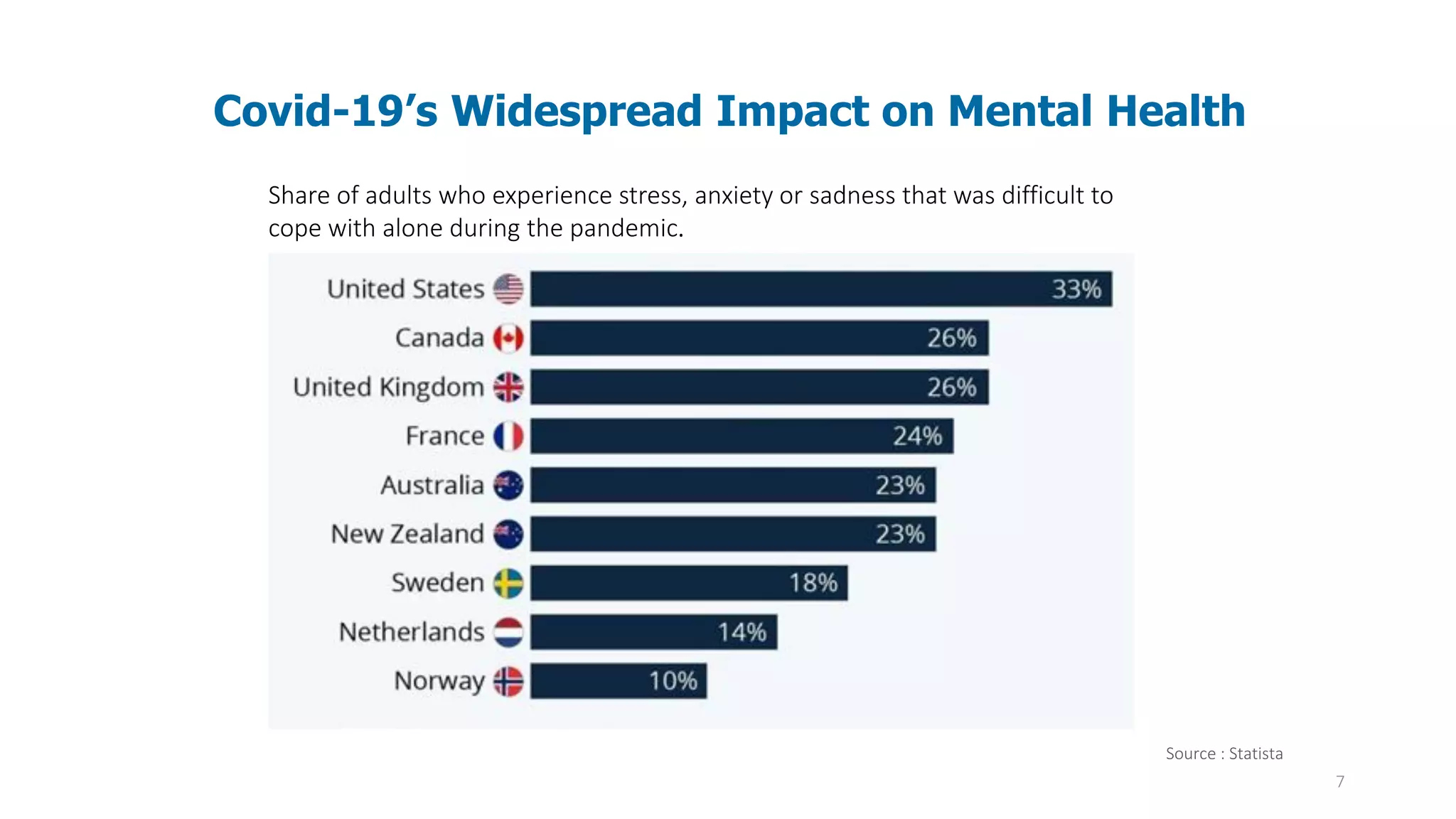
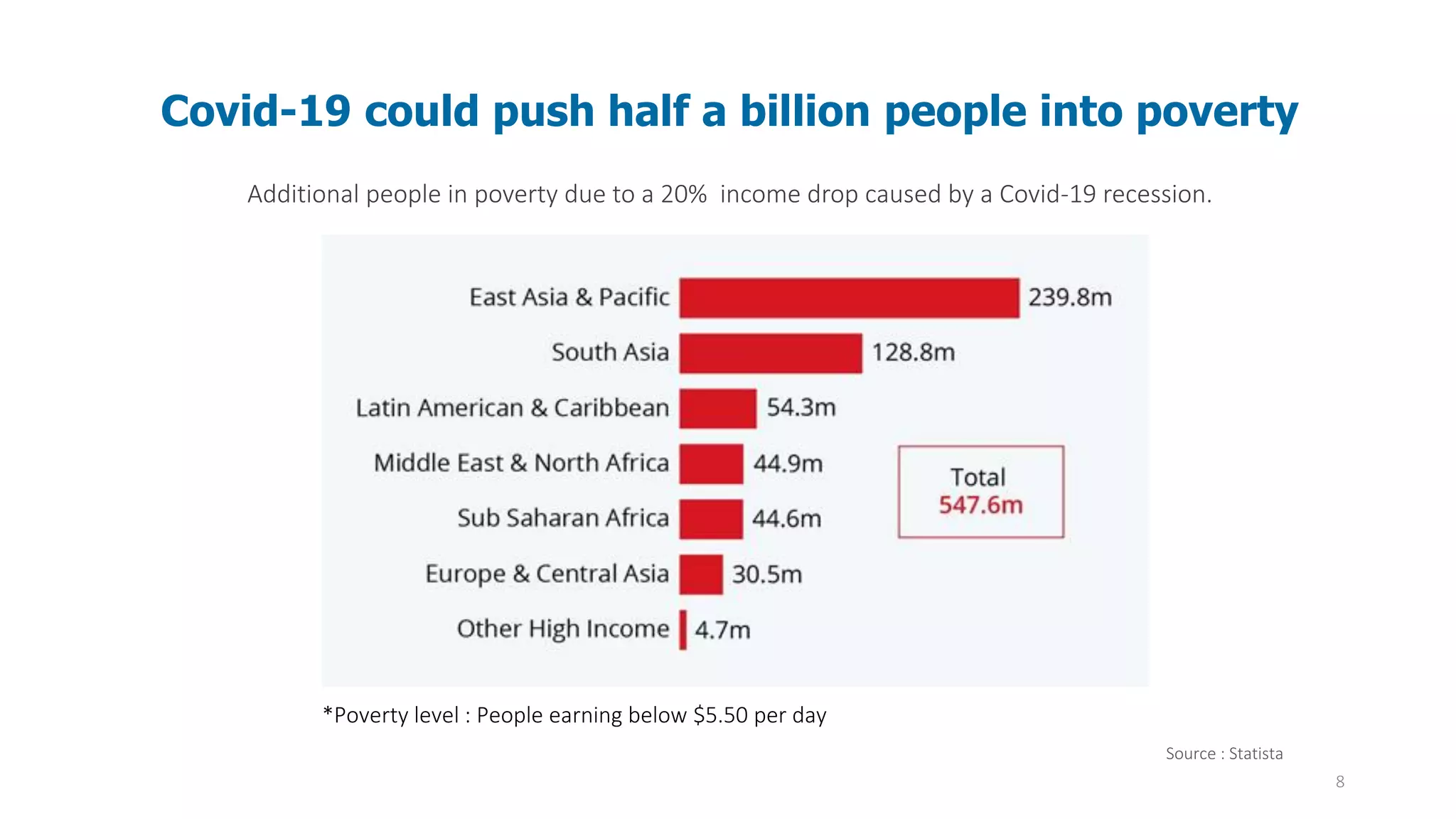
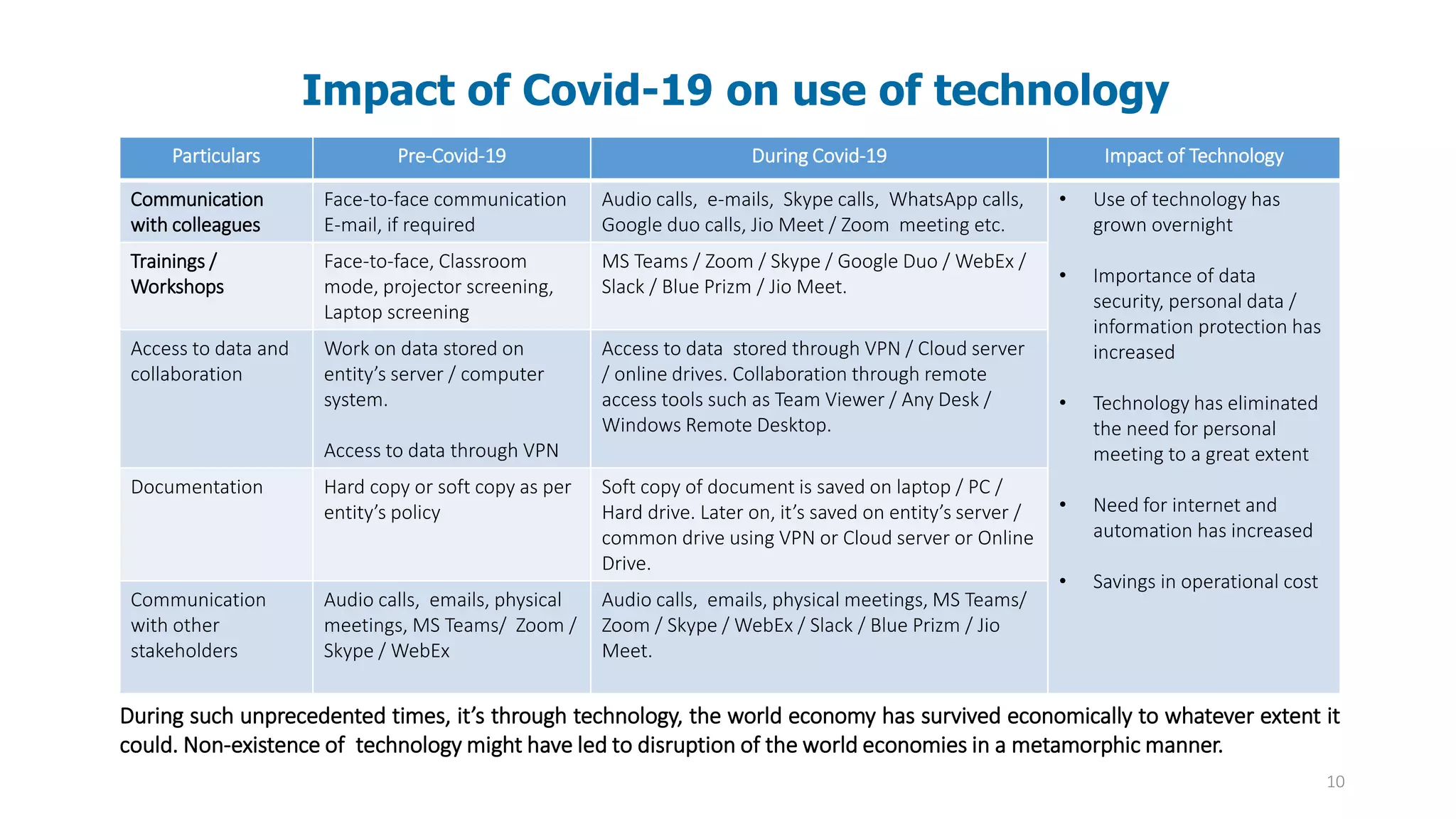
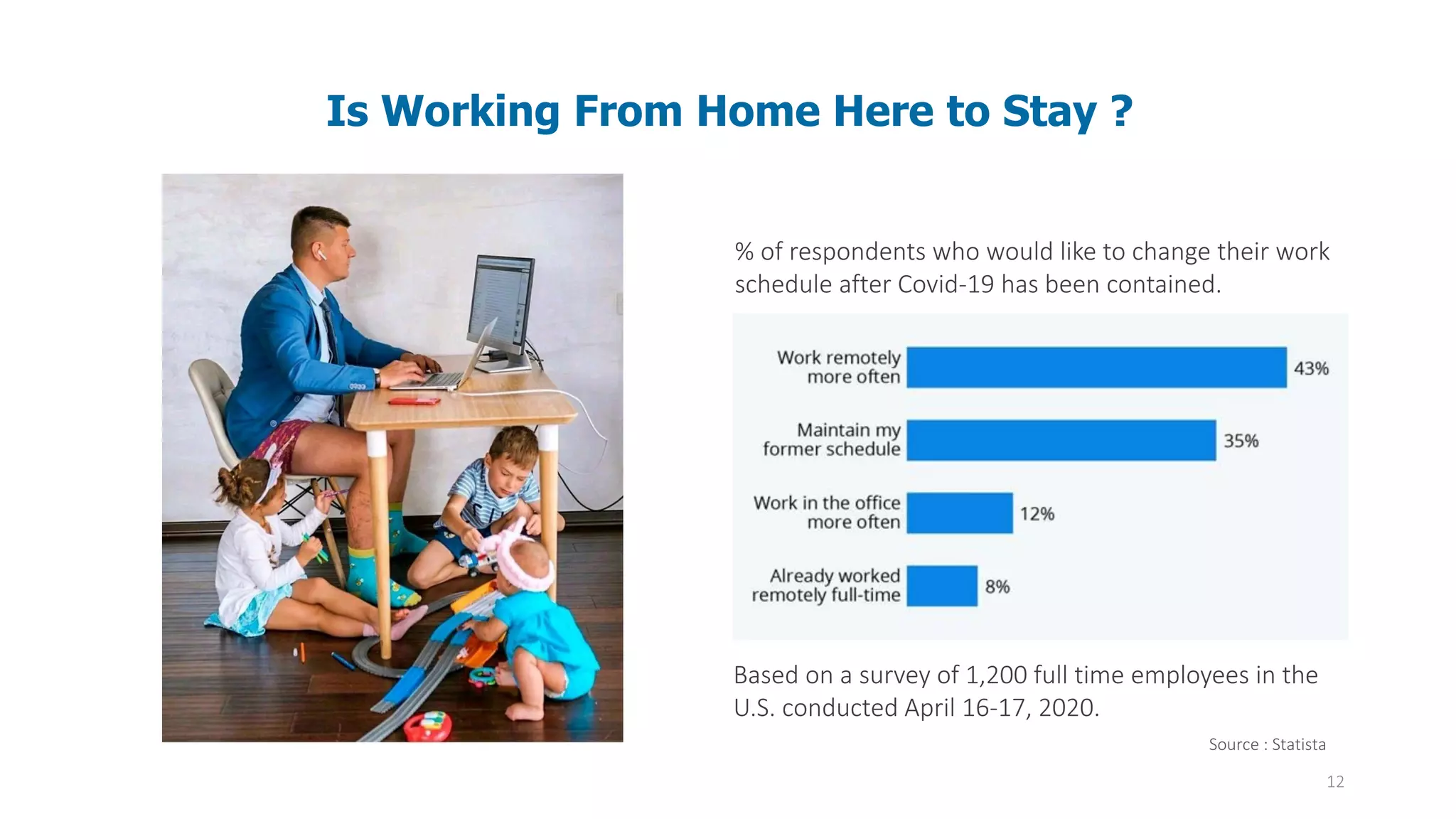
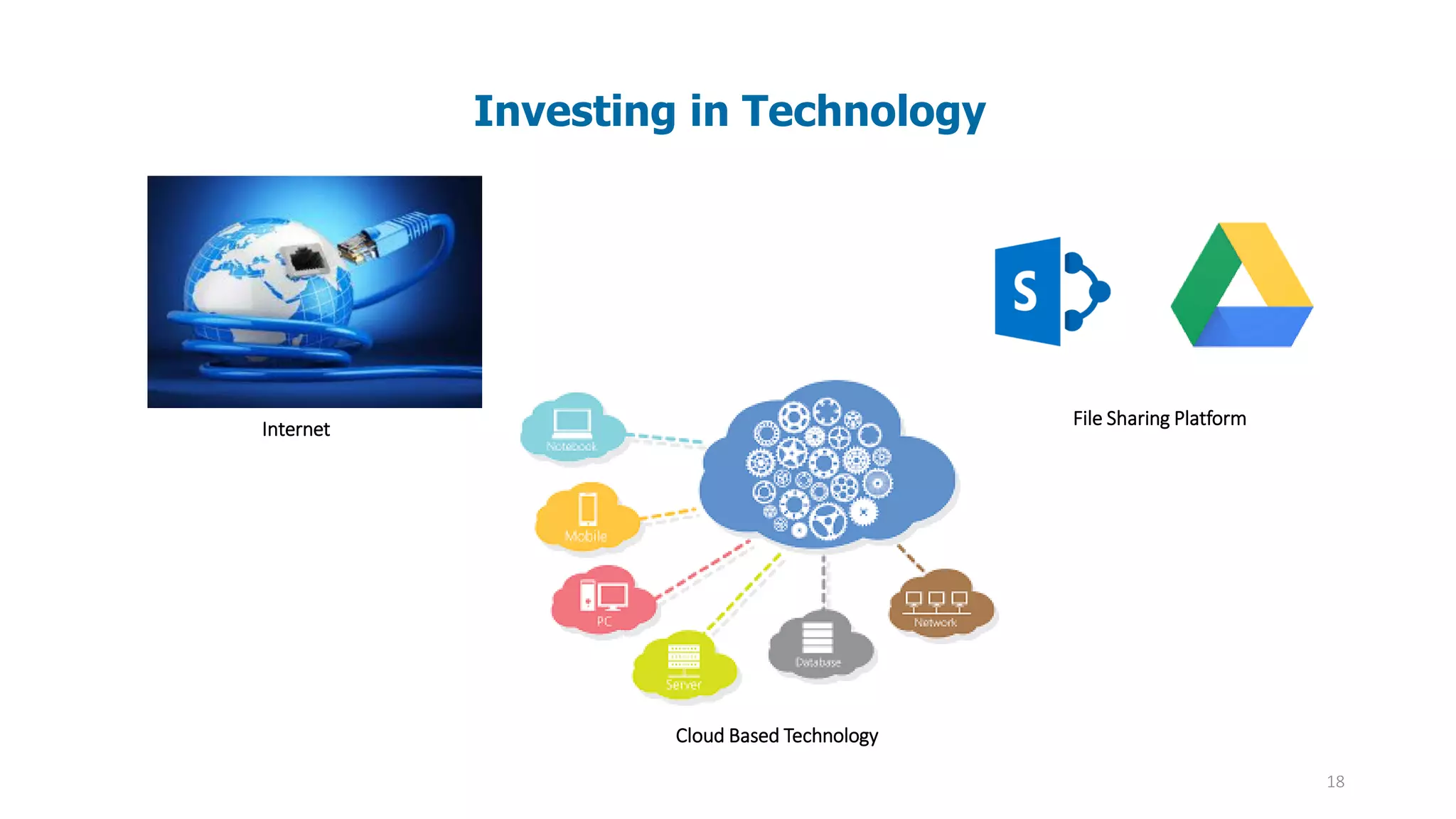
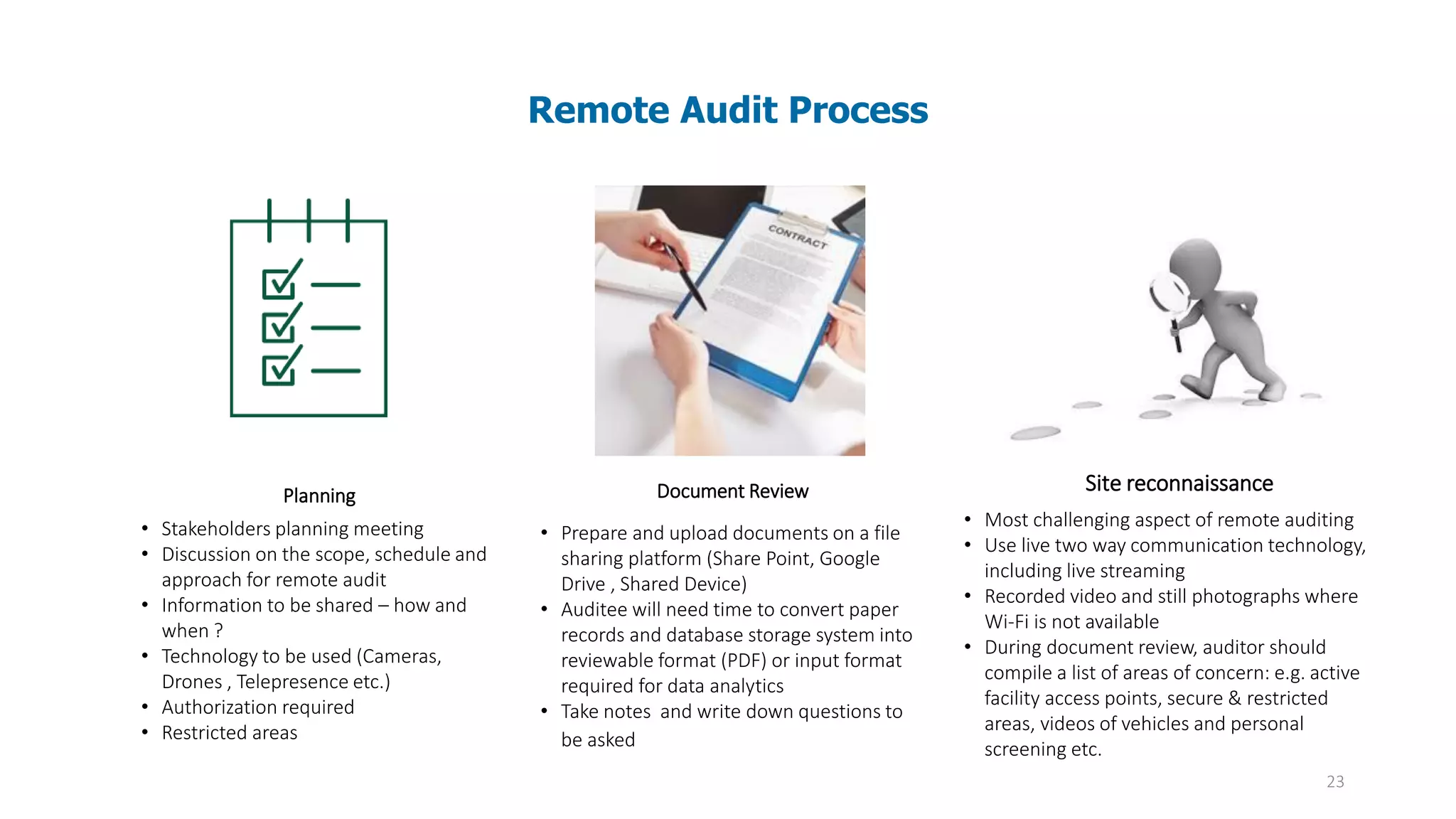
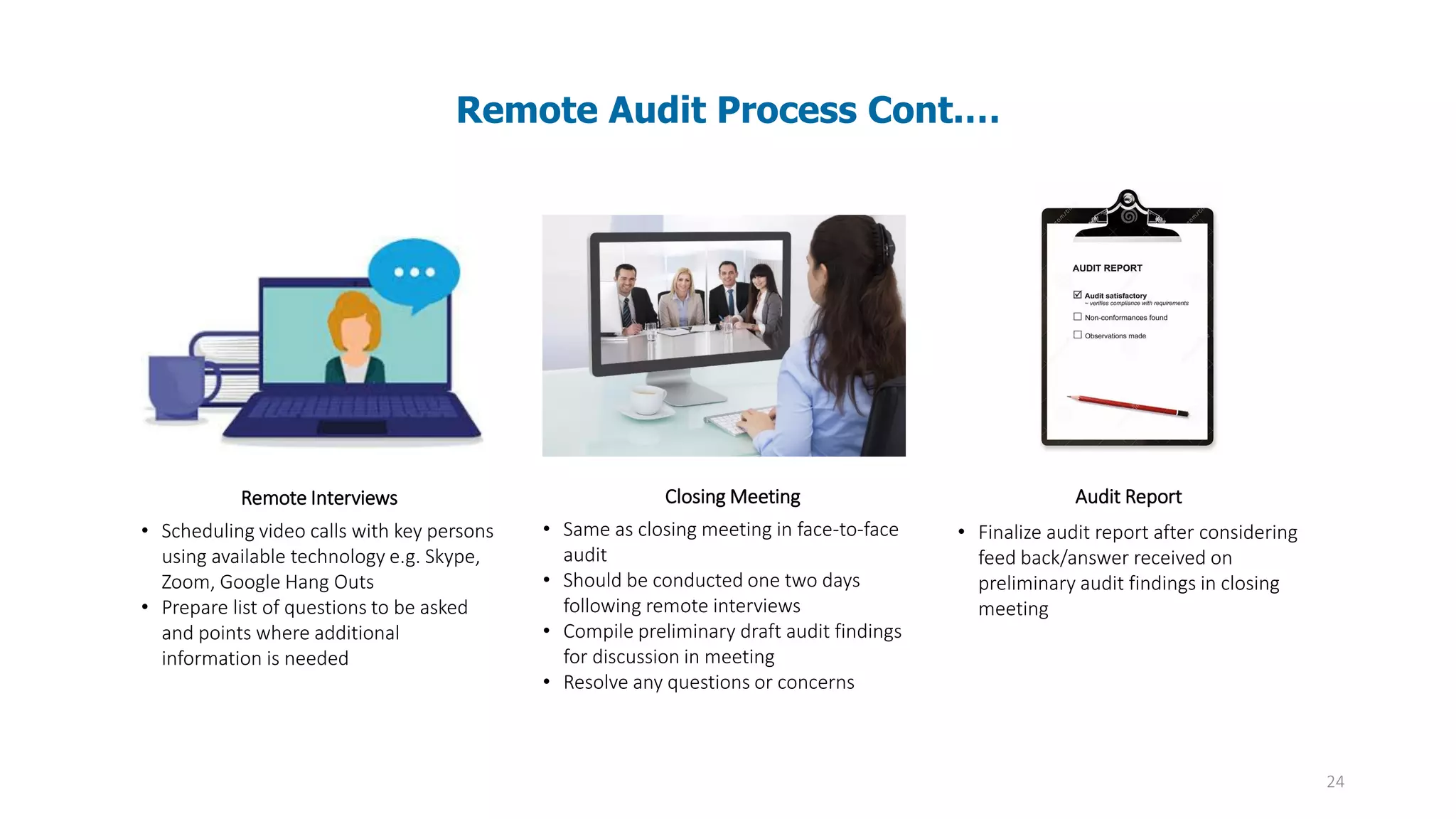
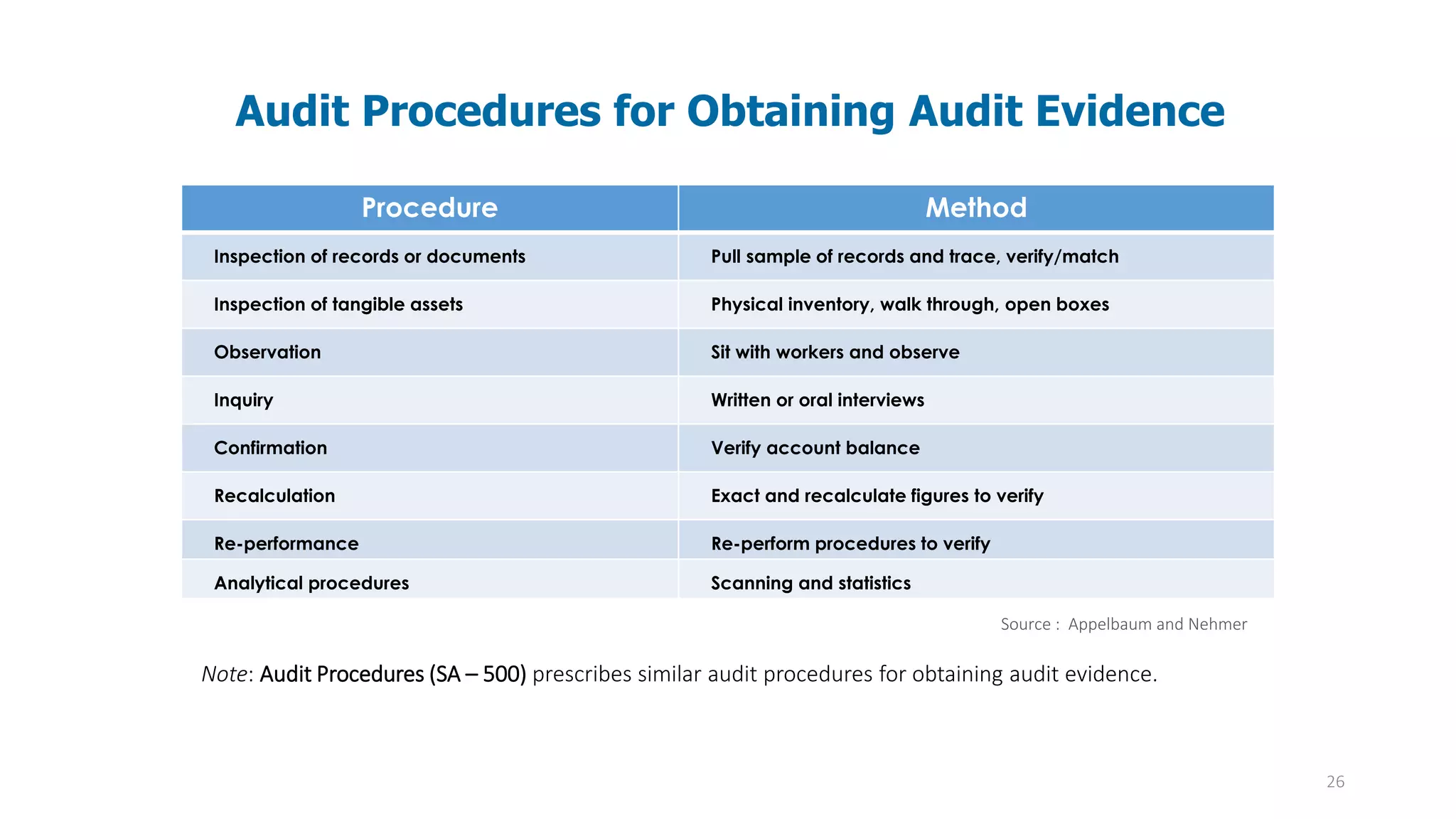
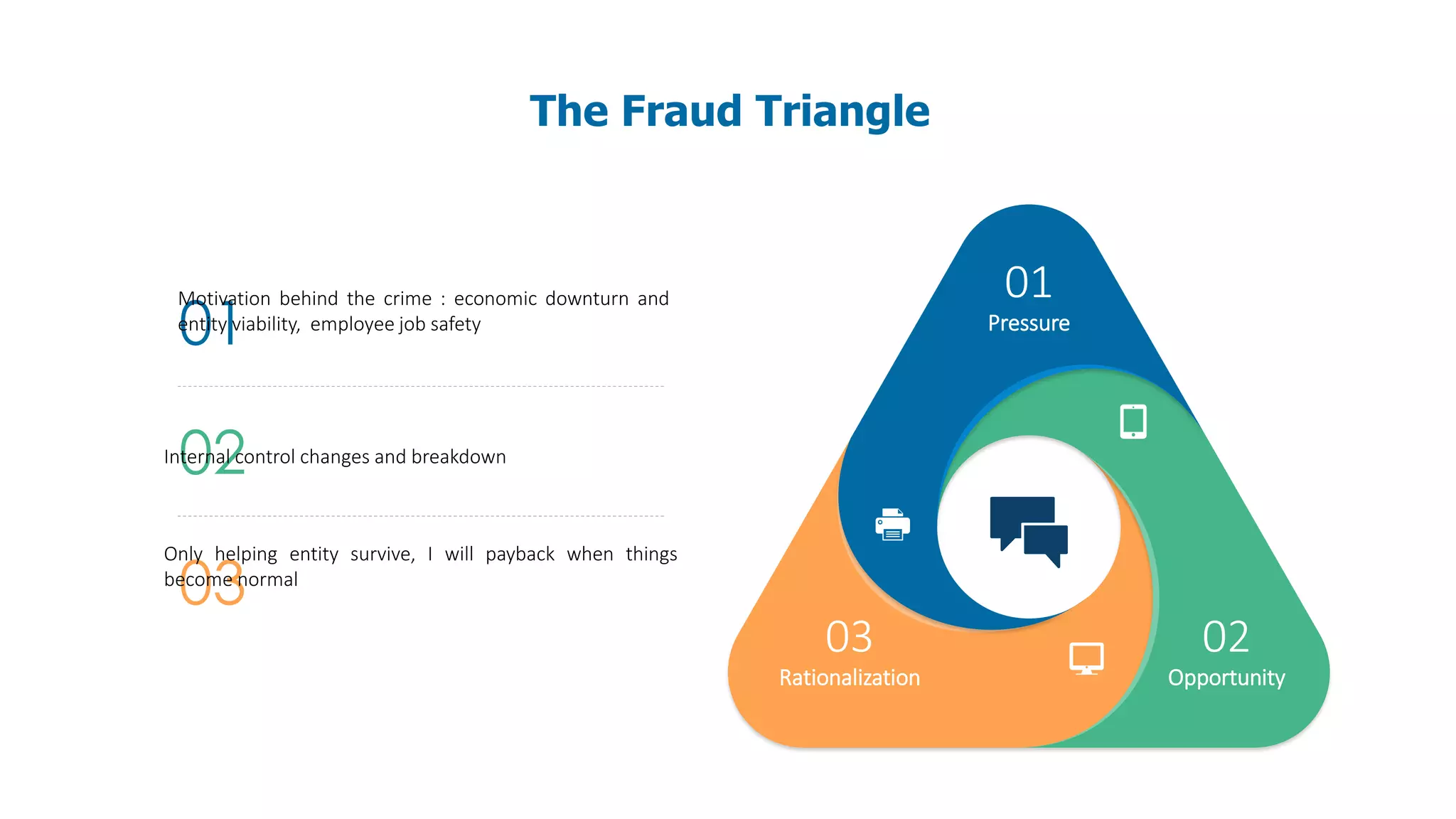
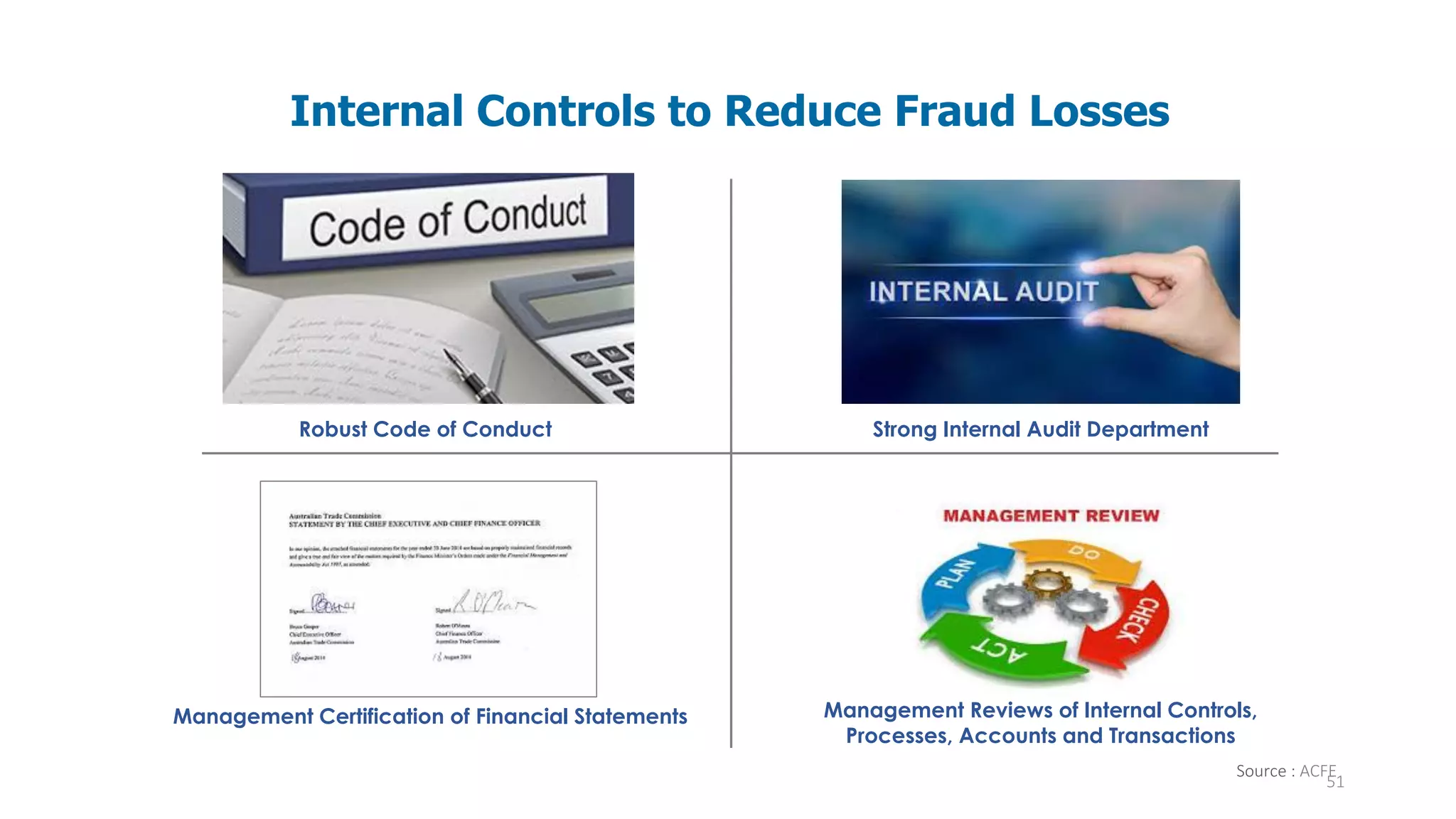
The document discusses the impact of COVID-19 on remote auditing practices, highlighting the shift to electronic audits that eliminate face-to-face interactions and the associated benefits and challenges. It outlines the evolving role of technology, the deficiencies in traditional auditing methods due to remote work, and the evolving expectations for audit committees in managing risk and ensuring accountability during the pandemic. The presentation emphasizes the need for continuous adaptation in auditing techniques and communication strategies to maintain quality and integrity in audits amidst the ongoing crisis.