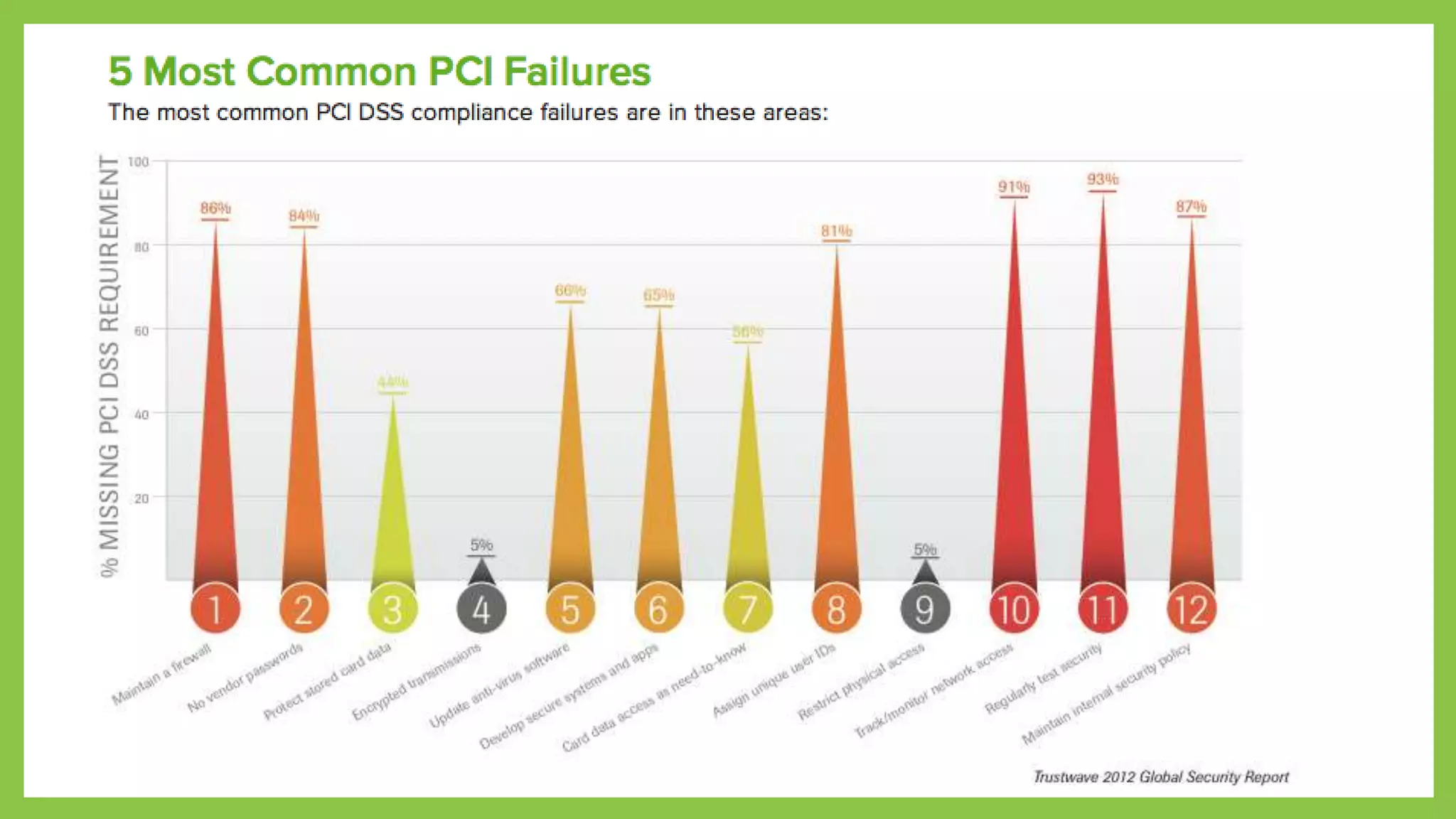
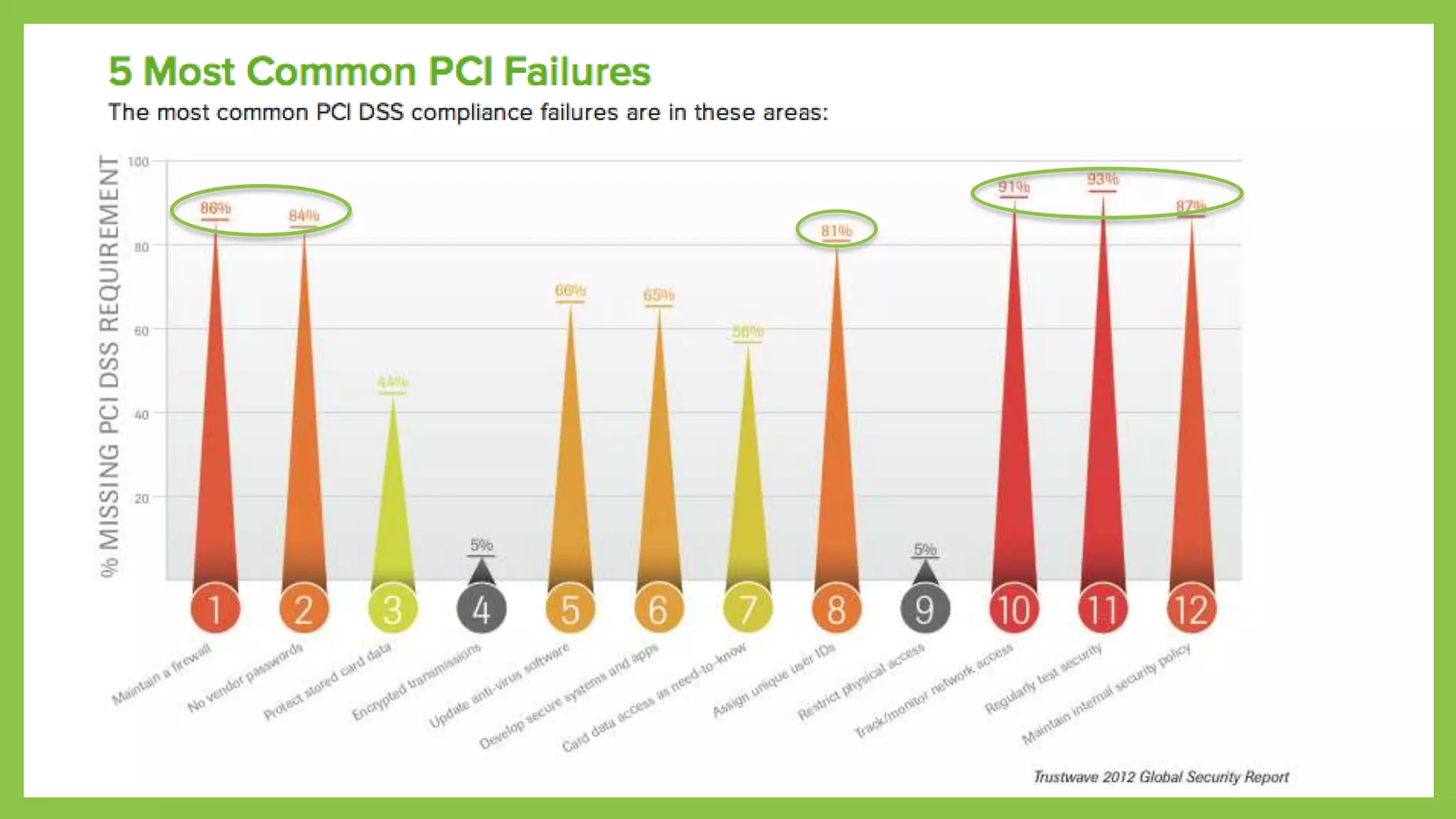
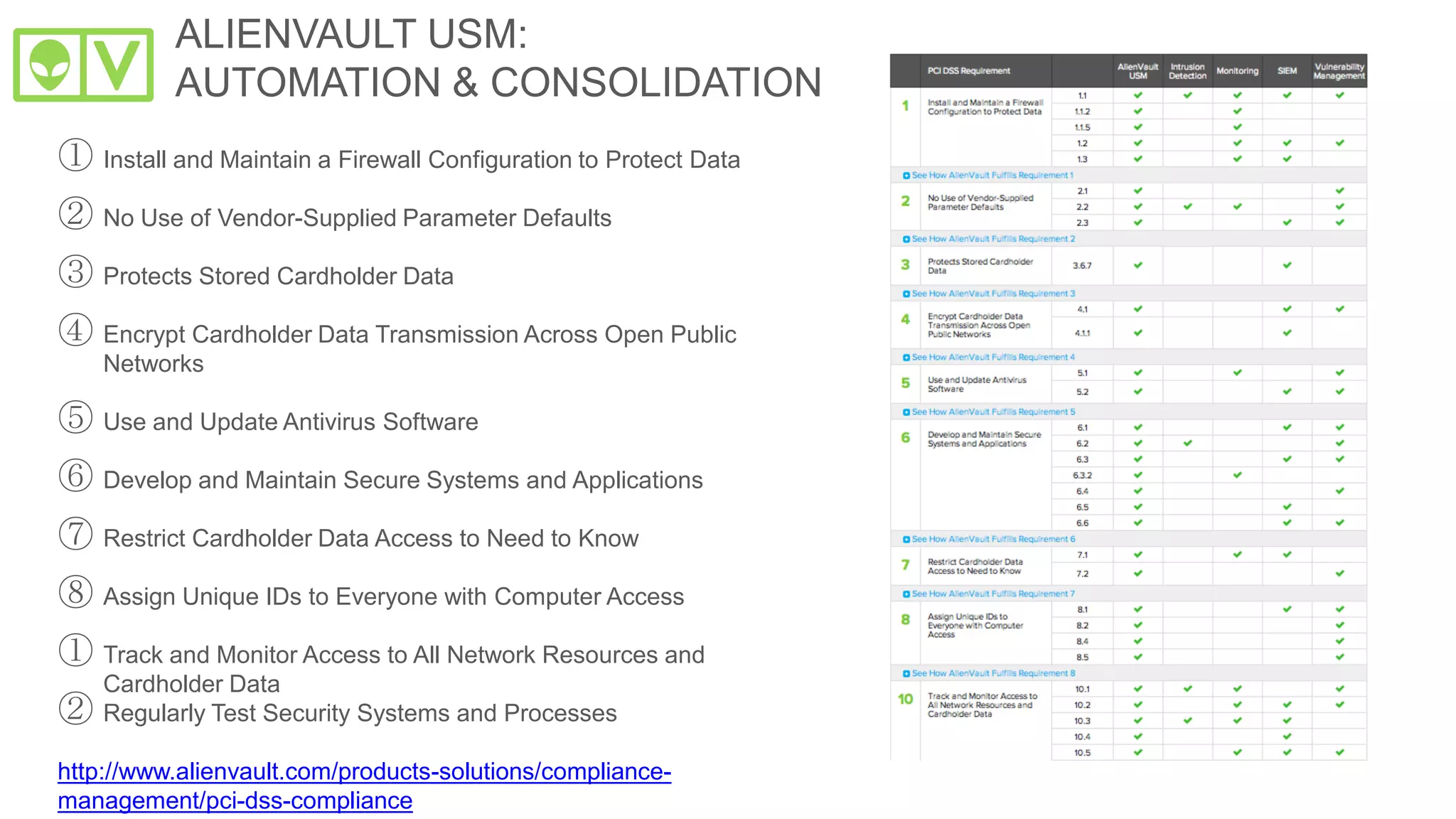
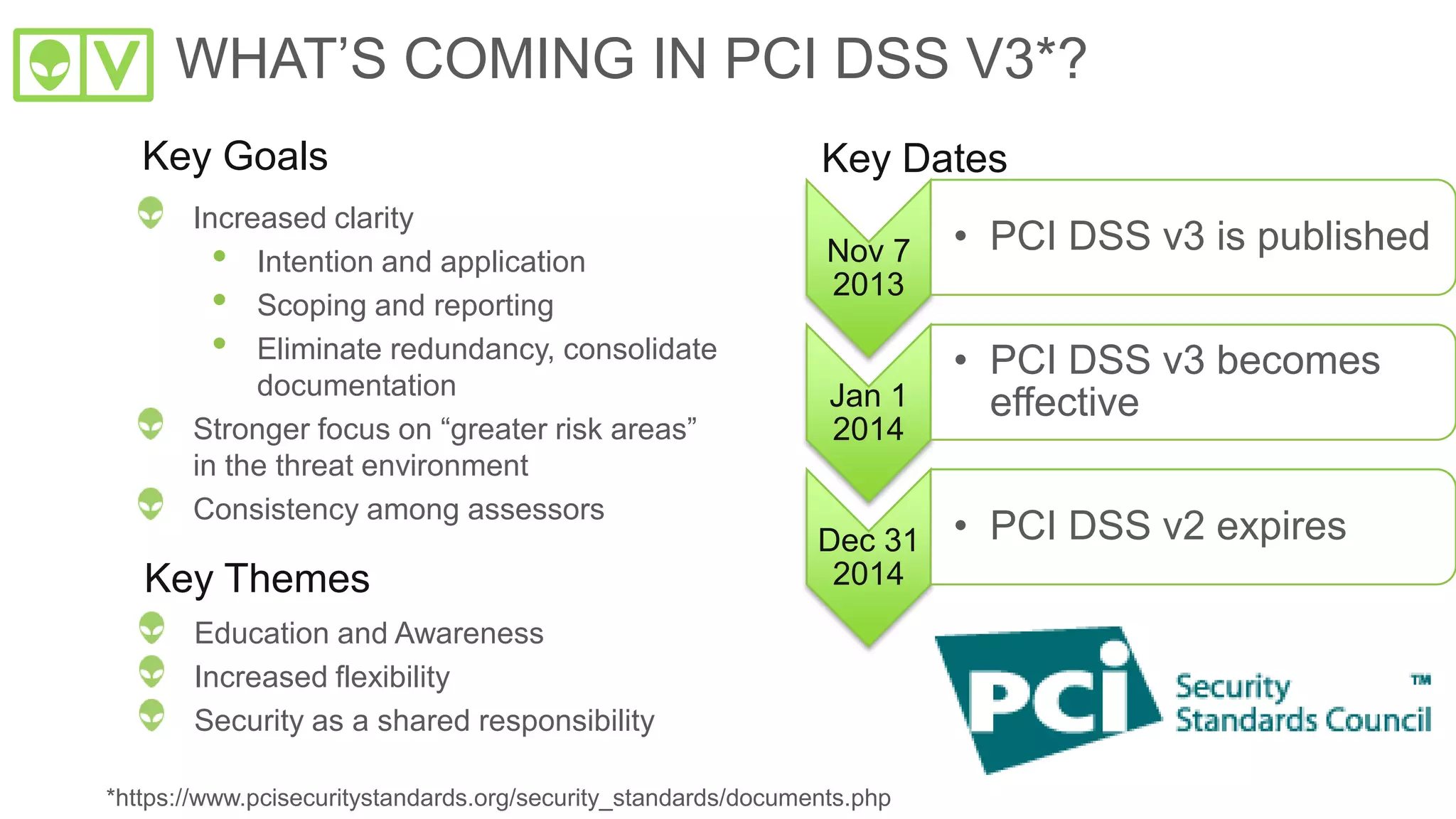
The document outlines key strategies for achieving PCI DSS compliance, emphasizing the importance of asset discovery, vulnerability assessment, and threat detection. It highlights essential practices such as maintaining effective security configurations, employing threat intelligence, and automating compliance processes. Additionally, it introduces AlienVault's Unified Security Management as a comprehensive solution for managing compliance and security needs in a streamlined manner.