Privacy Discusssion GM667 Saint Mary's University of MN
•
0 likes•592 views
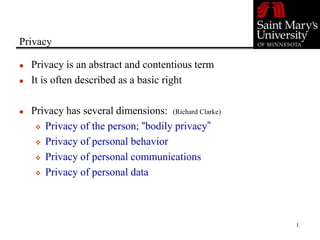
This document discusses privacy and information privacy. It outlines four dimensions of privacy including privacy of the person, personal behavior, personal communications, and personal data. Information privacy is defined as a combination of communications and data privacy that allows individuals control over collection, distribution, use, solicitation, and storage of private information. Many current privacy laws and guidelines are based on eight principles developed by the OECD in 1980 around limiting collection and ensuring security, quality, transparency and individual participation regarding personal data.
Report
Share
Report
Share
Recommended
ICSA Irish Region General Data Protection Regulation event, 10 October 2017

ICSA Irish Region General Data Protection Regulation event, 10 October 2017Institute of Chartered Secretaries and Administrators
Presentation slides from the ICSA Irish Region General Data Protection Regulation event that took place on 10 October 2017. TrustArc Webinar: Challenges & Risks Of Data Graveyards

With the rise of big data, companies now obtain and store many data in massive quantities. As a result, they end up having giant repositories of unused data stored in their servers, also called data graveyards.
Storage infrastructure, maintenance costs, compliance with privacy laws, security gaps, and risk of data corruption: risks due to data graveyards are numerous.
What can organizations do with a large amount of data? How can you uncover the value of data before storing it? How can you manage the maintenance costs of big data?
Join our panel in this webinar as we explore how your company should manage the risks and challenges associated with data graveyards.
This webinar will review:
- What data graveyards are
- How to manage data graveyards risks
- How to define data retention periods and stay compliant
Information Sharing and Protection

Information Sharing and ProtectionOxford Martin Centre, OII, and Computer Science at the University of Oxford
David Bray, 'The Need for Achieving Information Sharing and Information Protection', talk at the OII, 8 April 2011. David works on creating an information sharing environment for the US government. GDPR and WHOIS Compliance - Impact on Indian Stakeholders

GDPR or General Data Protection Regulation is a significant new EU Data Protection Regulation. Approved in April 2016, the GDPR is in effect since May 25th, 2018. Know more about GDPR here: https://serverguy.com/news/general-data-protection-regulation-gdpr-guide/
Québec's Privacy Modernization: Bill 64

Québec introduced a new bill that may bring GDPR, CCPA and Artificial Intelligence regulations into Canada. If passed, it will require businesses to have a designated privacy officer, incorporate "privacy by design" into new information systems projects, and introduce mandatory reporting of "confidentiality incidents".
Ivan Horodyskyy - Сloud and GDPR Legal and Organizational Steps to be Taken

Ivan Horodyskyy - Сloud and GDPR Legal and Organizational Steps to be TakenCloud Security Alliance Lviv Chapter
While 25th of May is coming, more and more myths around and about the GDPR appear. Many of them are considering the cloud as a ‘safe harbor’ from the GDPR requirements. Still, standards of the data protection established by the Regulation will be covering also a personal data which is storaged in the cloud. The legal and organizational steps should be taken in order to ensure compliance of cloud services with the GDPR will be considered.The Impact of Cloud: Cloud Computing Security and Privacy

Presentation to HKQAA: The Impact of Cloud: Cloud Computing Security and Privacy (2013.10.29)
Recommended
ICSA Irish Region General Data Protection Regulation event, 10 October 2017

ICSA Irish Region General Data Protection Regulation event, 10 October 2017Institute of Chartered Secretaries and Administrators
Presentation slides from the ICSA Irish Region General Data Protection Regulation event that took place on 10 October 2017. TrustArc Webinar: Challenges & Risks Of Data Graveyards

With the rise of big data, companies now obtain and store many data in massive quantities. As a result, they end up having giant repositories of unused data stored in their servers, also called data graveyards.
Storage infrastructure, maintenance costs, compliance with privacy laws, security gaps, and risk of data corruption: risks due to data graveyards are numerous.
What can organizations do with a large amount of data? How can you uncover the value of data before storing it? How can you manage the maintenance costs of big data?
Join our panel in this webinar as we explore how your company should manage the risks and challenges associated with data graveyards.
This webinar will review:
- What data graveyards are
- How to manage data graveyards risks
- How to define data retention periods and stay compliant
Information Sharing and Protection

Information Sharing and ProtectionOxford Martin Centre, OII, and Computer Science at the University of Oxford
David Bray, 'The Need for Achieving Information Sharing and Information Protection', talk at the OII, 8 April 2011. David works on creating an information sharing environment for the US government. GDPR and WHOIS Compliance - Impact on Indian Stakeholders

GDPR or General Data Protection Regulation is a significant new EU Data Protection Regulation. Approved in April 2016, the GDPR is in effect since May 25th, 2018. Know more about GDPR here: https://serverguy.com/news/general-data-protection-regulation-gdpr-guide/
Québec's Privacy Modernization: Bill 64

Québec introduced a new bill that may bring GDPR, CCPA and Artificial Intelligence regulations into Canada. If passed, it will require businesses to have a designated privacy officer, incorporate "privacy by design" into new information systems projects, and introduce mandatory reporting of "confidentiality incidents".
Ivan Horodyskyy - Сloud and GDPR Legal and Organizational Steps to be Taken

Ivan Horodyskyy - Сloud and GDPR Legal and Organizational Steps to be TakenCloud Security Alliance Lviv Chapter
While 25th of May is coming, more and more myths around and about the GDPR appear. Many of them are considering the cloud as a ‘safe harbor’ from the GDPR requirements. Still, standards of the data protection established by the Regulation will be covering also a personal data which is storaged in the cloud. The legal and organizational steps should be taken in order to ensure compliance of cloud services with the GDPR will be considered.The Impact of Cloud: Cloud Computing Security and Privacy

Presentation to HKQAA: The Impact of Cloud: Cloud Computing Security and Privacy (2013.10.29)
Revision of Legal issues for Unit 11.pptx

Revision guide for BTEC Unit 11 Cyber Security & Incident Management
Securing your Data, Reporting Recommended Practices

This session discusses points such as data classification, user education and highlights that there are many threats looking to obtain your data.
The GDPR Armageddon – One year on

The General Data Protection Regulation came into force on May 25th 2018 and some high profile penalties have already been passed down by the ICO for infringement. One year on, what impact is it having? Insight Data reveals the mistakes some companies are still making and how they can adapt their data processes to avoid fines of up to £20 million.
Lasa European NFP Technology Conference 2010 - Data protection and the cloud

Lasa European NFP Technology Conference 2010 - Paul Ticher's presentation on data protection and cloud computing
Preparing Research Data for Sharing

A description of the issues that need to be considered when considering sharing of research data
Privacy in Bigdata Era

The talk discusses how analytics can attack privacy and what we can do about it. It discusses the legal responses (e.g. GDPR) as well technical responses ( differential privacy and homomorphic encryption).
The video is in https://www.facebook.com/eduscopelive/videos/314847475765297/ from 1.18.
Data Privacy, Ethics and Protection. A Guidance Note on Big Data for Achievem...

This document was developed by UN Global Pulse for the United Nations Development Group. It sets out general guidance on data privacy, data protection and data ethics for the UNDG concerning the use of big data, collected in real time by private sector entities as part of their business offerings, and shared with UNDG
members for the purposes of strengthening operational
implementation of their programmes to support the
achievement of the 2030 Agenda.
Basic principles to information privacy in data mining & data warehouse

Basic Principles to
Protect Information Privacy in
Data Mining & Data Warehousing
GDPR Data Lifecycle

Global data protection regulation lifecycle of data or information on how to process data.
Personal privacy and computer technologies

these slides are about personal privacy and computer technology
GDPR Data Life Cycle

Global data protection regulation lifecycle of data or information on how to process data. Data protection, Data controller, or data processor
The Privacy Law Landscape: Issues for the research community

Presentation by Anna Johnston of Salinger Privacy to ARDC's 'GDPR and NDB scheme: Intersection with the Australian research sector' webinar on 13 September 2018
Why We Require GDPR?

About GDPR, Why we require, Penality, Principles, Cookies Management, Privacy by design, privacy notice, the web developer role
Developing a privacy compliance program

How to go about putting into pace a privacy compliance program to comply with GDPR or CCPA or similar legislation
Secure channels inc. basic rules for data protection compliance

There are general rules that cover data protection compliance. One is consent, where one should obtain consent before acquiring, holding, or using personal data wherever possible. It is also necessary to be careful with sensitive personal data, such as those pertaining to race, political opinion, health status, religious belief, sexuality, and criminal offense. https://securechannelsinc.blogspot.com/2017/09/basic-rules-for-data-protection.html
What is CJIS Compliance?

CJI applies to every individual including private entities, contractors, and members of a criminal justice entity or non-criminal justice agency representatives with access to, or who operate in support of, criminal justice services and information.
Adjusting to the GDPR: The Impact on Data Scientists and Behavioral Researchers

Our presentation introduces the GDPR then gives a brief overview of key GDPR principles and explains how they are likely to affect data scientists and behavioral researchers.
Information Security Discussion for GM667 Saint Mary's University of MN

Information Security Discussion for GM667 Saint Mary's University of MNSaint Mary's University of Minnesota
Information security basics
More Related Content
What's hot
Revision of Legal issues for Unit 11.pptx

Revision guide for BTEC Unit 11 Cyber Security & Incident Management
Securing your Data, Reporting Recommended Practices

This session discusses points such as data classification, user education and highlights that there are many threats looking to obtain your data.
The GDPR Armageddon – One year on

The General Data Protection Regulation came into force on May 25th 2018 and some high profile penalties have already been passed down by the ICO for infringement. One year on, what impact is it having? Insight Data reveals the mistakes some companies are still making and how they can adapt their data processes to avoid fines of up to £20 million.
Lasa European NFP Technology Conference 2010 - Data protection and the cloud

Lasa European NFP Technology Conference 2010 - Paul Ticher's presentation on data protection and cloud computing
Preparing Research Data for Sharing

A description of the issues that need to be considered when considering sharing of research data
Privacy in Bigdata Era

The talk discusses how analytics can attack privacy and what we can do about it. It discusses the legal responses (e.g. GDPR) as well technical responses ( differential privacy and homomorphic encryption).
The video is in https://www.facebook.com/eduscopelive/videos/314847475765297/ from 1.18.
Data Privacy, Ethics and Protection. A Guidance Note on Big Data for Achievem...

This document was developed by UN Global Pulse for the United Nations Development Group. It sets out general guidance on data privacy, data protection and data ethics for the UNDG concerning the use of big data, collected in real time by private sector entities as part of their business offerings, and shared with UNDG
members for the purposes of strengthening operational
implementation of their programmes to support the
achievement of the 2030 Agenda.
Basic principles to information privacy in data mining & data warehouse

Basic Principles to
Protect Information Privacy in
Data Mining & Data Warehousing
GDPR Data Lifecycle

Global data protection regulation lifecycle of data or information on how to process data.
Personal privacy and computer technologies

these slides are about personal privacy and computer technology
GDPR Data Life Cycle

Global data protection regulation lifecycle of data or information on how to process data. Data protection, Data controller, or data processor
The Privacy Law Landscape: Issues for the research community

Presentation by Anna Johnston of Salinger Privacy to ARDC's 'GDPR and NDB scheme: Intersection with the Australian research sector' webinar on 13 September 2018
Why We Require GDPR?

About GDPR, Why we require, Penality, Principles, Cookies Management, Privacy by design, privacy notice, the web developer role
Developing a privacy compliance program

How to go about putting into pace a privacy compliance program to comply with GDPR or CCPA or similar legislation
Secure channels inc. basic rules for data protection compliance

There are general rules that cover data protection compliance. One is consent, where one should obtain consent before acquiring, holding, or using personal data wherever possible. It is also necessary to be careful with sensitive personal data, such as those pertaining to race, political opinion, health status, religious belief, sexuality, and criminal offense. https://securechannelsinc.blogspot.com/2017/09/basic-rules-for-data-protection.html
What is CJIS Compliance?

CJI applies to every individual including private entities, contractors, and members of a criminal justice entity or non-criminal justice agency representatives with access to, or who operate in support of, criminal justice services and information.
Adjusting to the GDPR: The Impact on Data Scientists and Behavioral Researchers

Our presentation introduces the GDPR then gives a brief overview of key GDPR principles and explains how they are likely to affect data scientists and behavioral researchers.
What's hot (20)
Securing your Data, Reporting Recommended Practices

Securing your Data, Reporting Recommended Practices
Lasa European NFP Technology Conference 2010 - Data protection and the cloud

Lasa European NFP Technology Conference 2010 - Data protection and the cloud
Data Privacy, Ethics and Protection. A Guidance Note on Big Data for Achievem...

Data Privacy, Ethics and Protection. A Guidance Note on Big Data for Achievem...
Basic principles to information privacy in data mining & data warehouse

Basic principles to information privacy in data mining & data warehouse
The Privacy Law Landscape: Issues for the research community

The Privacy Law Landscape: Issues for the research community
Secure channels inc. basic rules for data protection compliance

Secure channels inc. basic rules for data protection compliance
Adjusting to the GDPR: The Impact on Data Scientists and Behavioral Researchers

Adjusting to the GDPR: The Impact on Data Scientists and Behavioral Researchers
Viewers also liked
Information Security Discussion for GM667 Saint Mary's University of MN

Information Security Discussion for GM667 Saint Mary's University of MNSaint Mary's University of Minnesota
Information security basics
Information security principles an understanding

Information Security Principles are framed by every organization. These Information Security Principles give out security protocols for securing information.
Information security: importance of having defined policy & process

Information security: importance of having defined policy & processInformation Technology Society Nepal
Presentation by Soumya Mondal, on "Information Security: Importance of having definded policy & process" at "Braindigit 9th National ICT Conference 2013" organized by Information Technology Society, Nepal at Alpha House, Kathmandu, Nepal on 26th January, 2013Viewers also liked (6)
Information Security Discussion for GM667 Saint Mary's University of MN

Information Security Discussion for GM667 Saint Mary's University of MN
Information security: importance of having defined policy & process

Information security: importance of having defined policy & process
Similar to Privacy Discusssion GM667 Saint Mary's University of MN
Overview of privacy and data protection considerations for DEVELOP

Overview of privacy and data protection considerations for the DEVELOP system
New opportunities and business risks with evolving privacy regulations

In the shadow of the global pandemic and the associated economic downturn, organizations are focused on cost optimization, which often leads to impulsive decisions to deprioritize compliance with all nonrevenue programs.
Regulators have evolved to adapt with the notable increase in data subject complaints and are getting more serious about organizations that don’t properly protect consumer data. Marriott was hit with a $124 million fine while Equifax agreed to pay a minimum of $575 million for its breach. The US Federal Trade Commission, the US Consumer Financial Protection Bureau (CFPB), and all 50 U.S. states and territories sued over the company’s failure to take “reasonable steps” to secure its sensitive personal data.
Privacy and data protection are enforced by a growing number of regulations around the world and people are actively demanding privacy protection — and legislators are reacting. More than 60 countries have introduced privacy laws in response to citizens’ cry for transparency and control. By 2023, 65% of the world’s population will have its personal information covered under modern privacy regulations, up from 10% today, according to Gartner. There is a convergence of data privacy principles, standards and regulations on a common set of fundamental principles.
The opportunities to use data are growing exponentially, but so too are the business and financial risks as the number of data protection and privacy regulations grows internationally.
Join this webinar to learn more about:
- Trends in modern privacy regulations
- The impact on organizations to protect and use sensitive data
- Data privacy principles
- The impact of General Data Protection Regulation (GDPR) and data transfer between US and EU
- The evolving CCPA, the new PCI DSS version 4 and new international data privacy laws or regulations
- Data privacy best practices, use cases and how to control sensitive personal data throughout the data life cycle
Data Privacy and consent management .. .

Data privacy and consent management are critical aspects of ensuring that individuals' personal information is handled responsibly and ethically, particularly in healthcare settings where sensitive medical data is involved. Data privacy refers to the protection of personal information from unauthorized access, use, or disclosure, while consent management involves obtaining and managing individuals' permissions for the collection, storage, and processing of their data.
In healthcare, patients entrust providers with their sensitive medical information, expecting that it will be kept confidential and used only for legitimate purposes related to their care. Robust data privacy measures include encryption, access controls, and anonymization techniques to safeguard patient data from unauthorized access or breaches. Additionally, healthcare organizations must adhere to regulatory standards such as HIPAA in the United States or GDPR in the European Union, which outline specific requirements for the protection of patient information and impose penalties for non-compliance.
Consent management plays a crucial role in ensuring that individuals have control over how their data is used. Patients should be informed about the purposes for which their data will be collected and processed, as well as any potential risks or benefits associated with its use. Obtaining informed consent involves providing individuals with clear and transparent information about their privacy rights and giving them the opportunity to consent to or decline the use of their data for specific purposes. Consent management systems help healthcare organizations track and manage patients' consent preferences, ensuring that data is used in accordance with their wishes and legal requirements.
Effective data privacy and consent management practices not only protect individuals' privacy rights but also foster trust and transparency in healthcare relationships. By implementing robust security measures, respecting patients' autonomy, and promoting informed decision-making, healthcare organizations can uphold the principles of data privacy and consent while leveraging data responsibly to improve patient care and outcomes.
Data privacy and consent management (K.sailaja).pptx

Data Privacy and consent management in clinical research.
General Data Protection Regulation or GDPR

General Data Protection Regulation or GDPR,he way companies across the world will handle their customers' personal information and creating strengthened and unified data protection for all individuals within the EU.
Digital Personal Data Protection (DPDP) Practical Approach For CISOs

Key Discussion Pointers:
1. Introduction to Data Privacy
- What is data privacy
- Privacy laws around the globe
- DPDPA Journey
2. Understanding the New Indian DPDPA 2023
- Objectives
- Principles of DPDPA
- Applicability
- Rights & Duties of Individuals
- Principals
- Legal implications/penalties
3. A practical approach to DPDPA compliance
- Personal data Inventory
- DPIA
- Risk treatment
GDPR Breakfast Briefing for Business Advisors

GDPR Breakfast Briefing for Business Advisors at Hilton Puckrup Hall, on 8th March 2018
GDPR Breakfast Briefing - For Business Owners, HR Directors, Marketing Direct...

GDPR Breakfast Briefing - For Business Owners, HR Directors, Marketing Direct...Harrison Clark Rickerbys
Slideshow from GDPR Breakfast Briefing - For Business Owners, HR Directors, Marketing Directors, IT Directors & Ops Directors, on 7th March 2018 at Hilton Puckrup HallReasonable Security Practices And Procedures And Sensitive Personala 24 06 2...

REASONABLE SECURITY PRACTICES AND PROCEDURES AND SENSITIVE PERSONAL DATA OR INFORMATION RULES, 2011
Under
The (Indian) Information Technology Act, 2000
Ichec & ESC gdpr feb 2020

Class given in February 2020 at Ichec Brussels Management School and at ESC Rennes
Similar to Privacy Discusssion GM667 Saint Mary's University of MN (20)
Overview of privacy and data protection considerations for DEVELOP

Overview of privacy and data protection considerations for DEVELOP
New opportunities and business risks with evolving privacy regulations

New opportunities and business risks with evolving privacy regulations
Data privacy and consent management (K.sailaja).pptx

Data privacy and consent management (K.sailaja).pptx
Digital Personal Data Protection (DPDP) Practical Approach For CISOs

Digital Personal Data Protection (DPDP) Practical Approach For CISOs
Saying "I Don't": the requirement of data subject consent for purposes of dat...

Saying "I Don't": the requirement of data subject consent for purposes of dat...
GDPR Breakfast Briefing - For Business Owners, HR Directors, Marketing Direct...

GDPR Breakfast Briefing - For Business Owners, HR Directors, Marketing Direct...
Managing Data Protection guide powerpoint presentation

Managing Data Protection guide powerpoint presentation
Reasonable Security Practices And Procedures And Sensitive Personala 24 06 2...

Reasonable Security Practices And Procedures And Sensitive Personala 24 06 2...
More from Saint Mary's University of Minnesota
Digital literacy, competence and citizenship

A presentation on Digital literacy, competence and citizenship
Symposium eddeve

Please see & post my attached Power Point Presentation for the EDD Symposium assignment requested by Dr. McClure.
Thanks, Elena V-E
At risk high school students and high prestige

Here are five slides that provide some information about my dissertation proposal. -Todd
Blackboard Basics for New Faculty Orientation 10/15

Blackboard Basics for New Faculty Orientation 10/15
Strategic Change Interventions Team D/Module 7 

Tami Bennett-Tait
Patrice Howard
Nerita Hughes
Rebecca Stuart
More from Saint Mary's University of Minnesota (20)
Blackboard Basics for New Faculty Orientation 10/15

Blackboard Basics for New Faculty Orientation 10/15
Recently uploaded
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Recently uploaded (20)
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Privacy Discusssion GM667 Saint Mary's University of MN
- 1. 1 Privacy Privacy is an abstract and contentious term It is often described as a basic right Privacy has several dimensions: (Richard Clarke) Privacy of the person; “bodily privacy” Privacy of personal behavior Privacy of personal communications Privacy of personal data
- 2. 2 Information Privacy A combination of communications and data privacy Recognition of the impact computer and networking technologies have had upon our individual privacy Affords us the control over: Acquisition of private information; access; collection Distribution or transfer of private information Use of private information; intended purpose Unwanted solicitation; “invasion of privacy” Storage
- 3. 3 Privacy Laws, Rules and Guidelines Many privacy rules and laws can be traced back to the foundational work of the OECD in 1980. Organization for Economic Cooperation and Development: www.oecd.org Eight privacy principles were developed that were forward looking and technology neutral. TC 615 Fall 2007
- 4. 4 OECD on Privacy Collection Limitation Principle There should be limits to the collection of personal data and any such data should be obtained by lawful and fair means and, where appropriate, with the knowledge or consent of the data subject. Data Quality Principle Personal data should be relevant to the purposes for which they are to be used, and, to the extent necessary for those purposes, should be accurate, complete and kept up-to-date. Purpose Specification Principle The purposes for which personal data are collected should be specified not later than at the time of data collection and the subsequent use limited to the fulfillment of those purposes. Use Limitation Principle Personal data should not be disclosed, made available or otherwise used for purposes other than those specified in accordance with the above, except with the consent of the data subject or by the authority of law
- 5. 5 TC 615 Fall 2007 OECD on Privacy Security Safeguards Principle Personal data should be protected by reasonable security safeguards against such risks as loss or unauthorized access, destruction, use, modification or disclosure of data. Openness Principle There should be a general policy of openness about developments, practices and policies with respect to personal data. Means should be readily available of establishing the existence and nature of personal data, and the main purposes of their use, as well as the identity and usual residence of the data controller
- 6. 6 TC 615 Fall 2007 OECD on Privacy Individual Participation Principle An individual should have the right: a) to obtain from a data controller, or otherwise, confirmation of whether or not the data controller has data relating to him; b) to have communicated to him, data relating to him within a reasonable time; at a charge, if any, that is not excessive; in a reasonable manner; and in a form that is readily intelligible to him; c) to be given reasons if a request made under subparagraphs(a) and (b) is denied, and to be able to challenge such denial; and d) to challenge data relating to him and, if the challenge is successful to have the data erased, rectified, completed or amended. Accountability Principle A data controller should be accountable for complying with measures which give effect to the principles stated above
