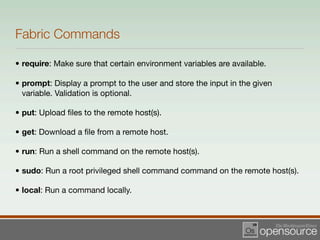
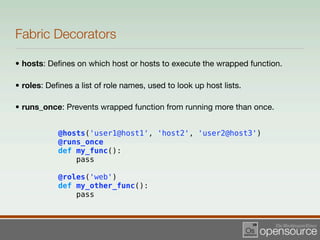
The document discusses the deployment automation tool Fabric version 0.9, emphasizing its use for managing different environments such as testing, staging, and production across multiple computers. It outlines the installation process, task definition, and various Fabric commands, including examples of how to clean and manage files on remote hosts. Additionally, it presents usage scenarios where Fabric can streamline server management and deployment tasks.


![The fabfile.py
from fabric.api import *
env.roledefs = {
'web': ['172.16.12.1', '172.16.12.2',],
'media': ['172.16.12.4',],
'staging': ['172.16.12.5',],
'testing': ['172.16.12.6',],
'database': ['172.16.12.7', '172.16.12.8',],
}
env.root_path = '/var/websites'](https://image.slidesharecdn.com/fabricpresentation-090801075009-phpapp02/85/Pythonic-Deployment-with-Fabric-0-9-6-320.jpg)
![Define Tasks to Setup Environments
def testing():
env.hosts = env.roledefs['testing']
env.user = 'testuser'
def staging():
env.hosts = env.roledefs['staging']
env.user = 'staginguser'
def production():
env.hosts = env.roledefs['web']
env.user = 'produser'](https://image.slidesharecdn.com/fabricpresentation-090801075009-phpapp02/85/Pythonic-Deployment-with-Fabric-0-9-7-320.jpg)
![Task Example
def clean(site=None):
"""Remove .pyc files from a site."""
from os import path
if not site:
site = prompt('Please specify which site(s) to
clean (a comma delimited list is accepted): ',
validate=r'^[w-.,]+$')
site_list = site.split(',')
for item in site_list:
path = path.join(env.root_path, item)
sudo("find %s -name '*.pyc' -depth -exec rm {} ;"
% path)](https://image.slidesharecdn.com/fabricpresentation-090801075009-phpapp02/85/Pythonic-Deployment-with-Fabric-0-9-8-320.jpg)

![Usage Example
$ fab testing clean:site=basenews
[172.16.12.6] sudo: find /var/websites/basenews -name
'*.pyc' -depth -exec rm {} ;
Password for testuser@192.168.56.3:
Done.
Disconnecting from 172.16.12.6... done.
$](https://image.slidesharecdn.com/fabricpresentation-090801075009-phpapp02/85/Pythonic-Deployment-with-Fabric-0-9-12-320.jpg)