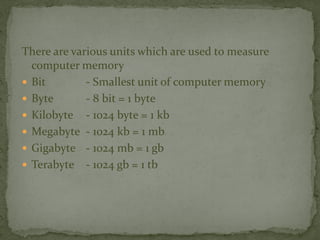
This document discusses computer memory and storage. It defines different units of memory like bits, bytes, kilobytes etc. It describes primary memory (RAM and ROM) and secondary storage devices like magnetic tapes, disks, optical disks (CDs and DVDs). RAM is volatile and needs power, while ROM is non-volatile and contains the BIOS. Common secondary storage devices include hard disks to store operating systems and files, floppy disks, and optical disks like CDs and DVDs for high capacity storage.