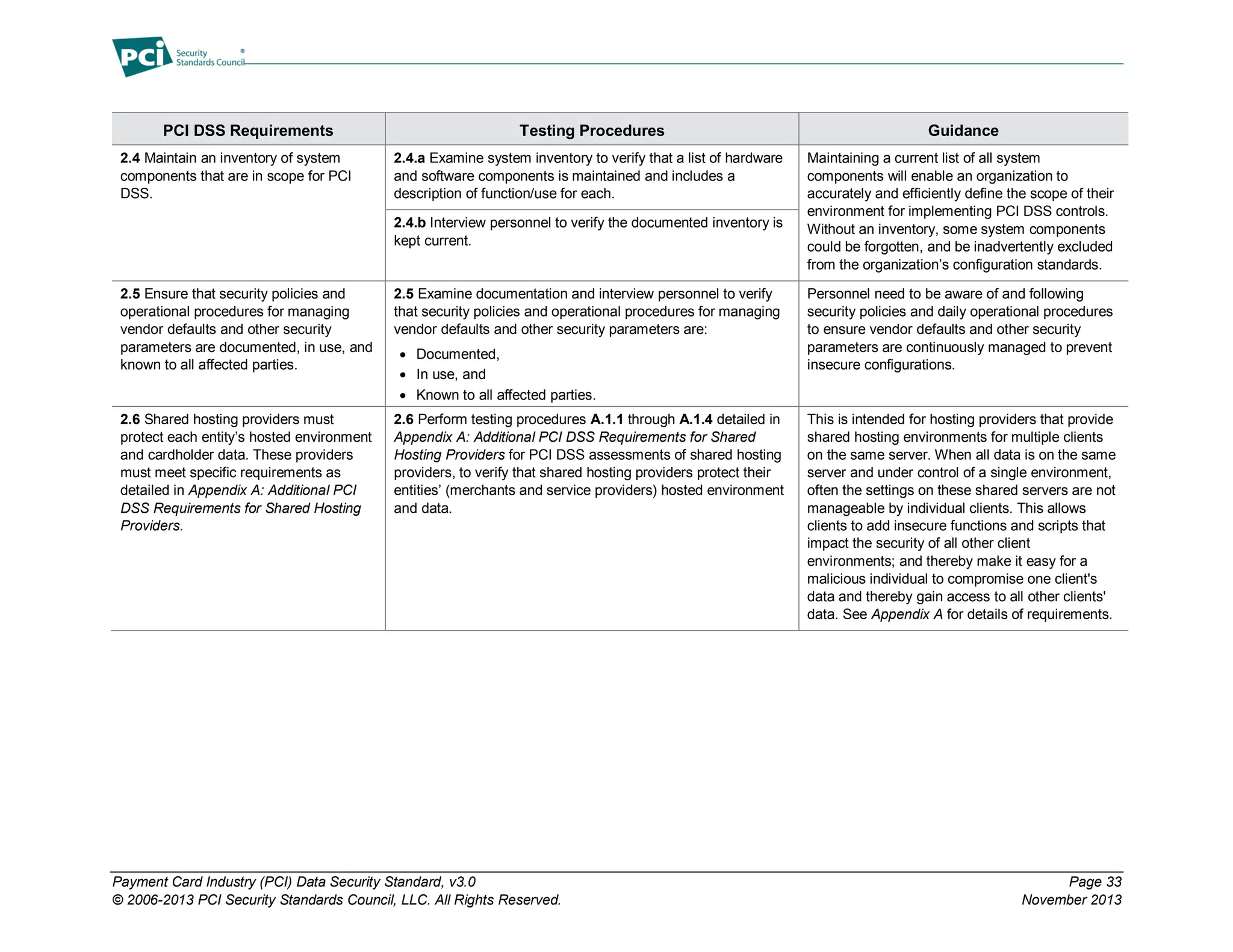
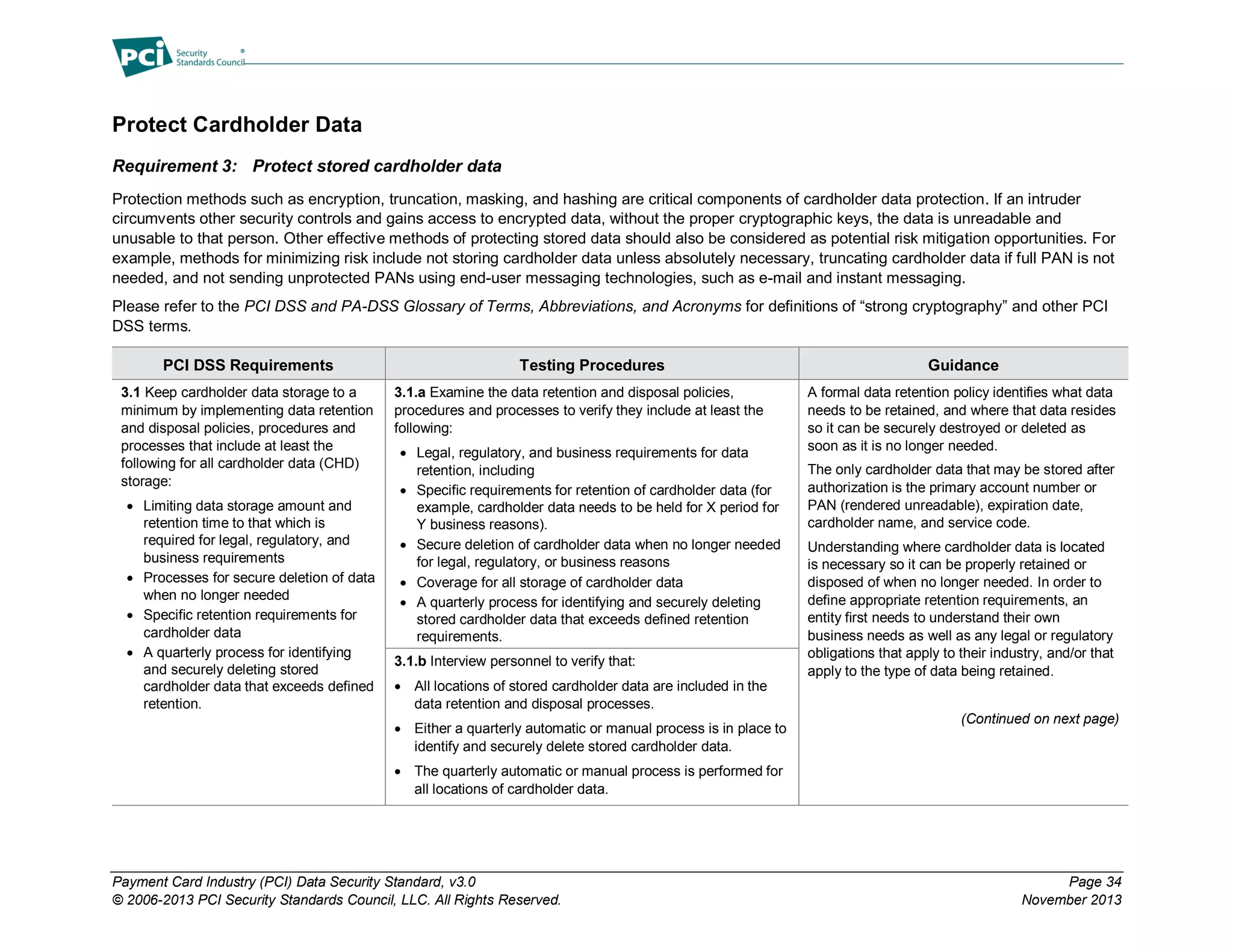
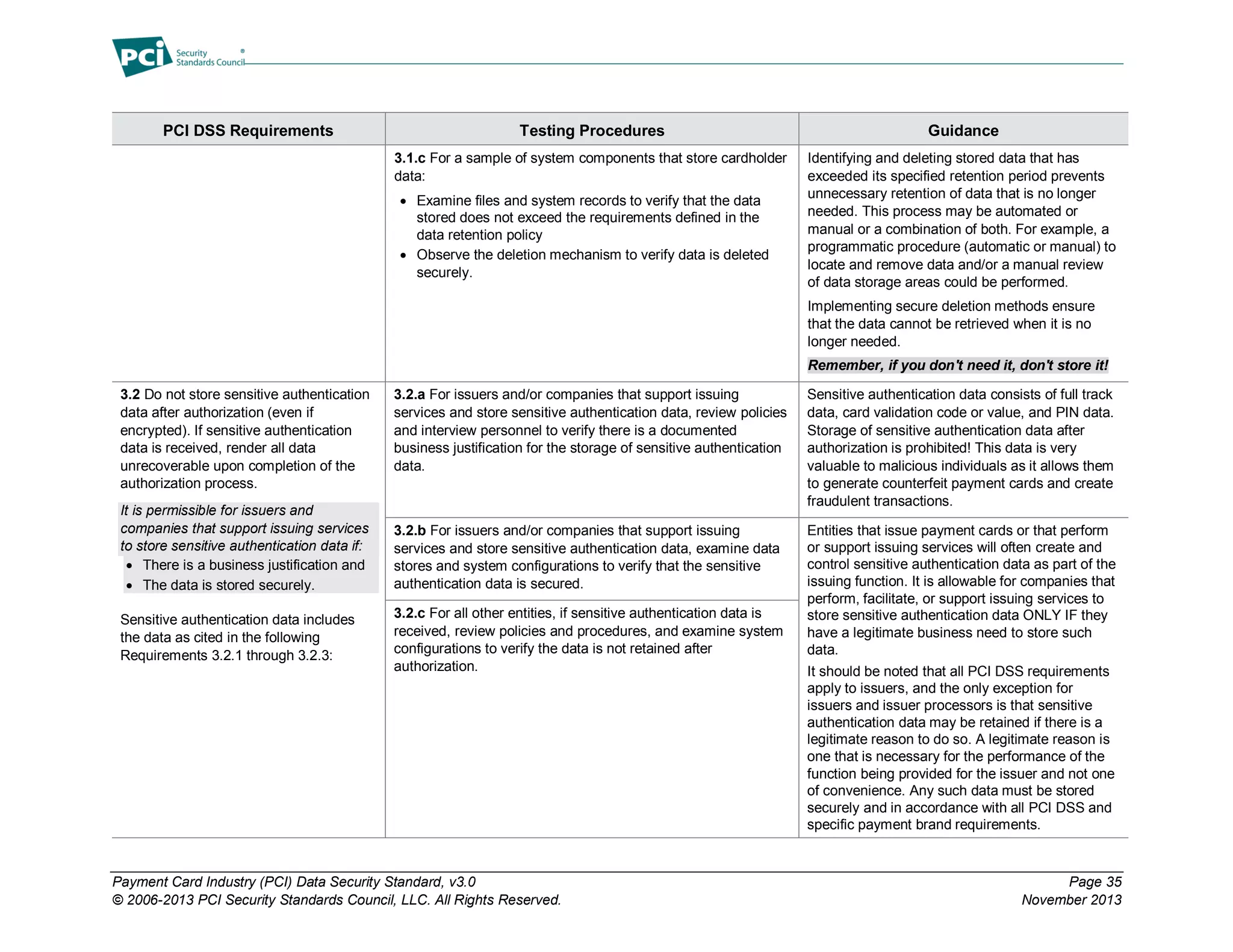
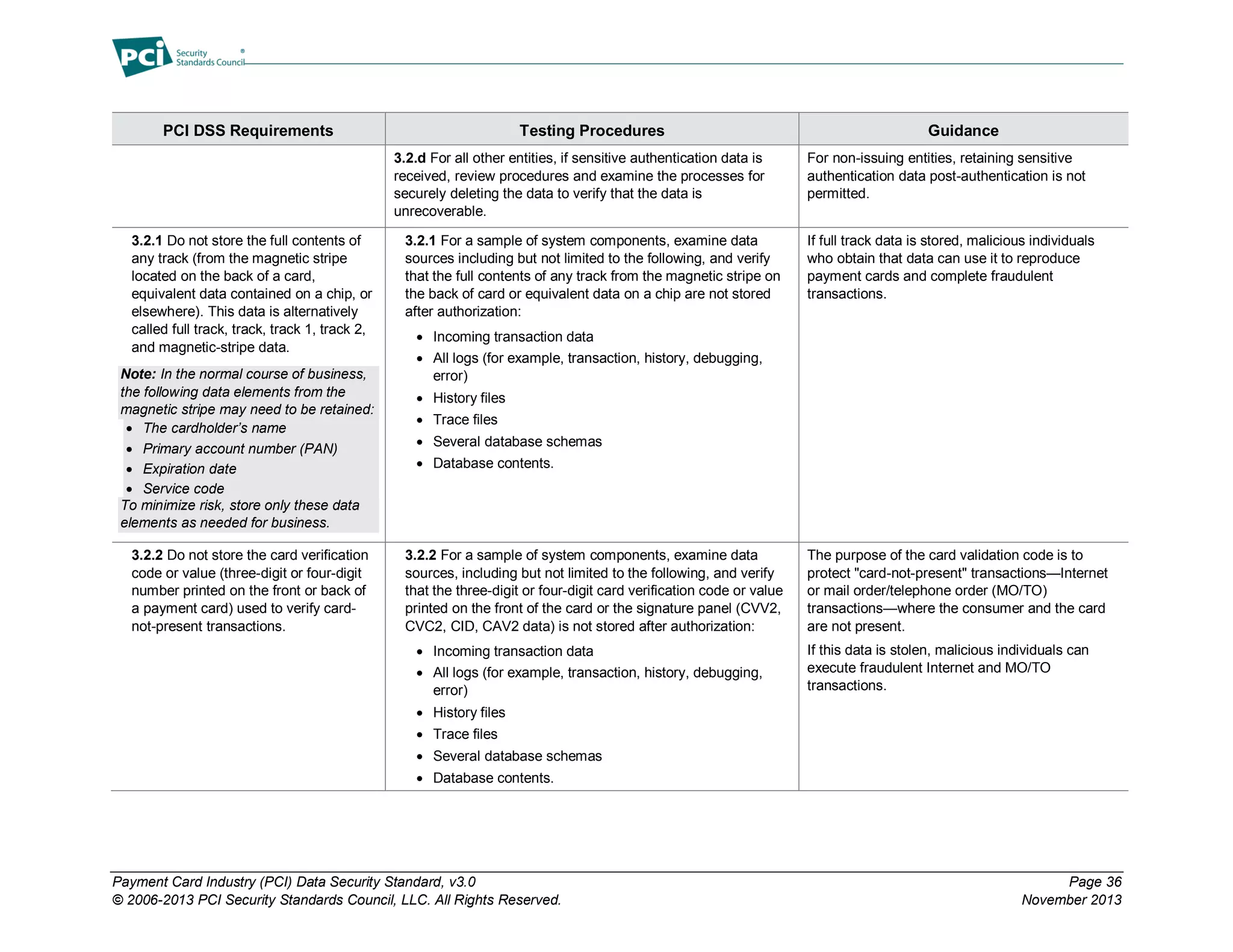
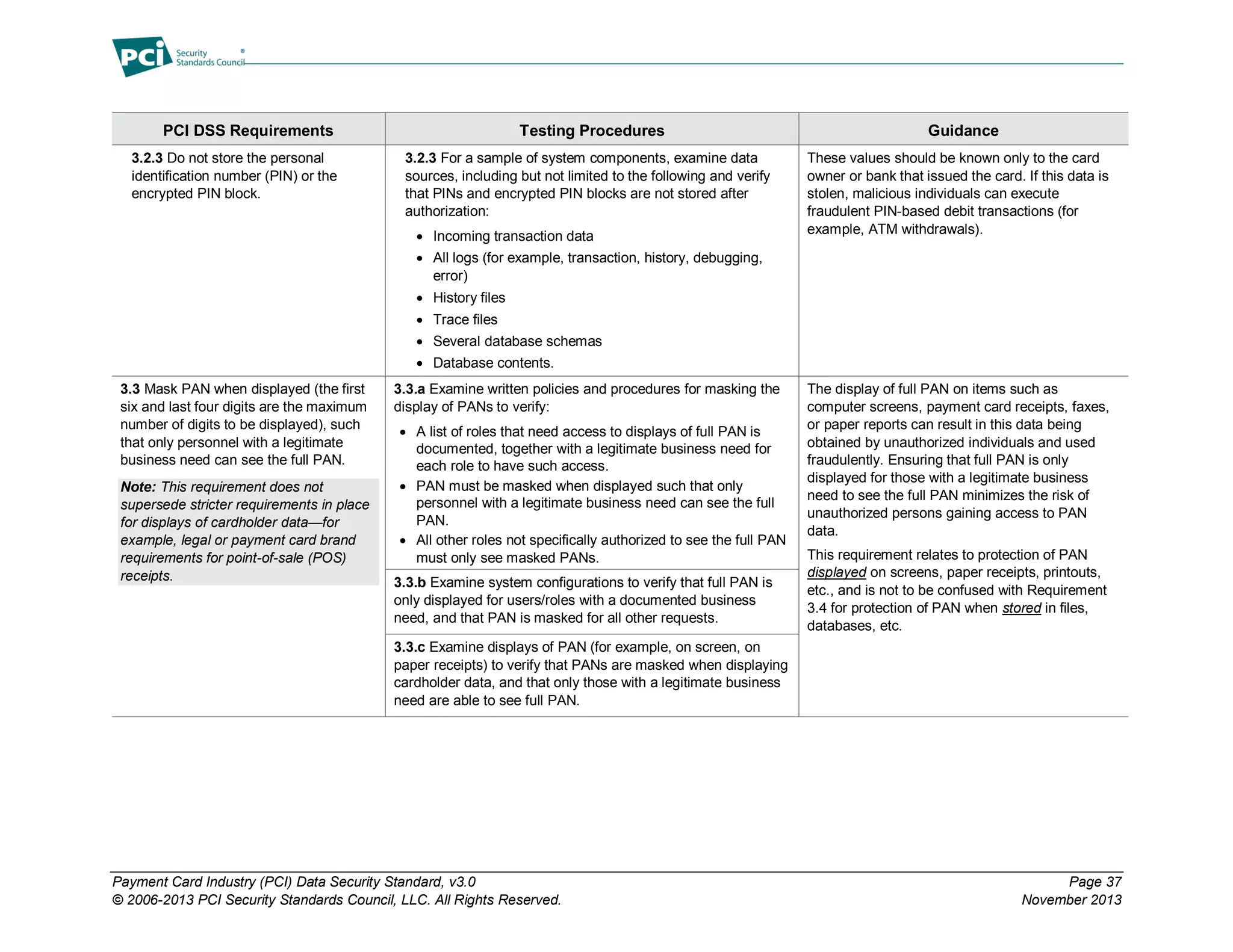
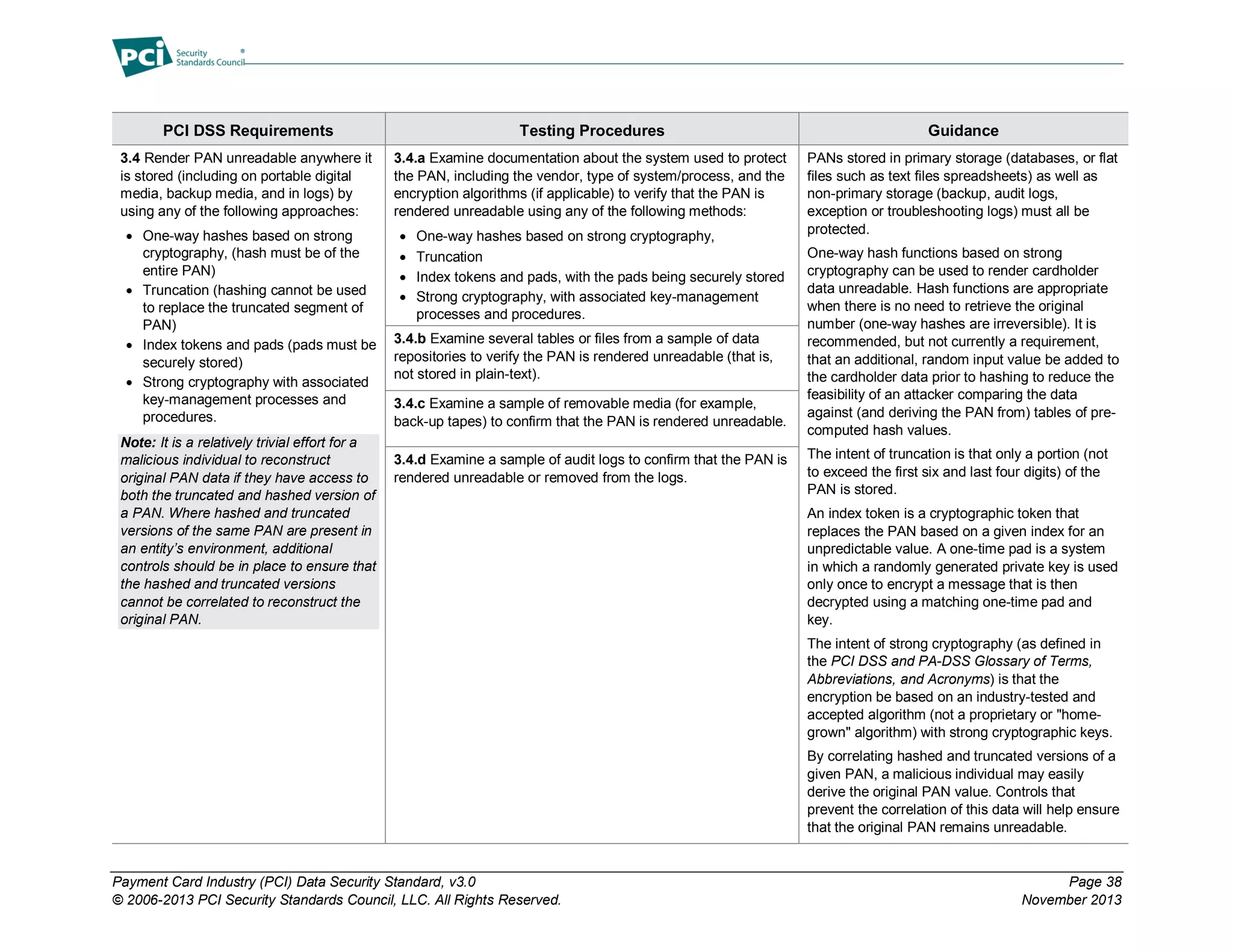
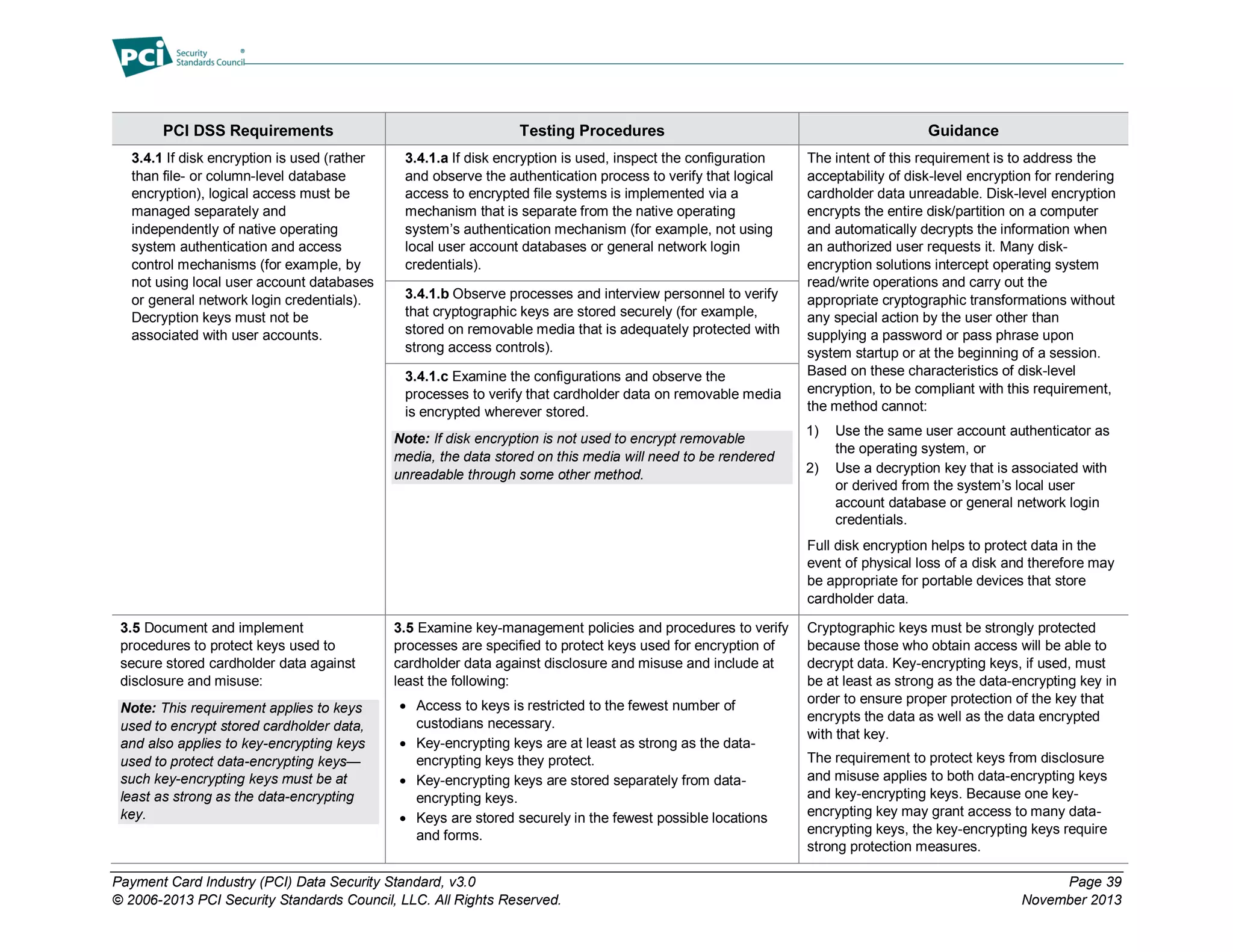
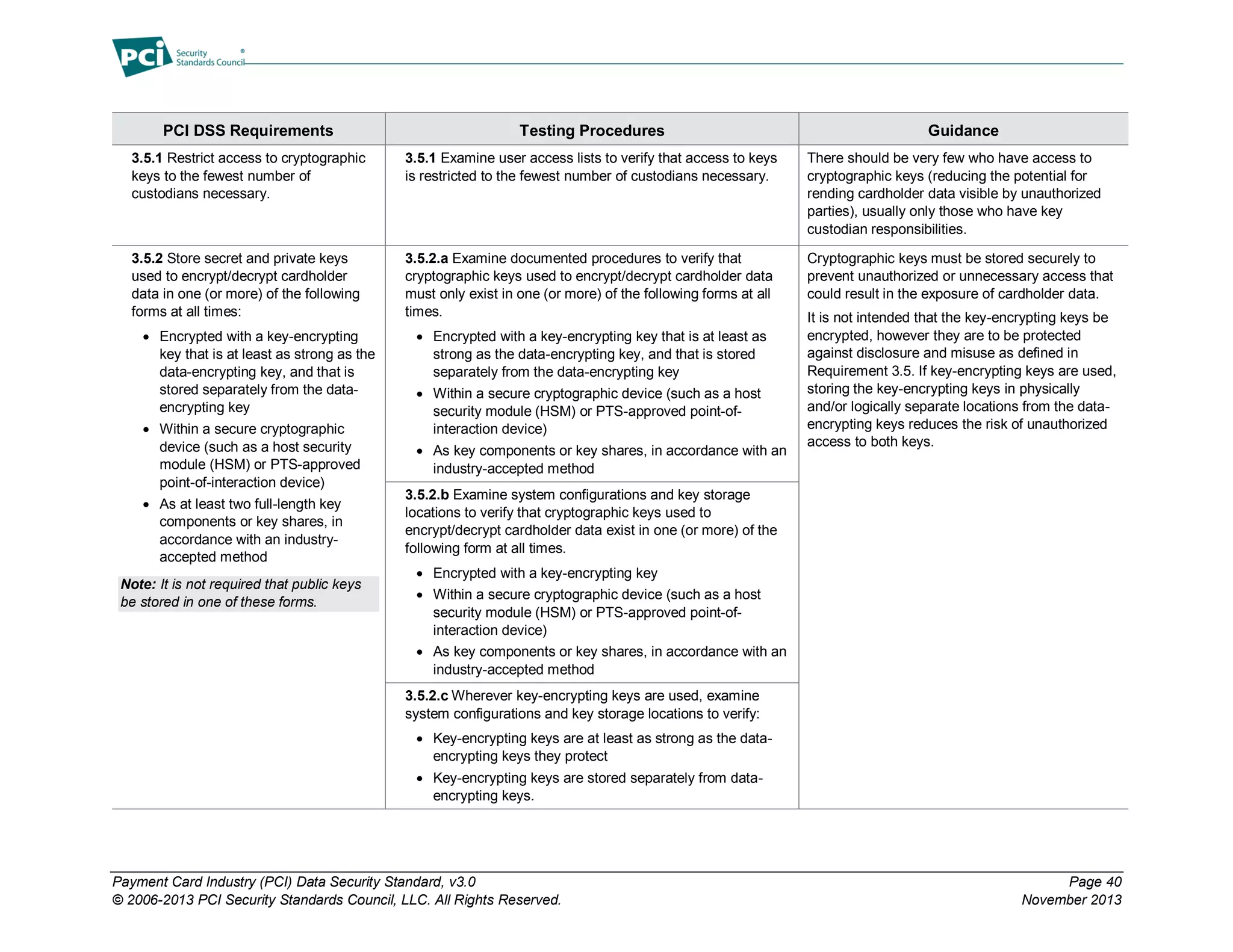
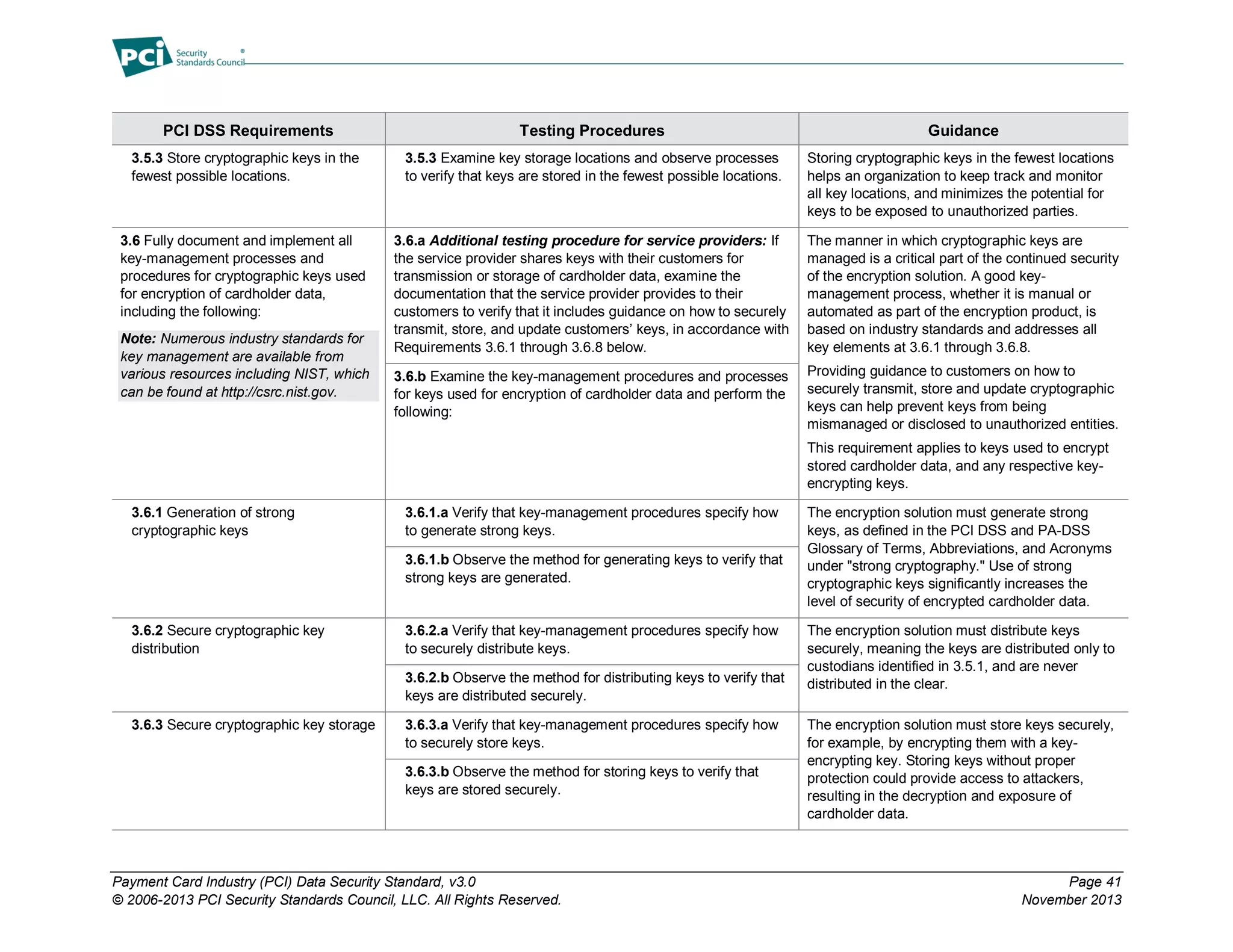
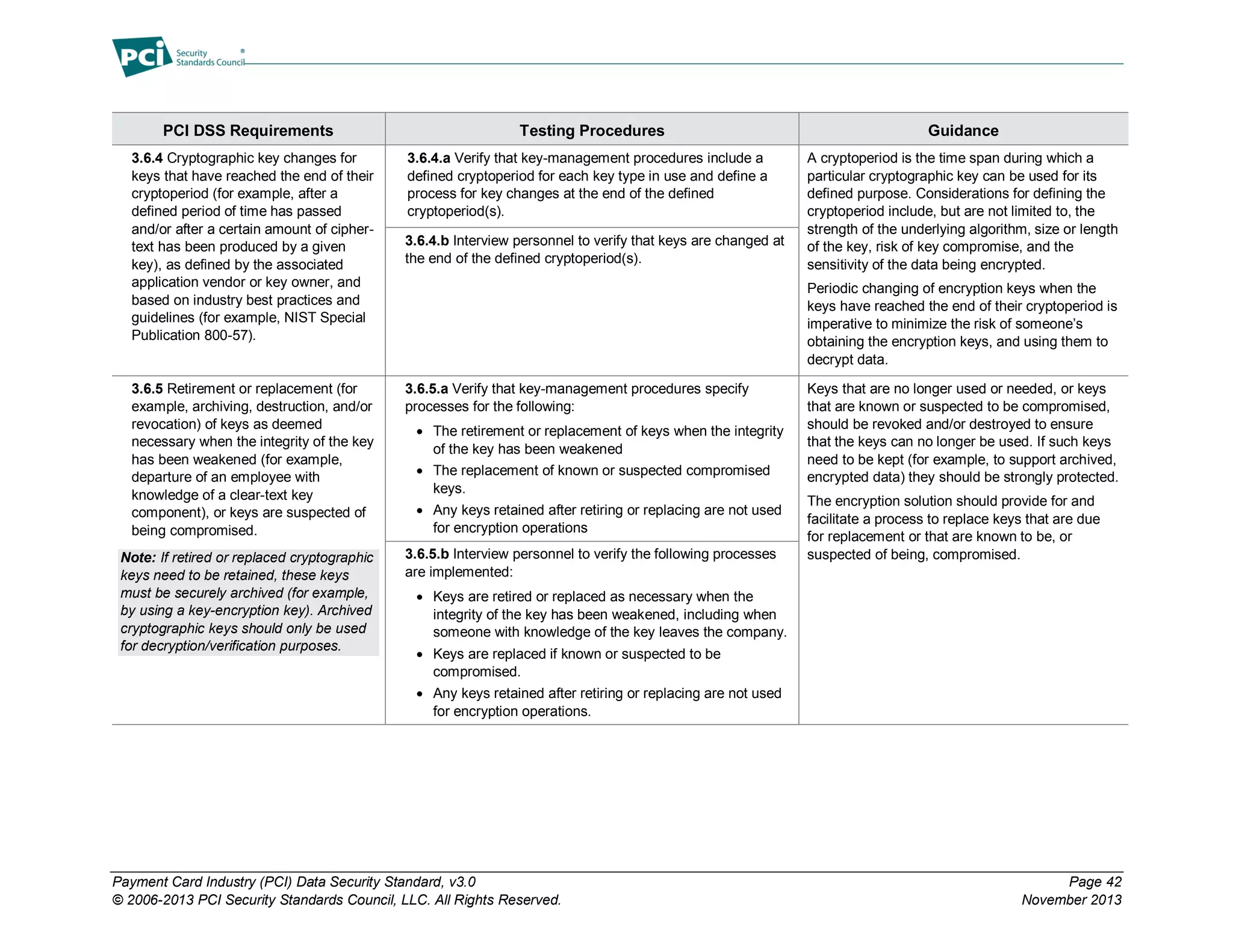
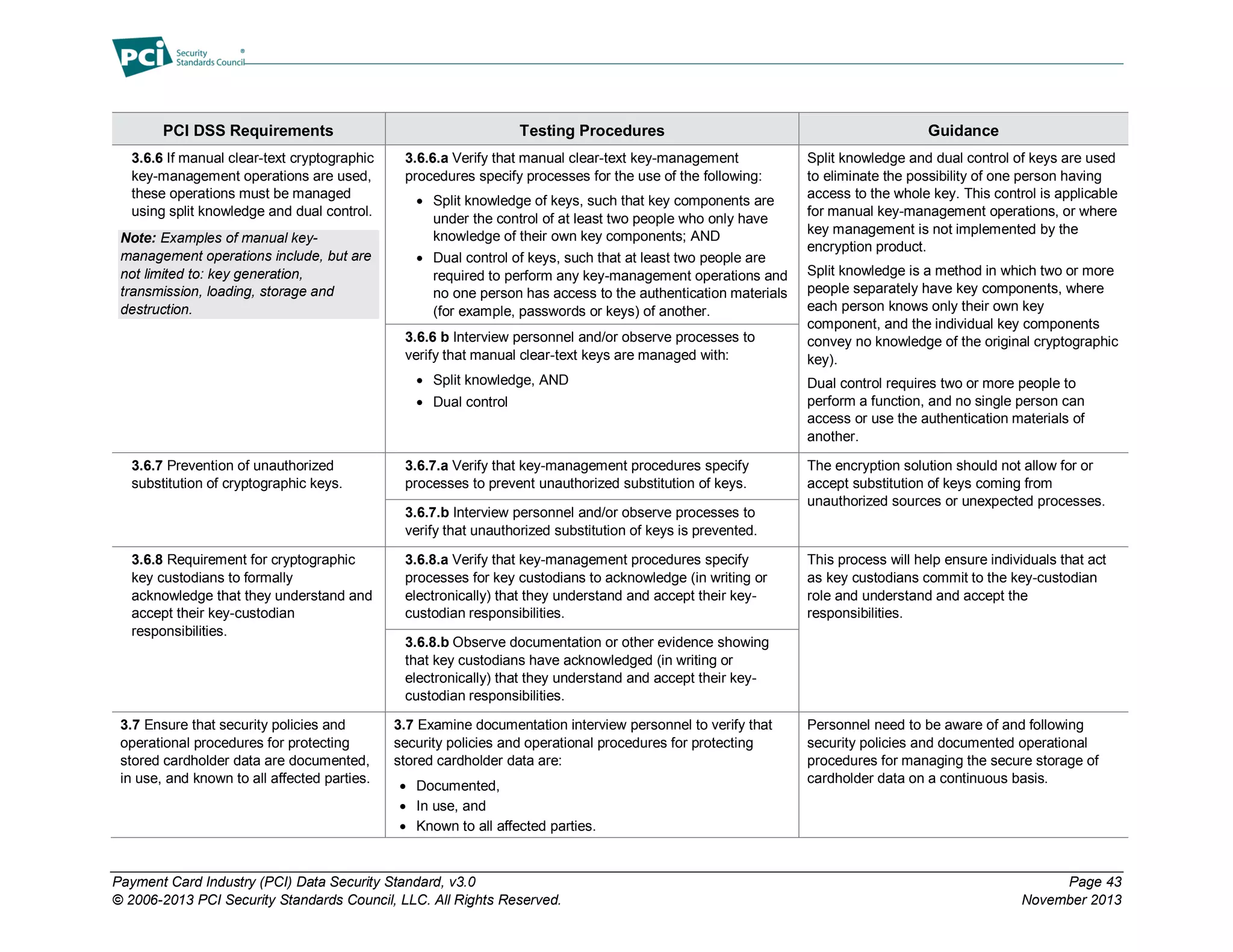
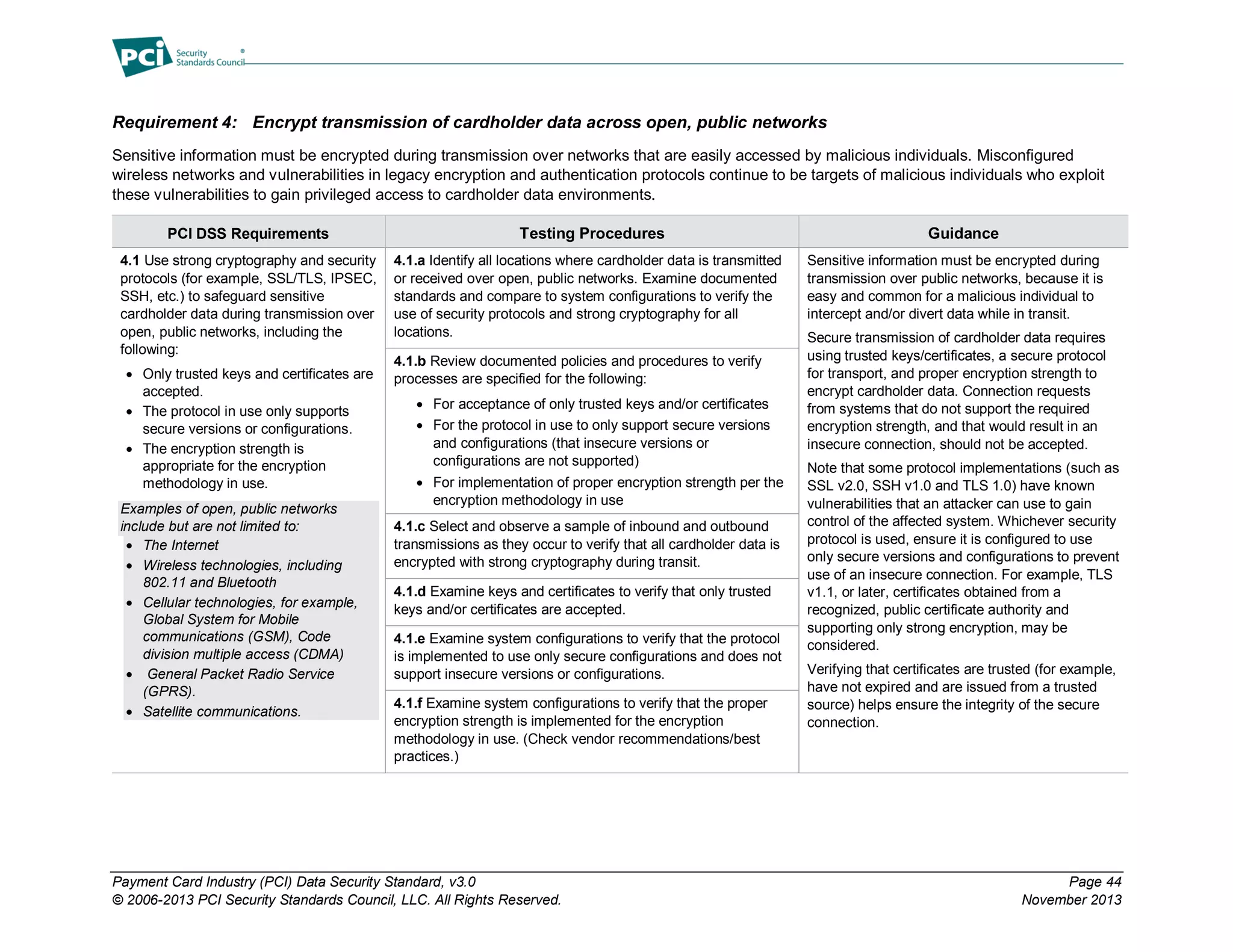
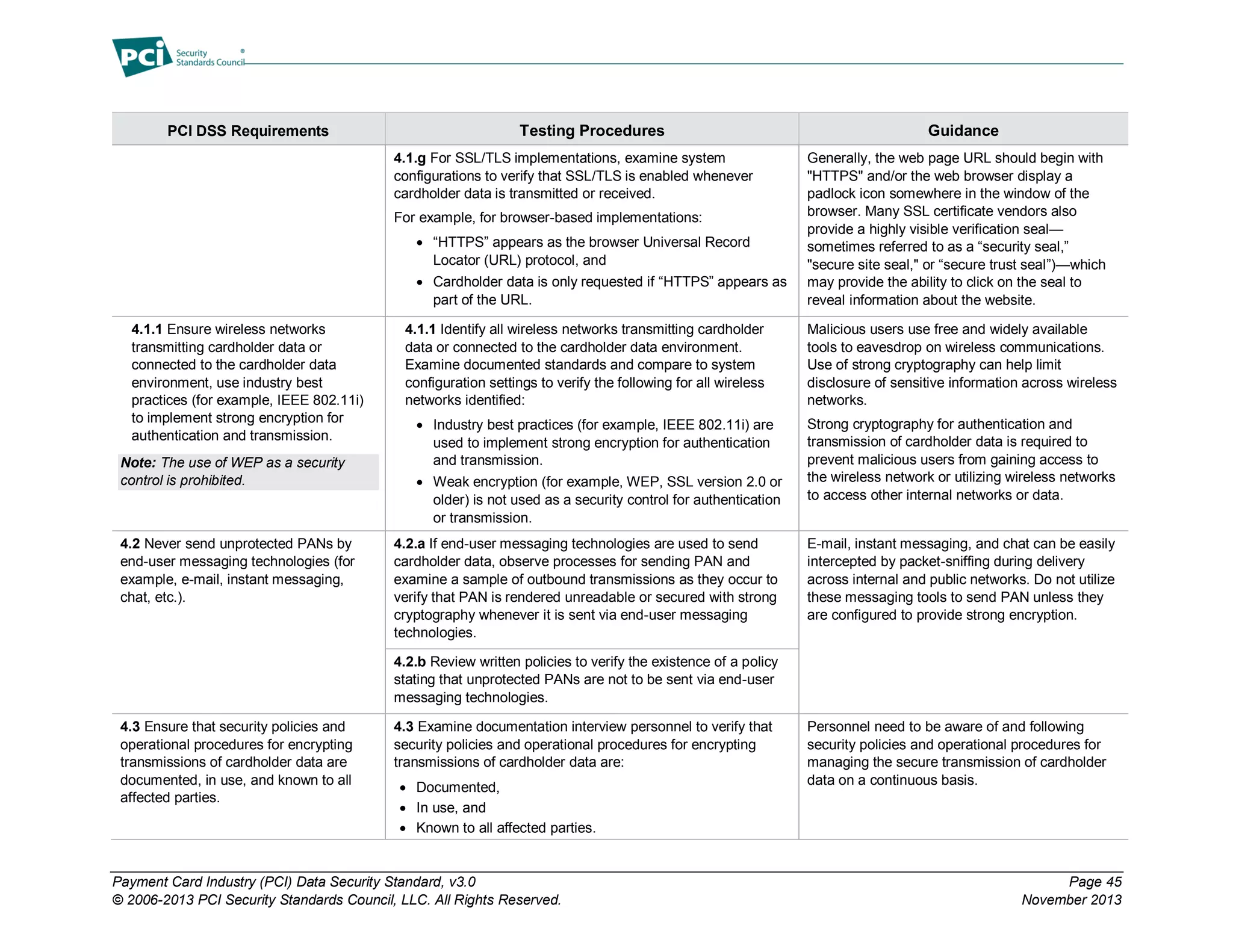
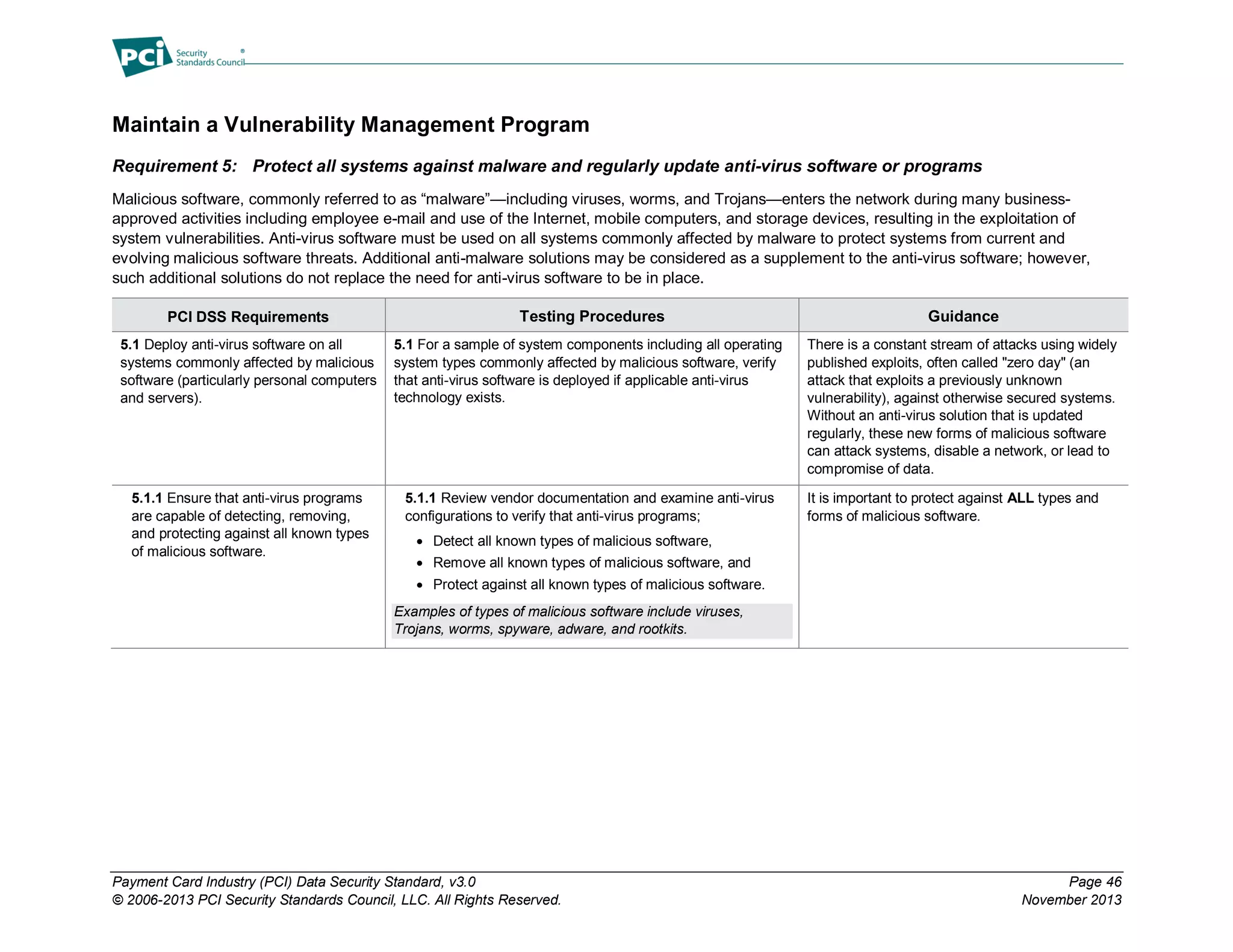
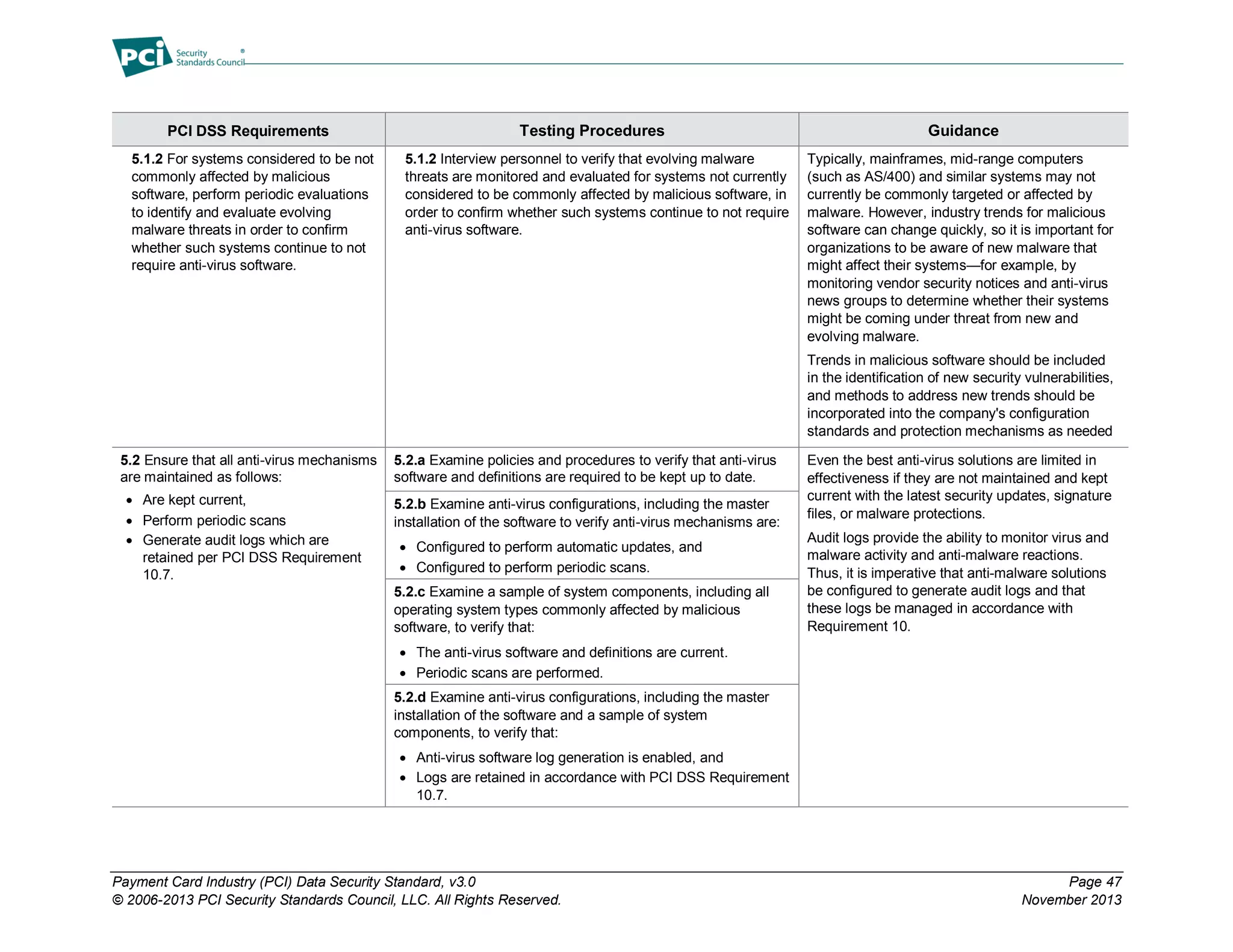
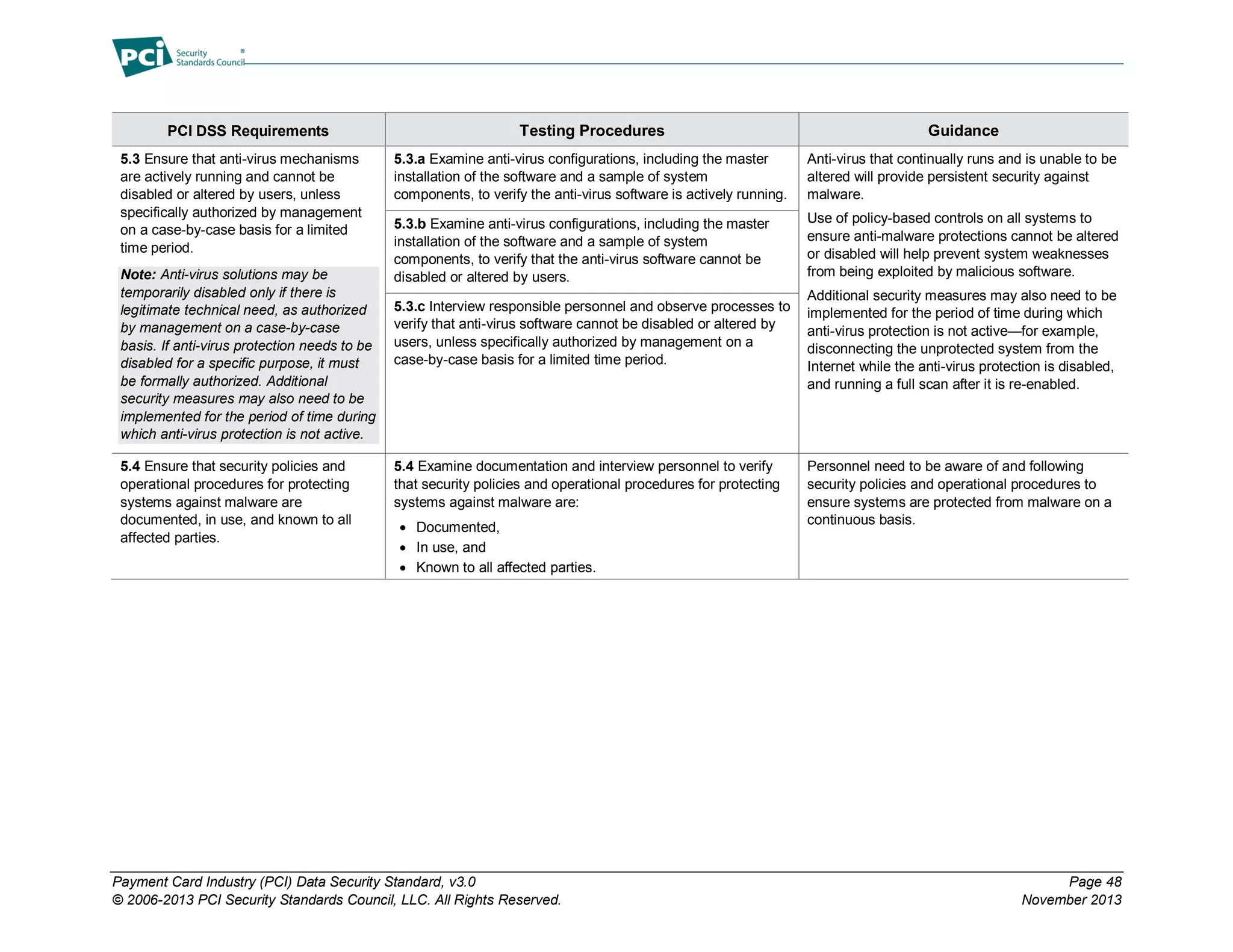
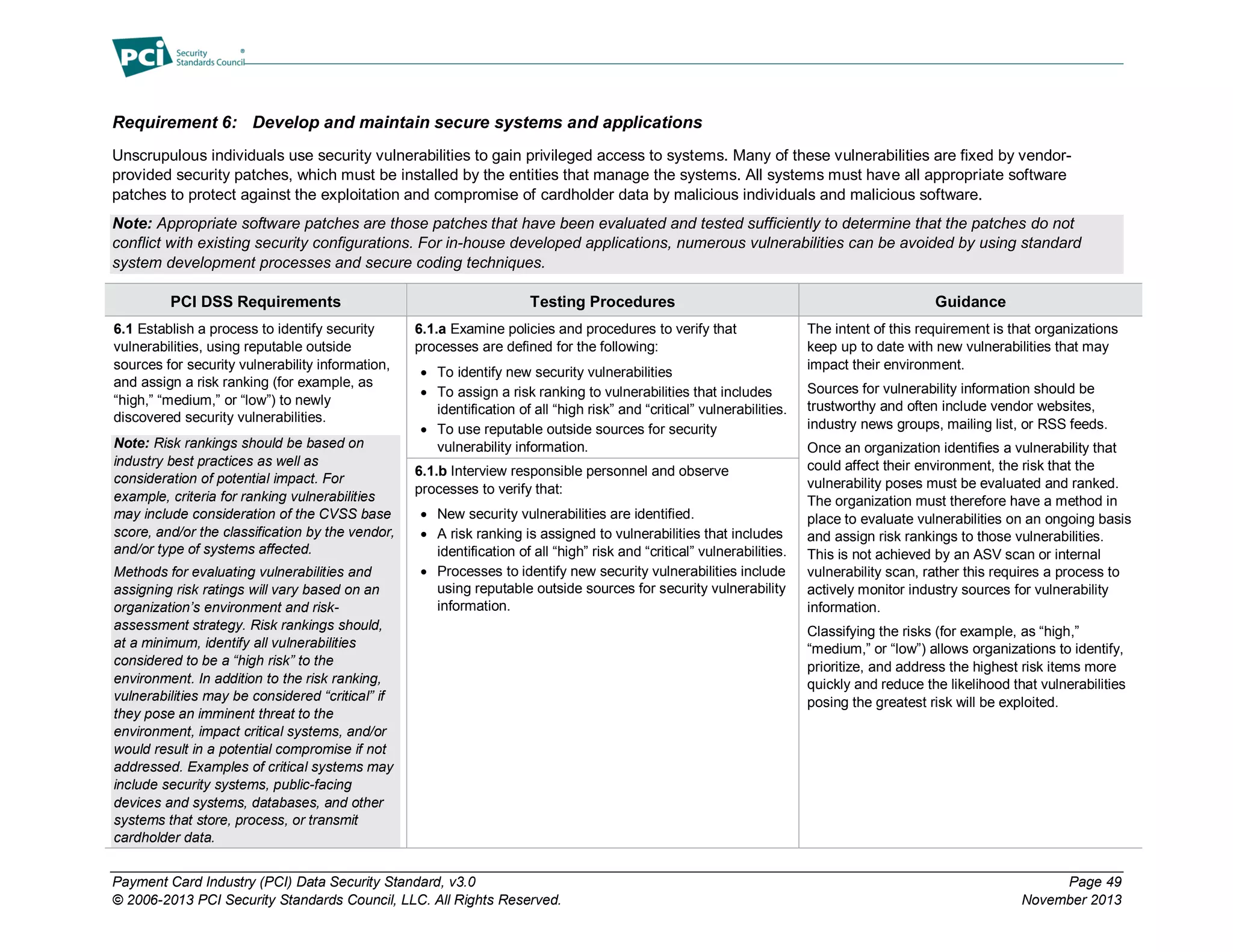
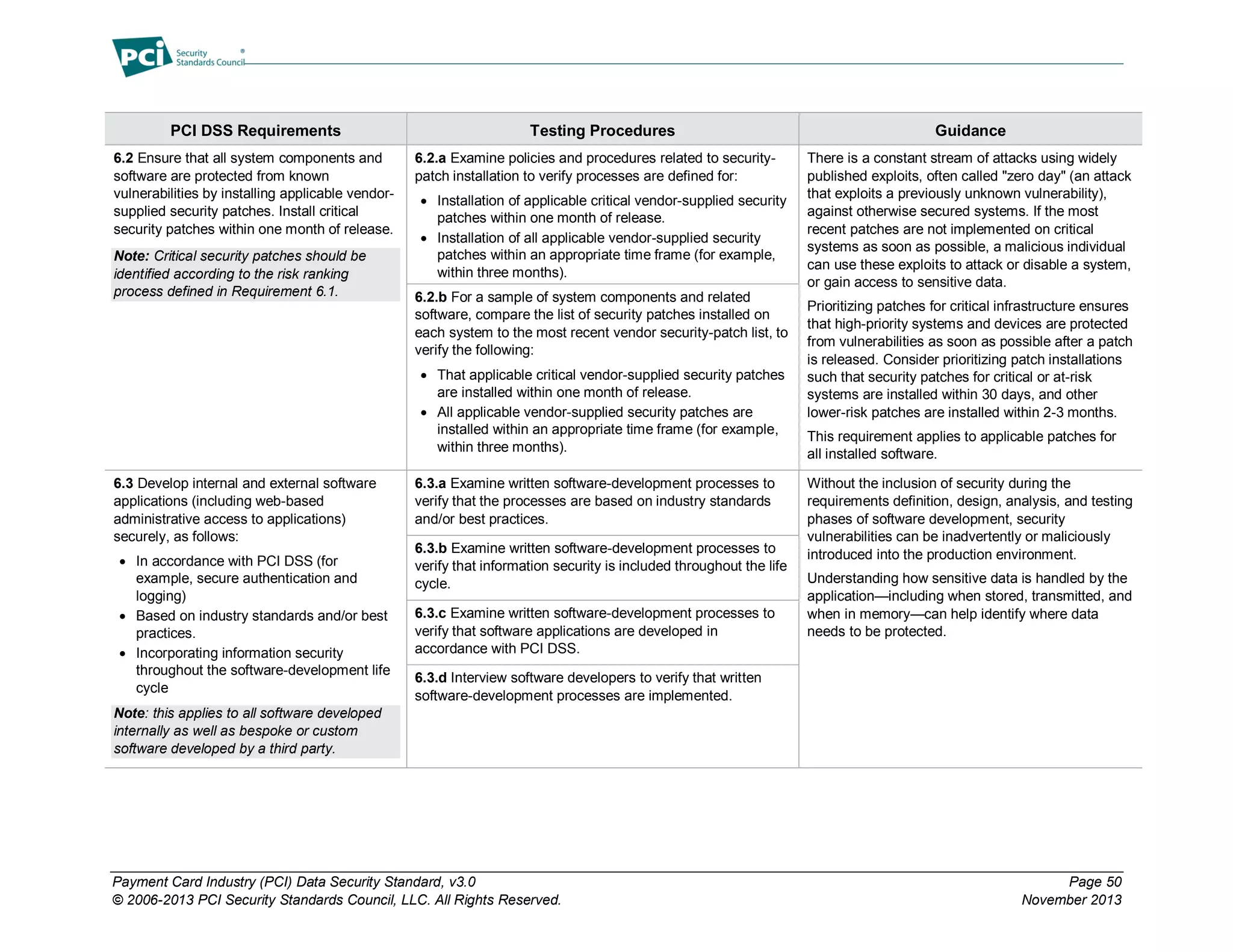
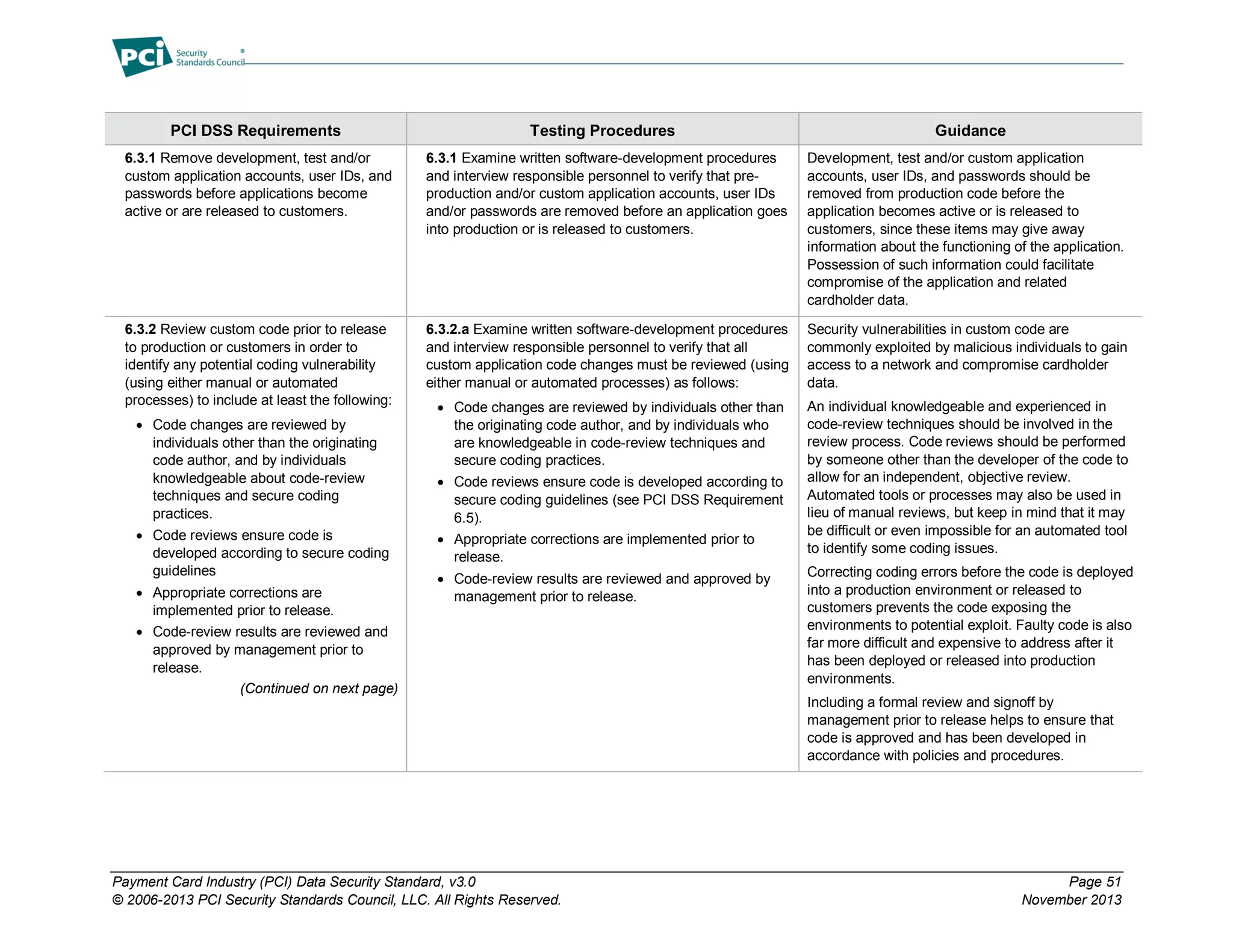
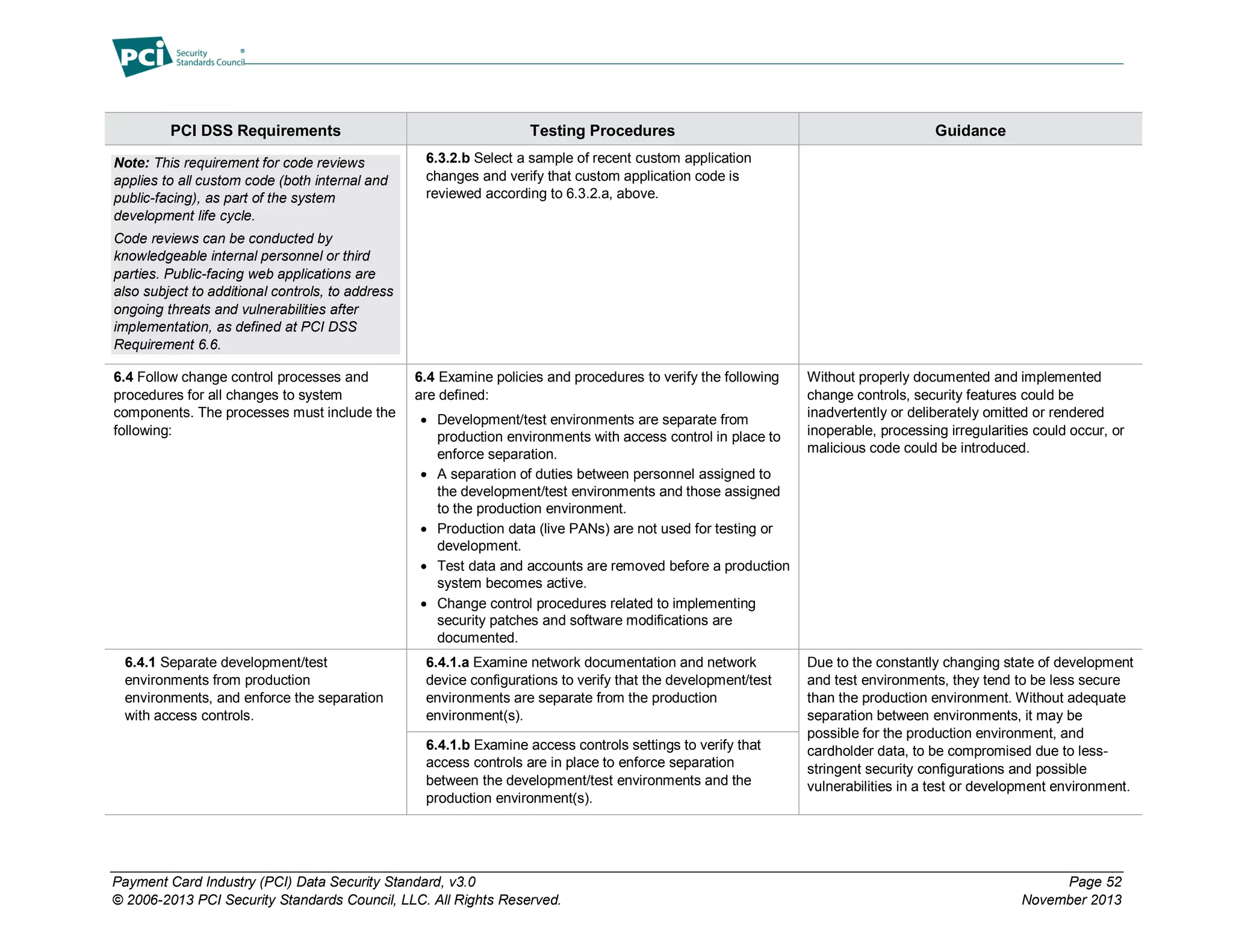
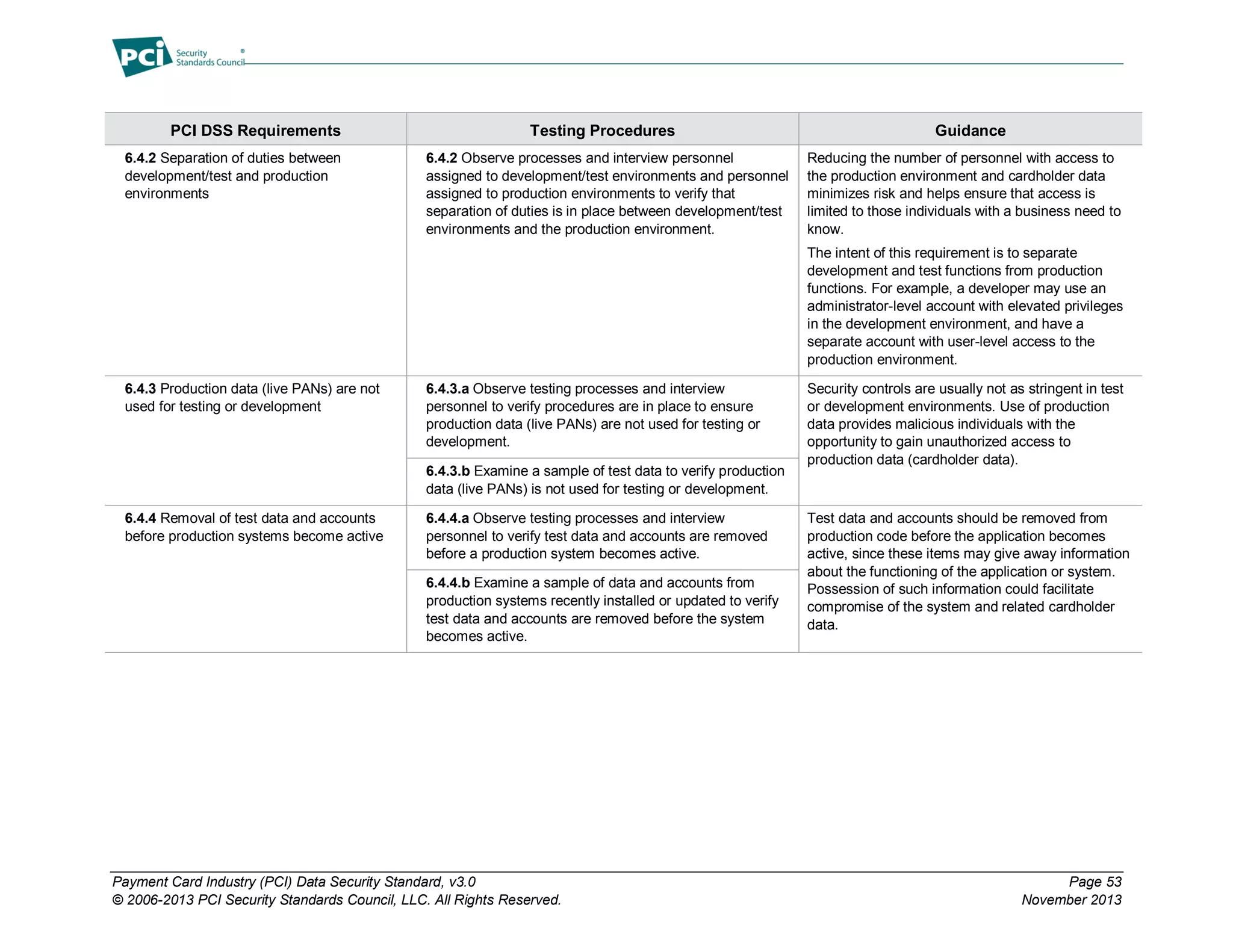
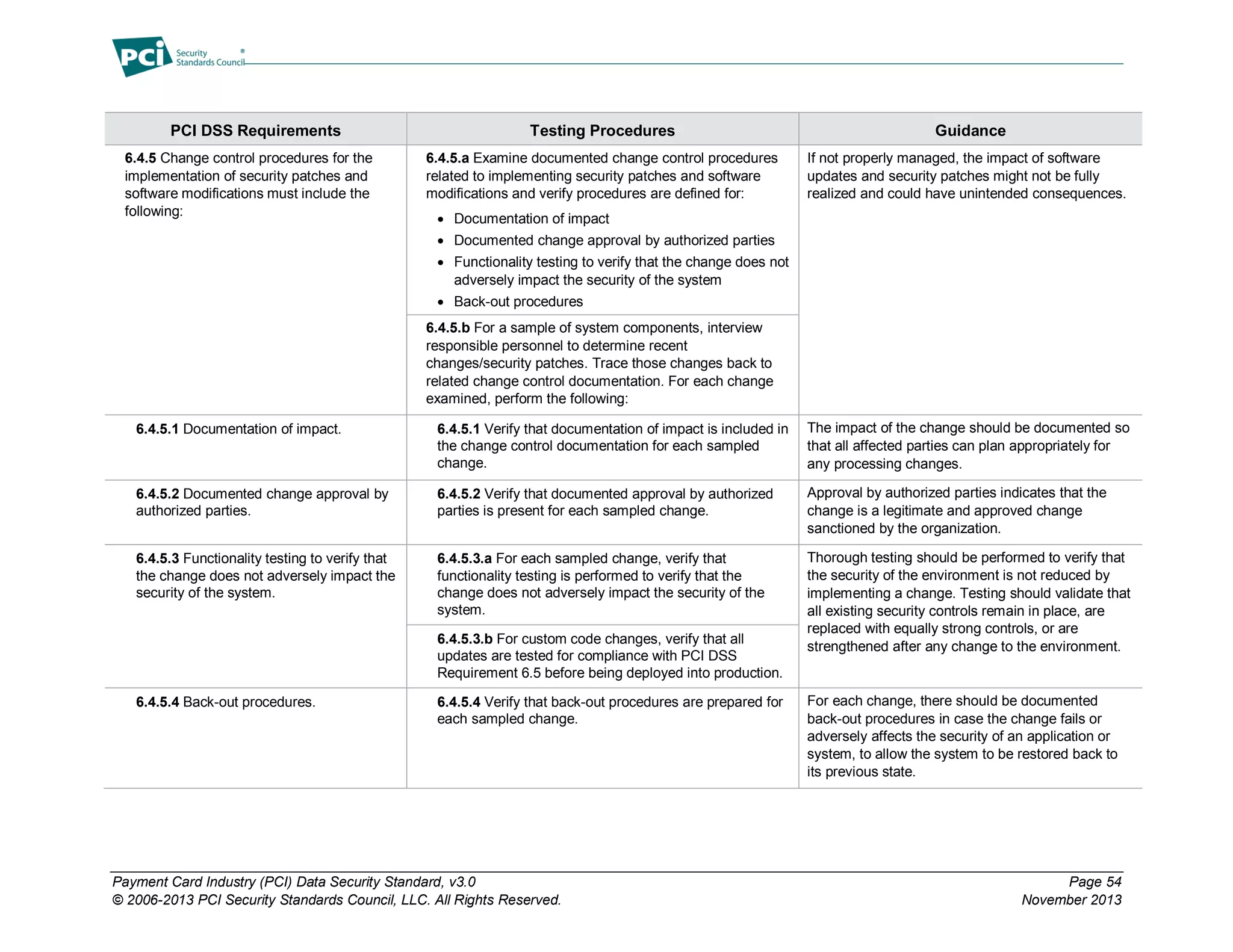
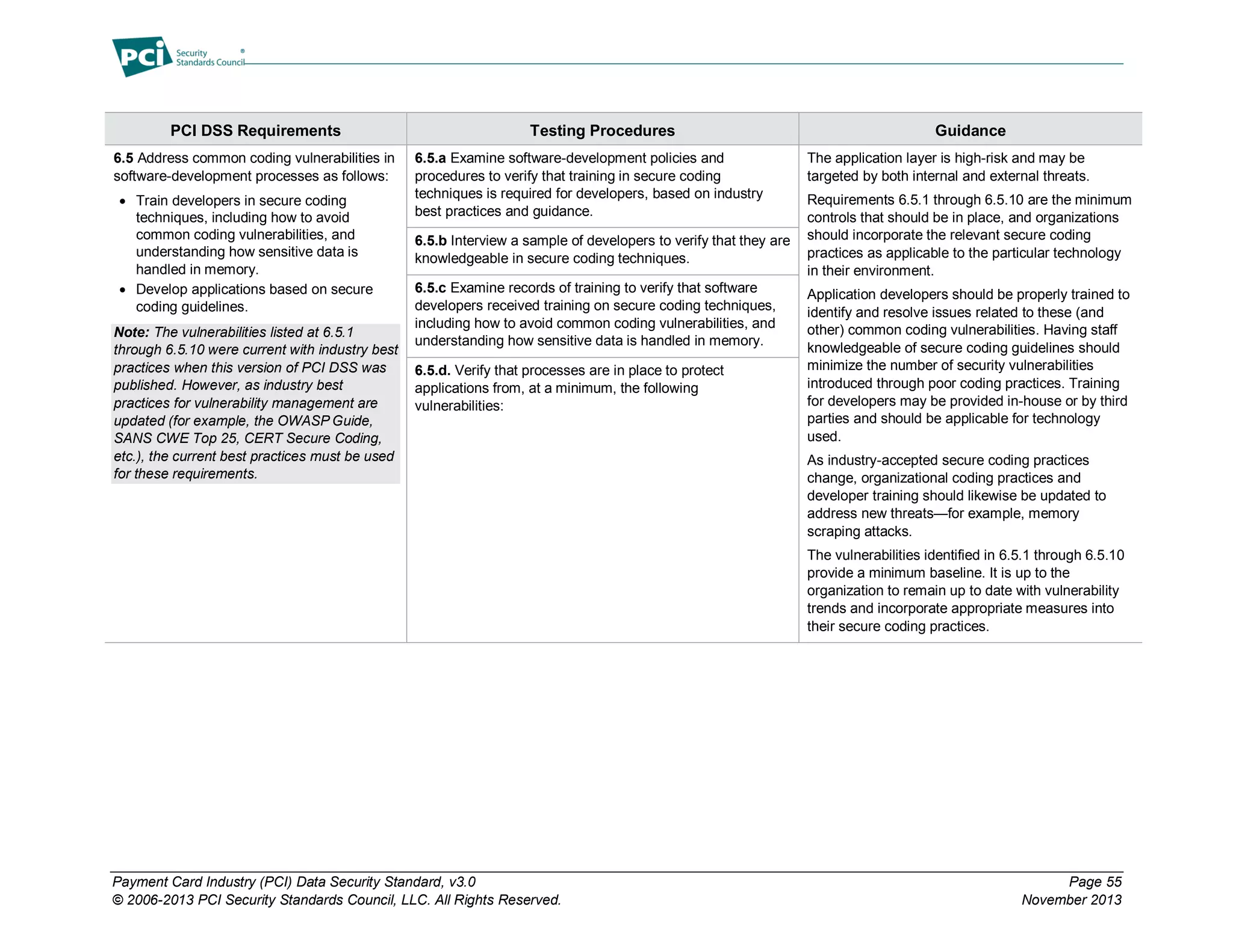
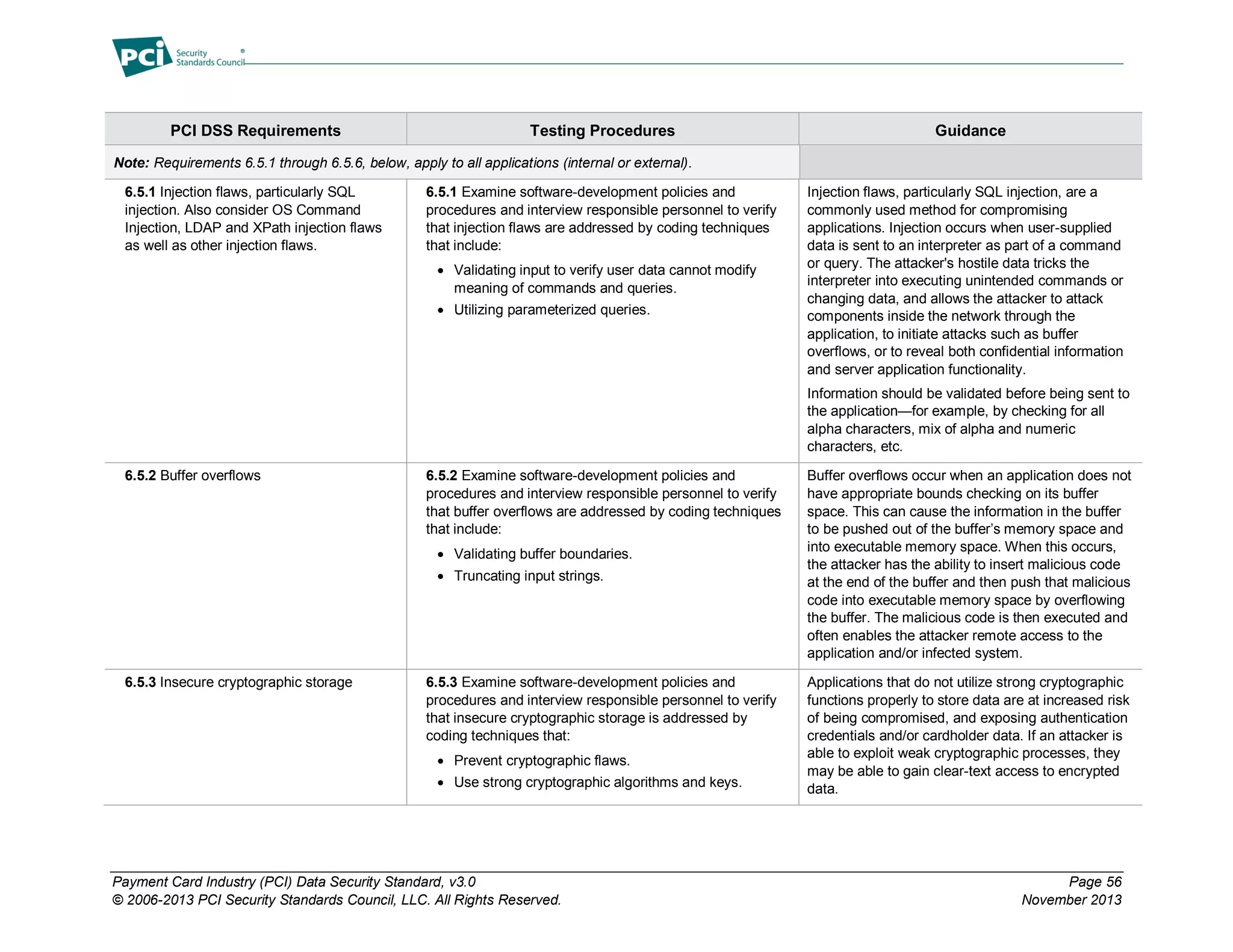
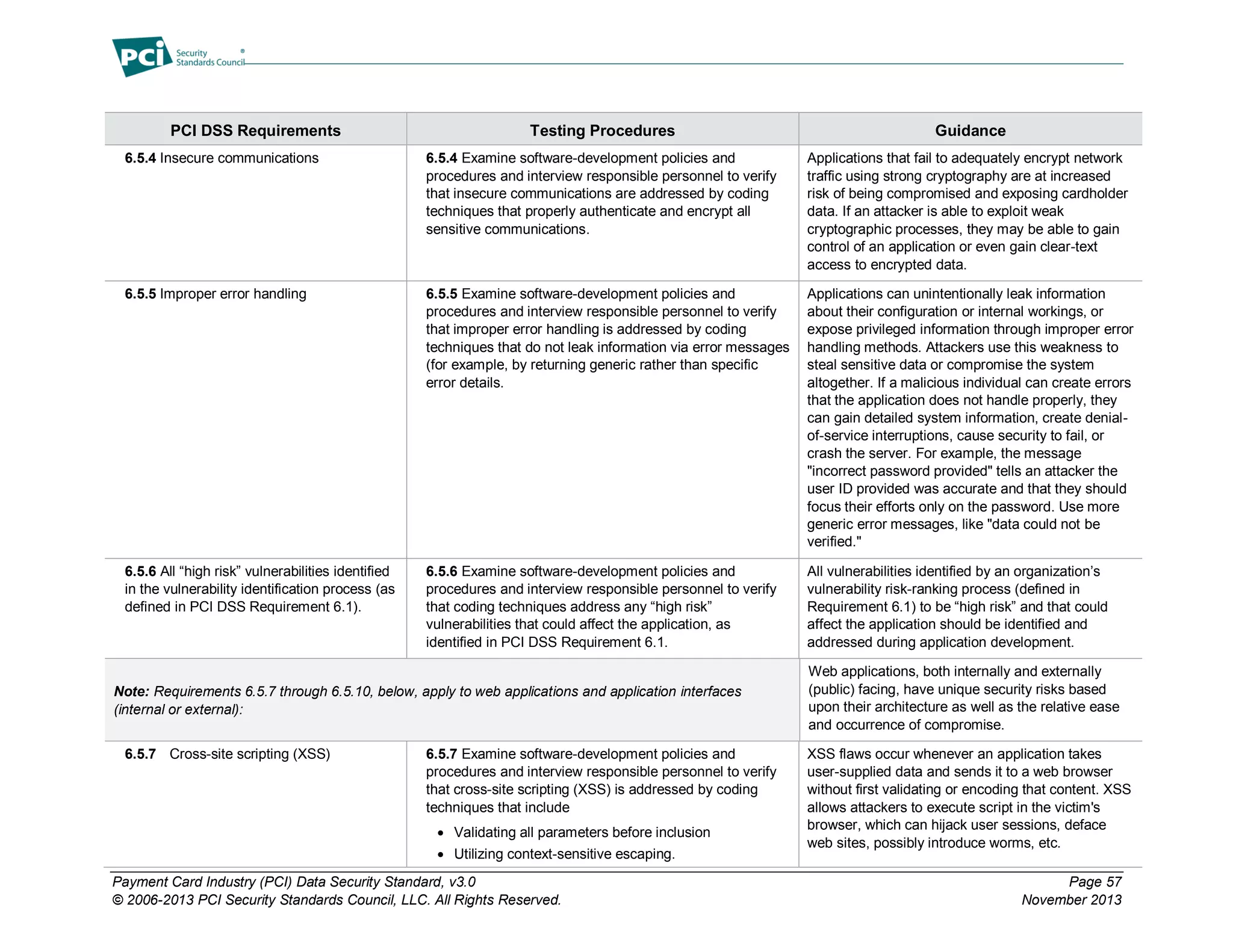
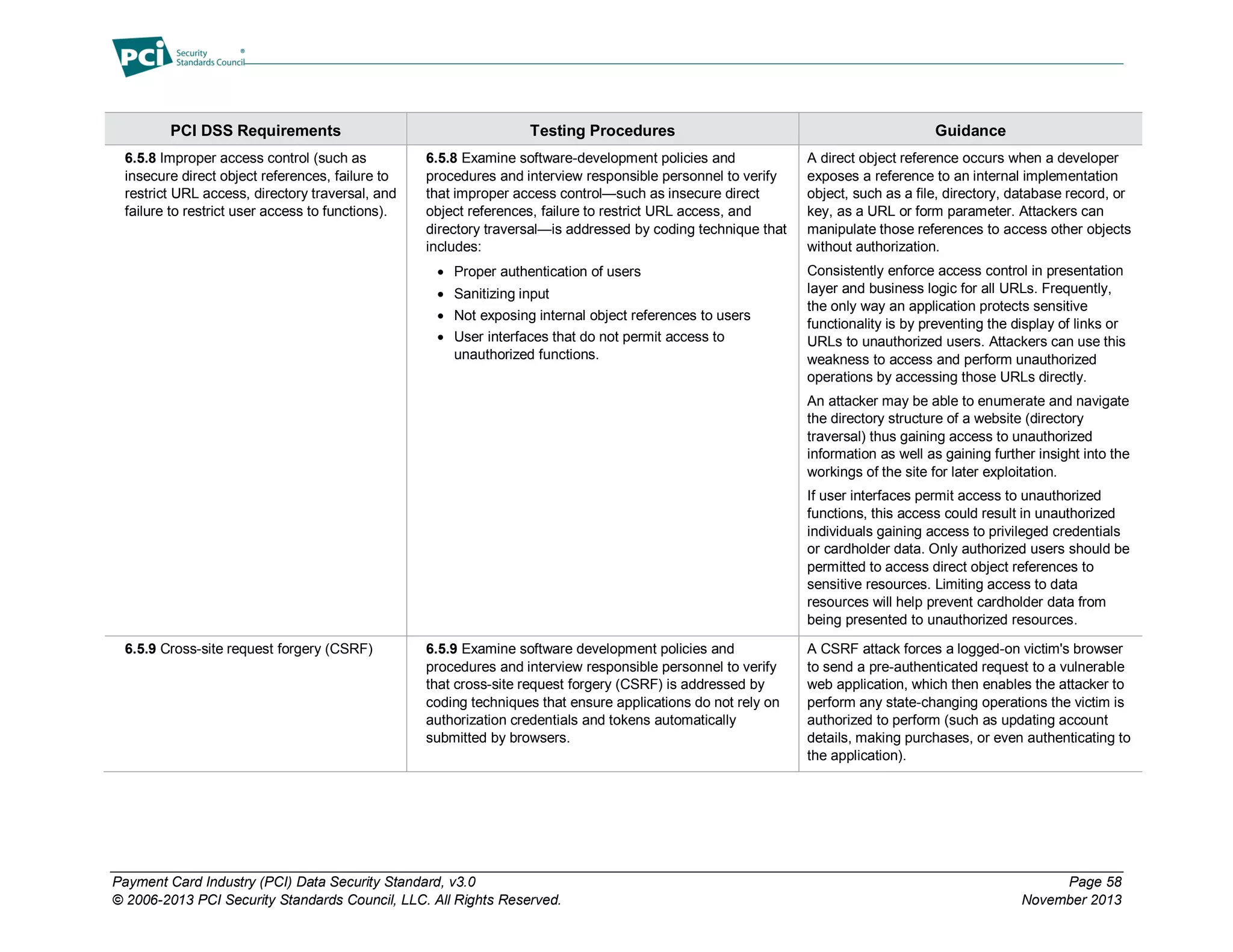
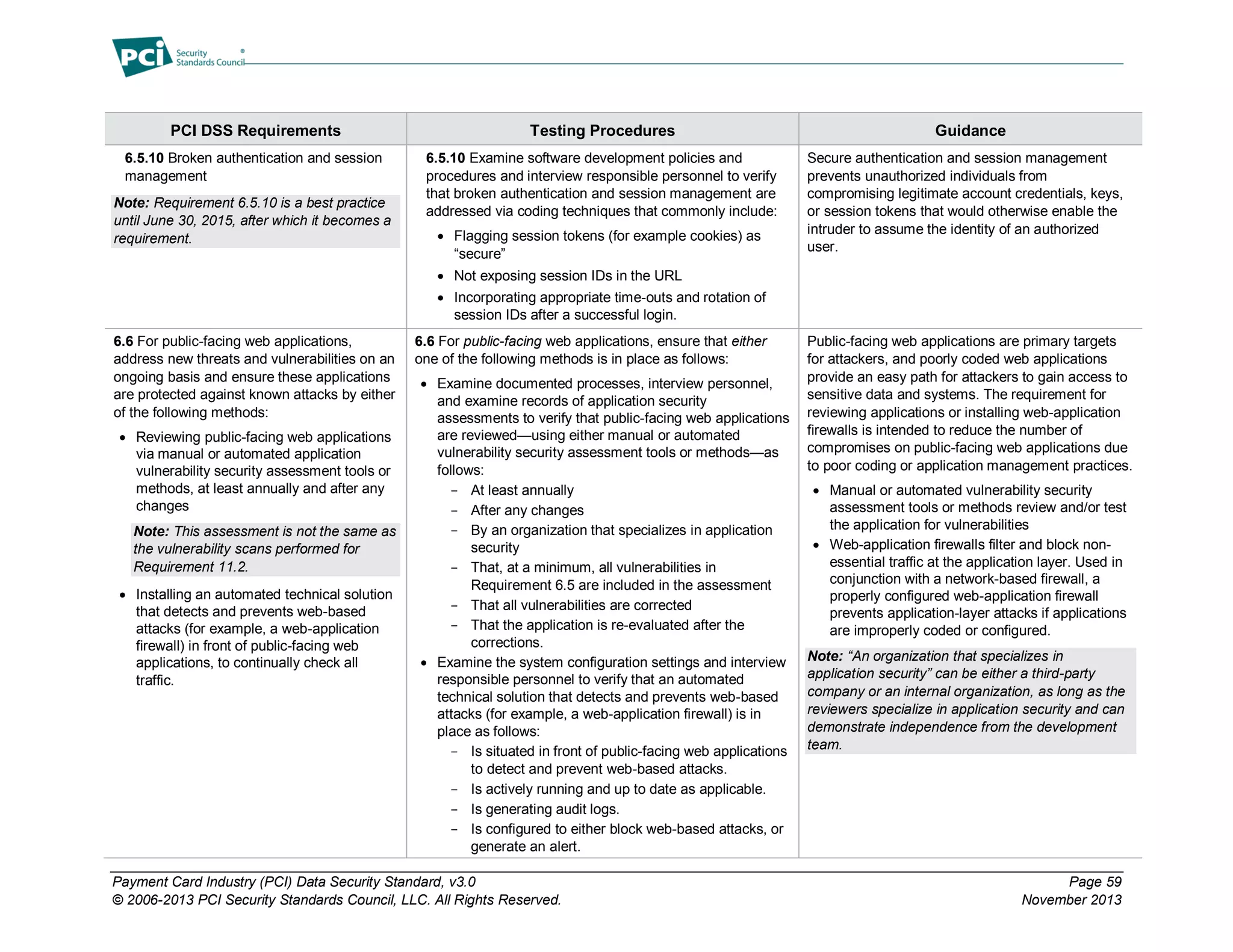
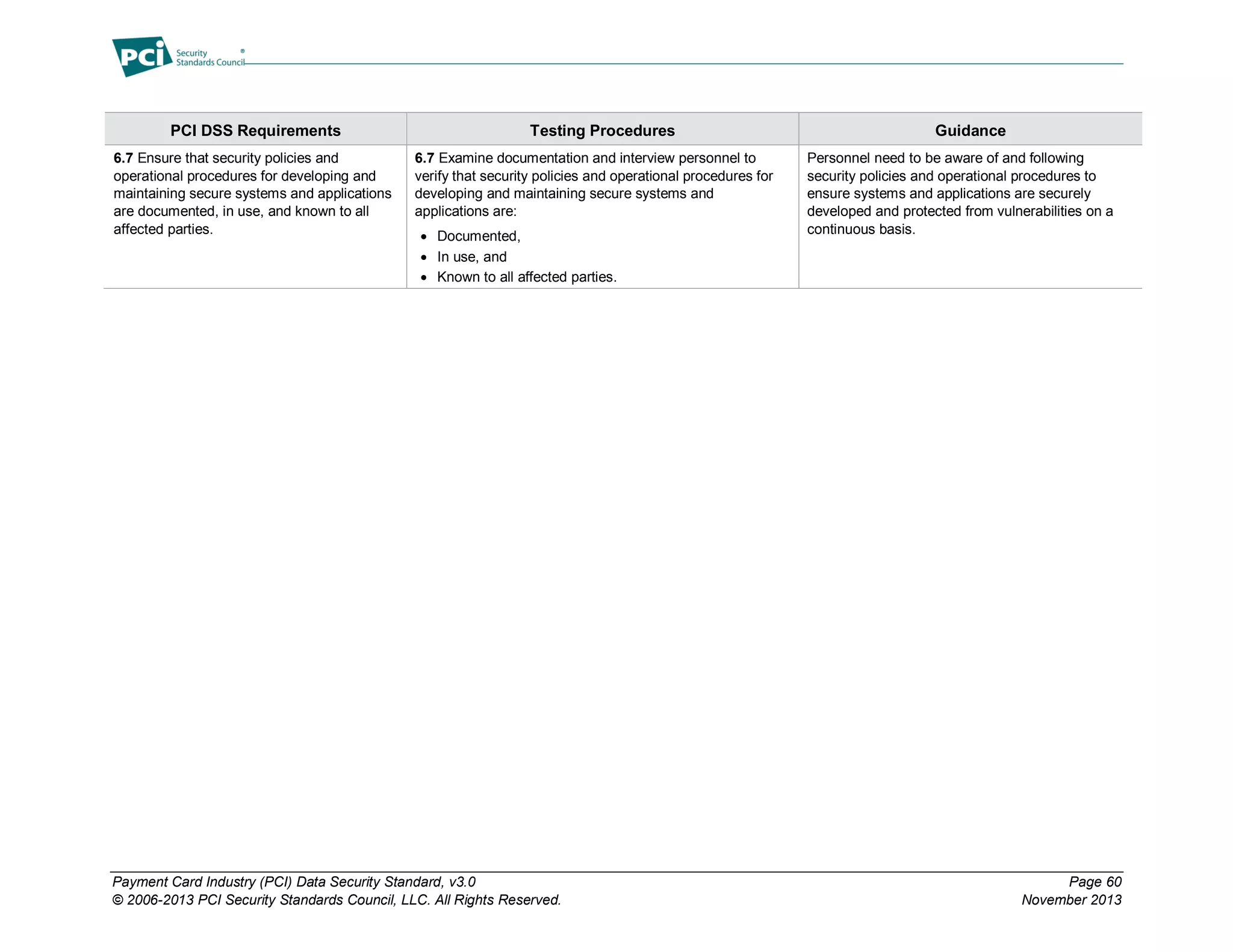
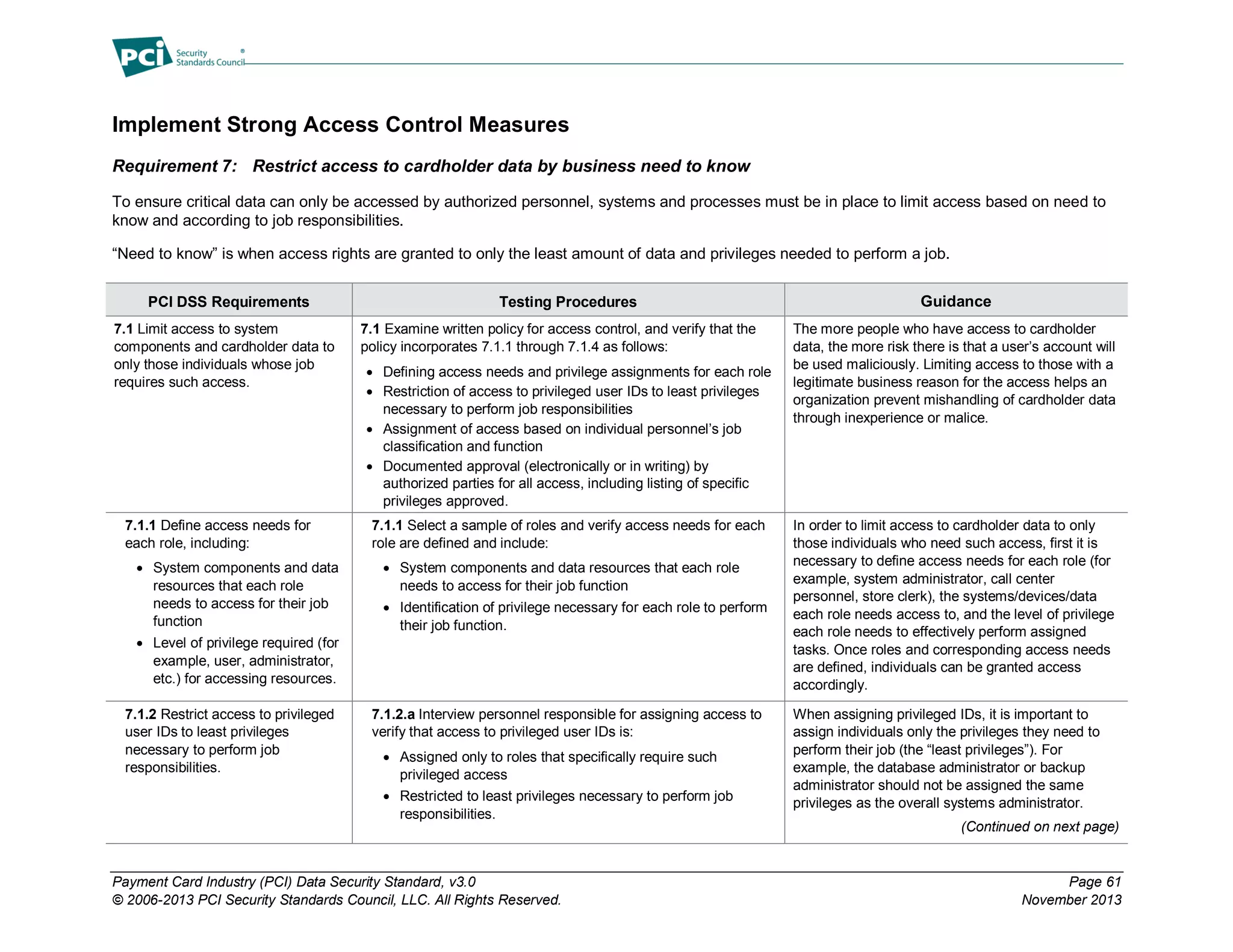
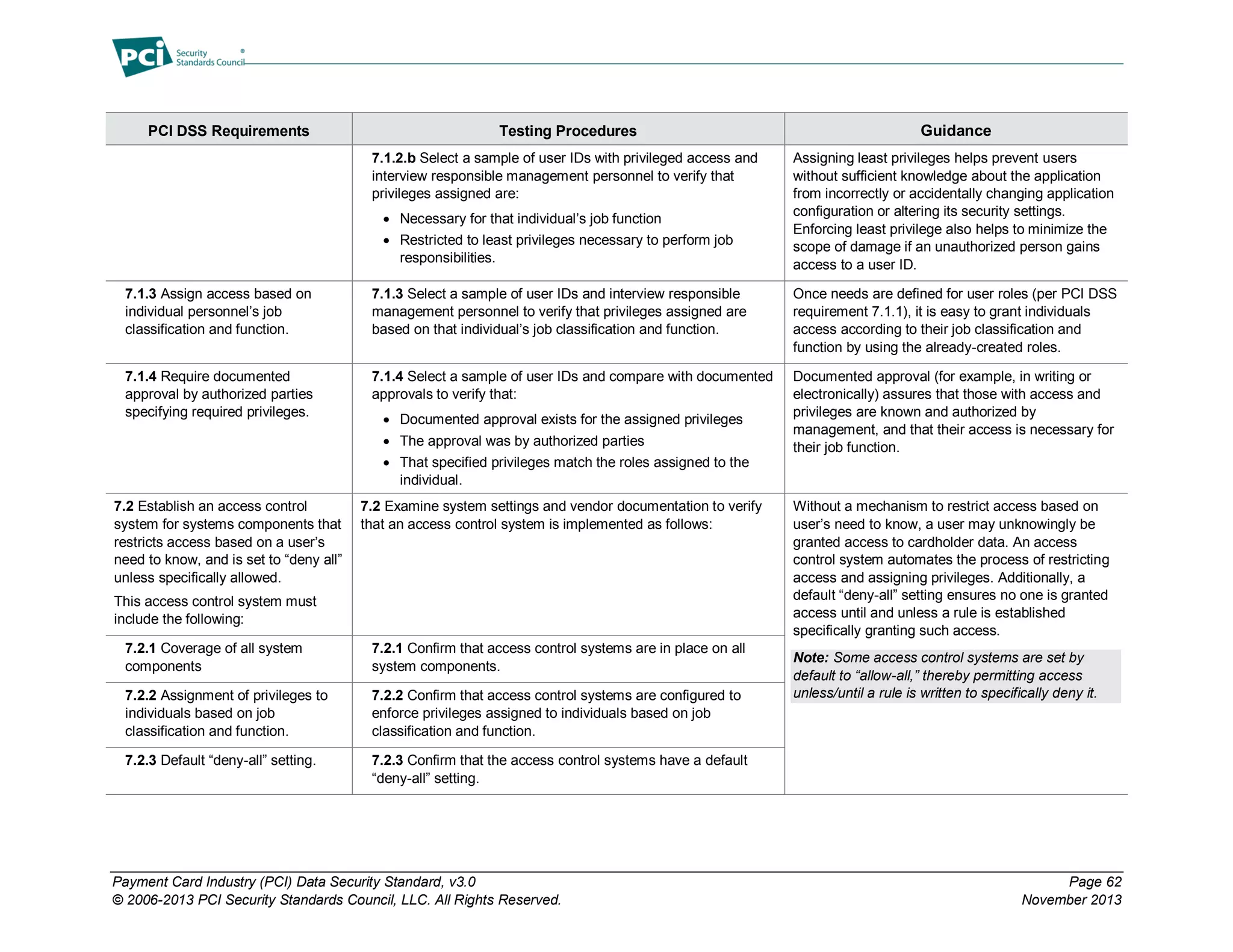
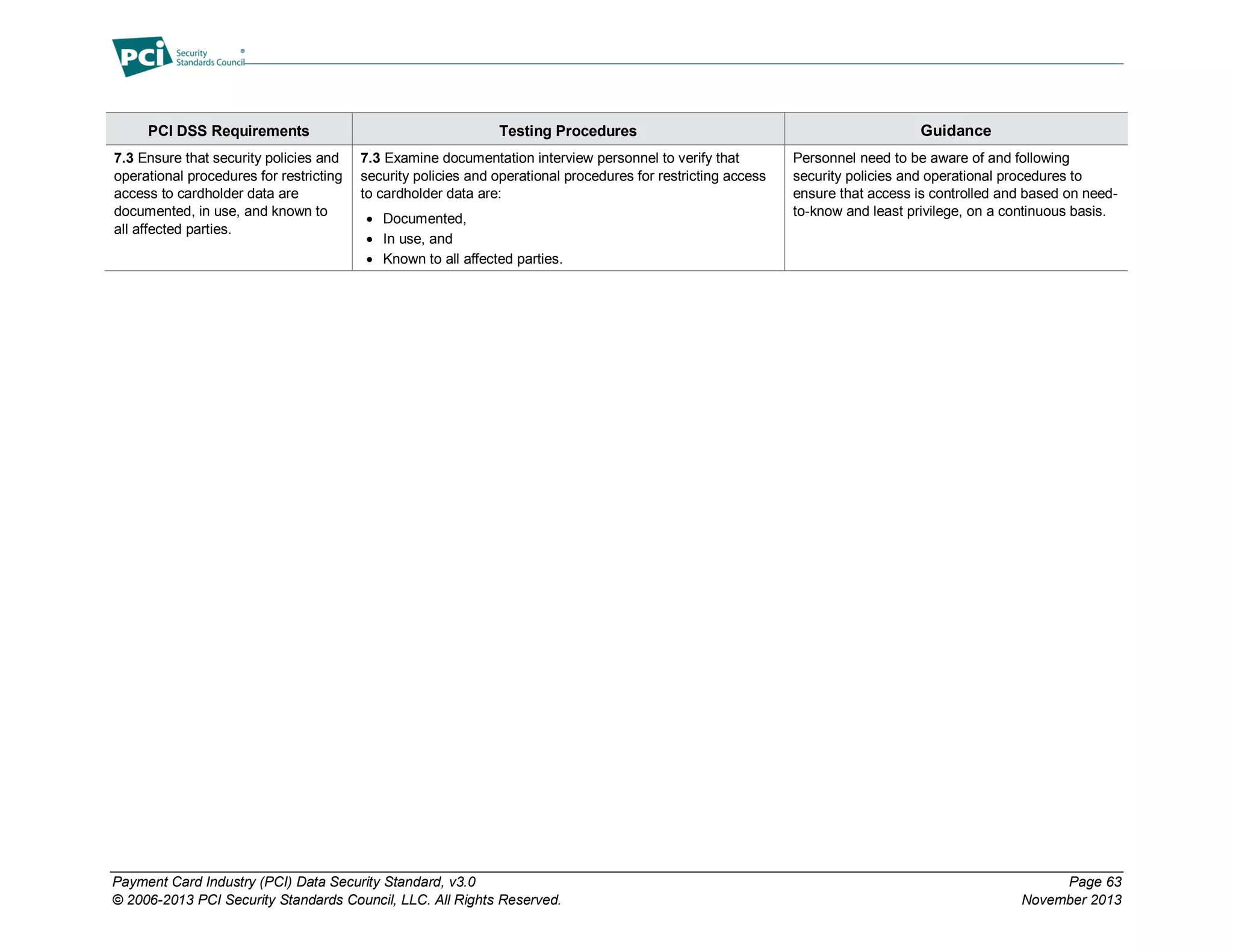
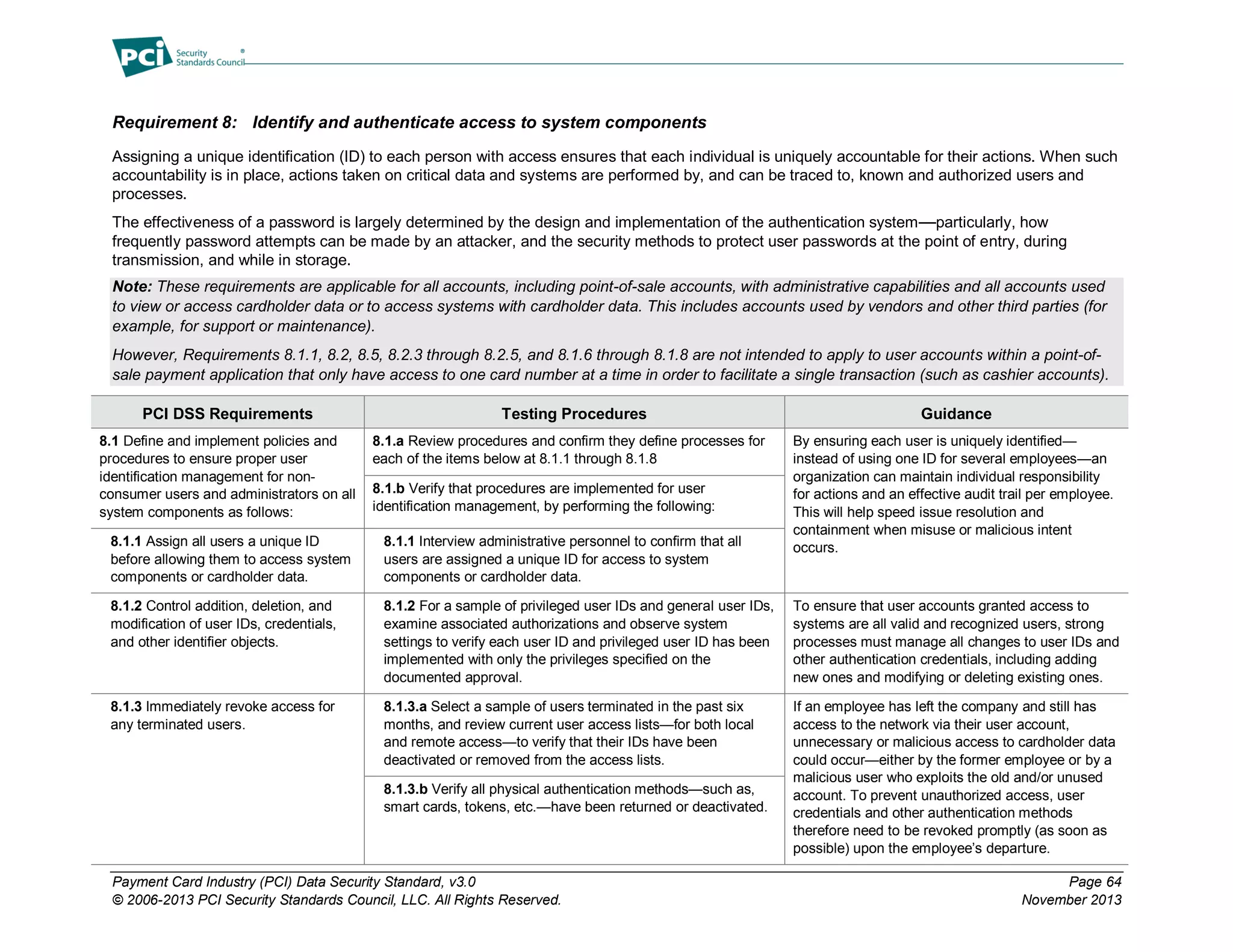
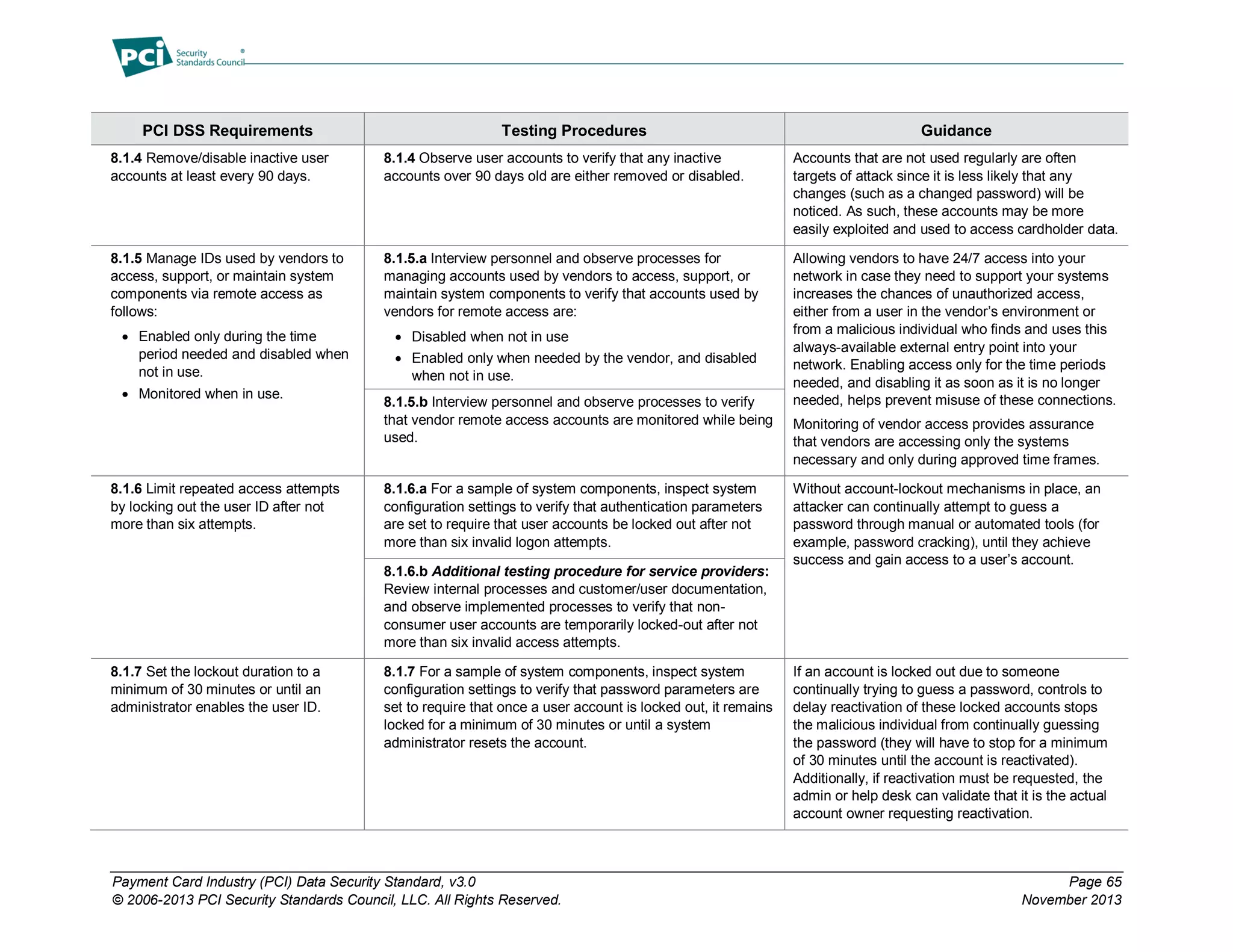
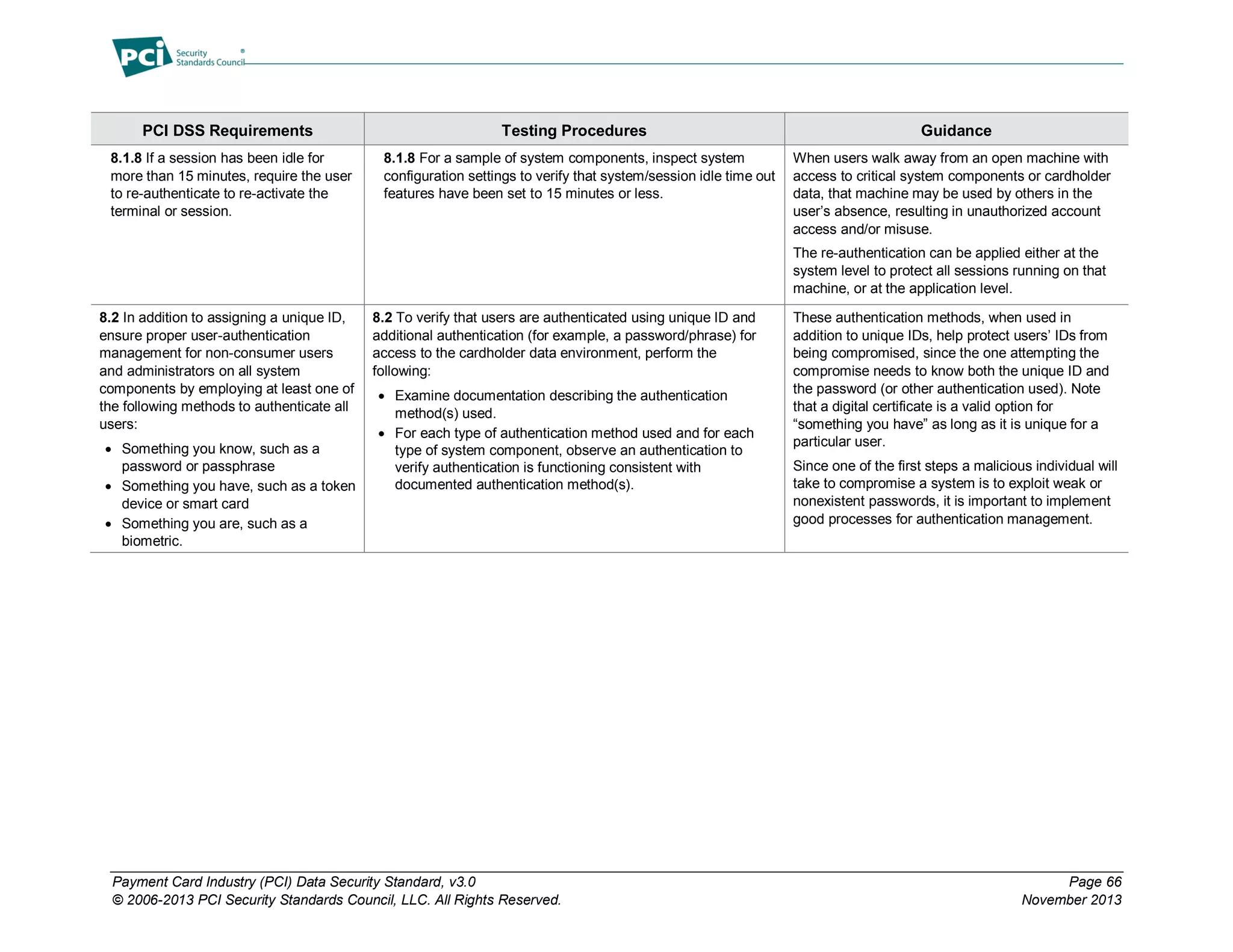
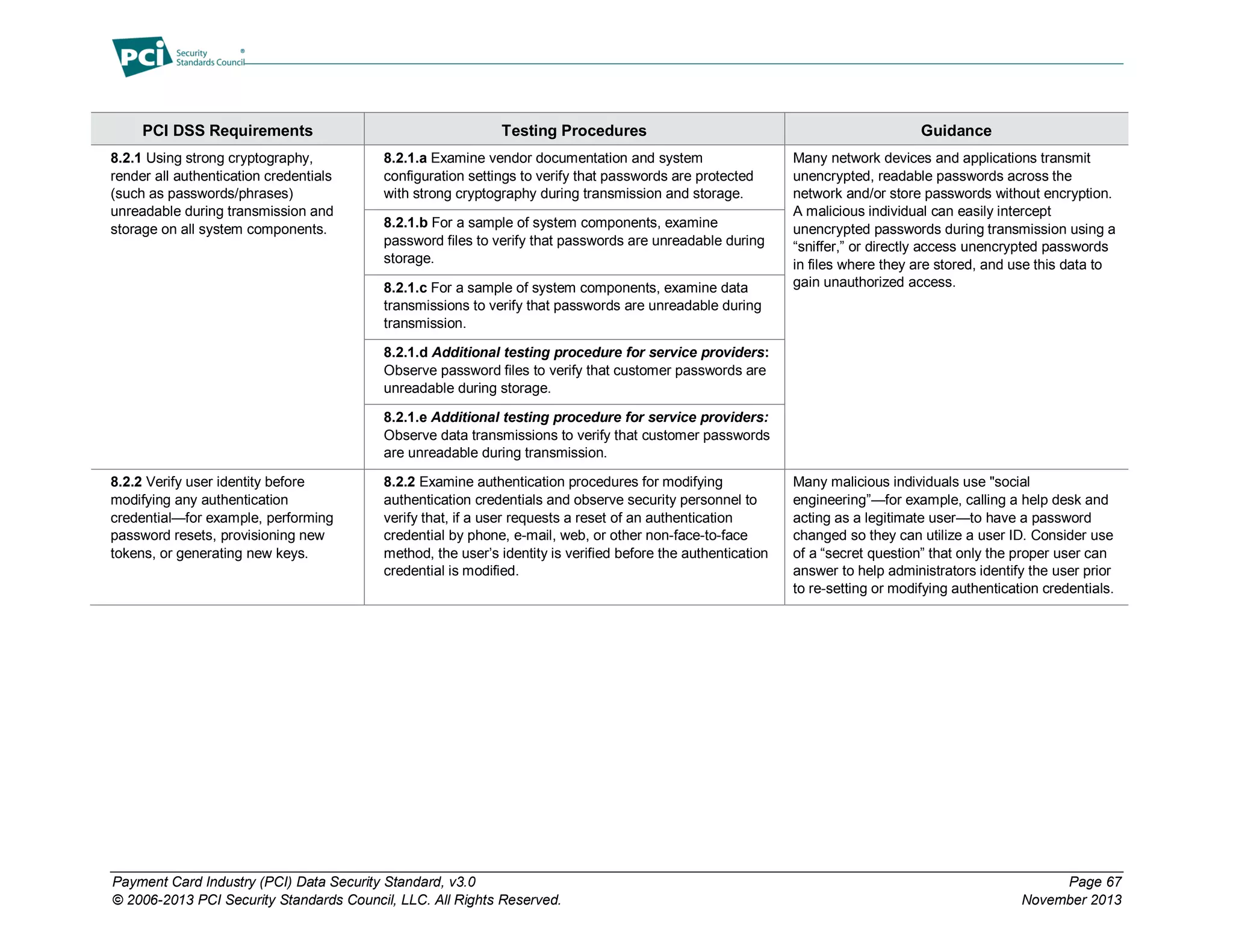
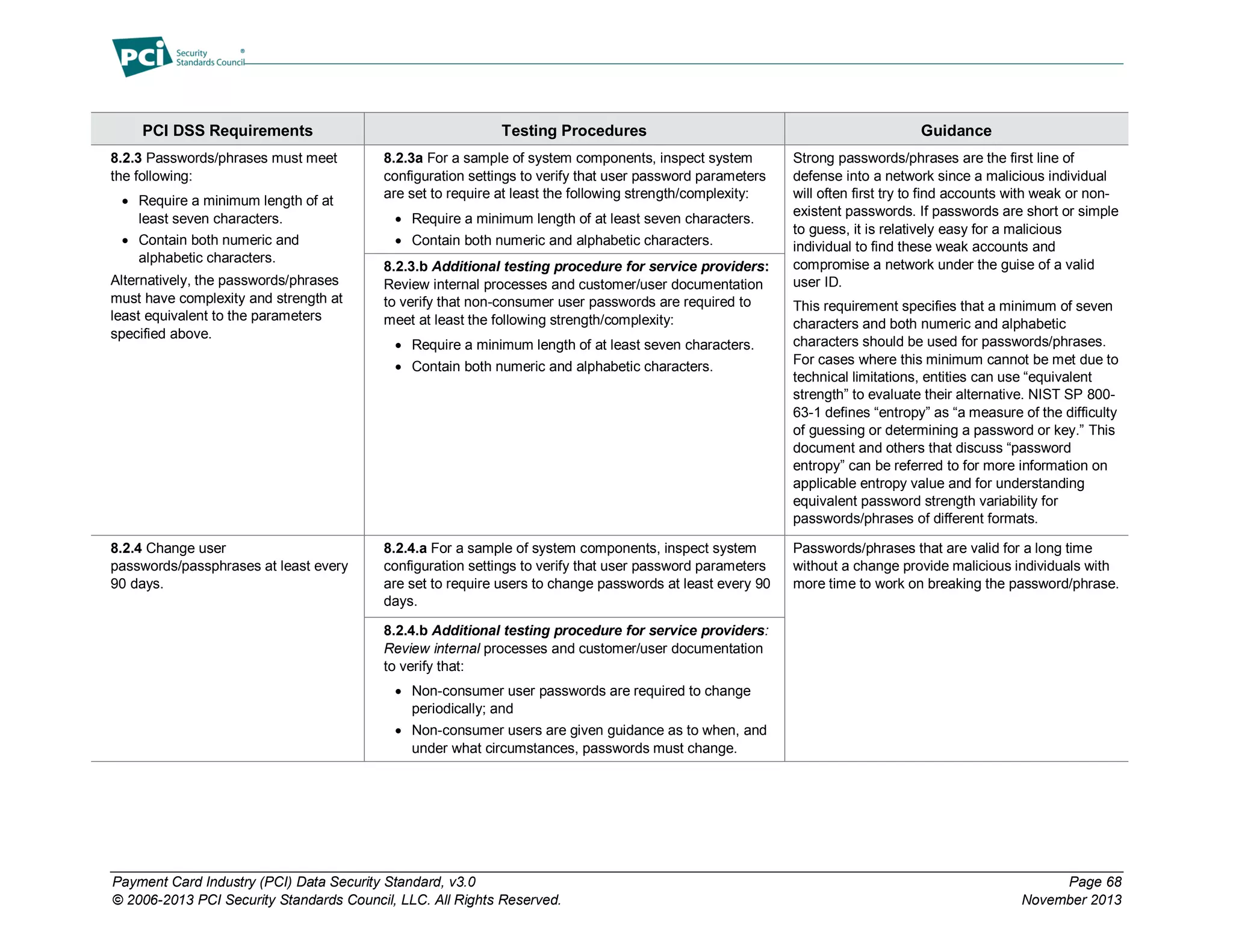
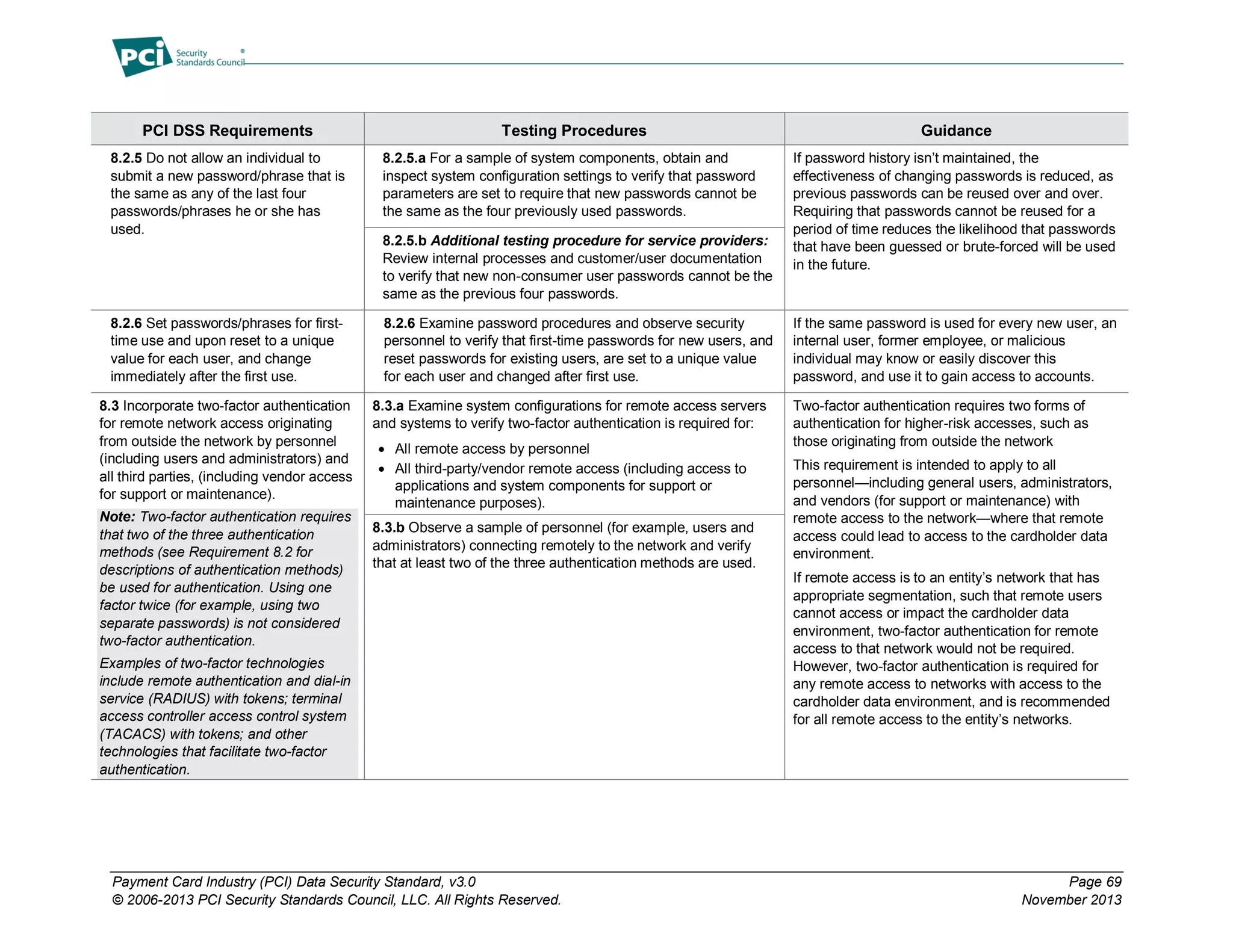
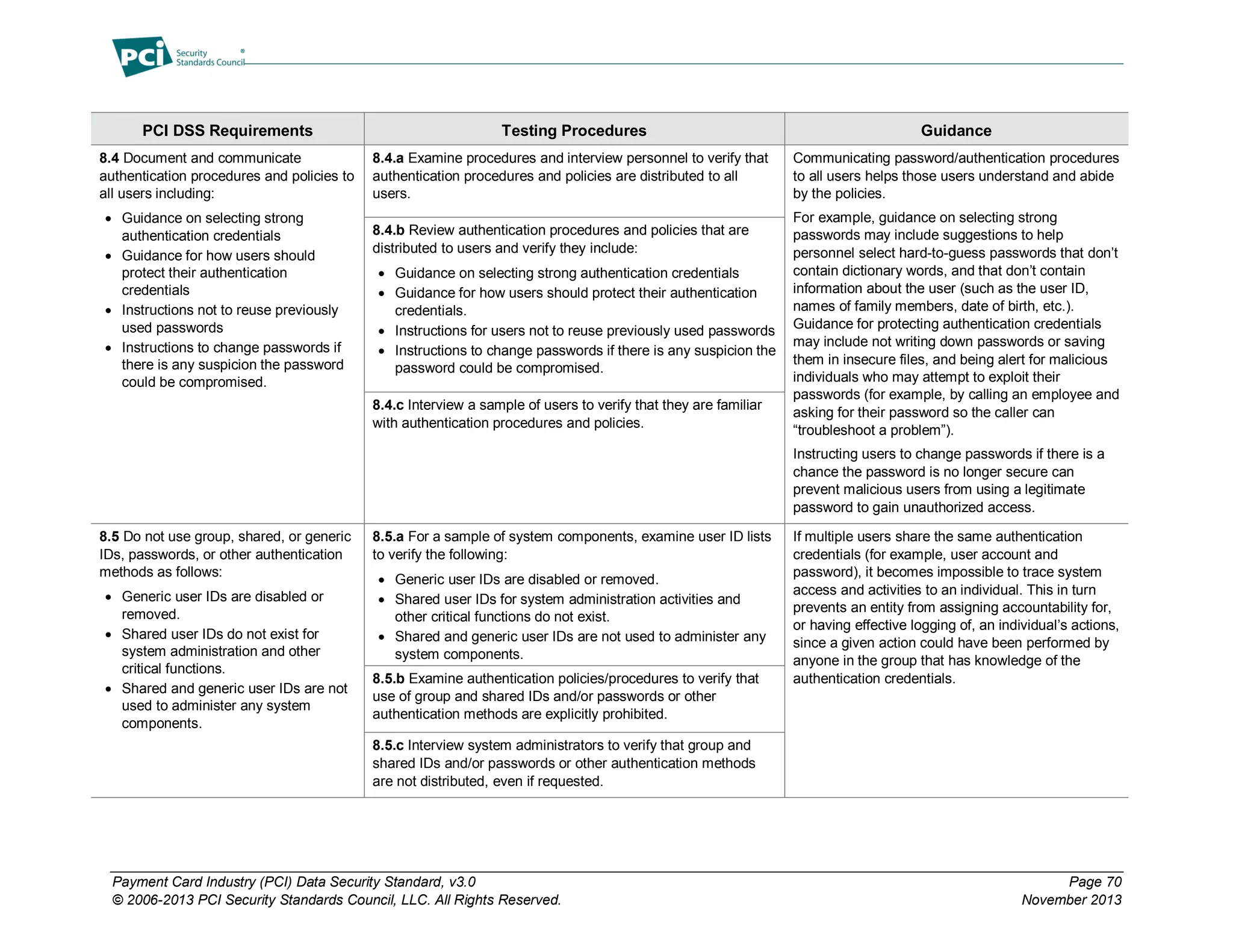
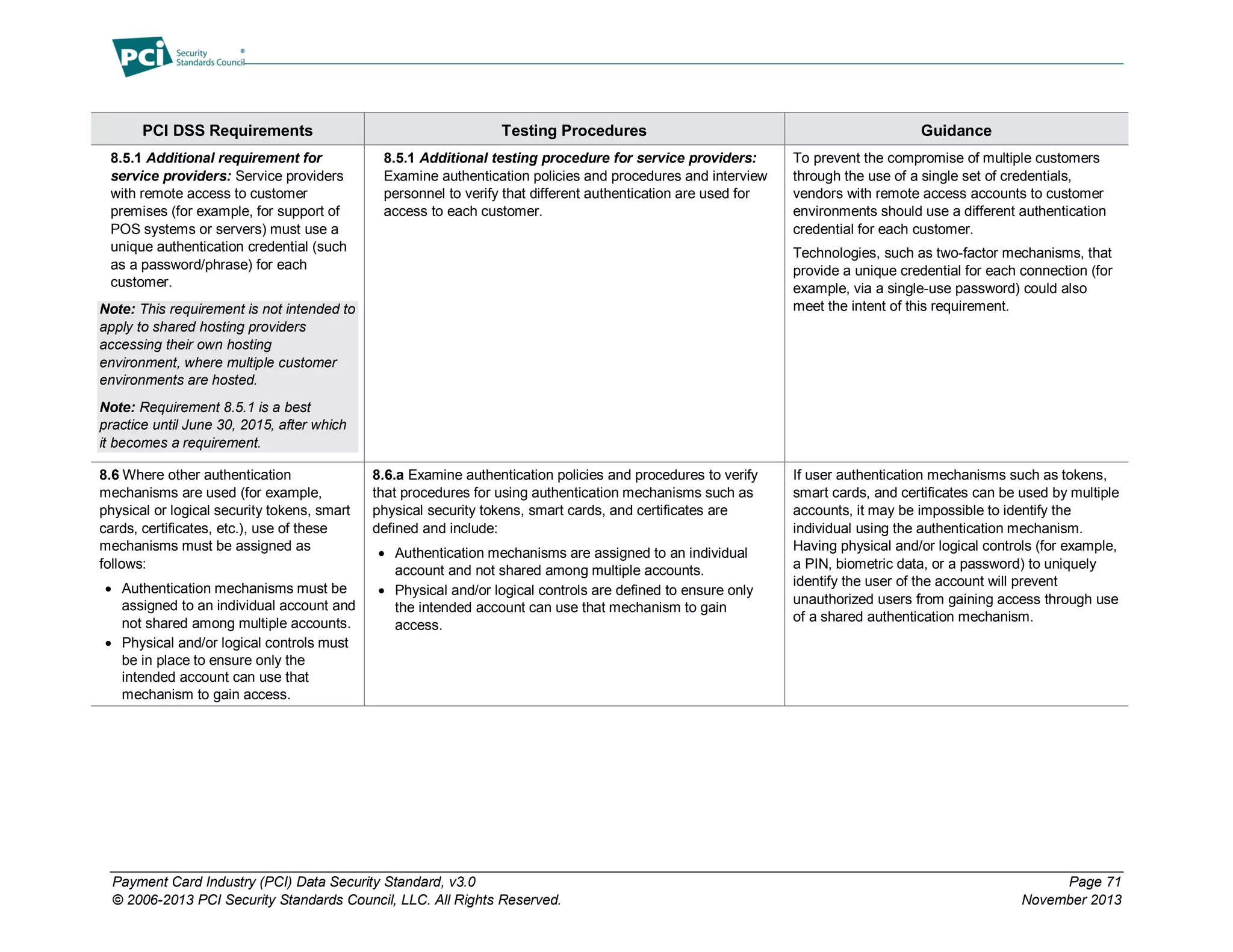
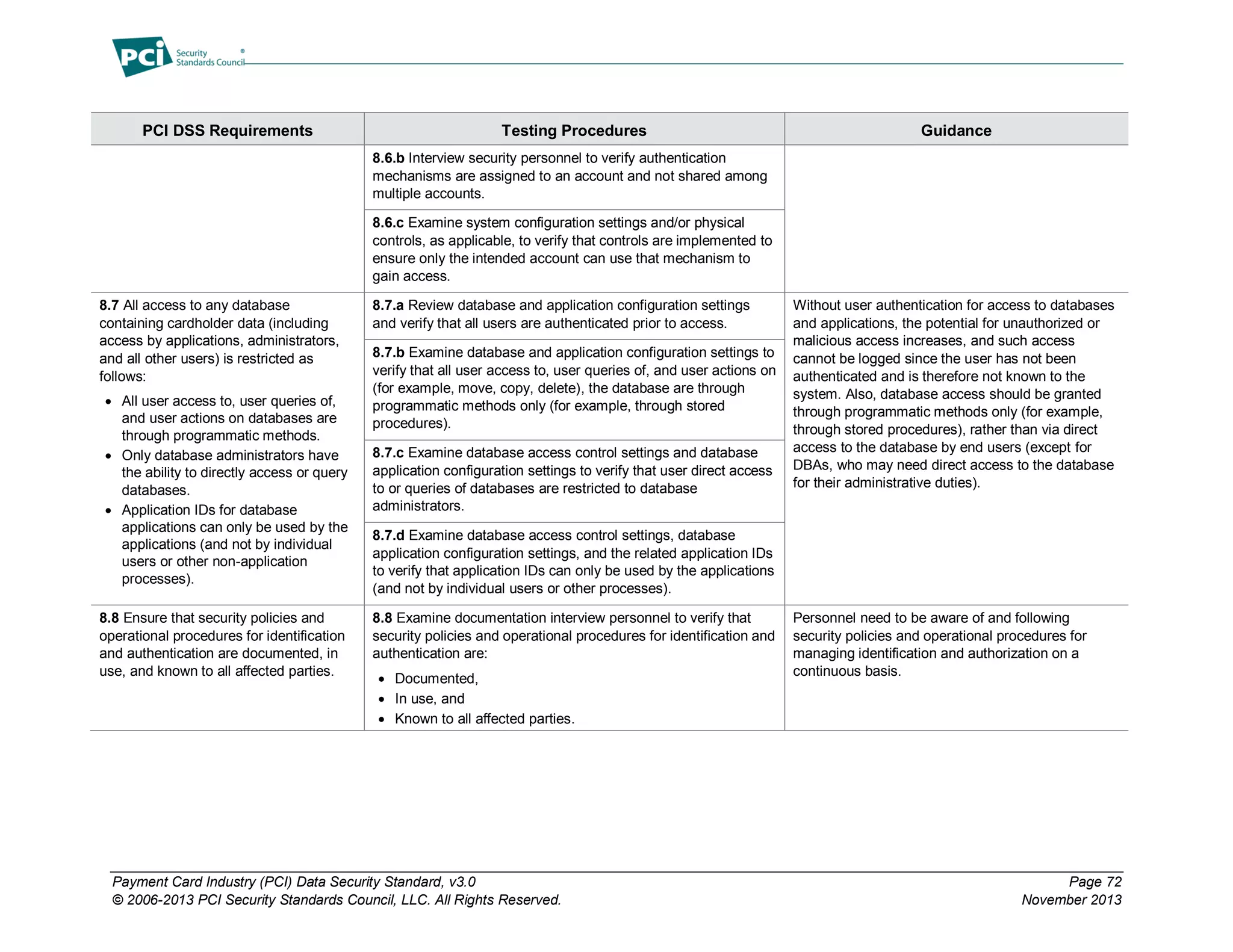
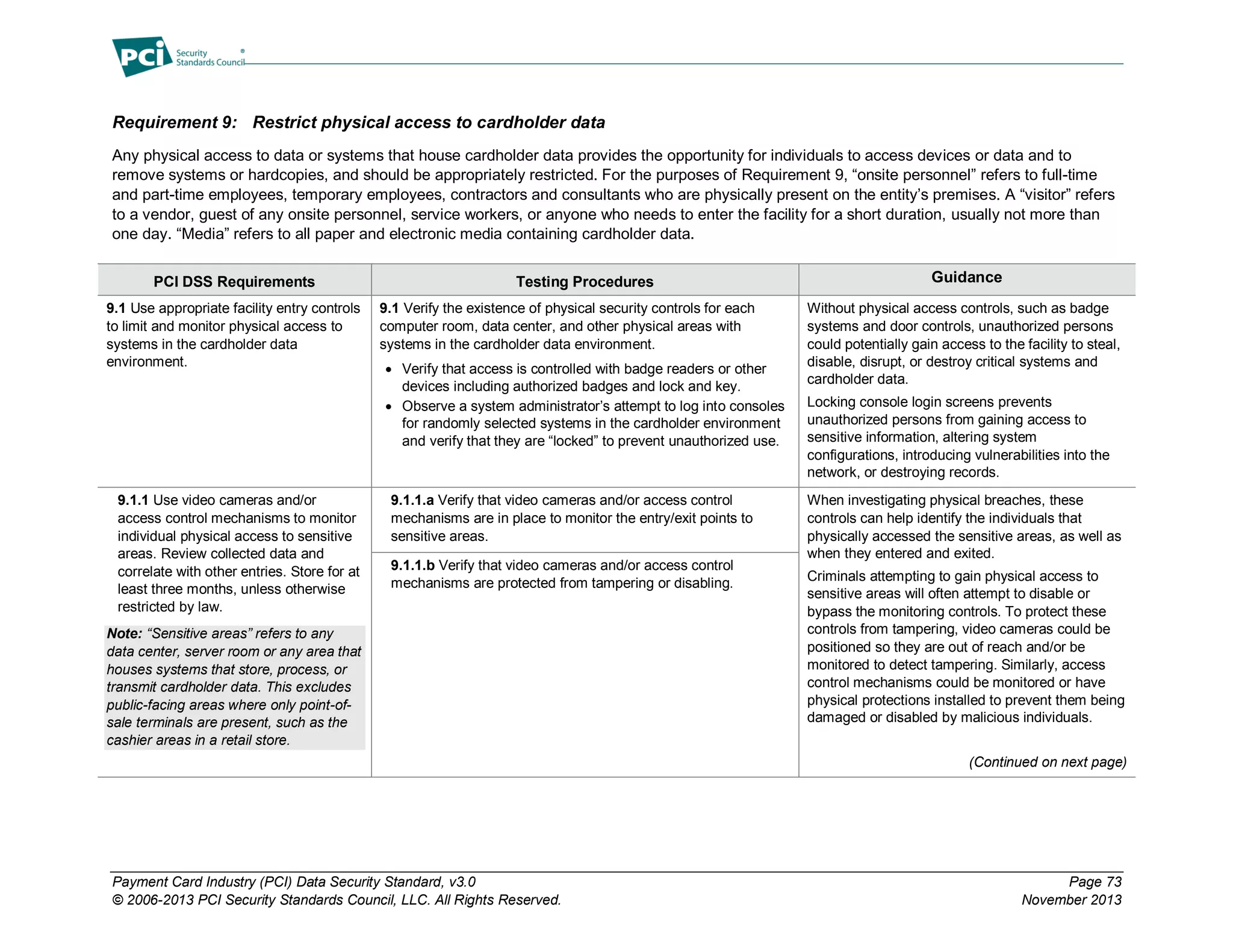
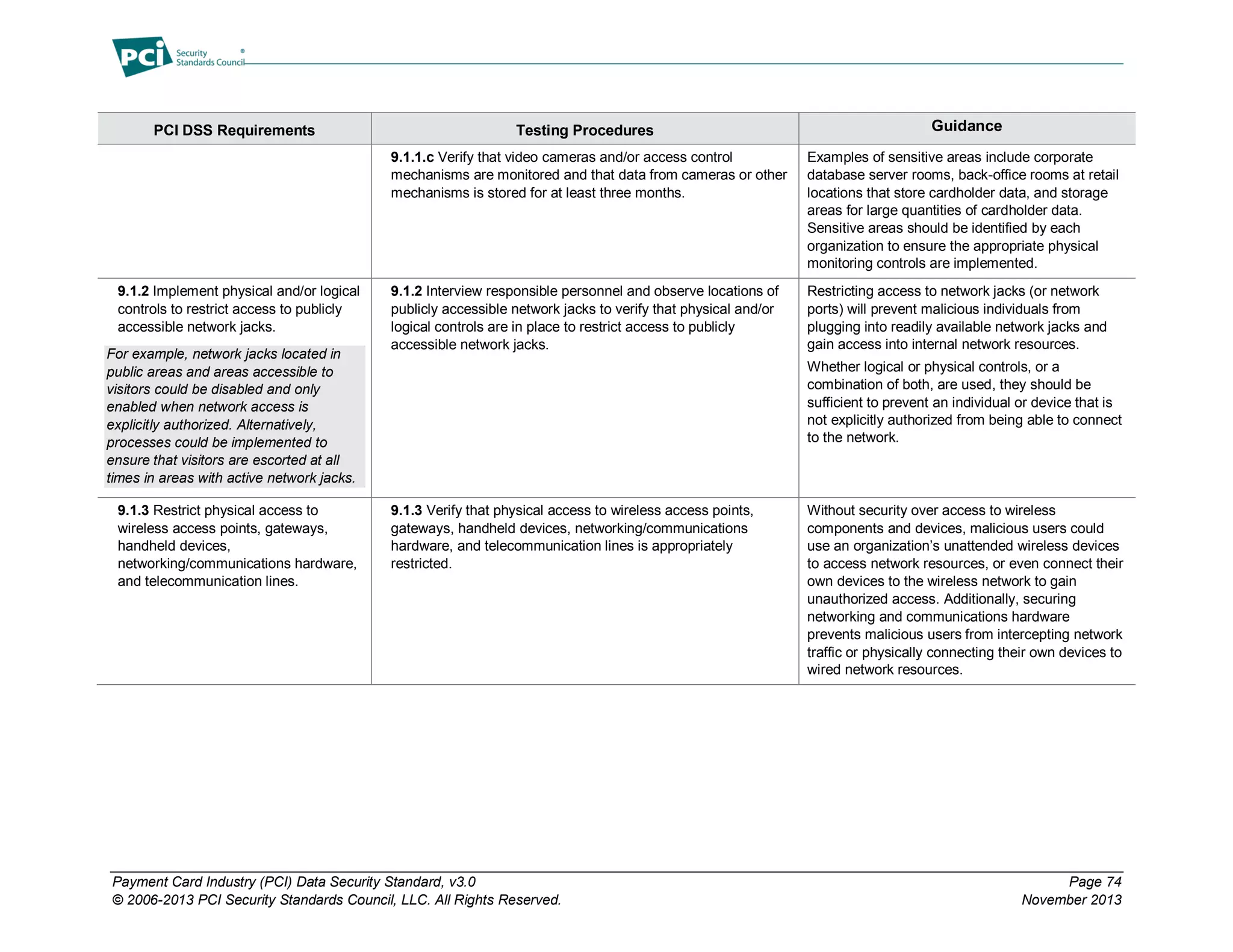
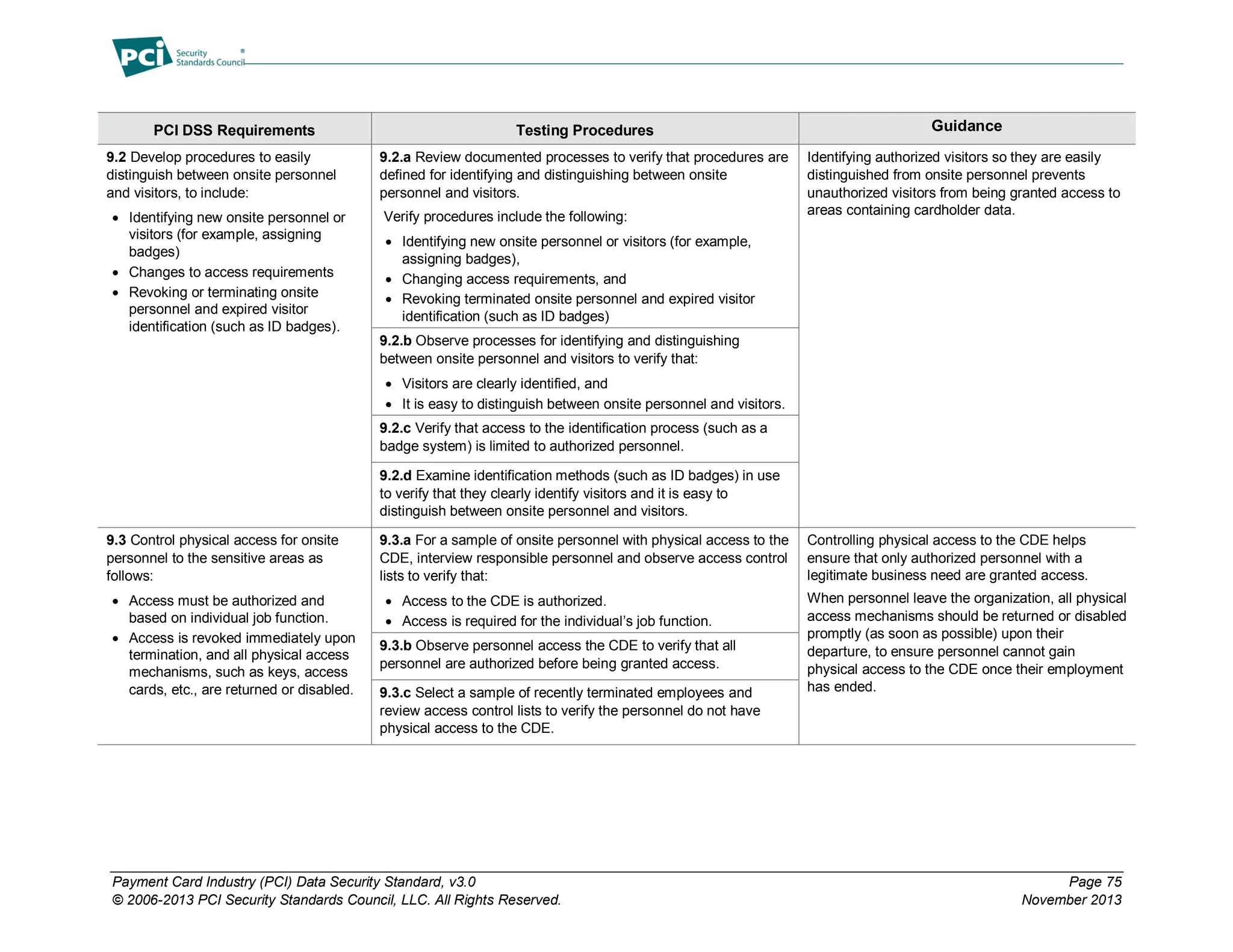
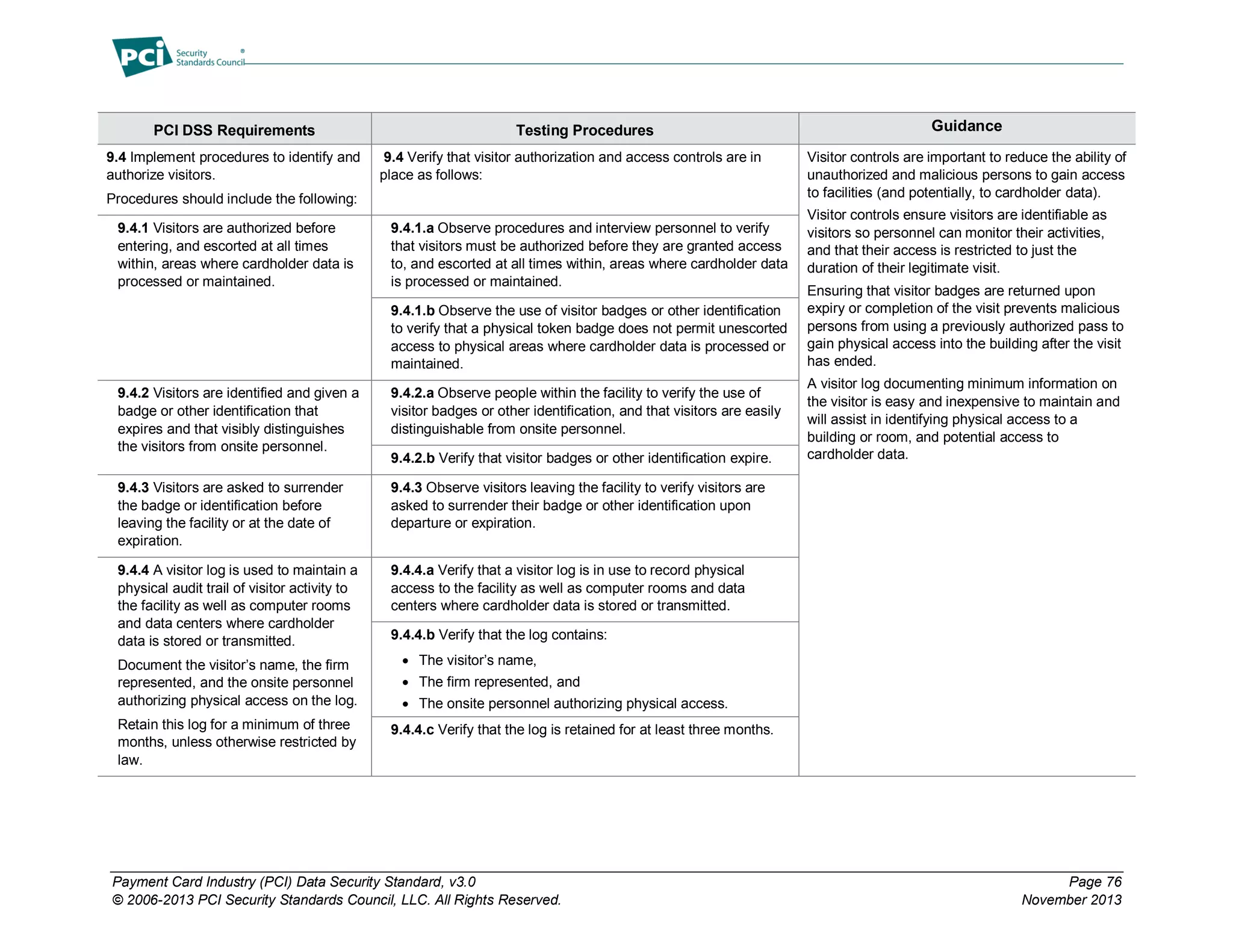
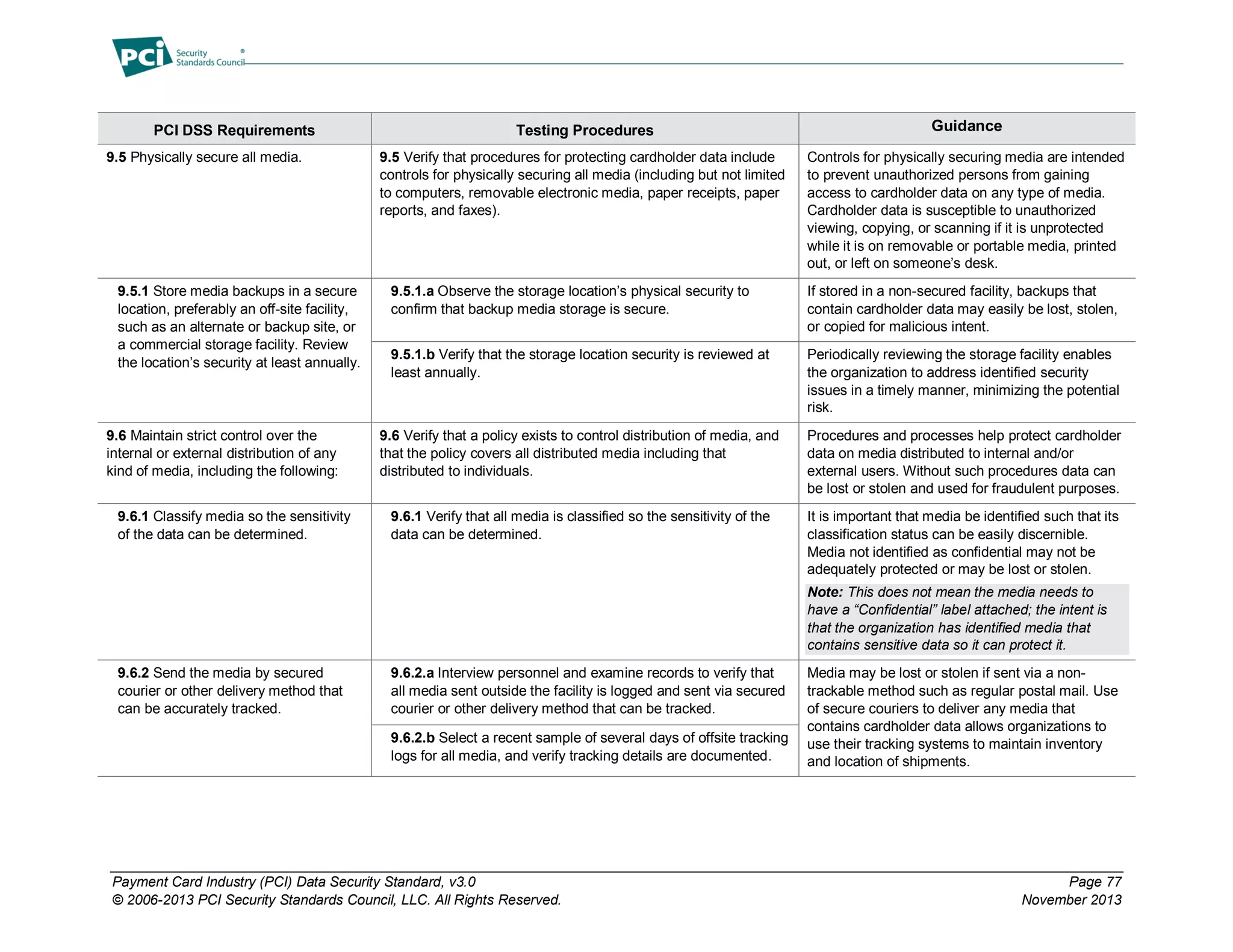
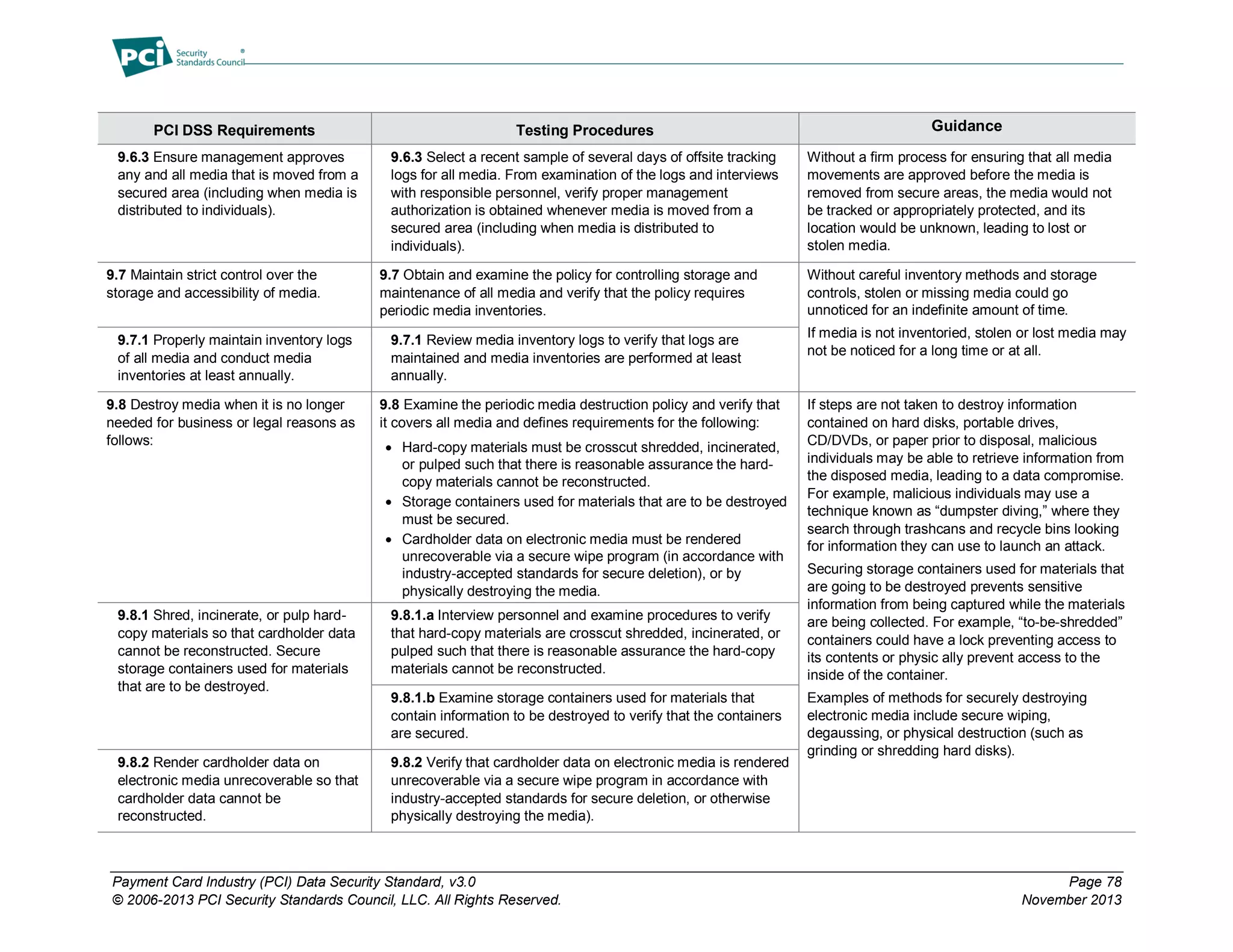
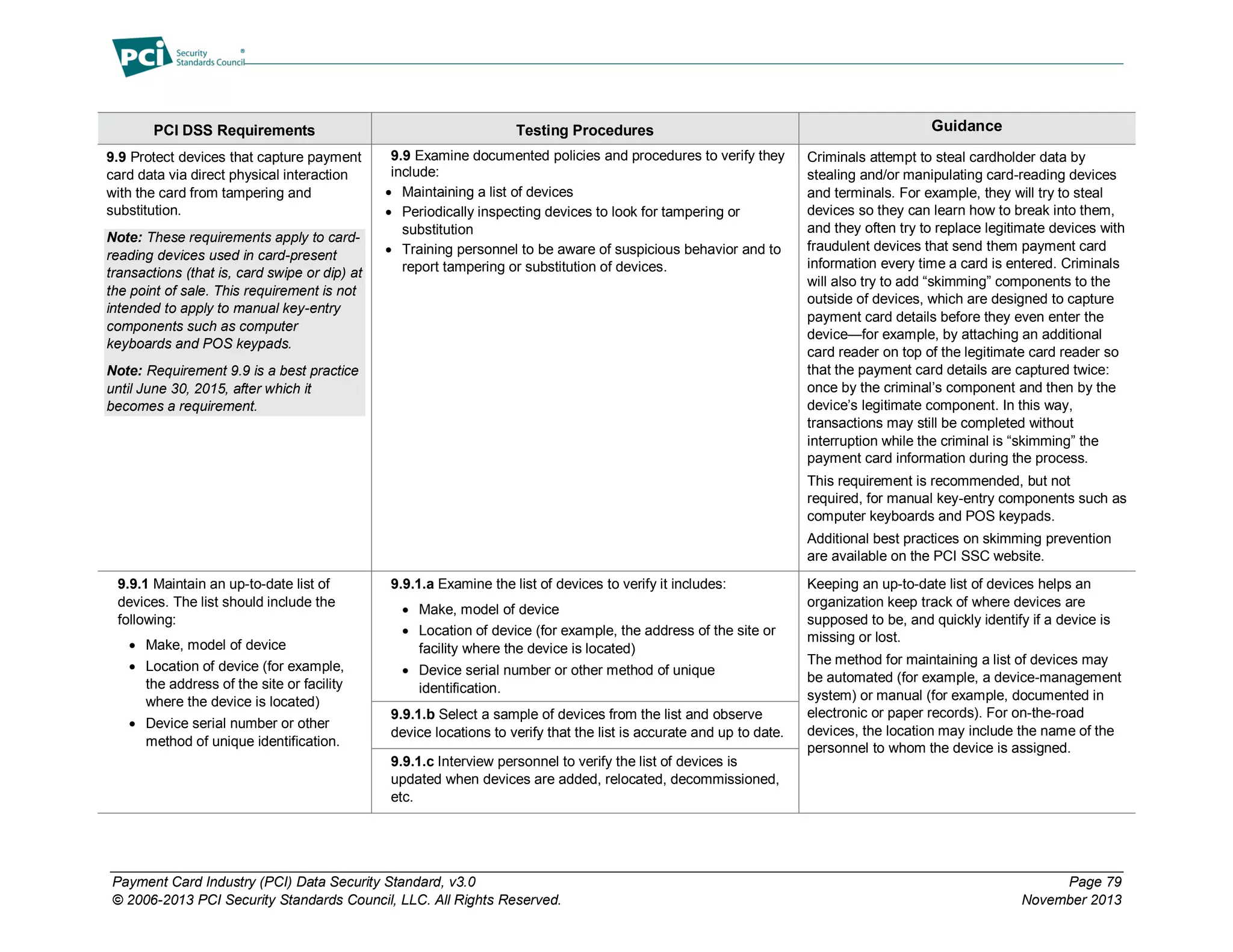
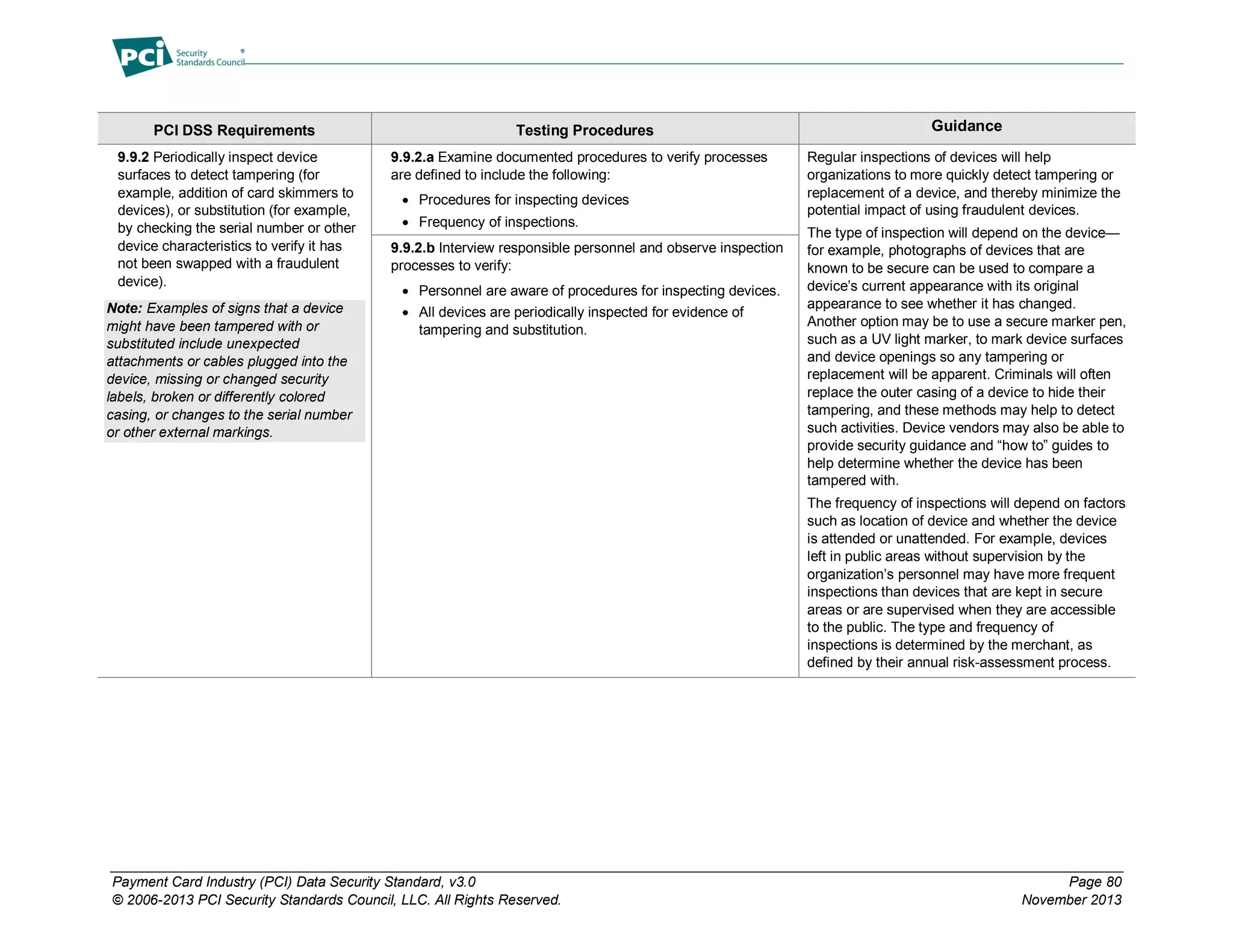
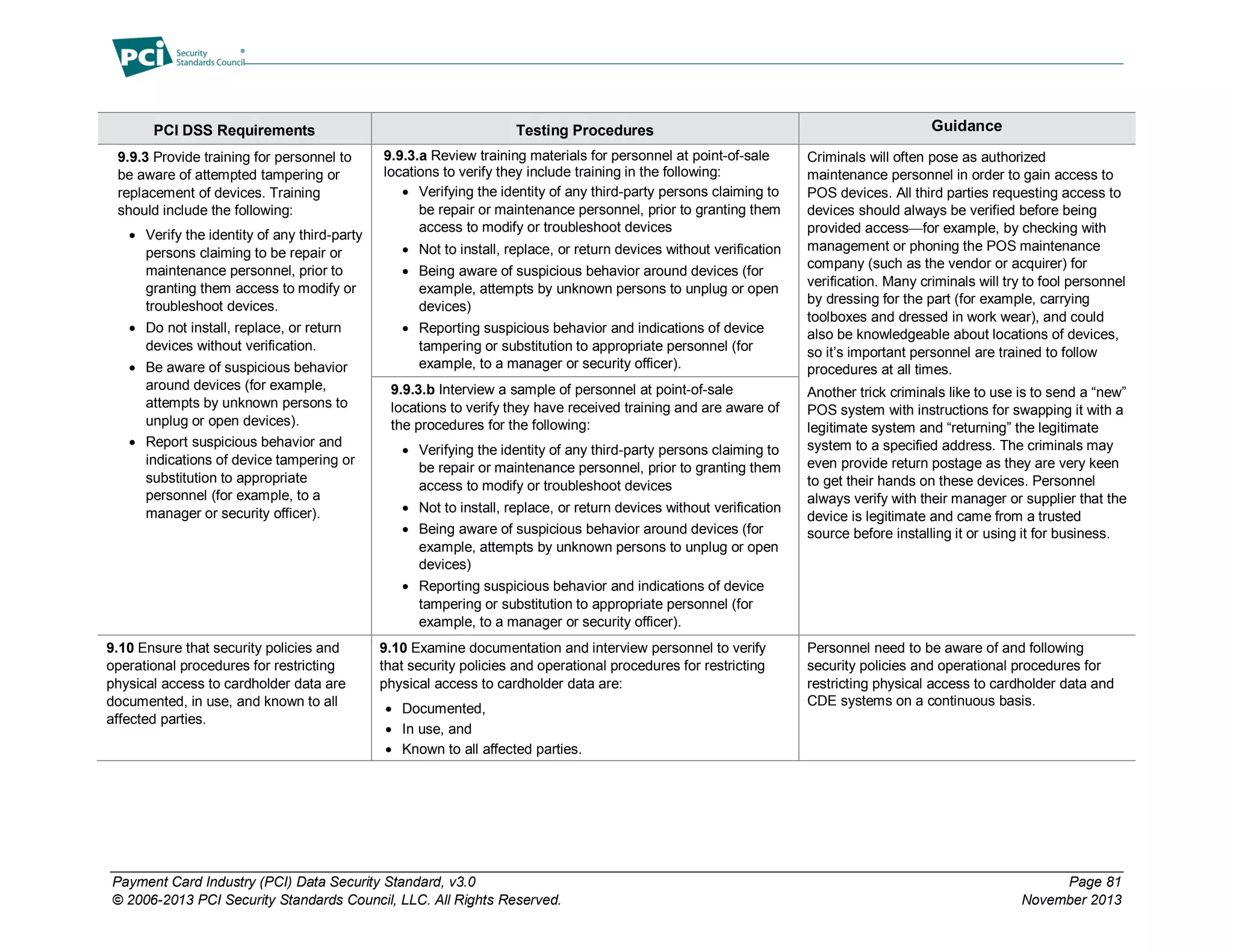
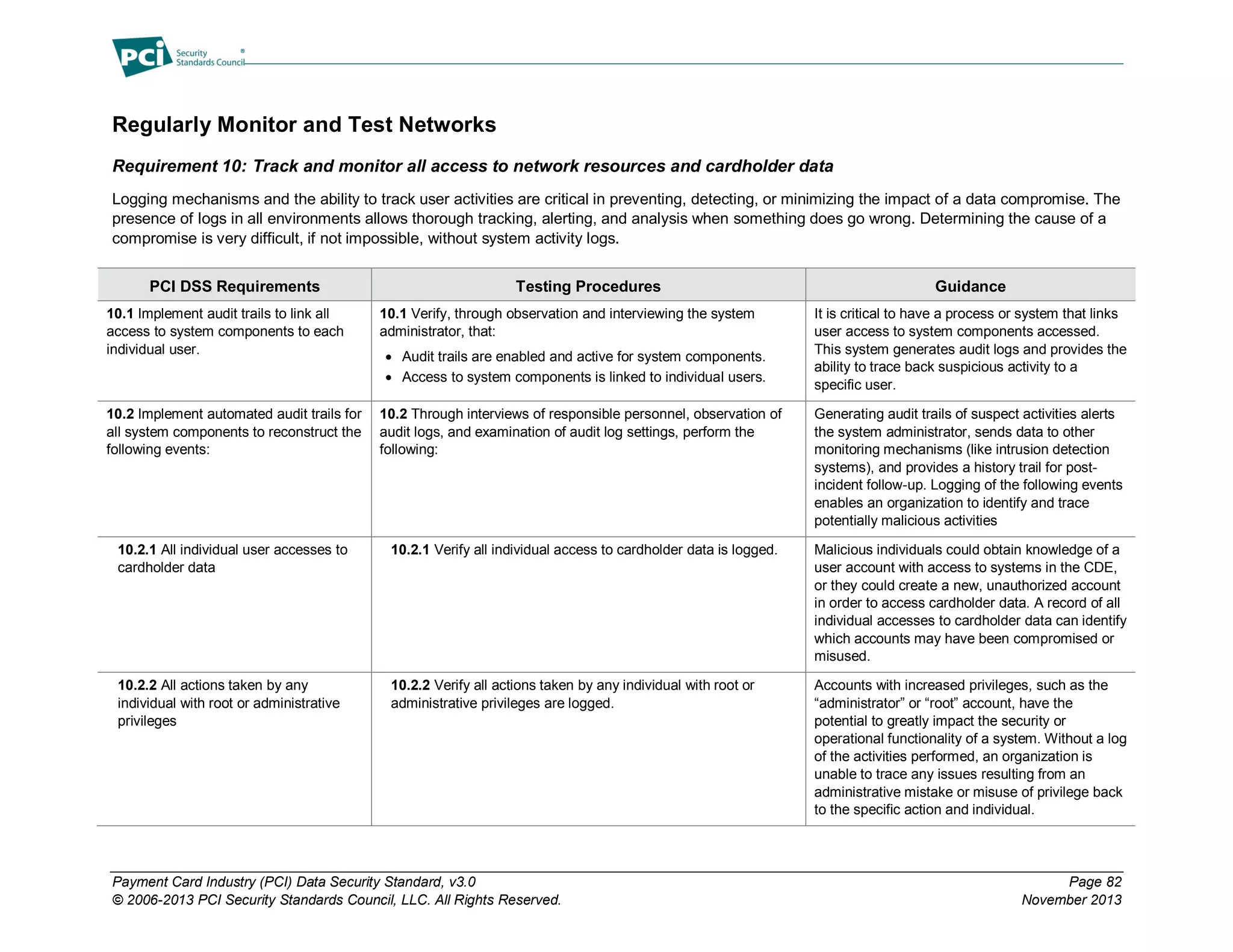
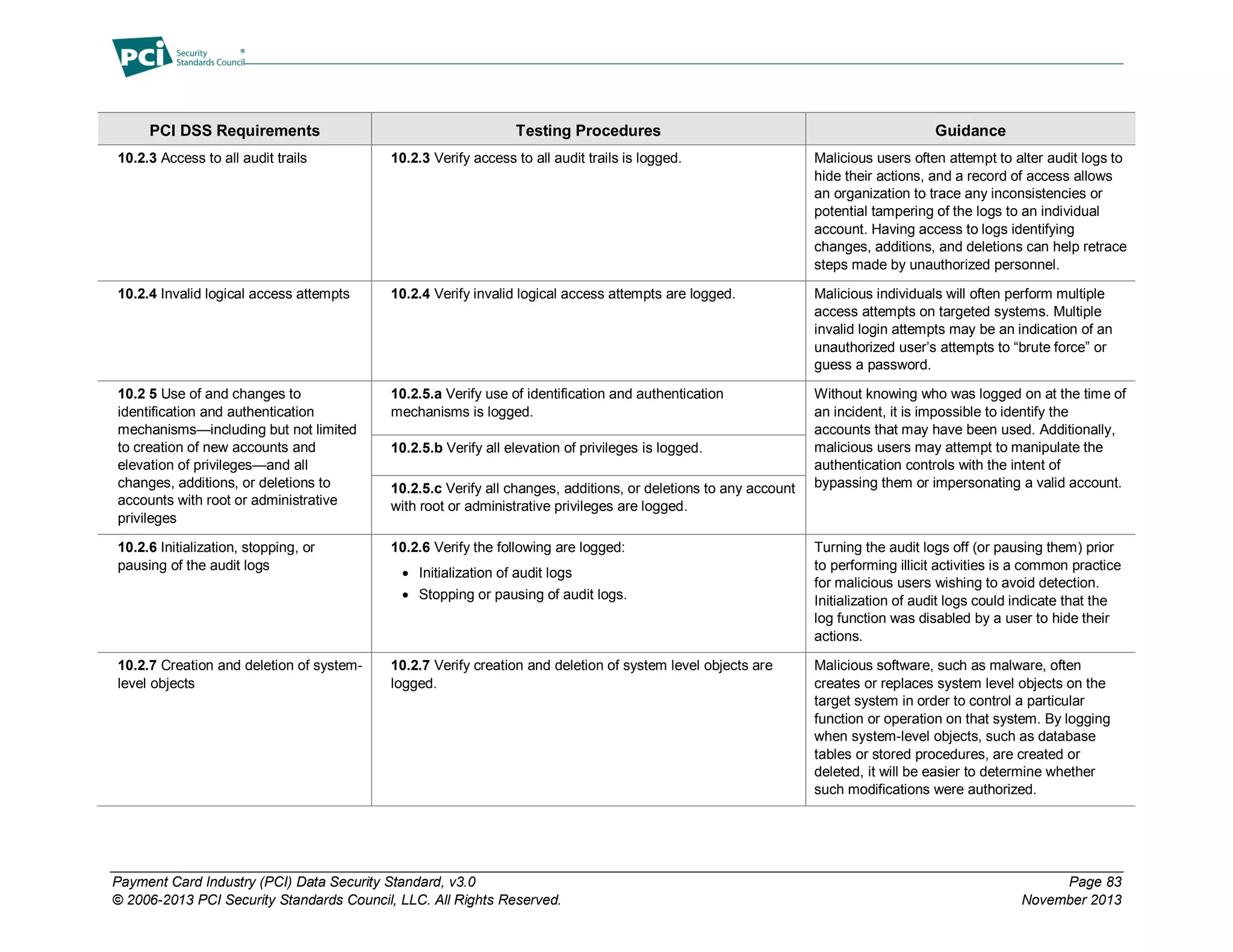
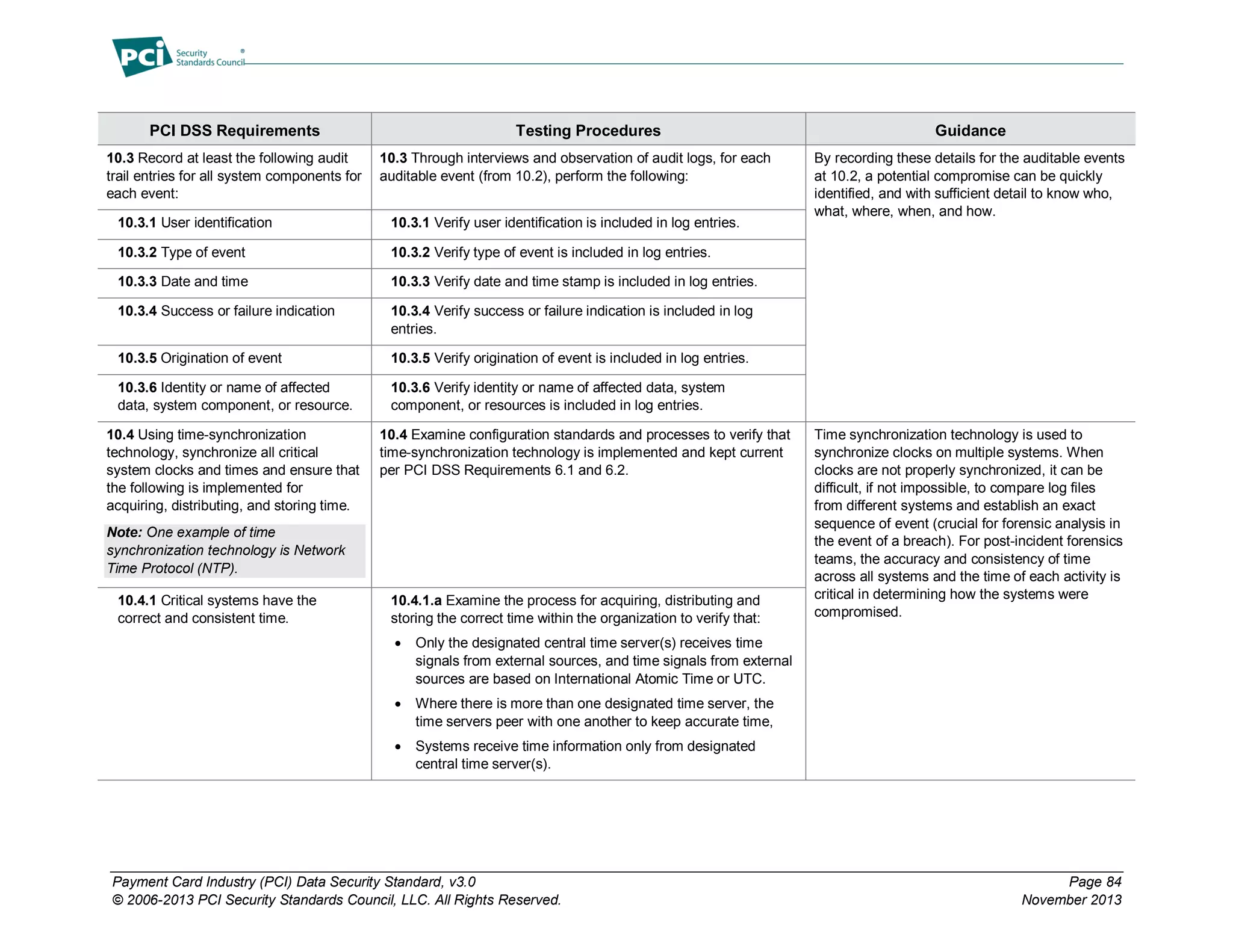
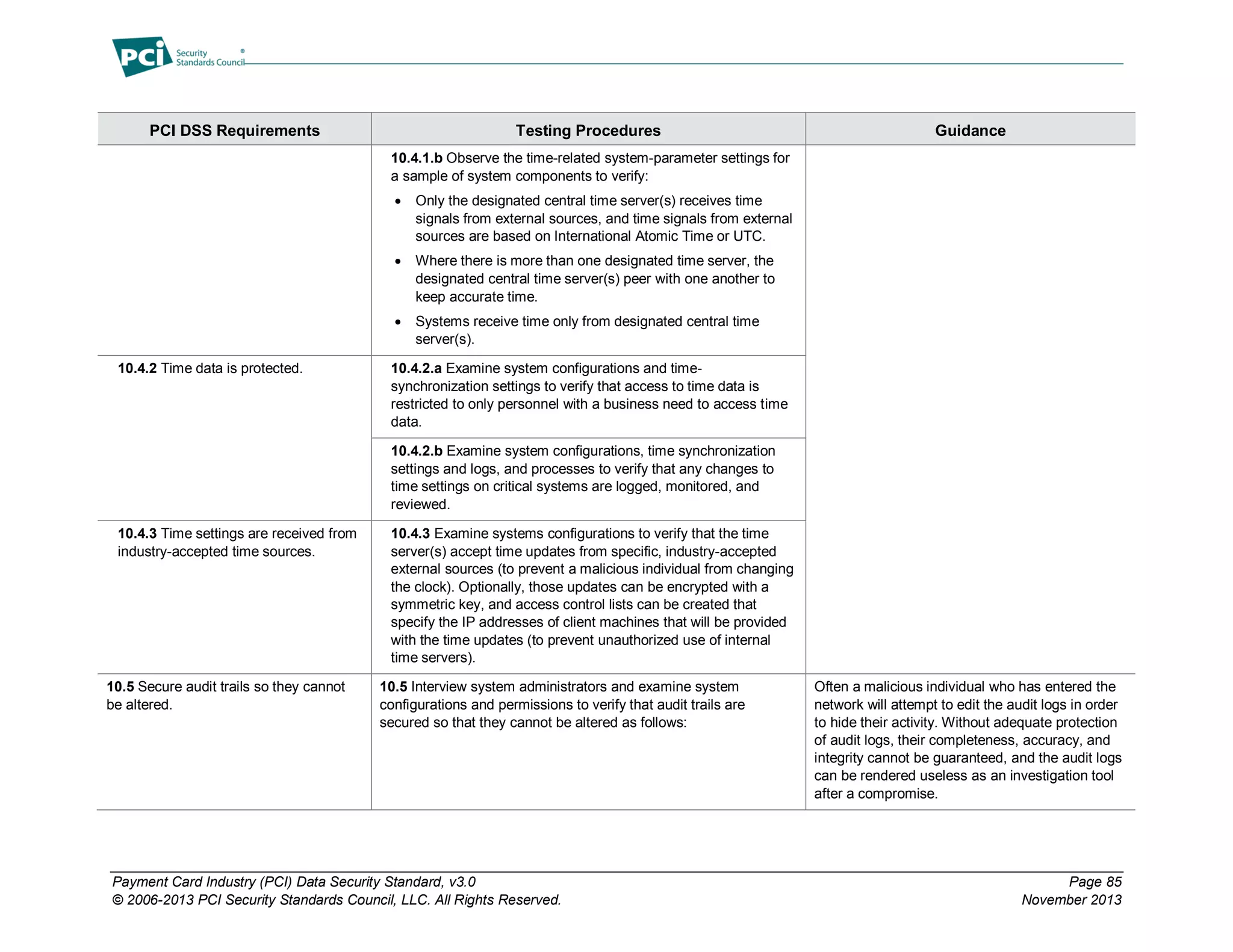
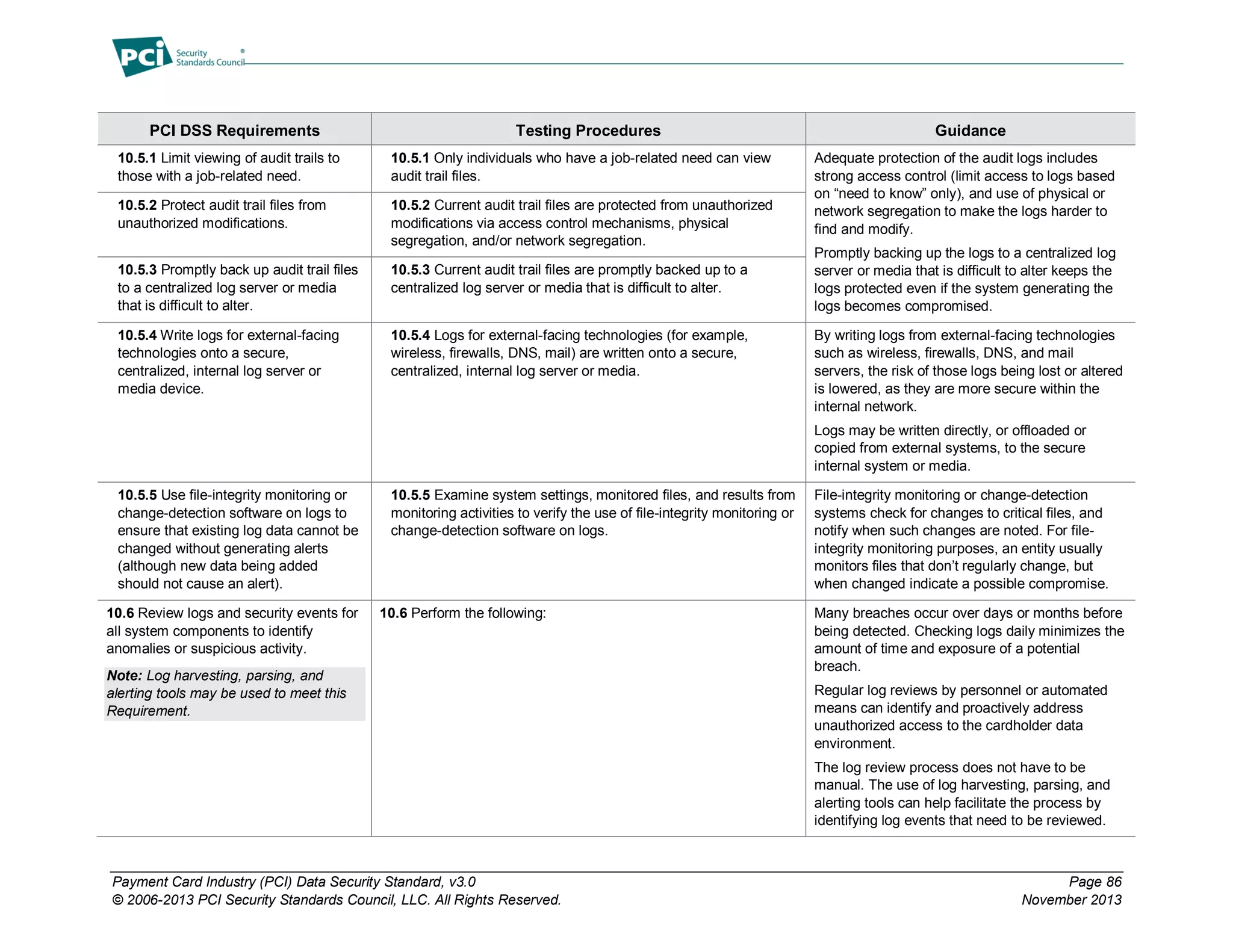
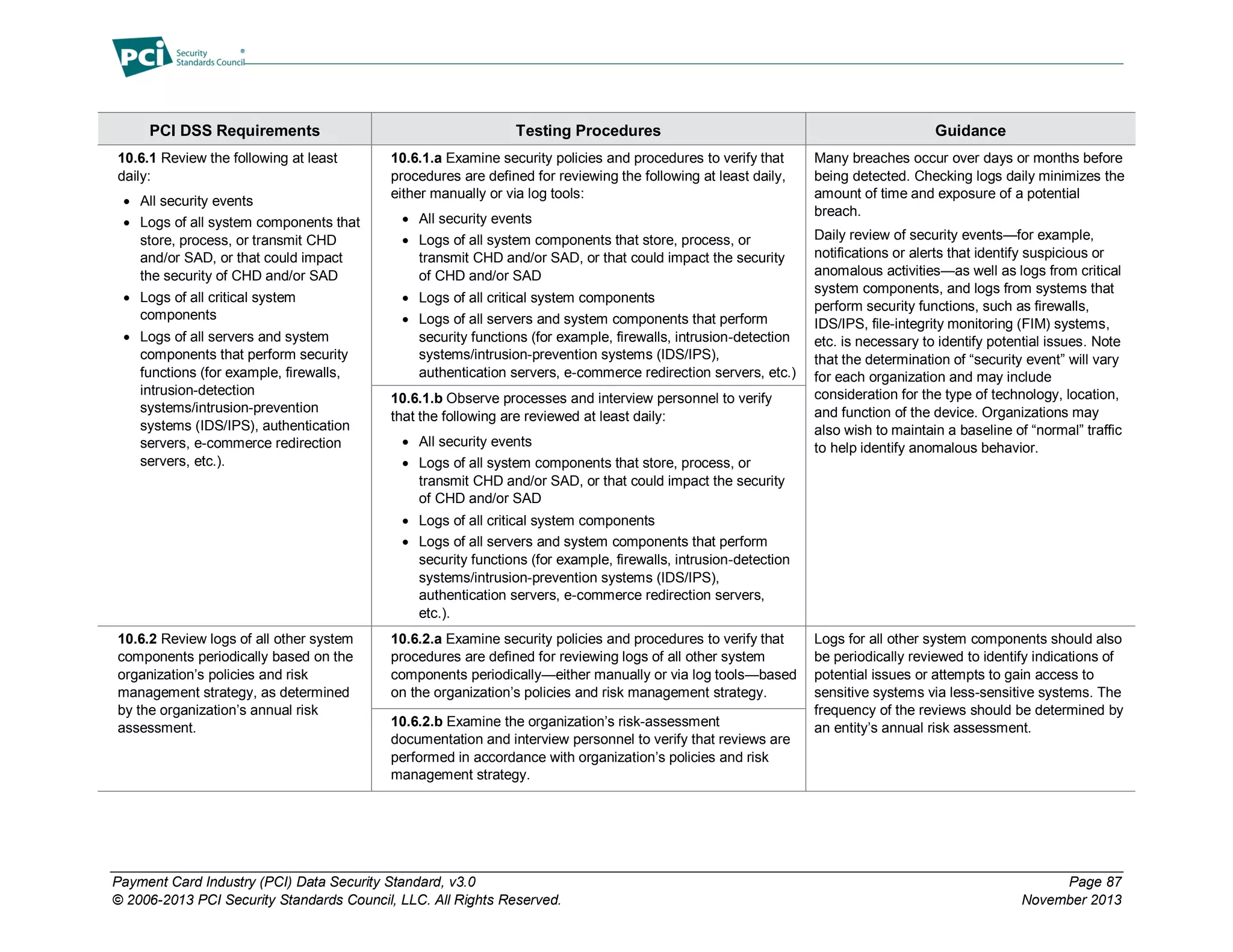
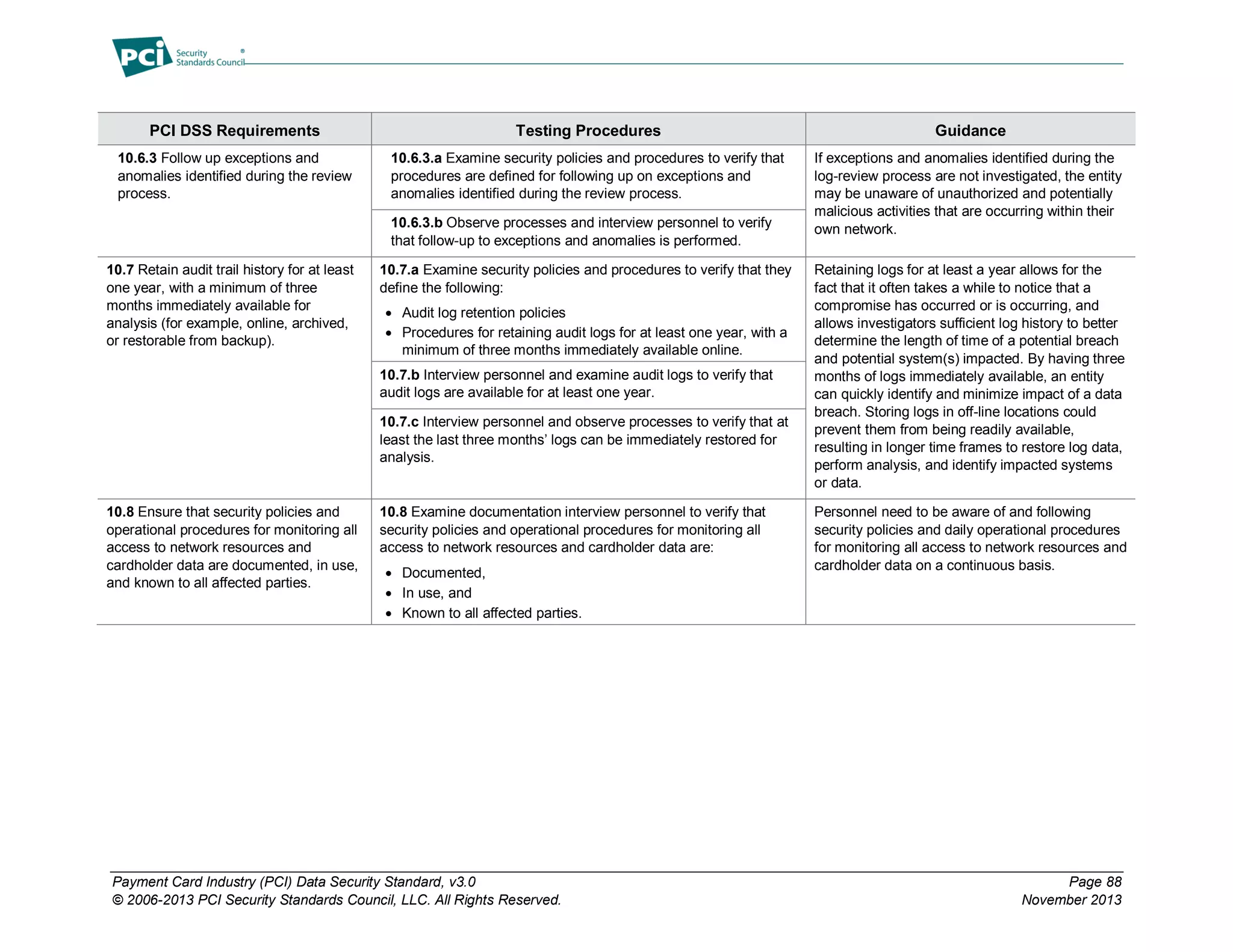
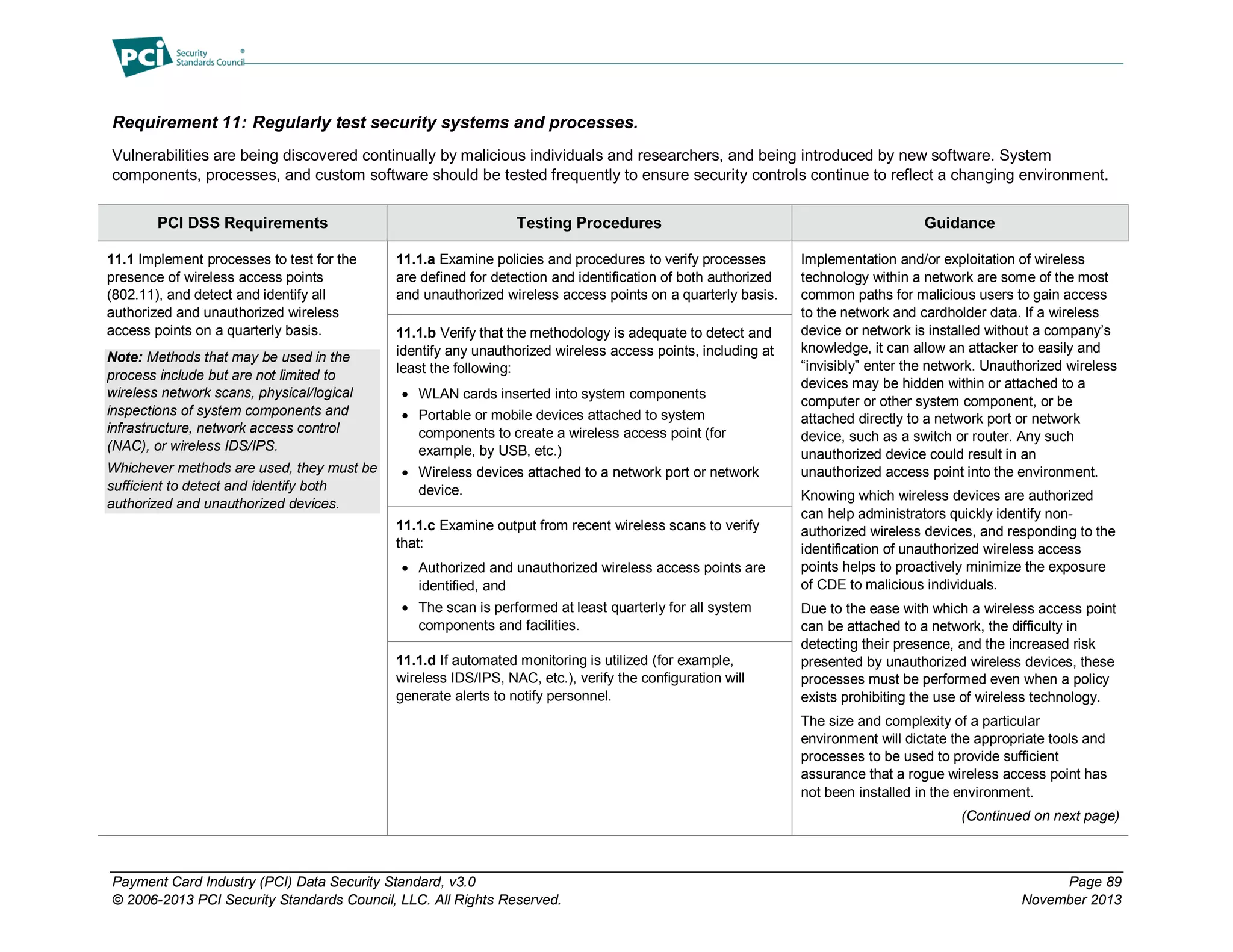
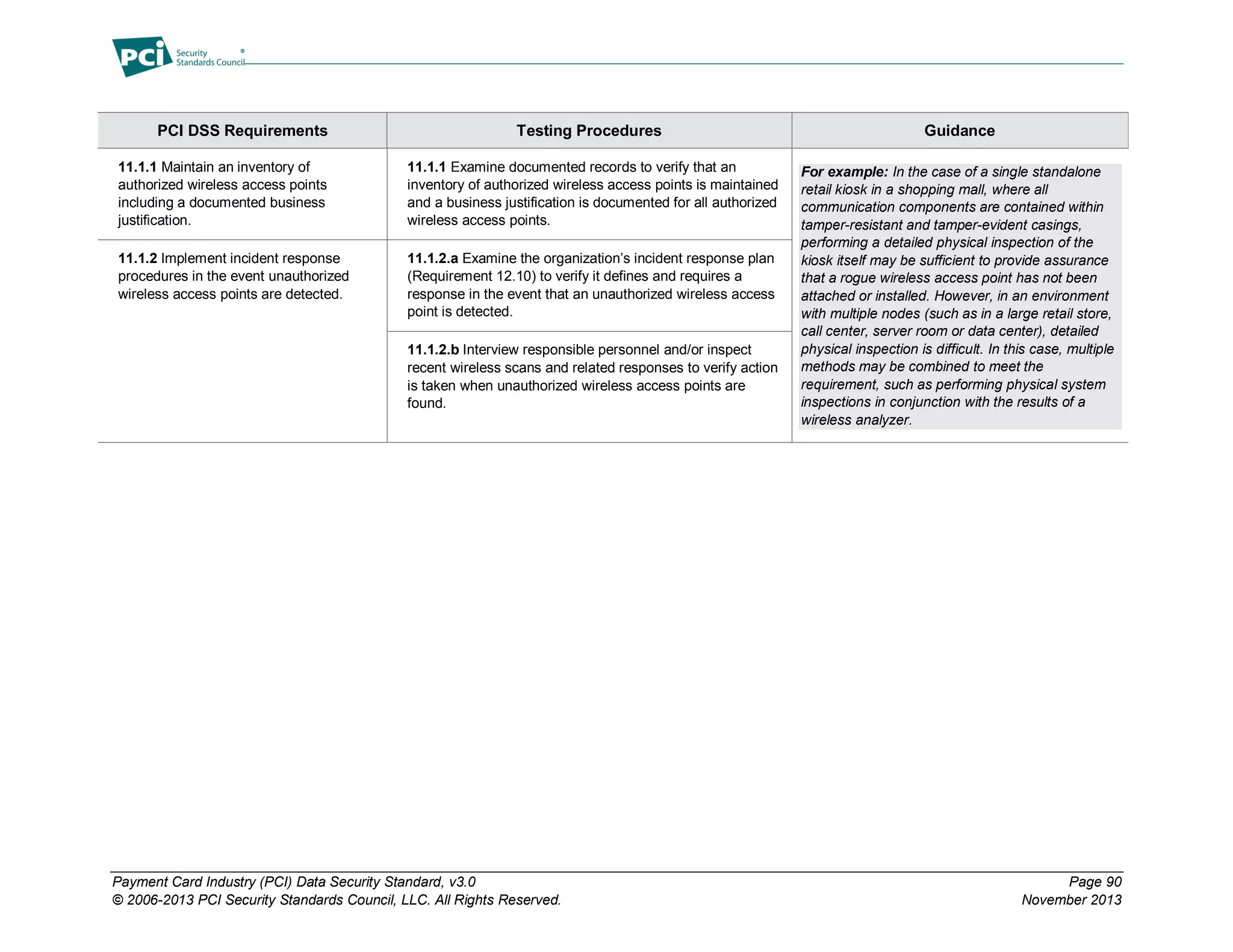
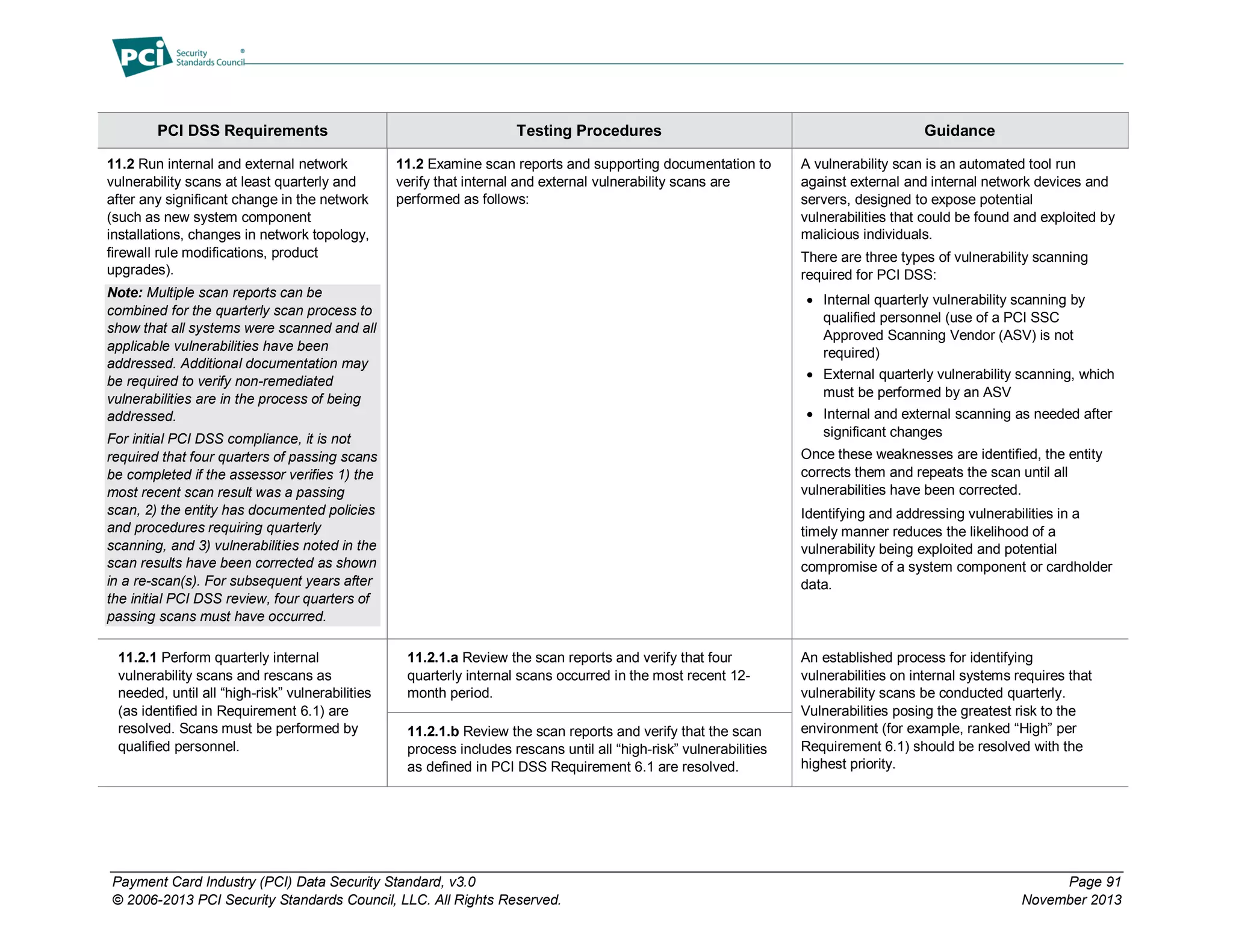
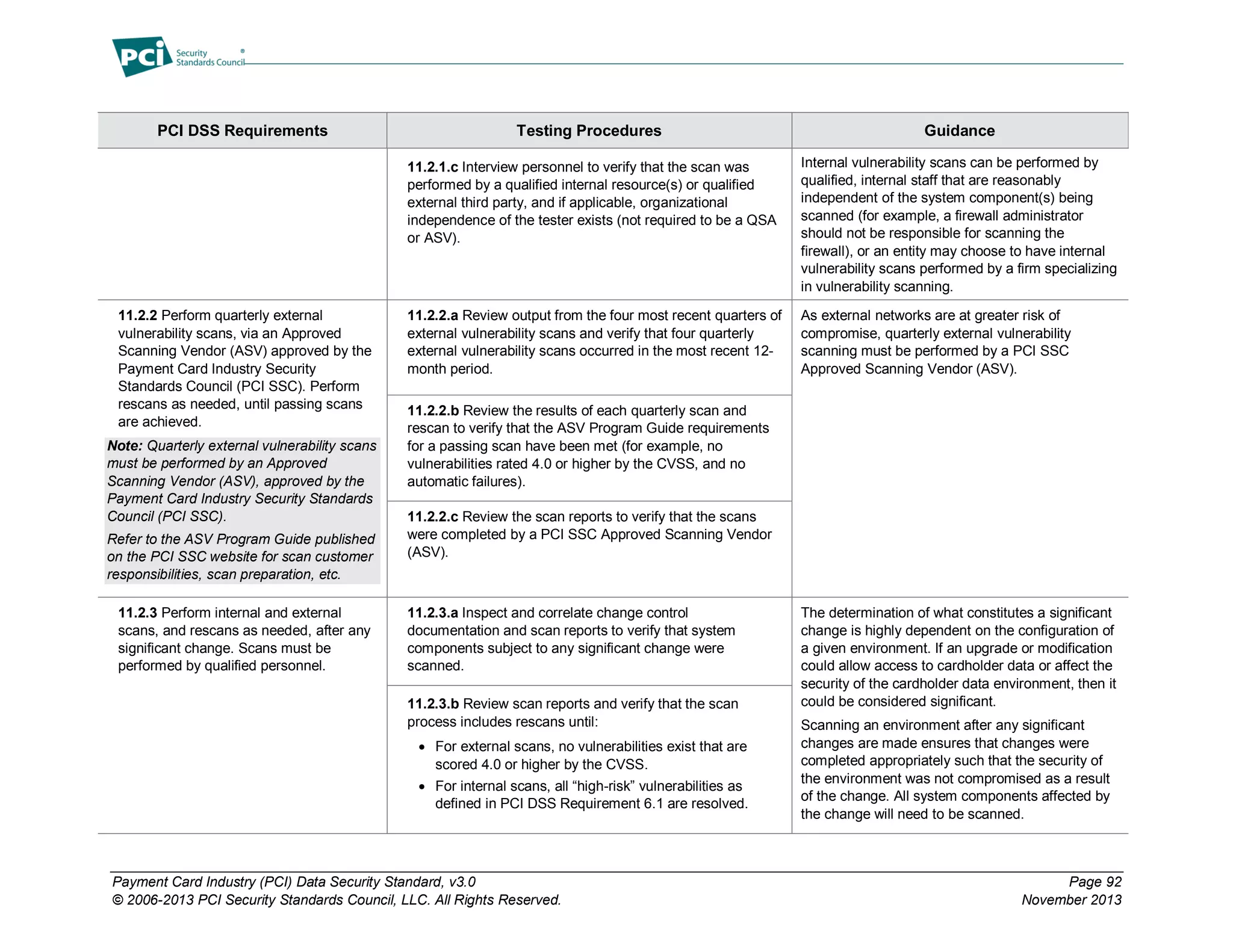
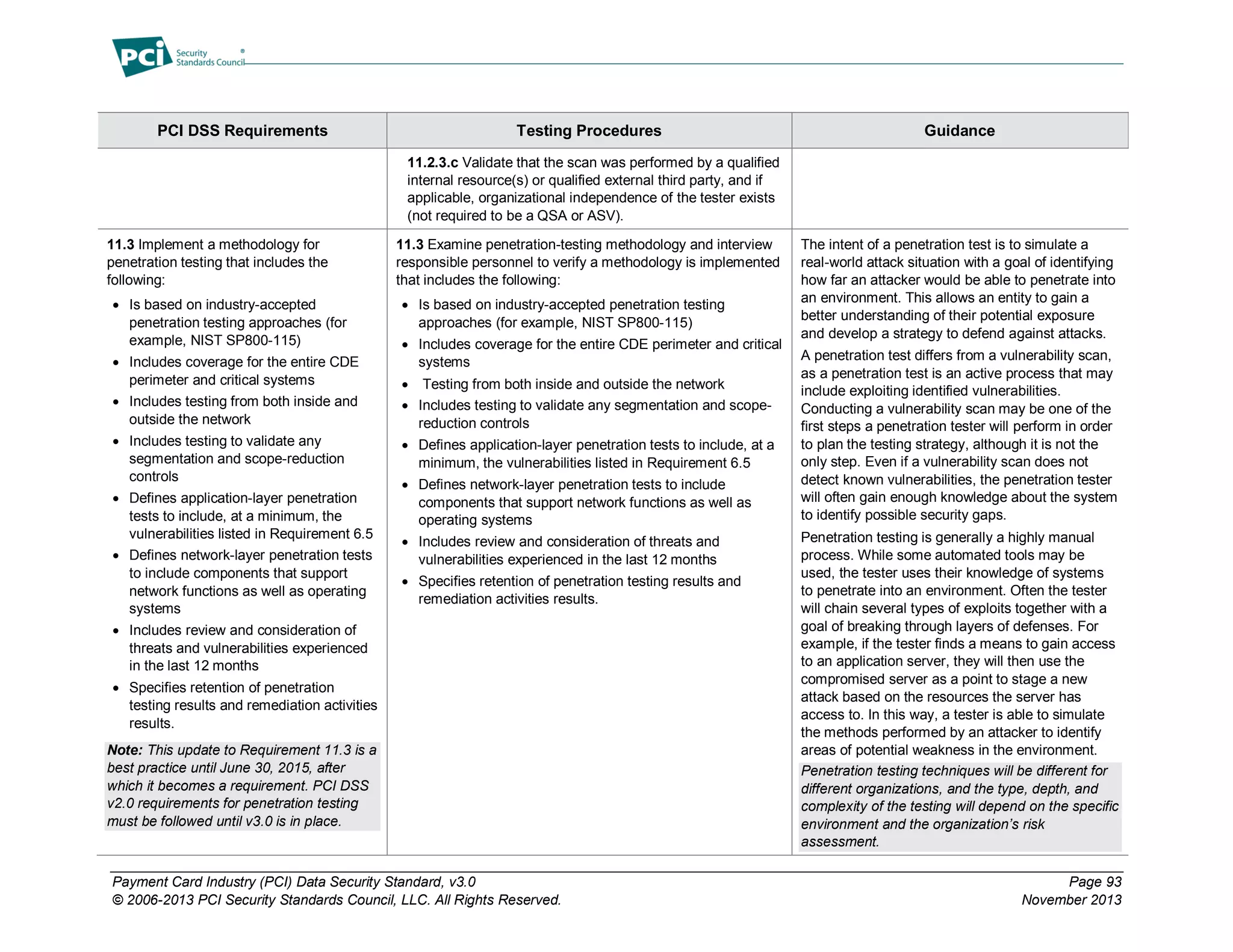
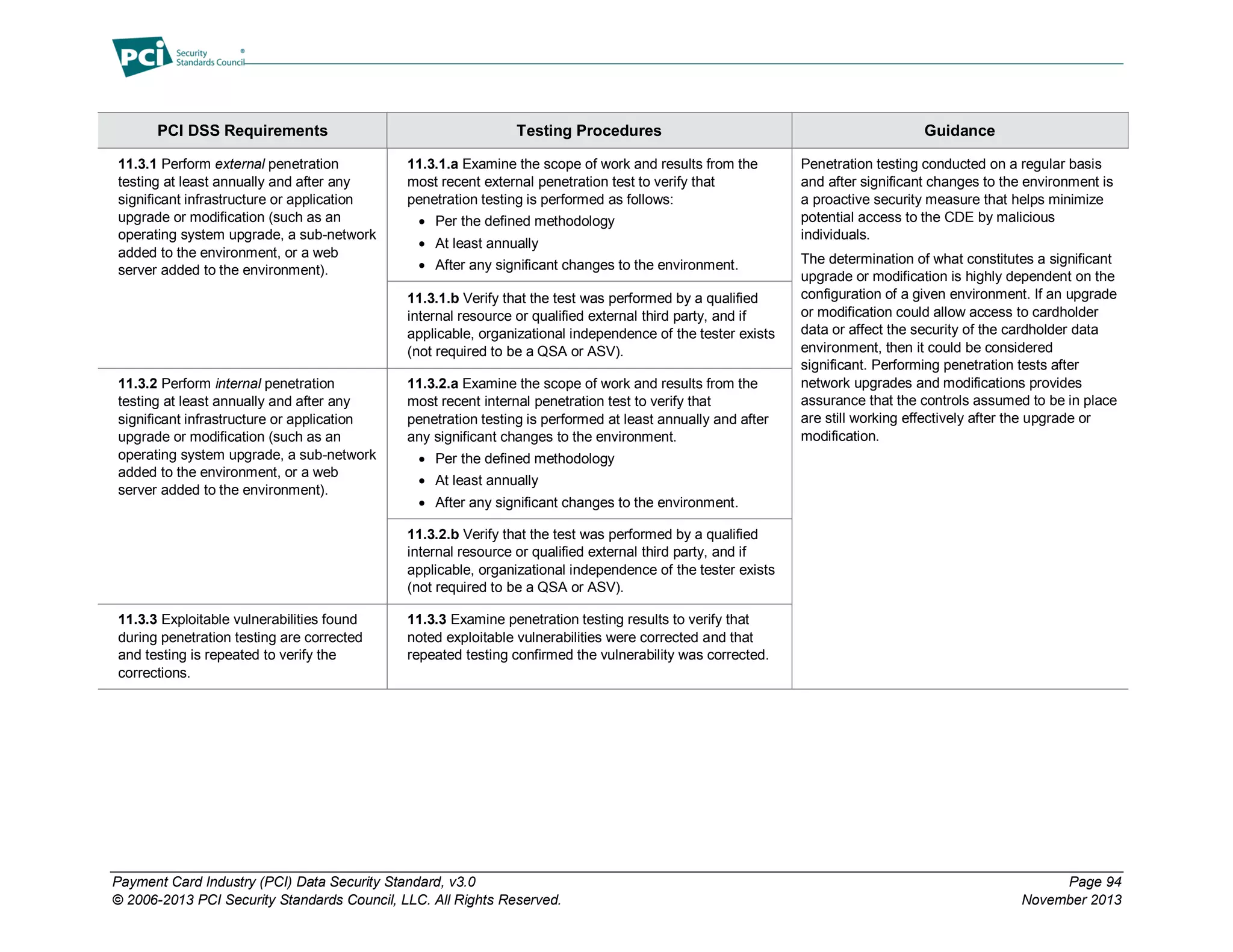
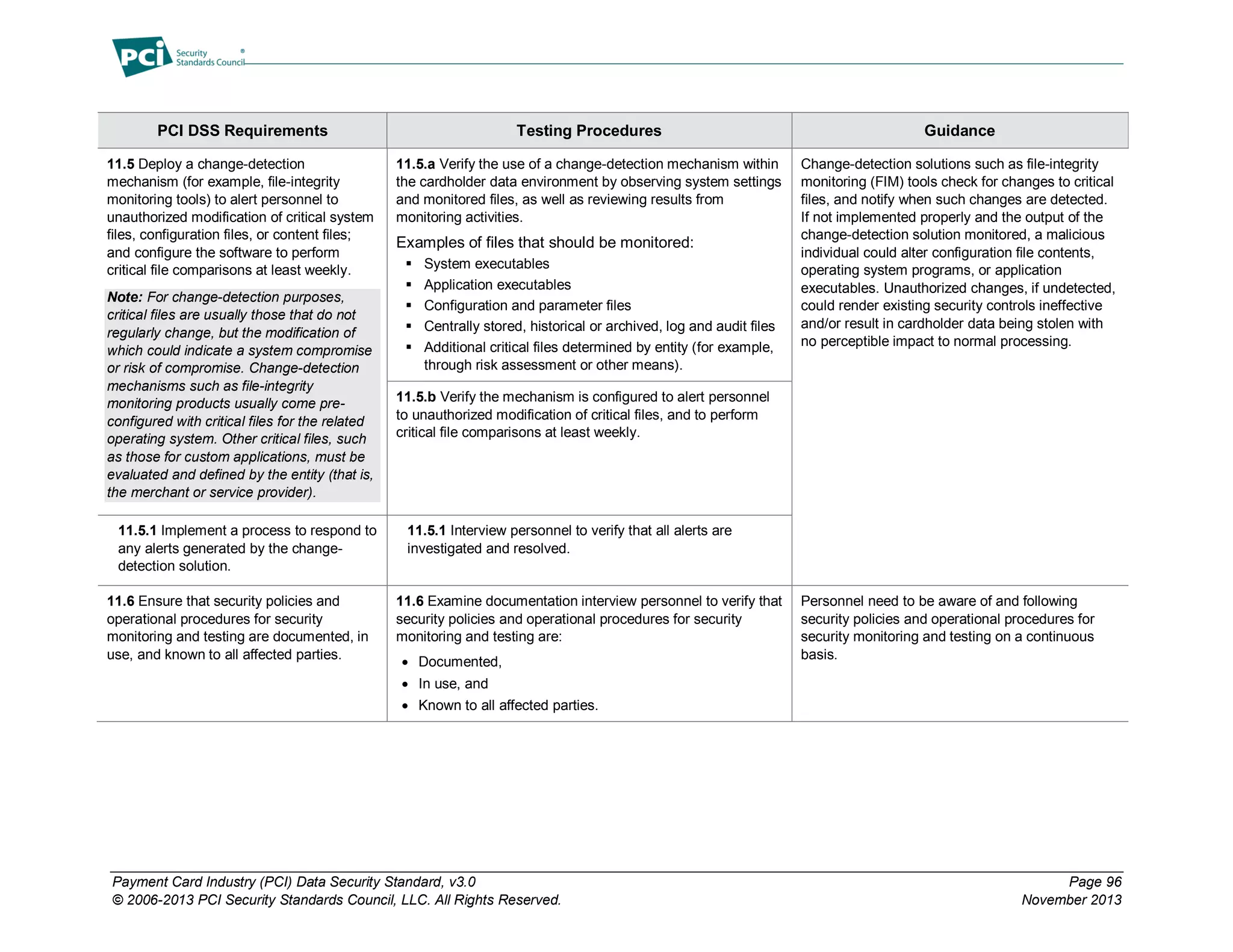
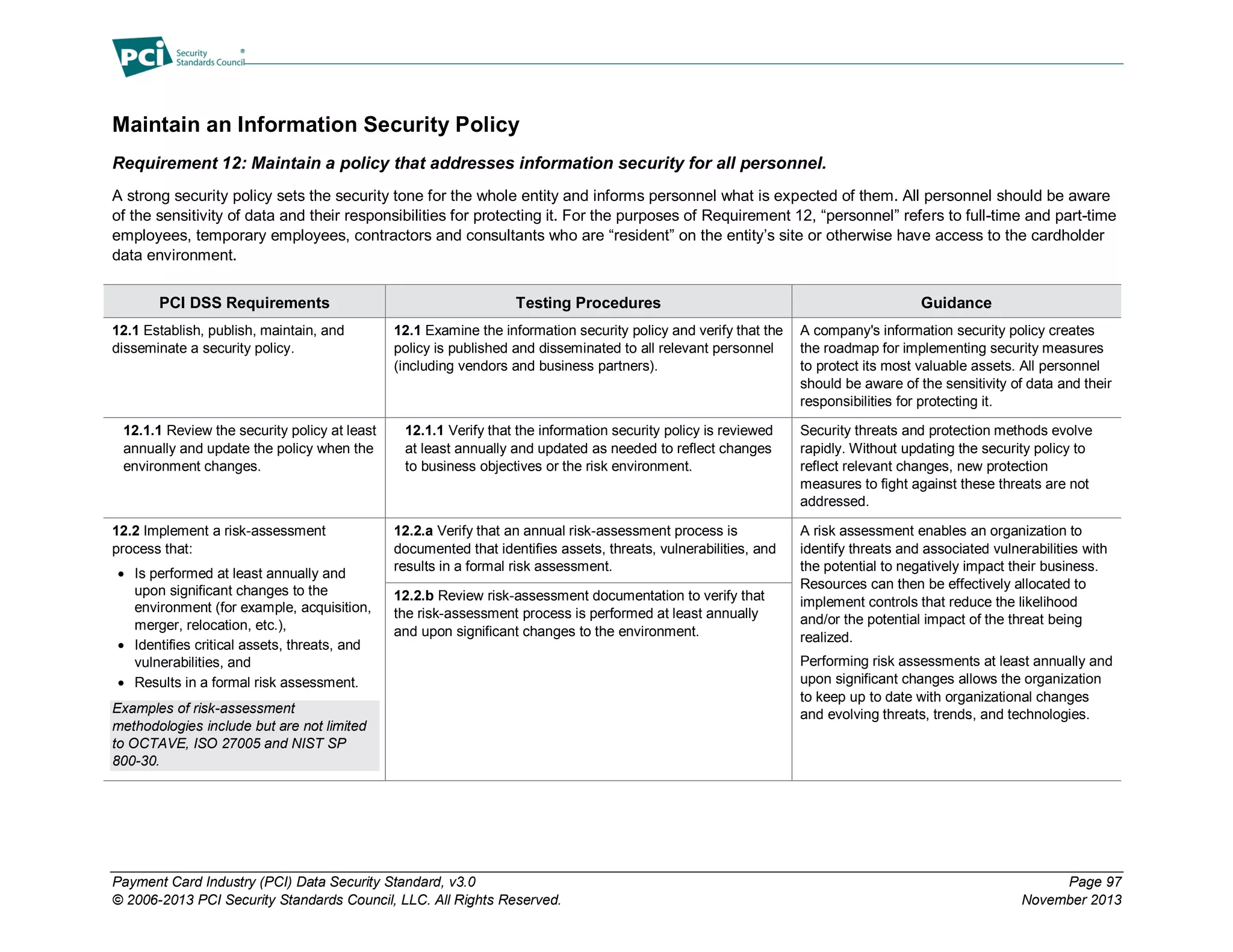
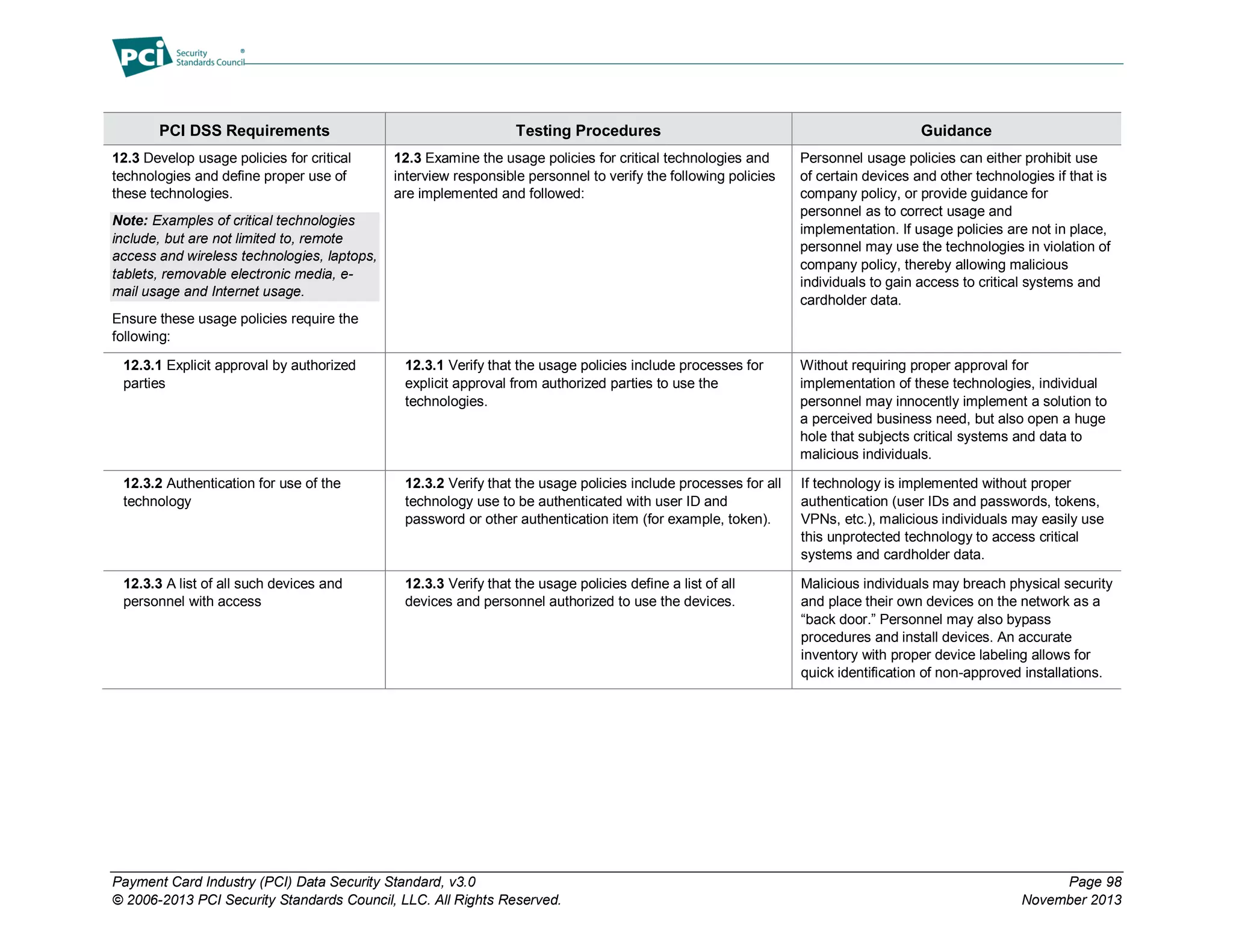
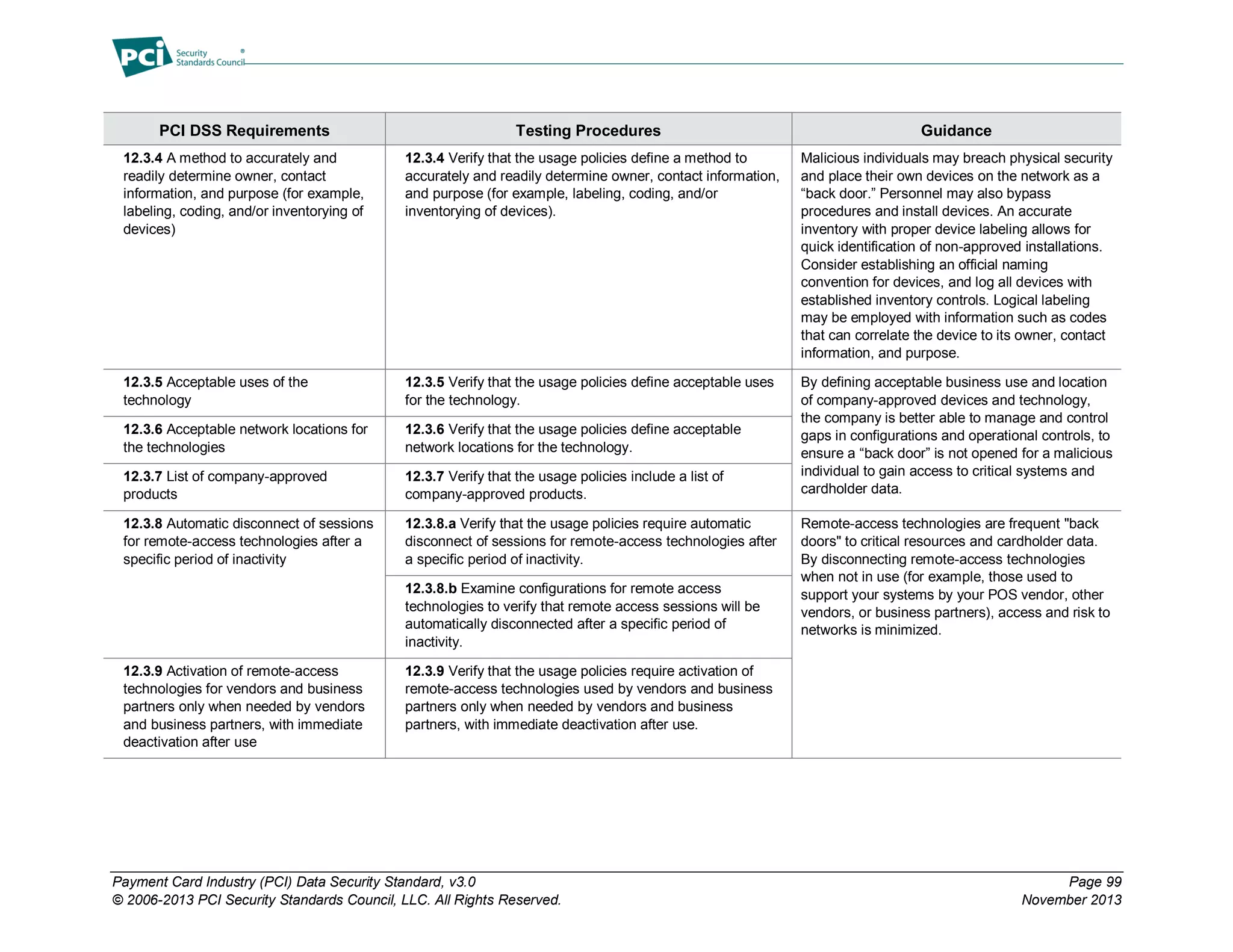
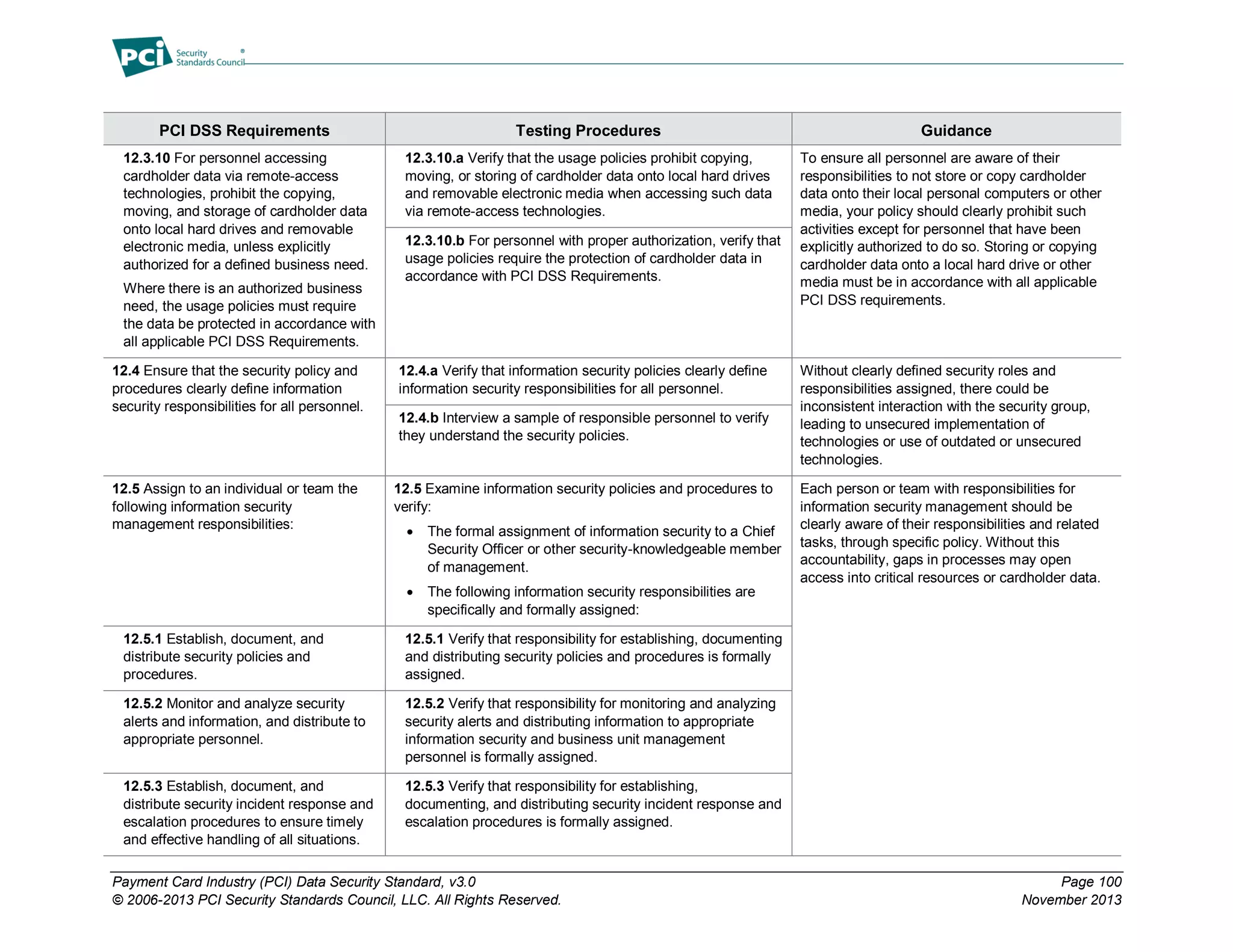
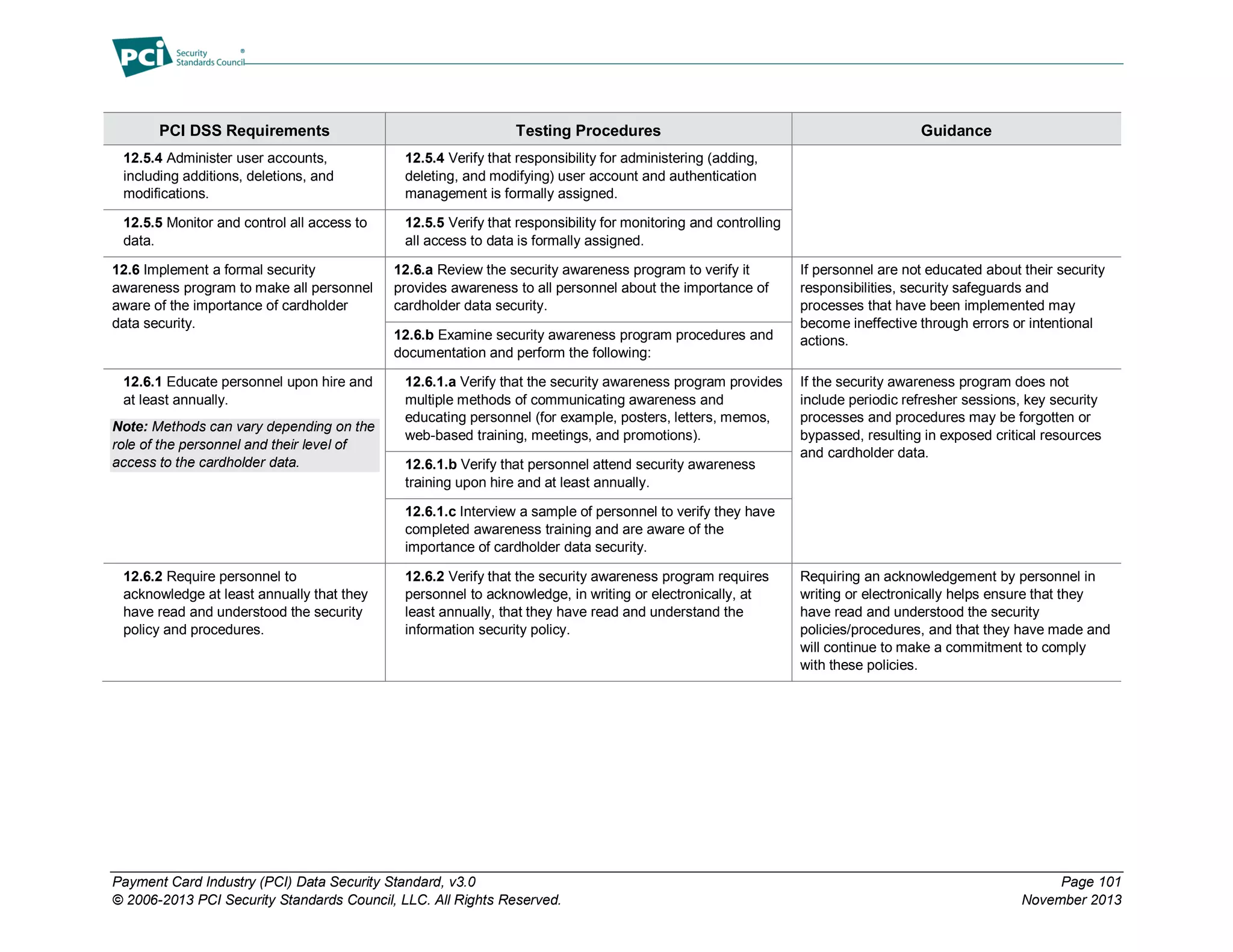
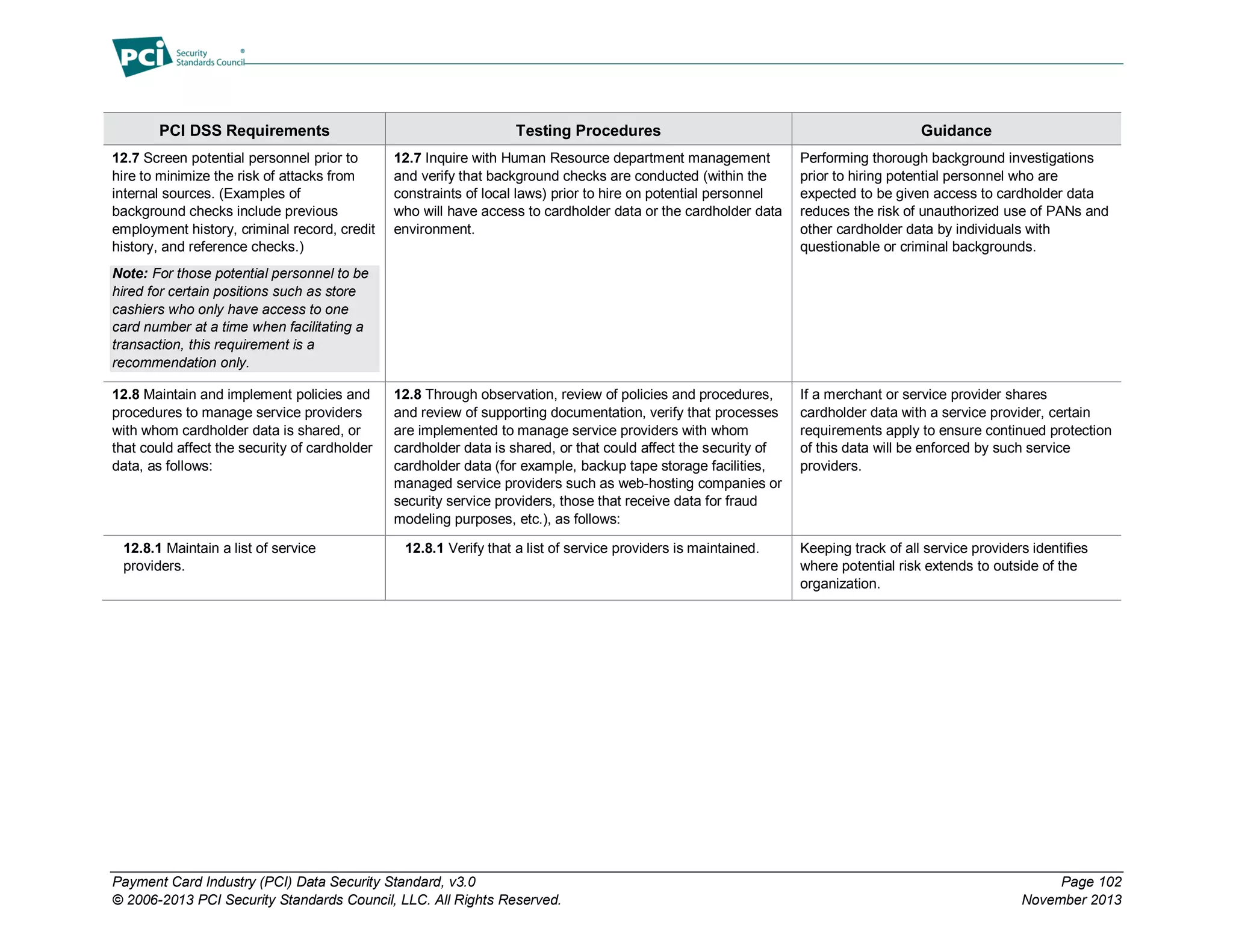
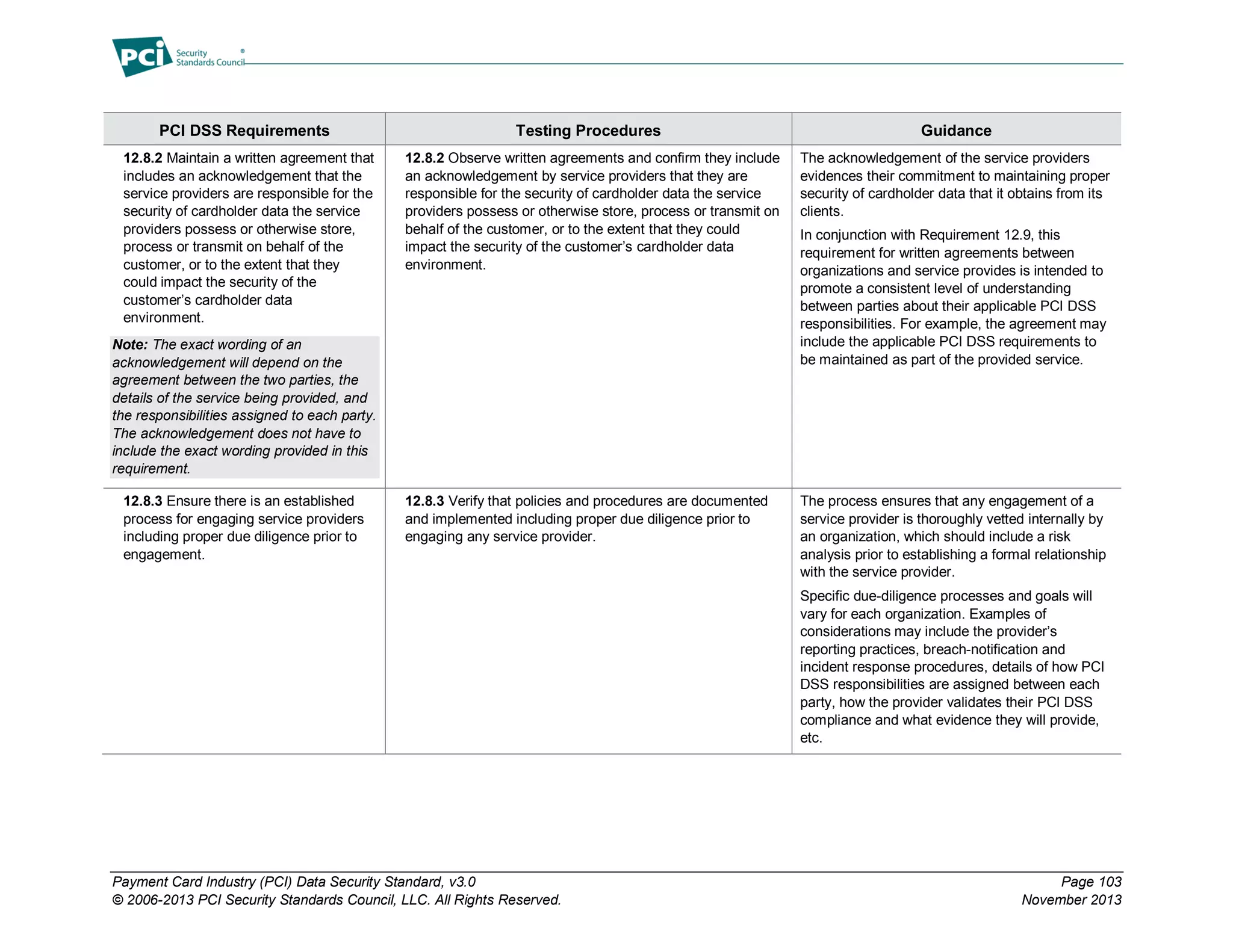
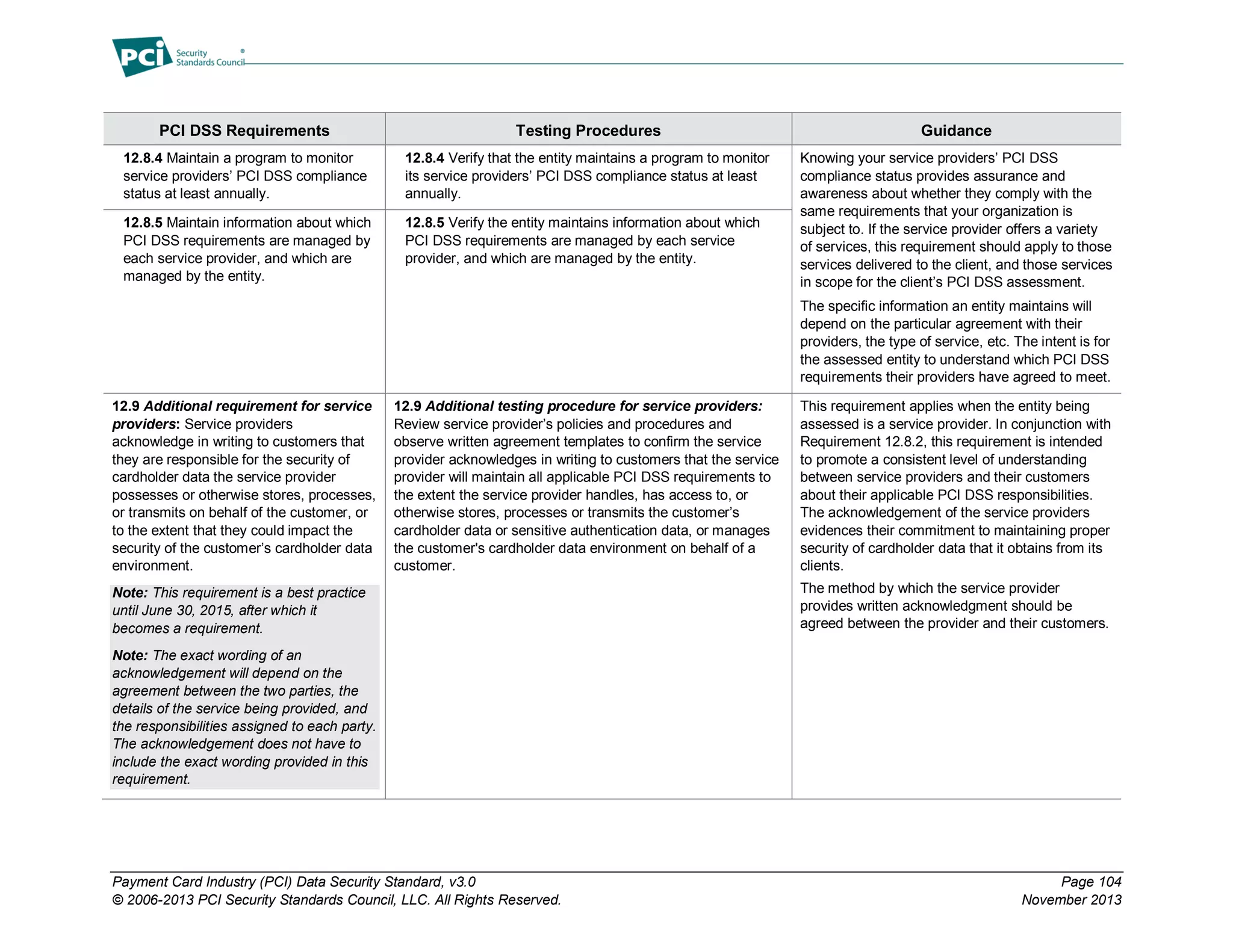
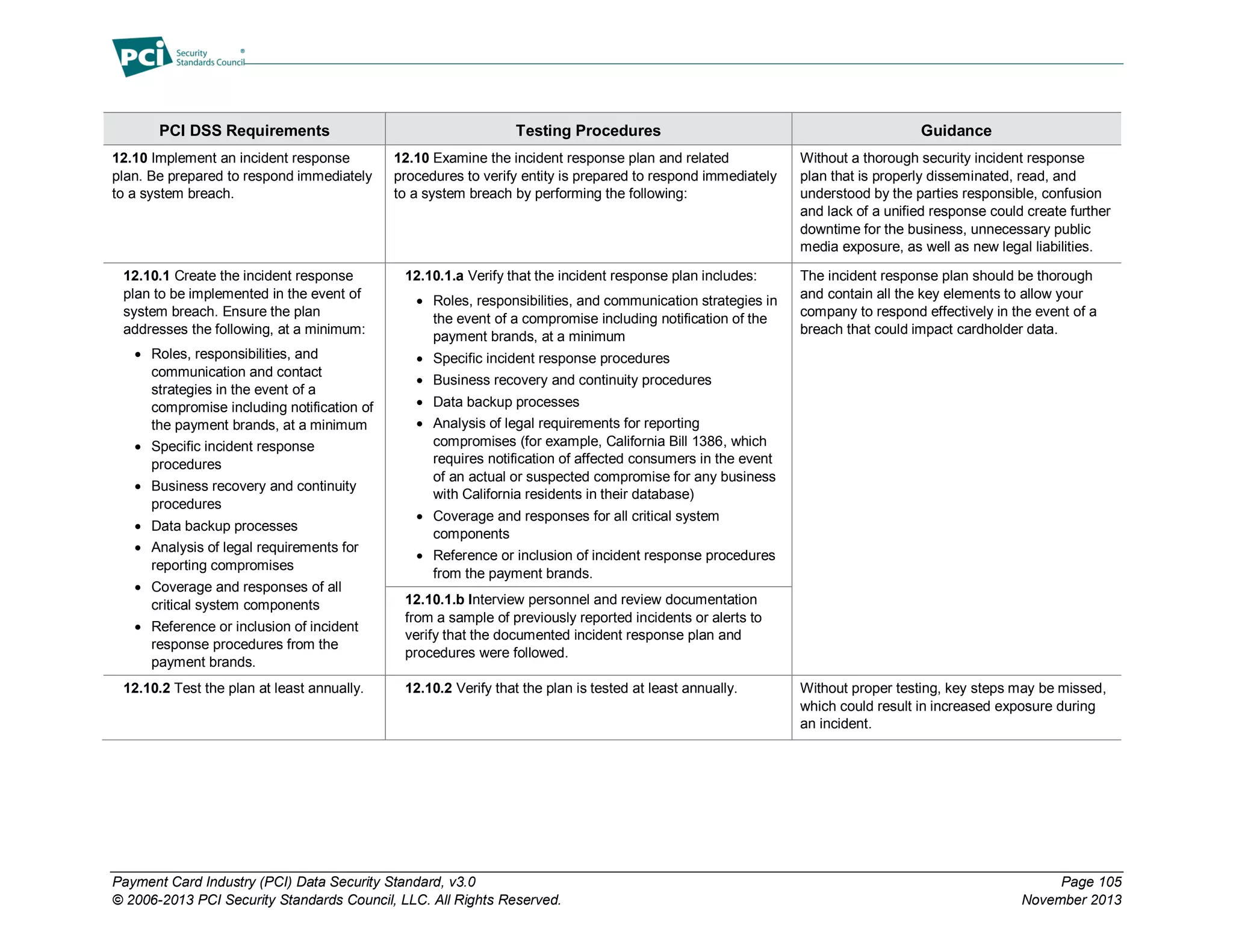
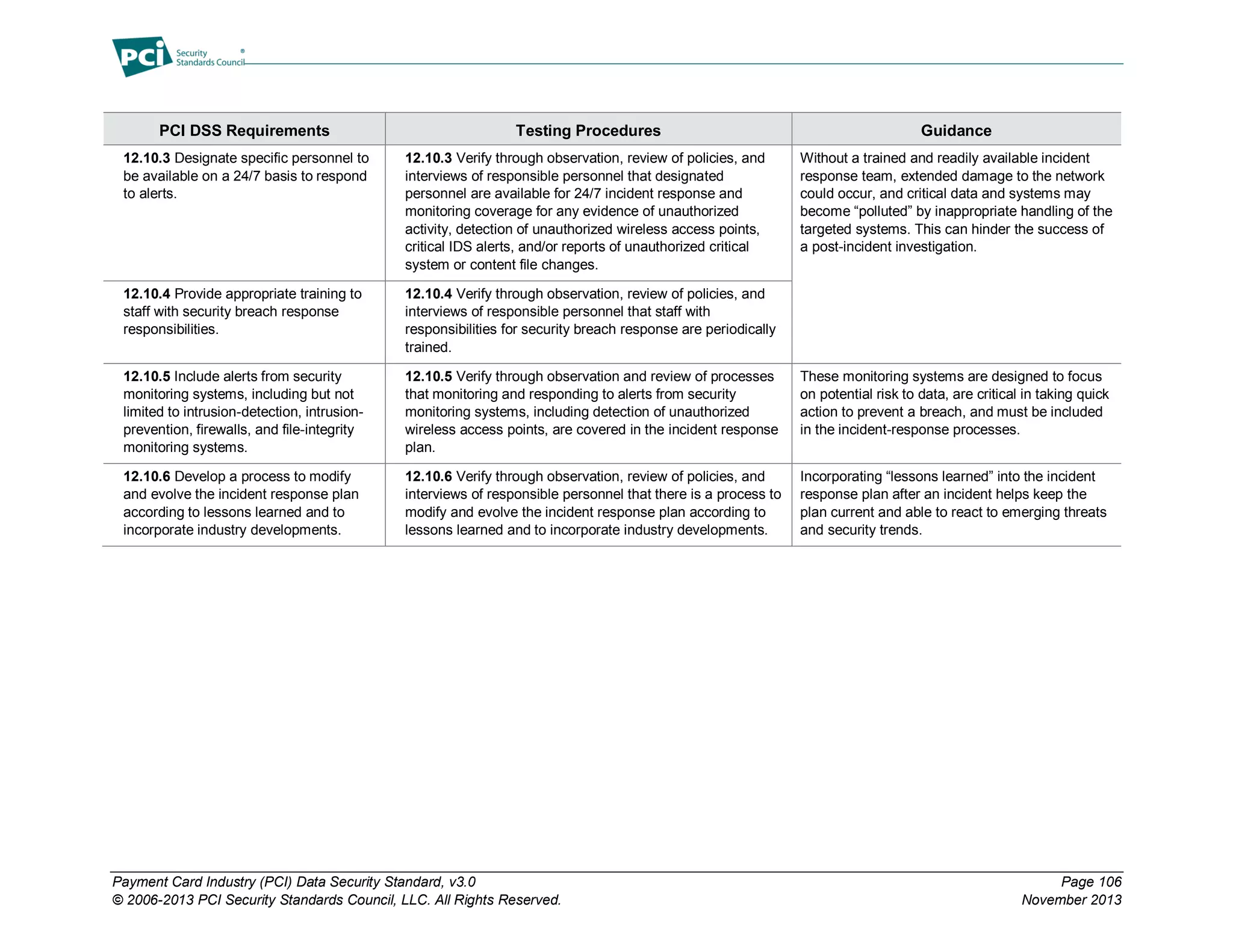
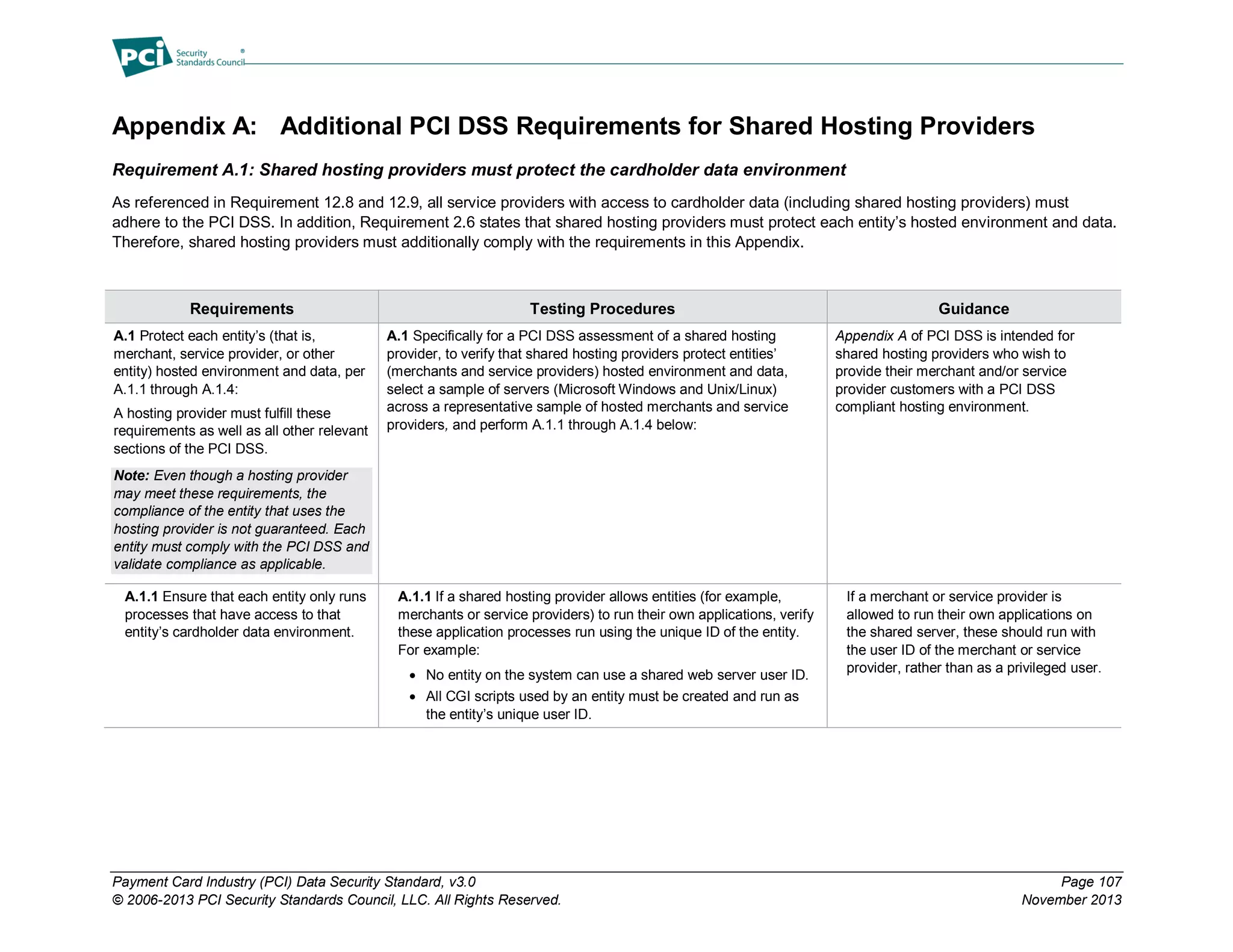
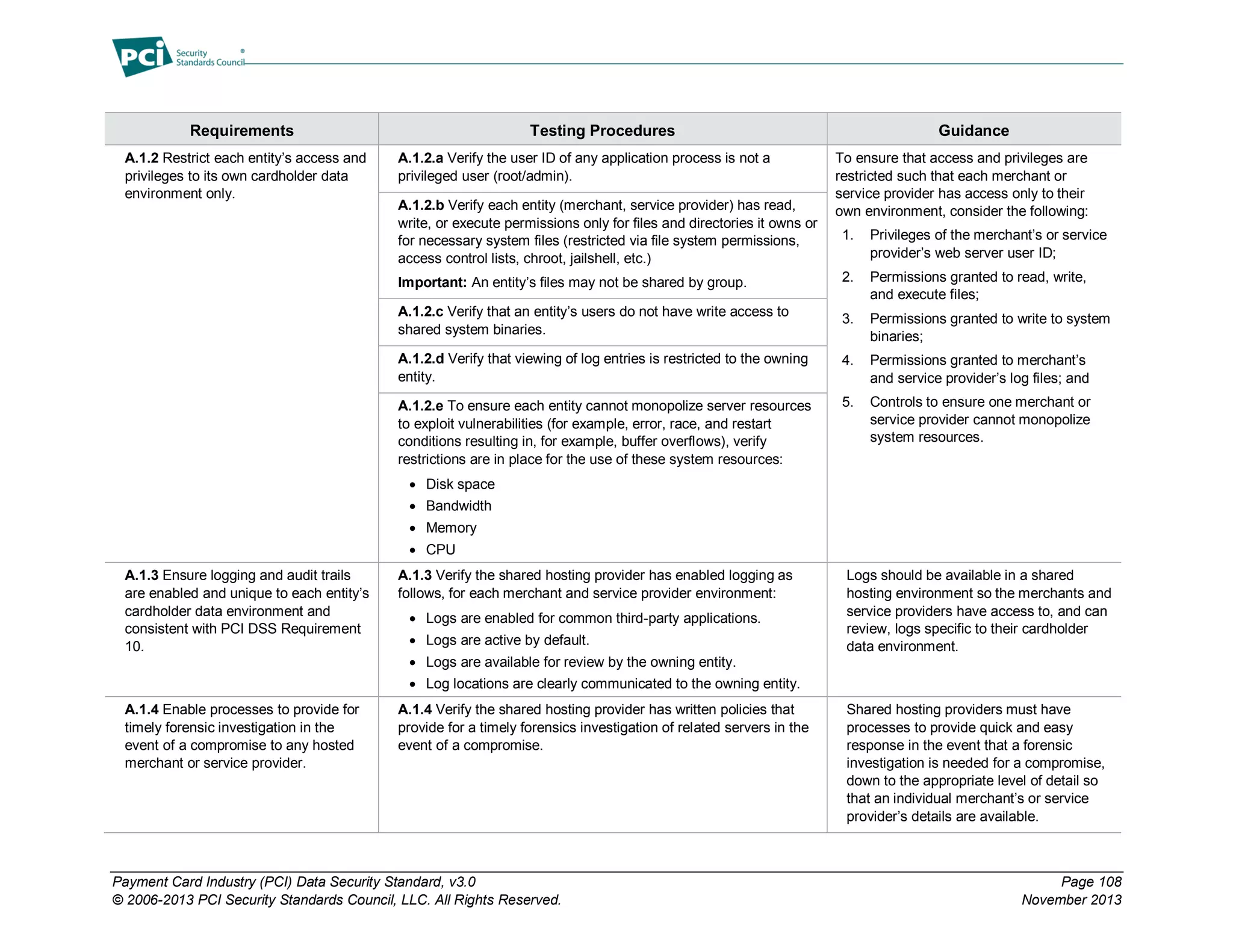
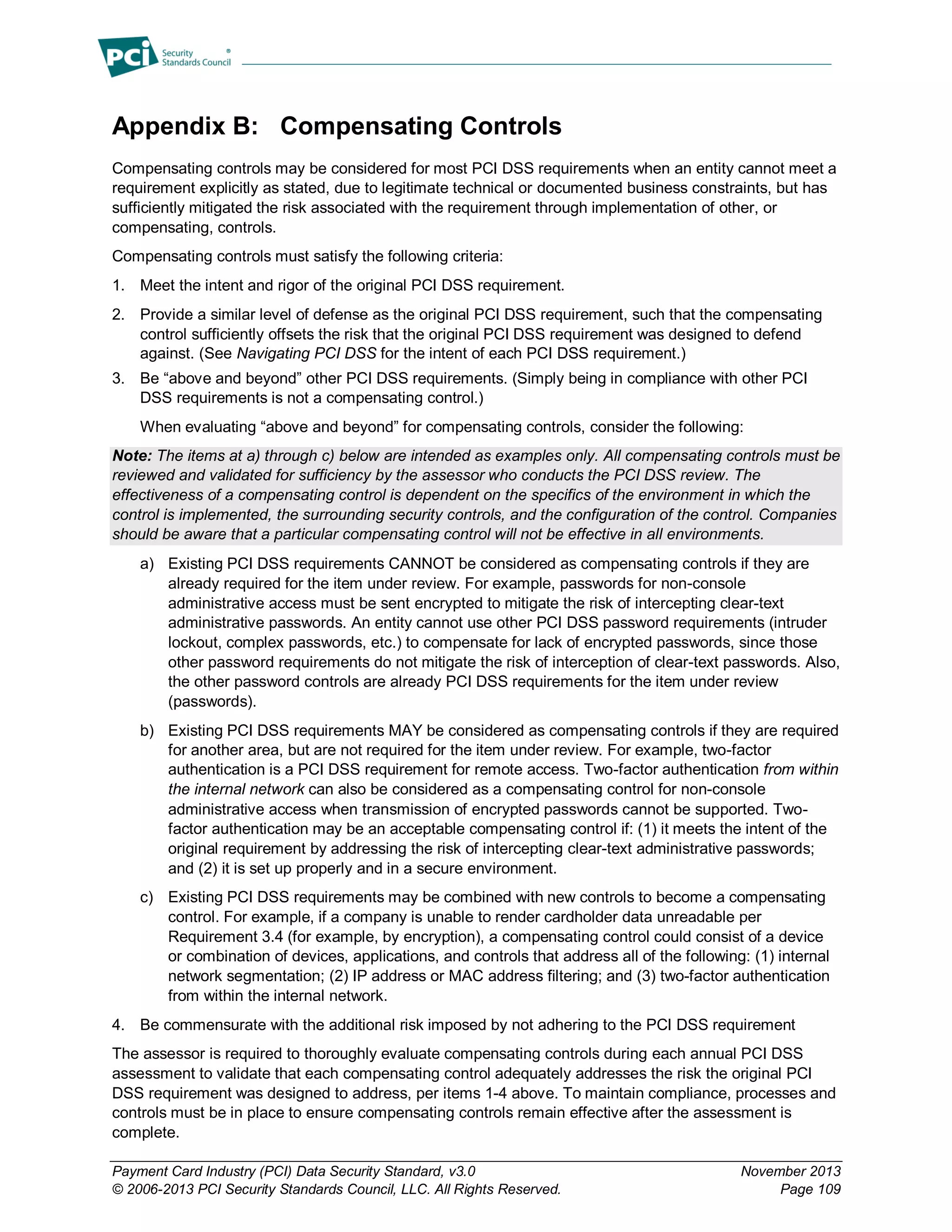
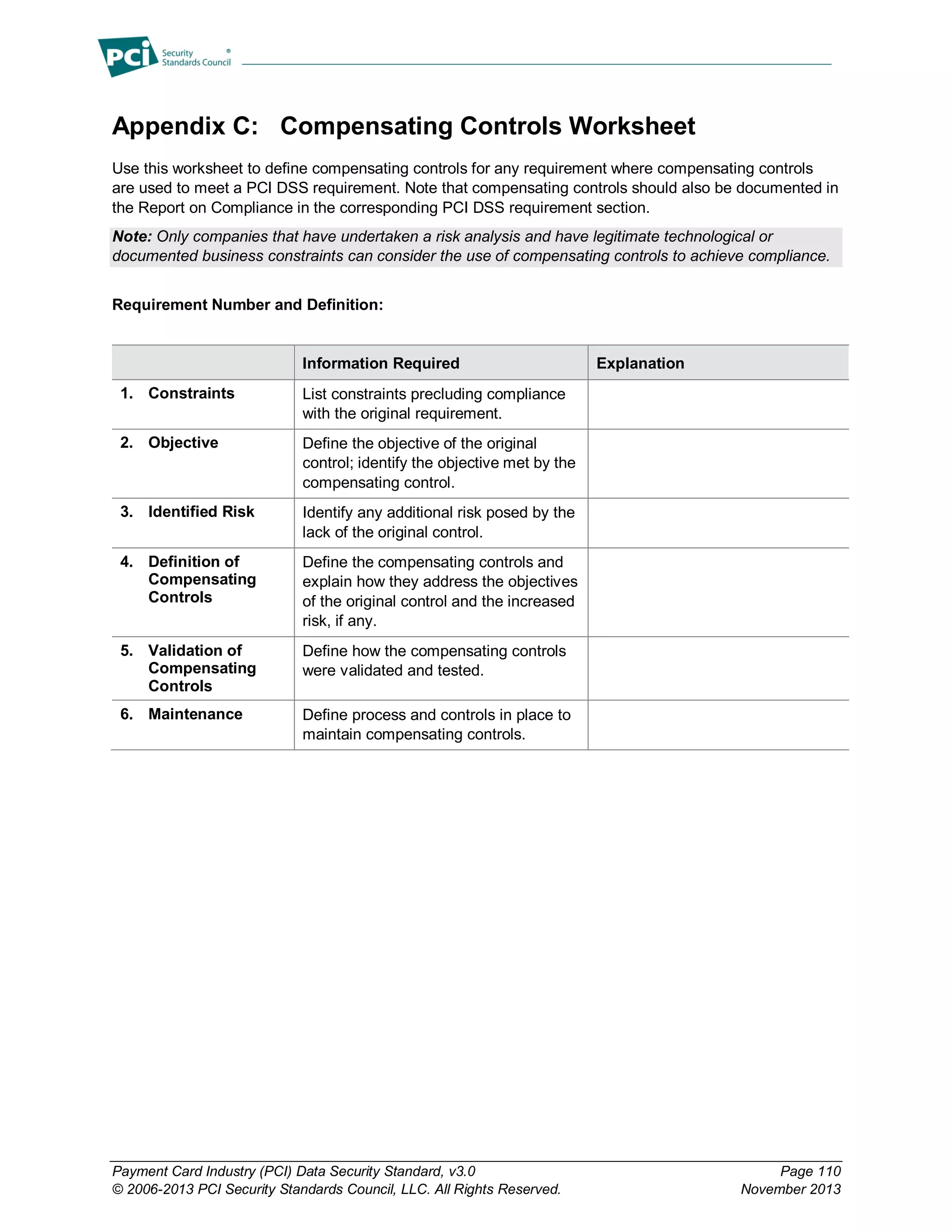
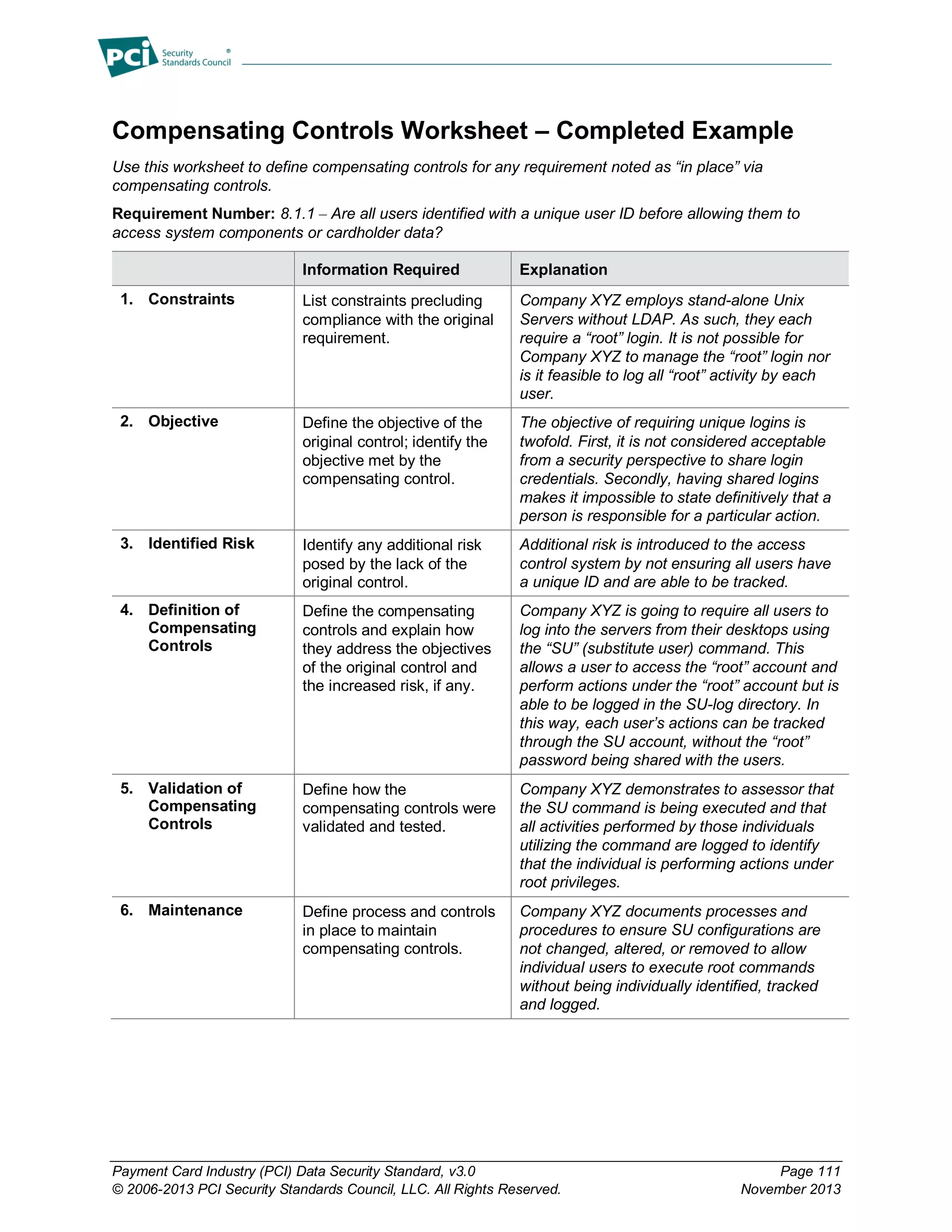
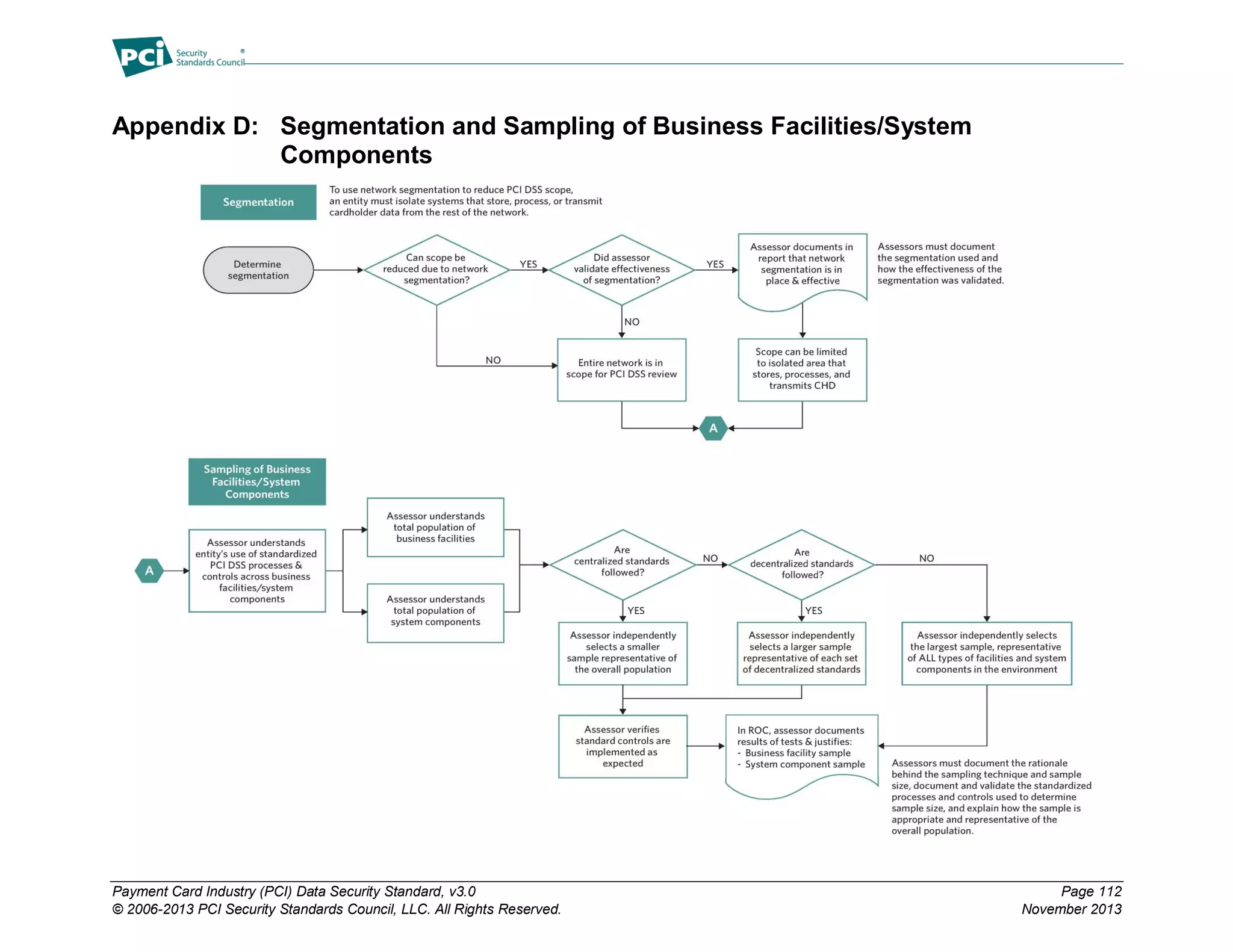
The Payment Card Industry Data Security Standard (PCI DSS) version 3.0 outlines essential security requirements for entities involved in payment card processing to protect cardholder data. It includes twelve high-level security requirements covering network security, data protection, access control, monitoring, and policy maintenance. The document serves as a comprehensive assessment tool for compliance and emphasizes the need for all involved parties to ensure rigorous data protection measures.