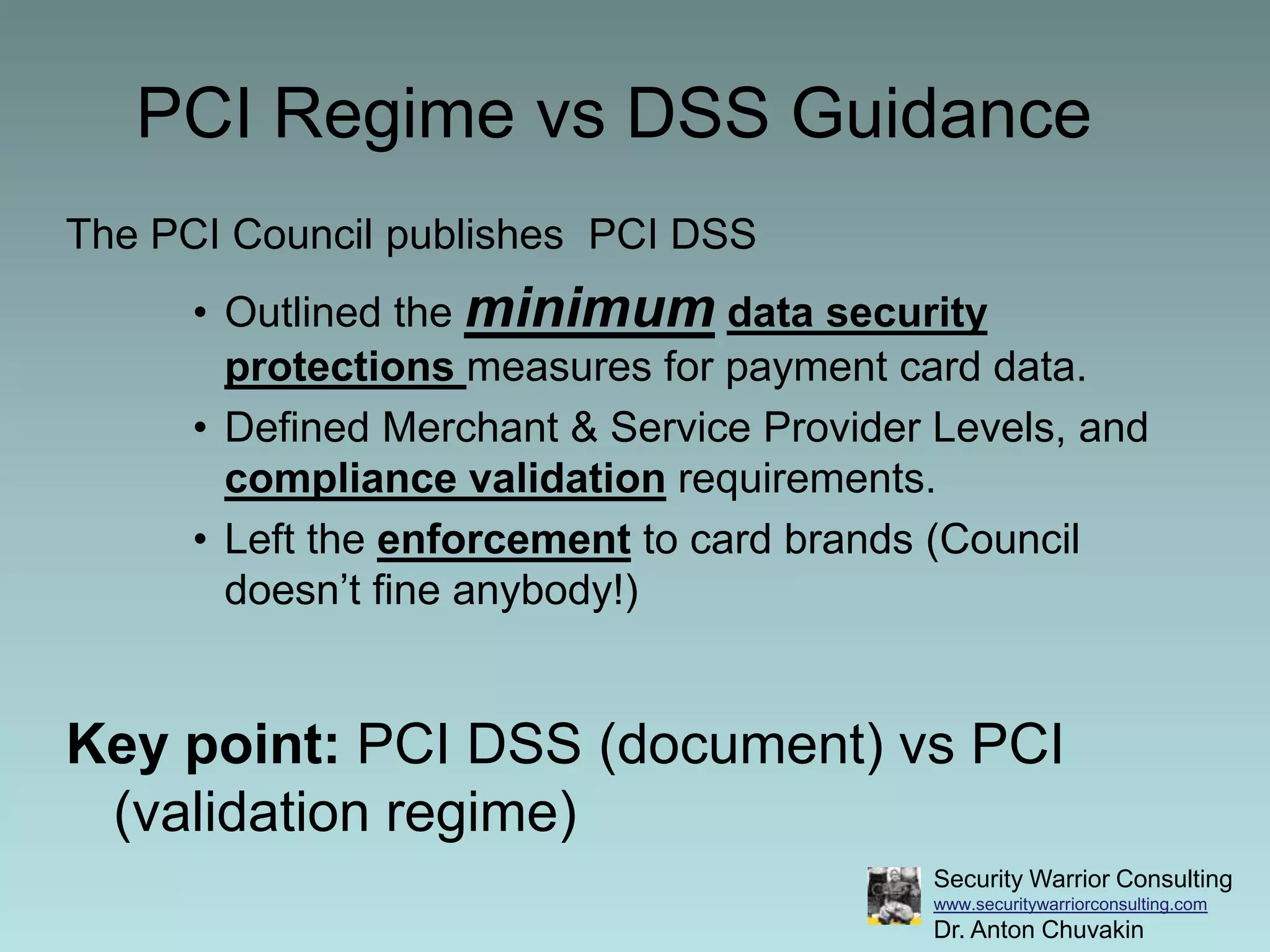
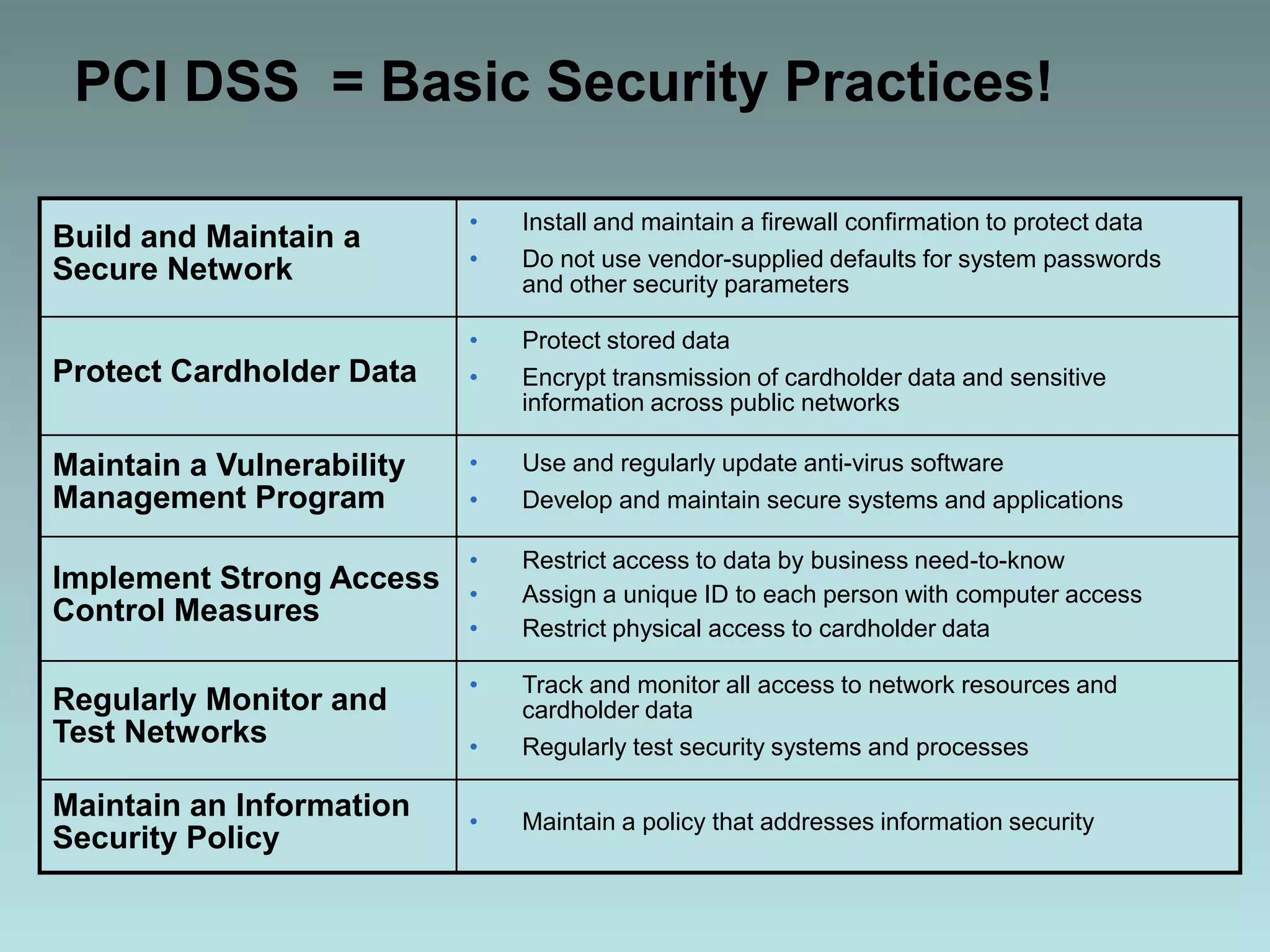
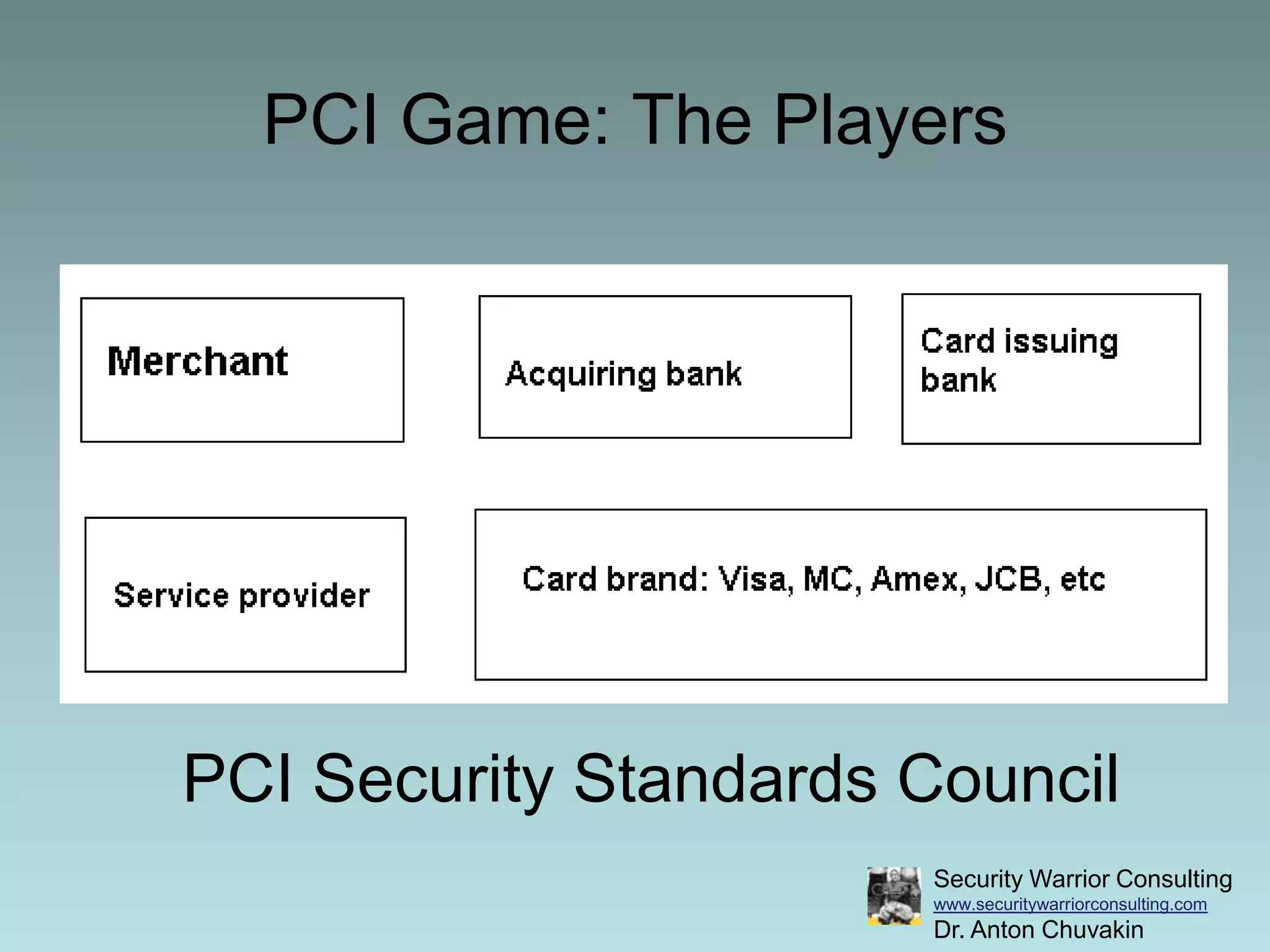
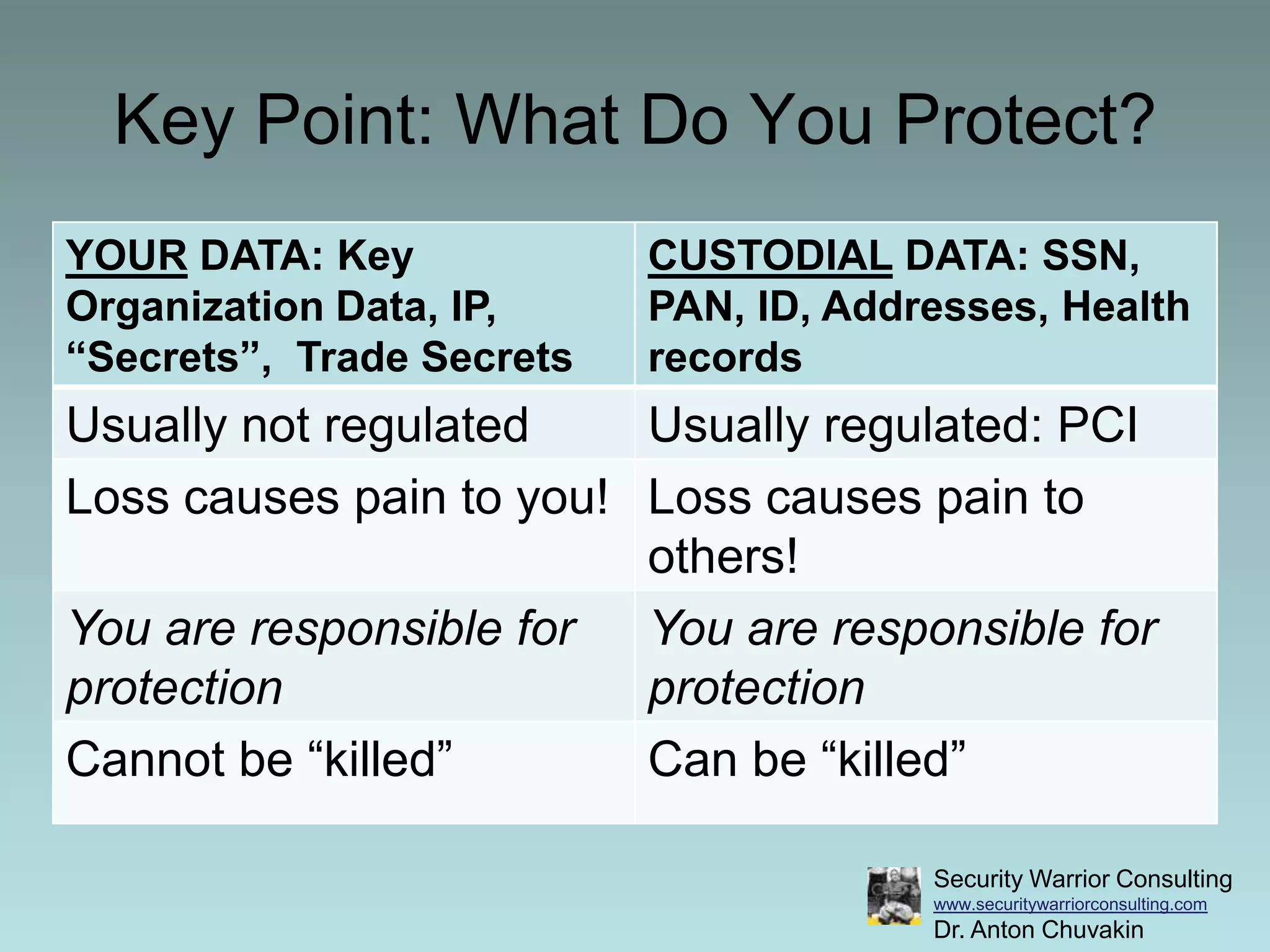
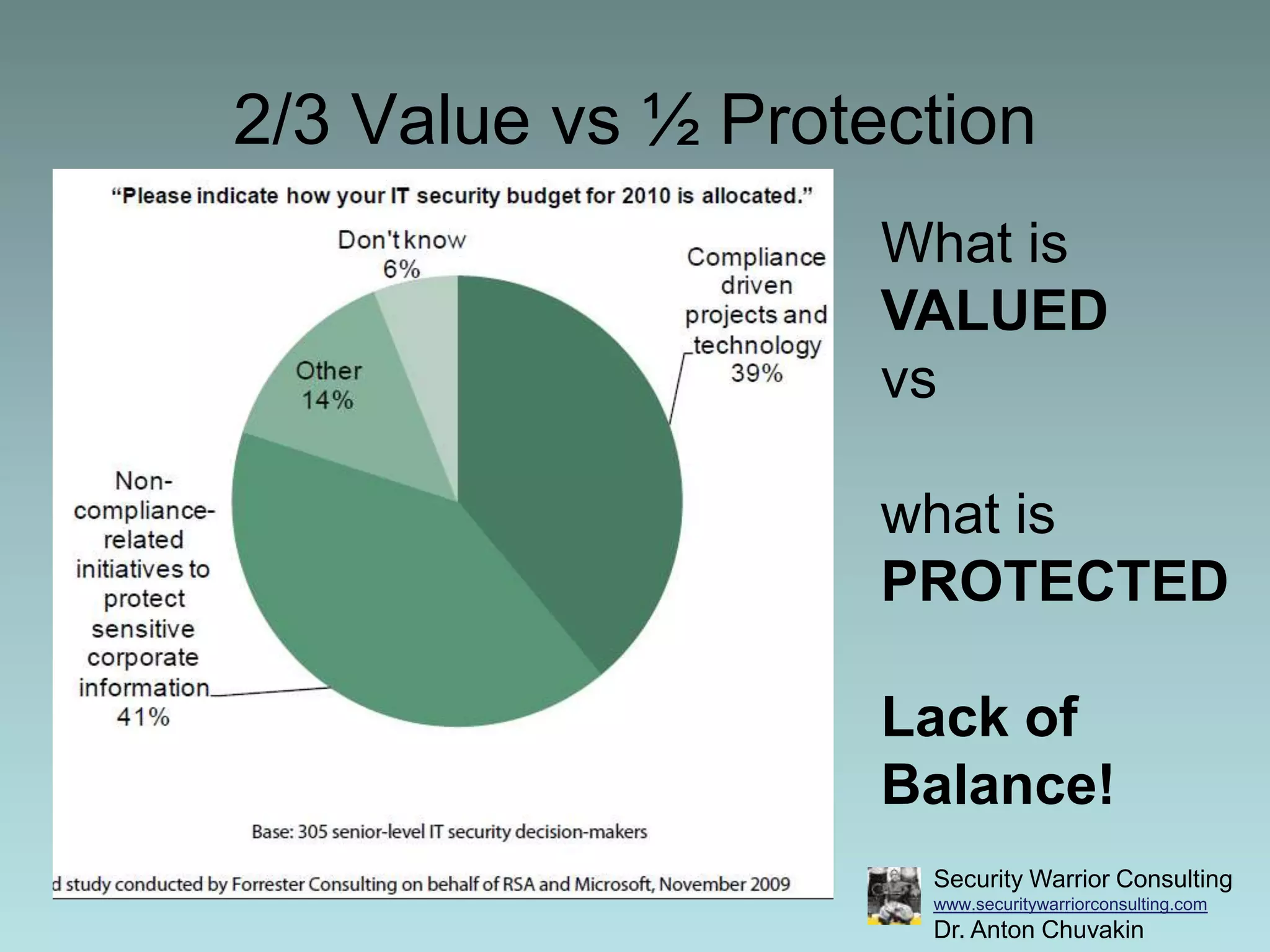
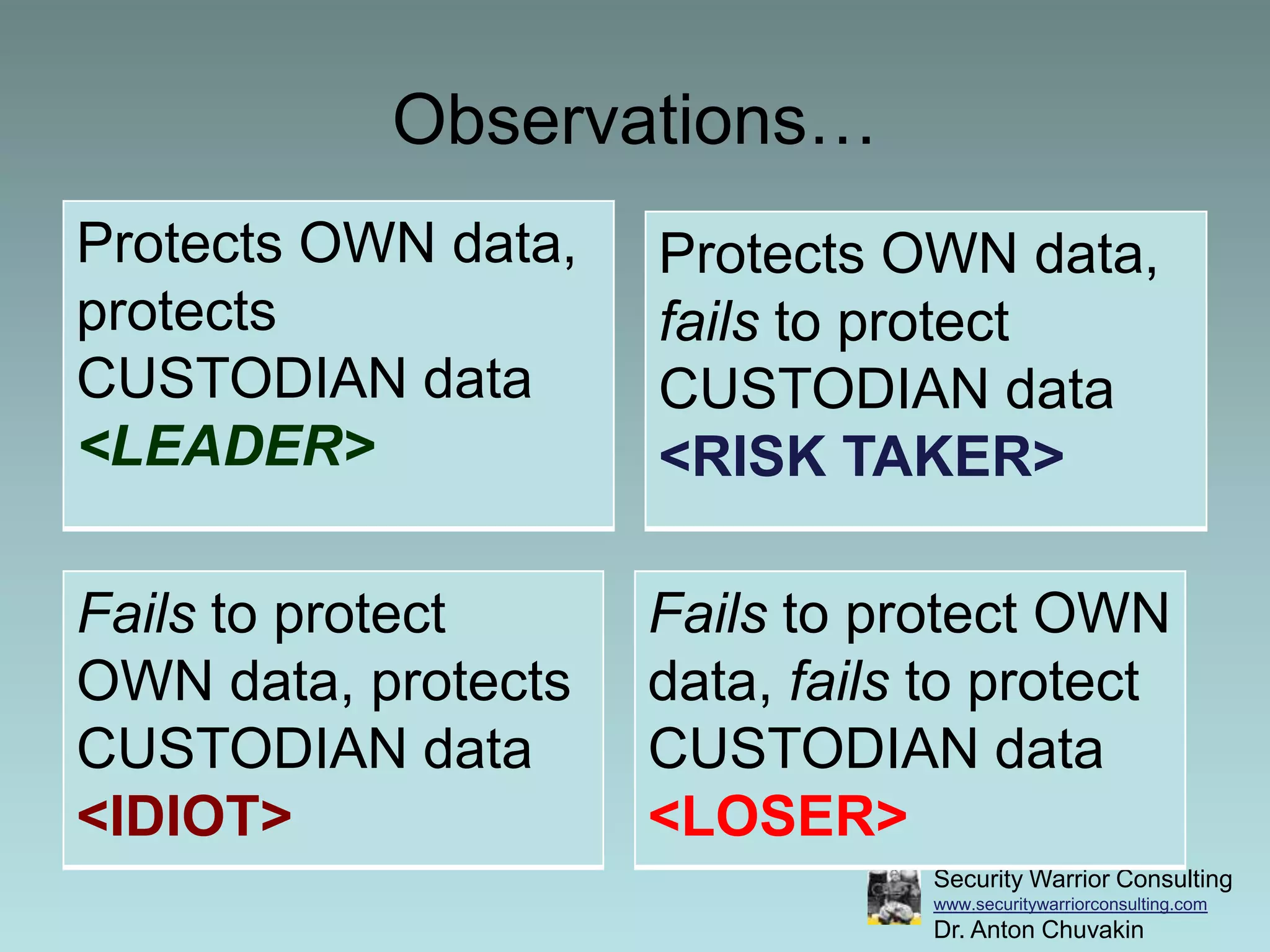
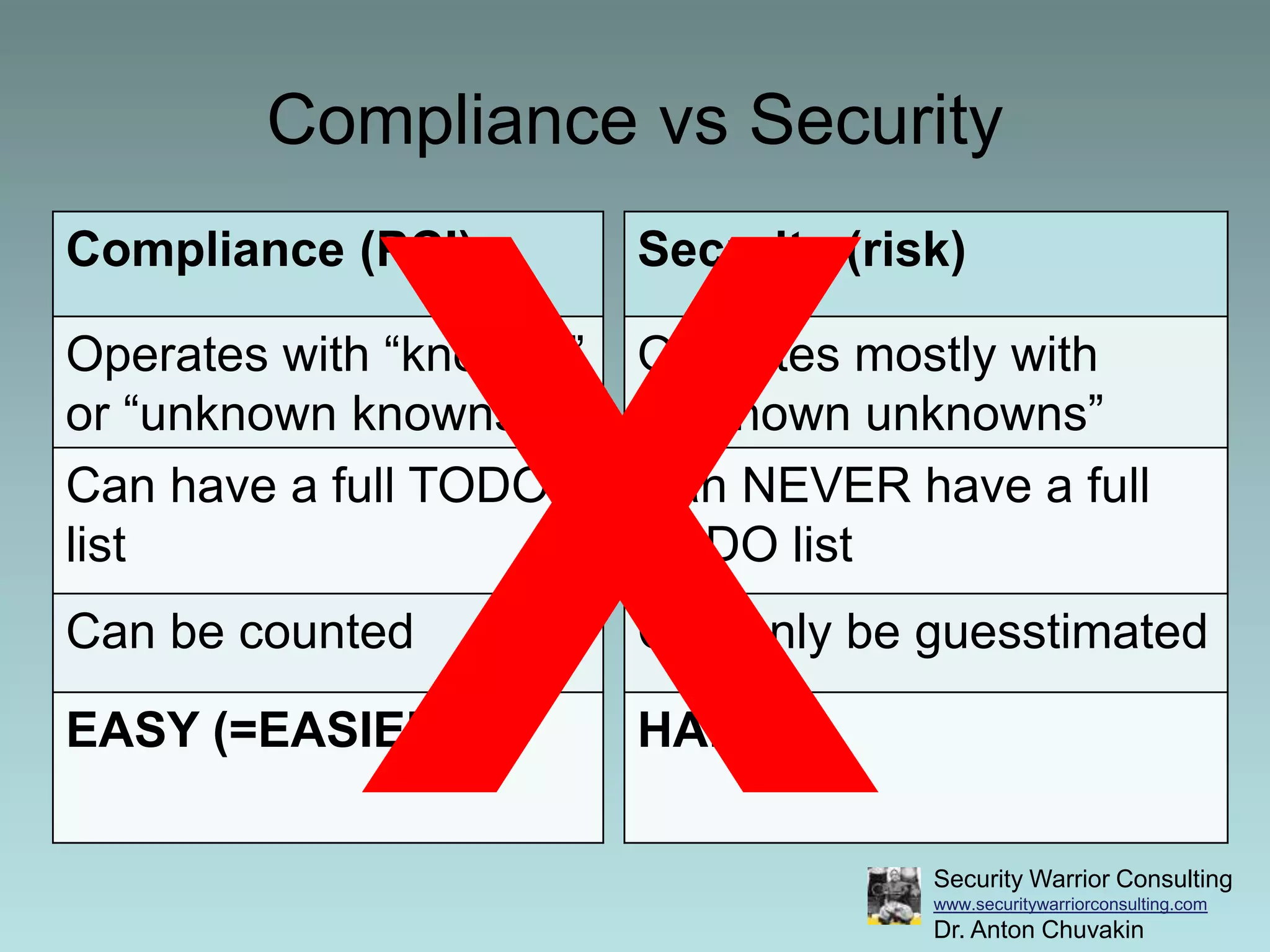
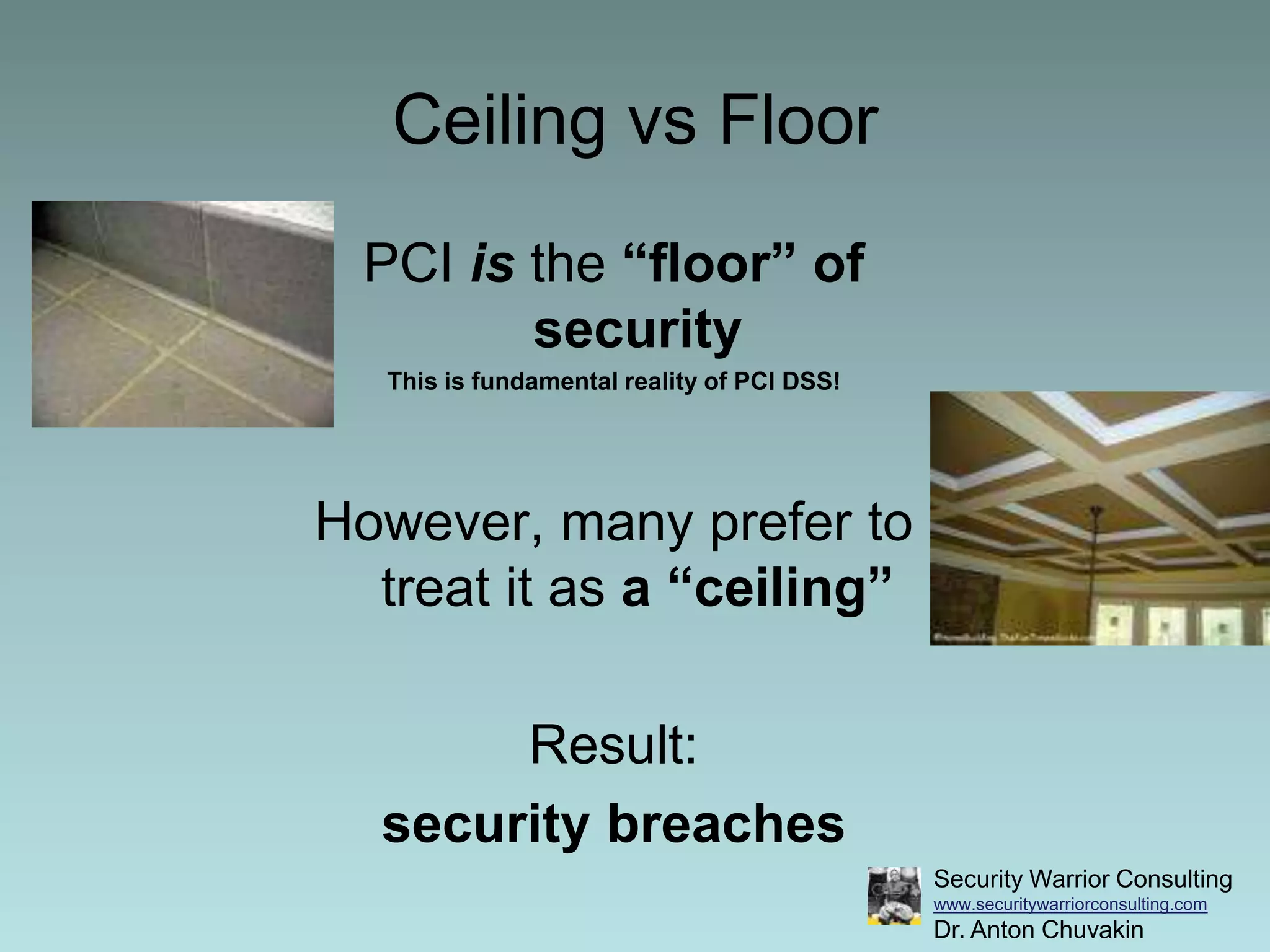
Dr. Anton Chuvakin's keynote at the PCI in Higher Education workshop emphasizes the true purpose of PCI DSS: to reduce security breaches and card fraud rather than merely fulfilling compliance. He critiques the checklist mentality surrounding PCI compliance, urging organizations to prioritize genuine security improvements over mere adherence to standards. The document advocates for a shift in thinking from compliance to a broader security mindset, highlighting that effective PCI practices should lead to actual security benefits.