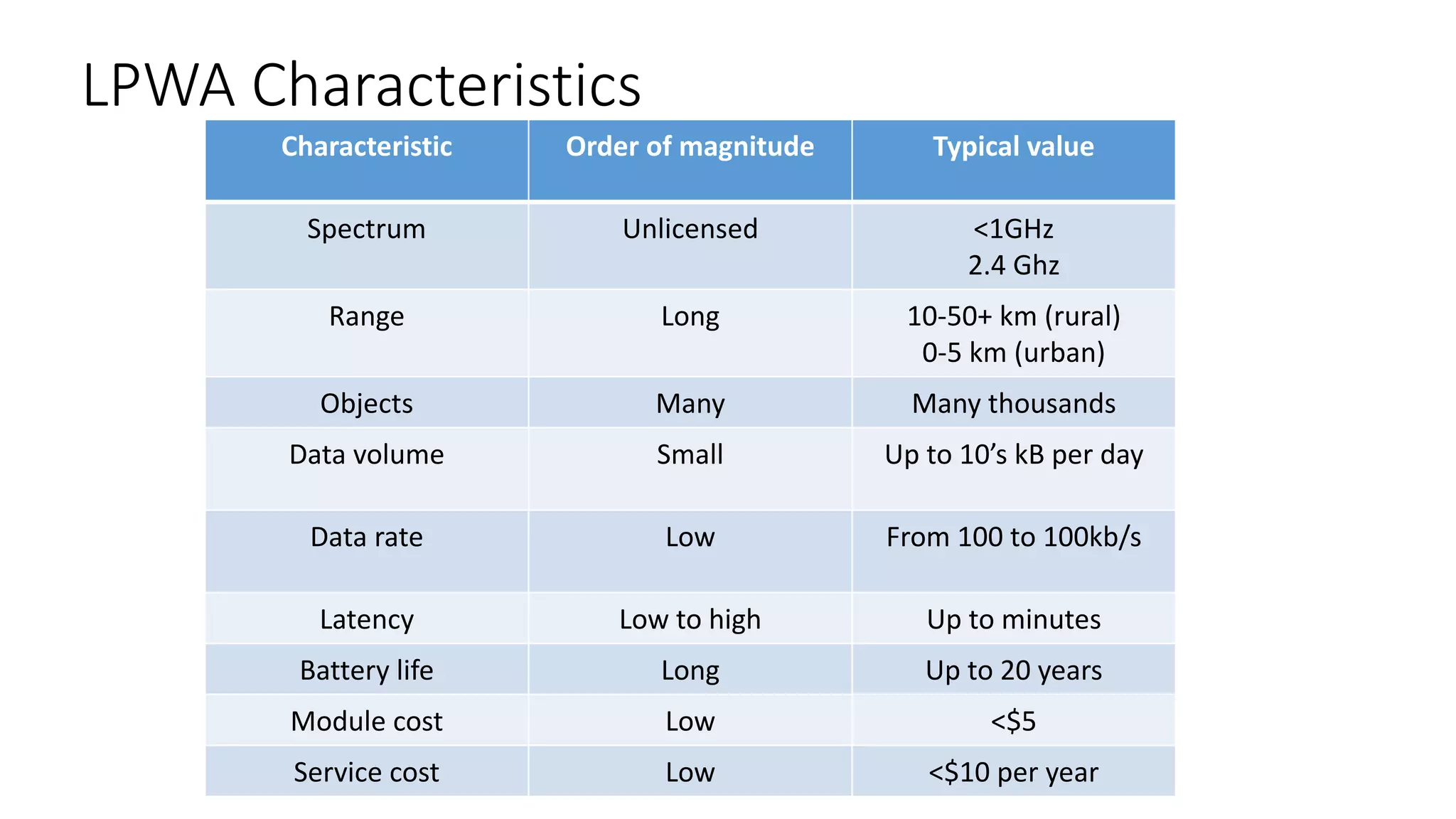
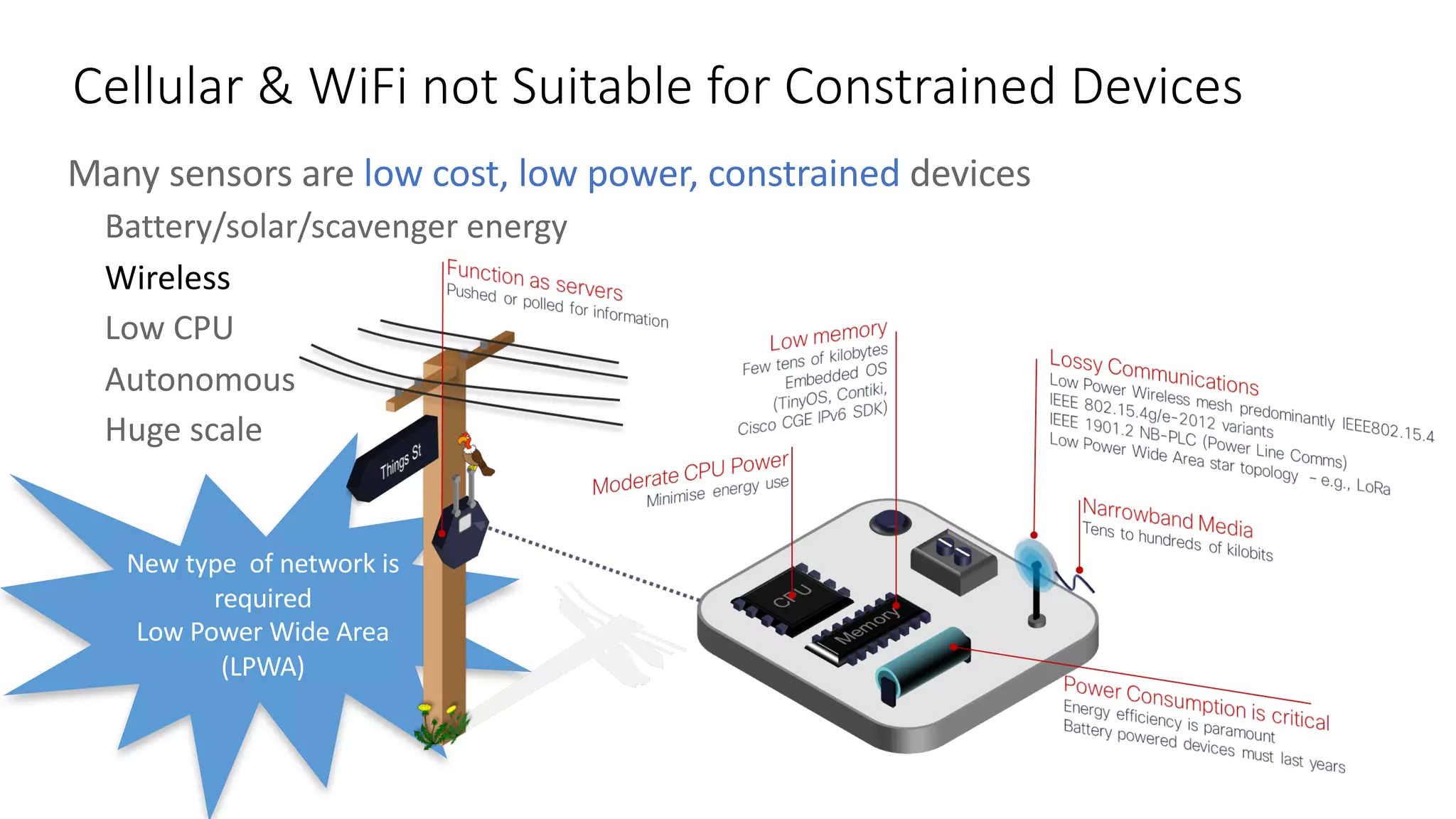
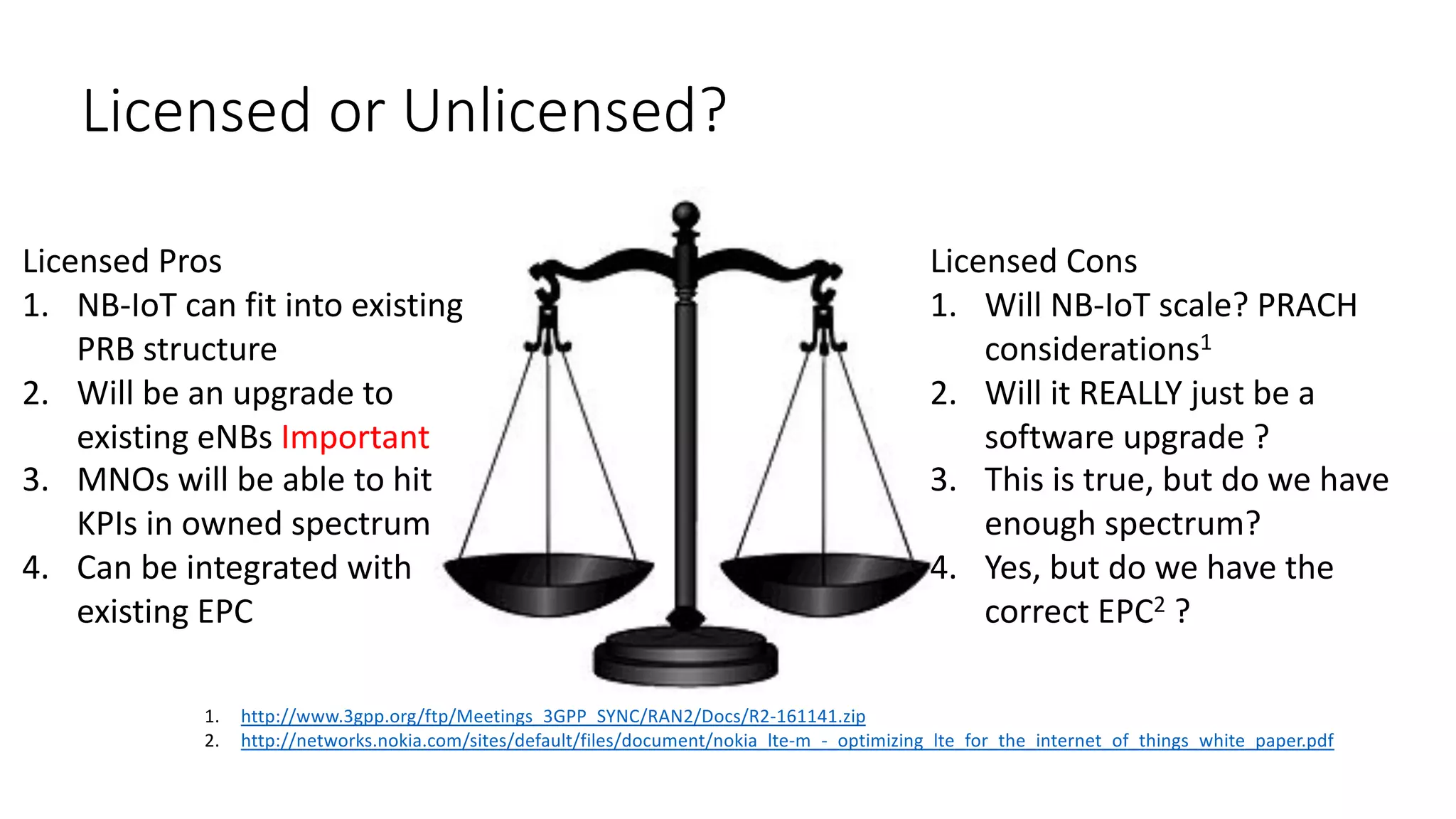
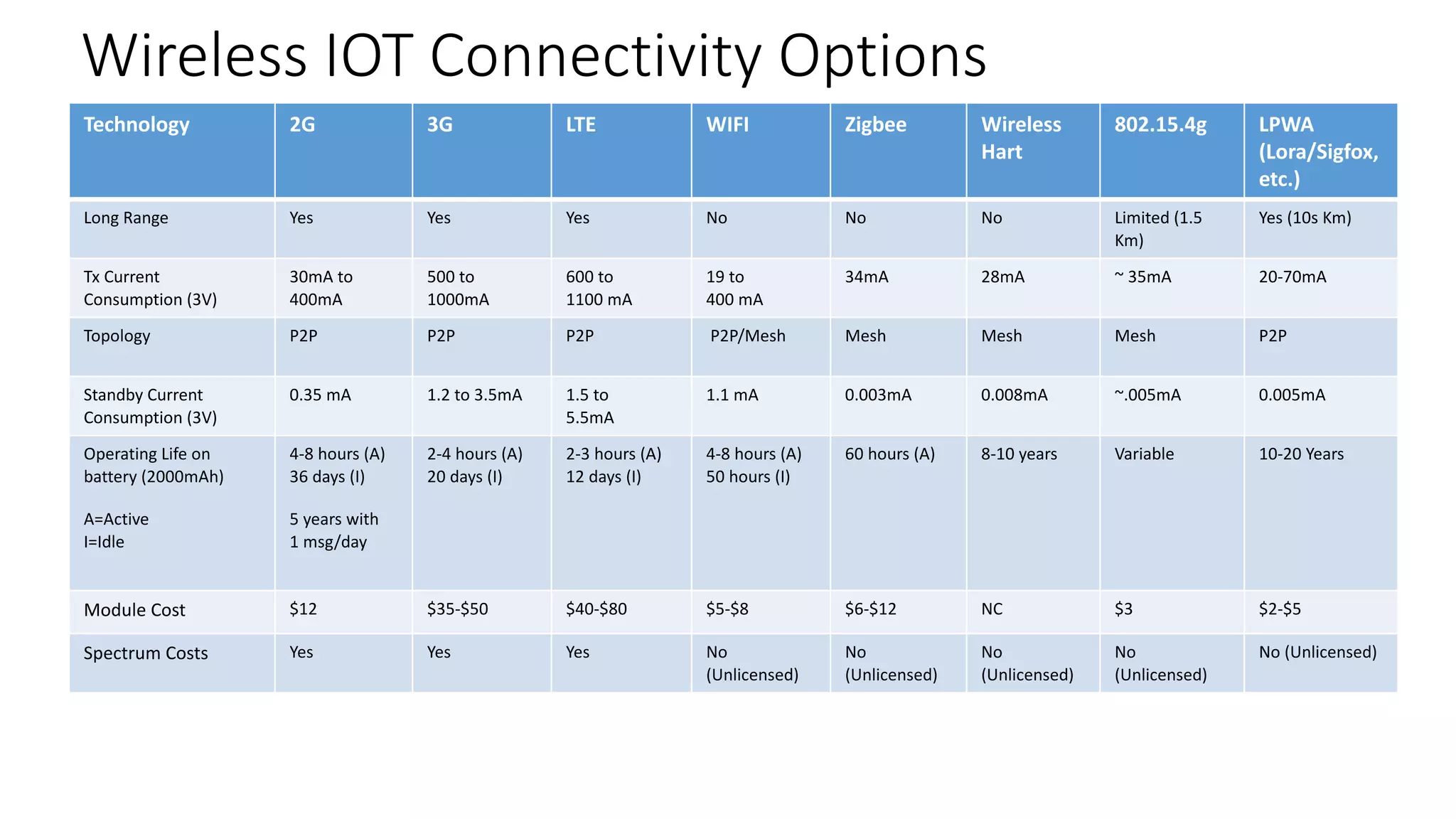
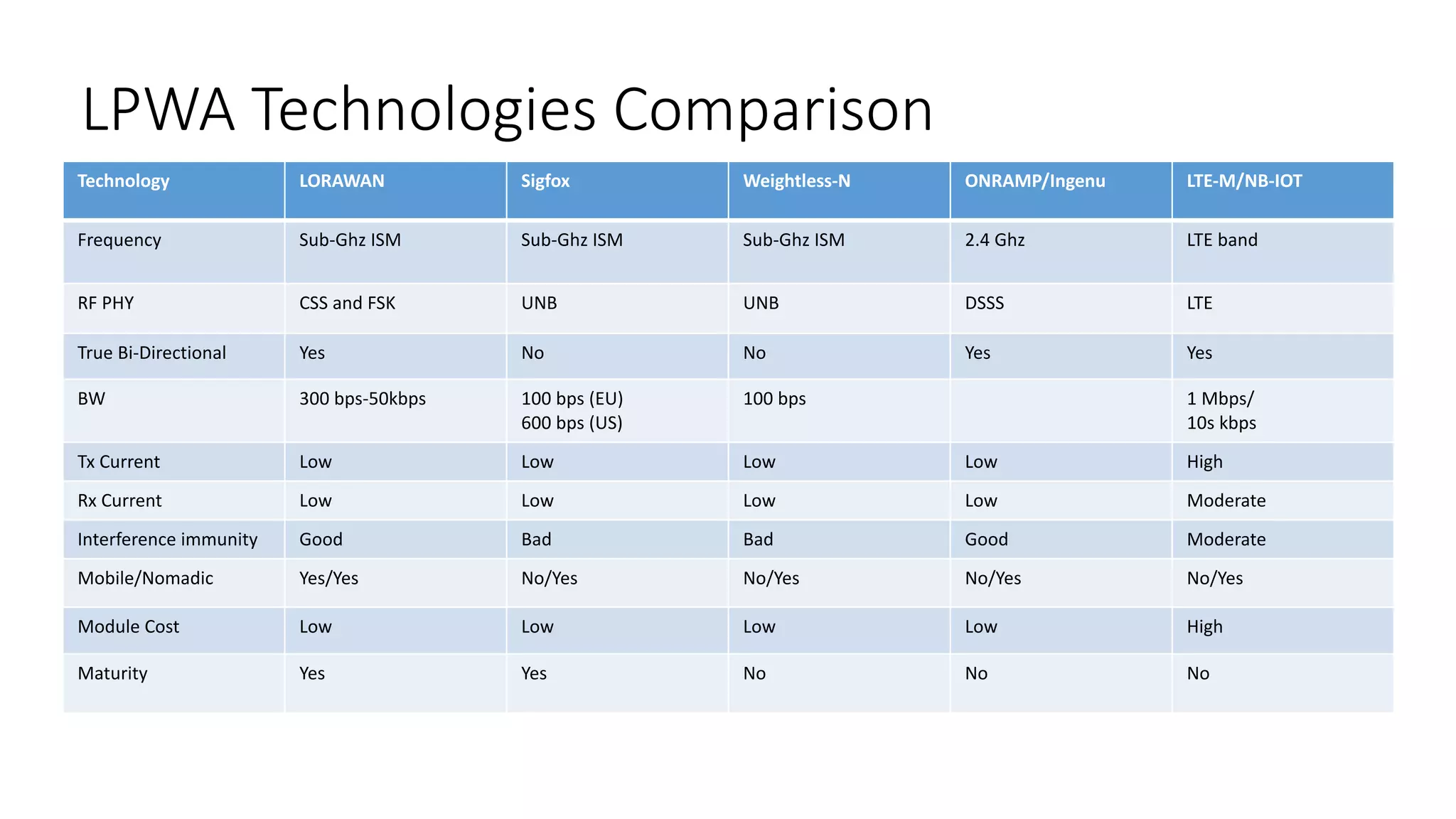
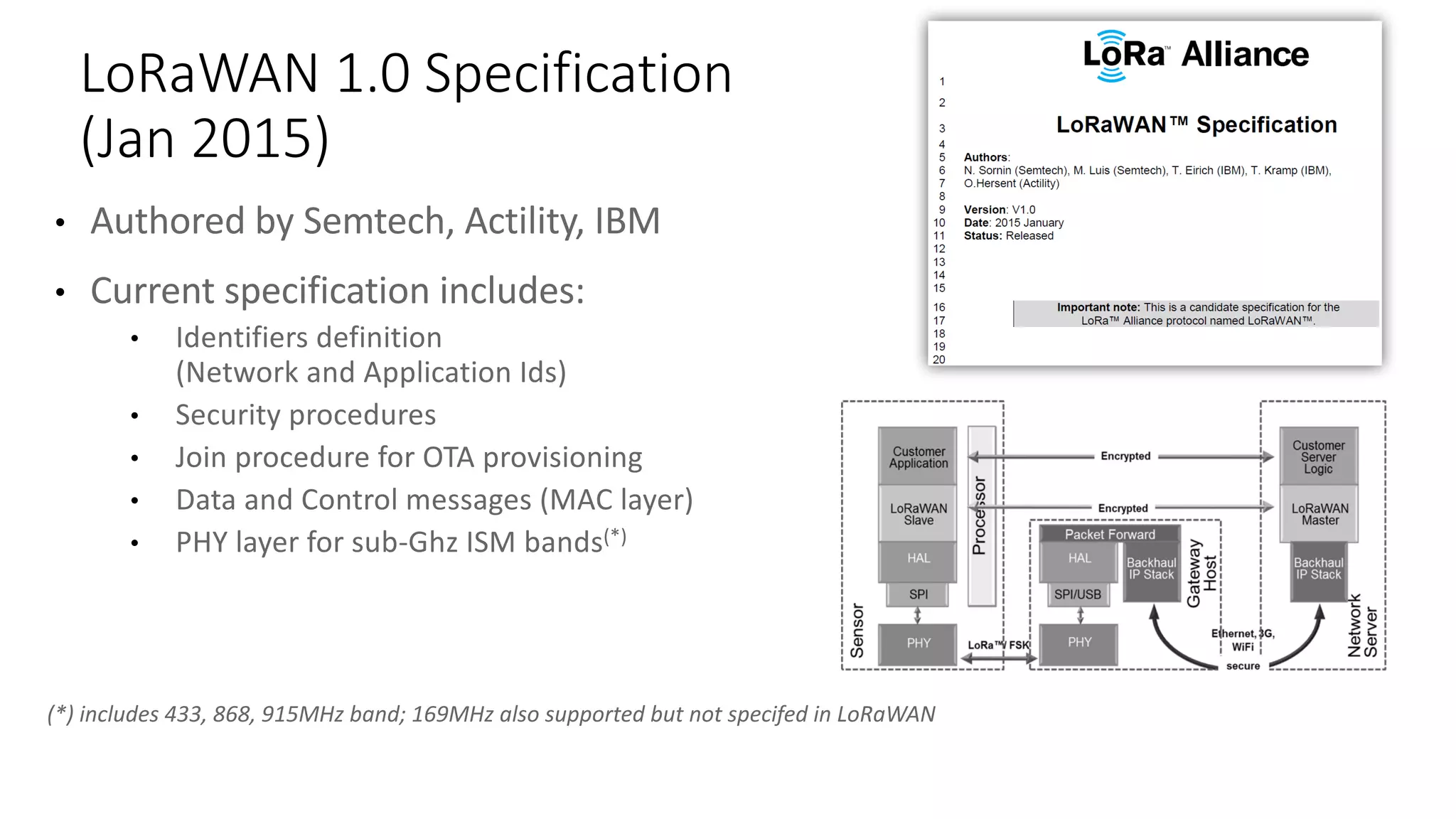
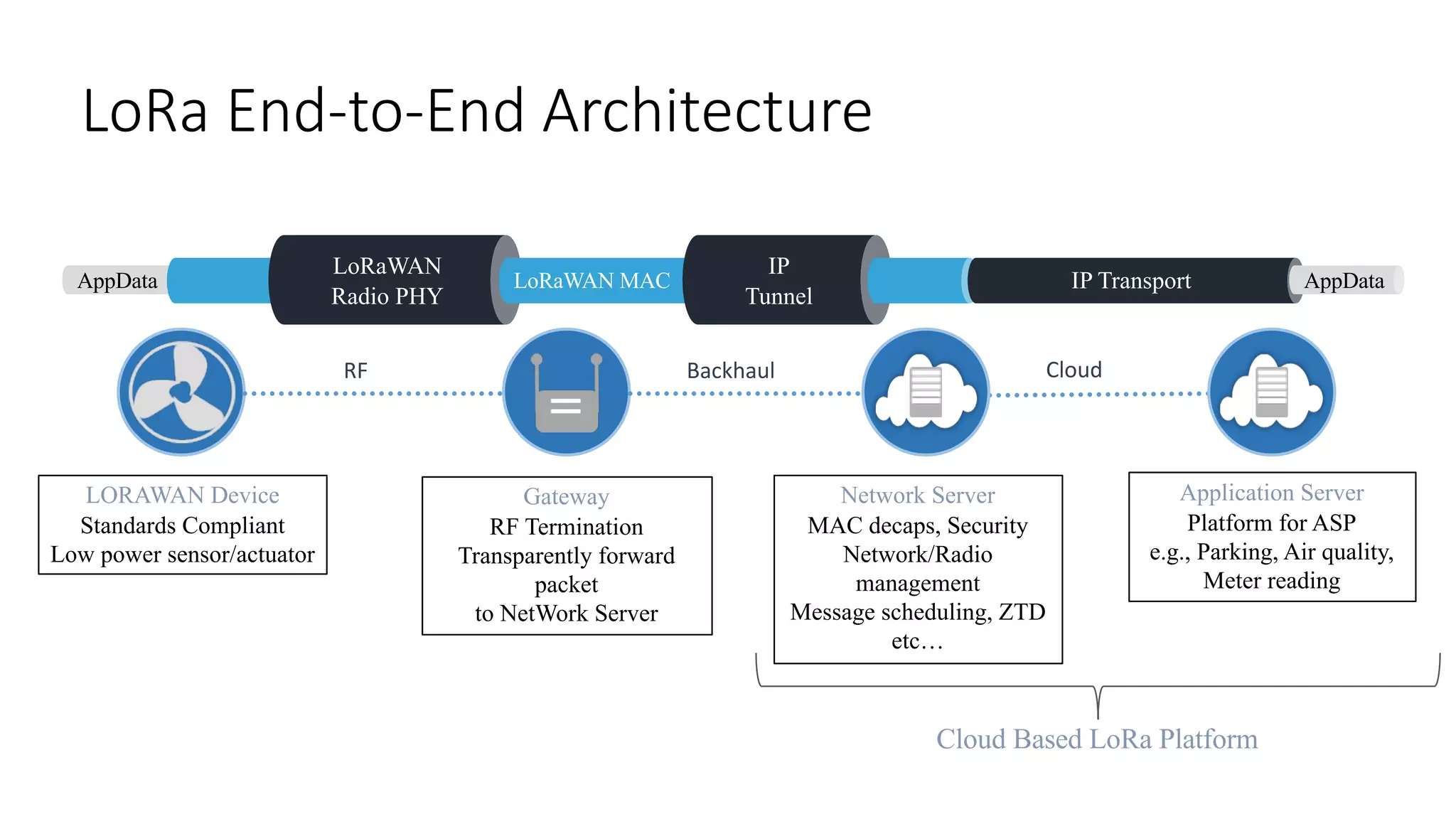
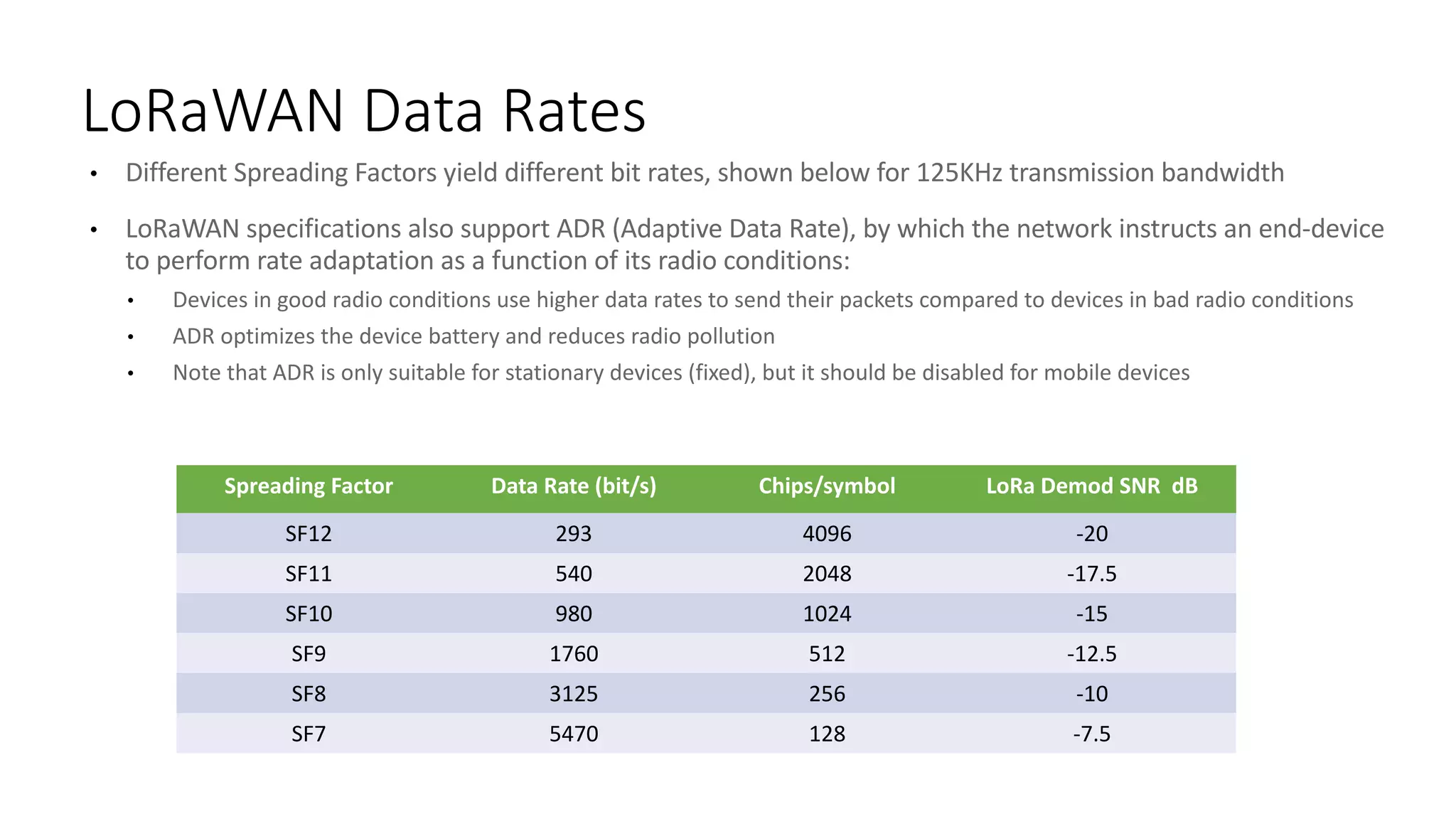
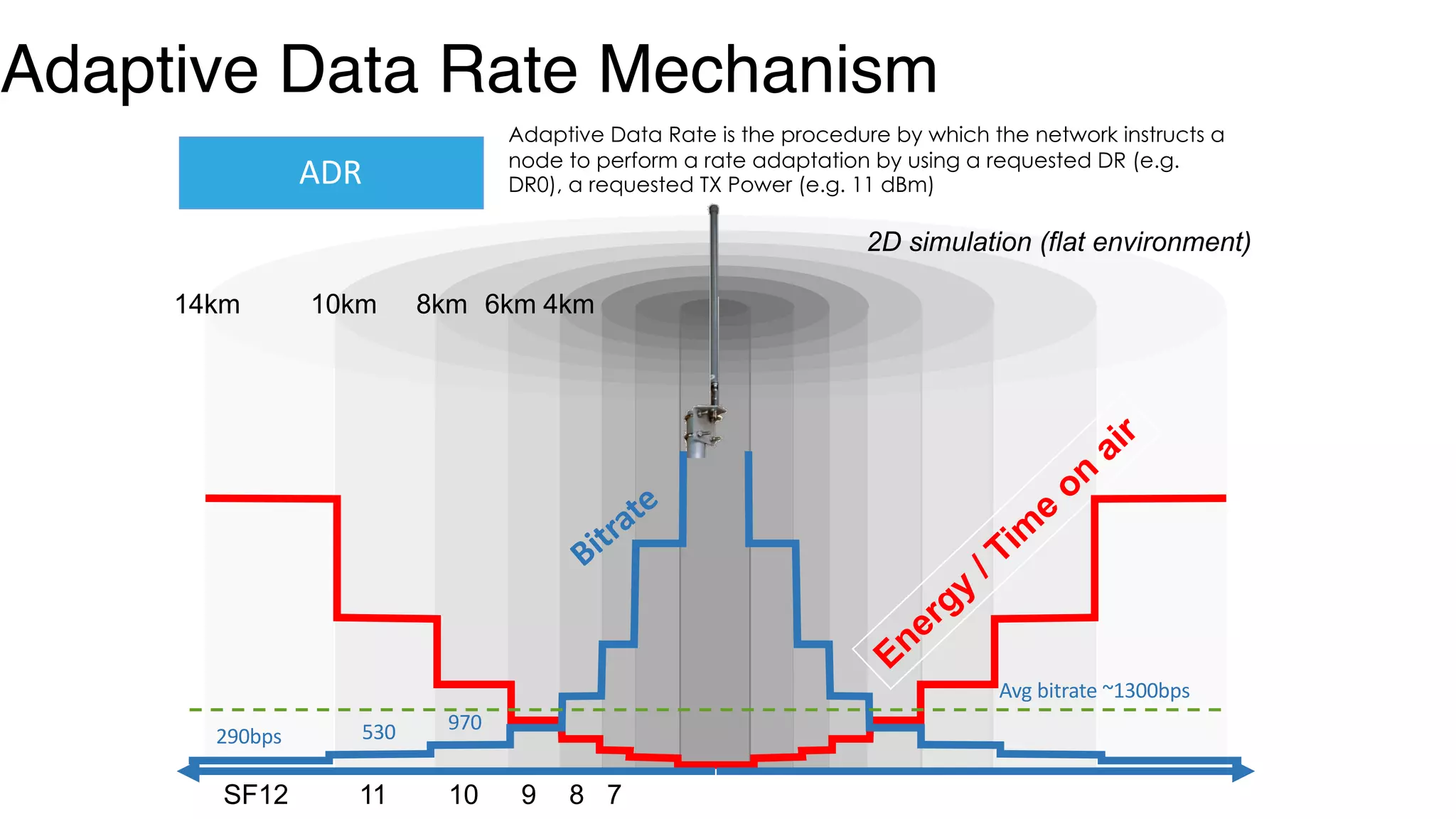
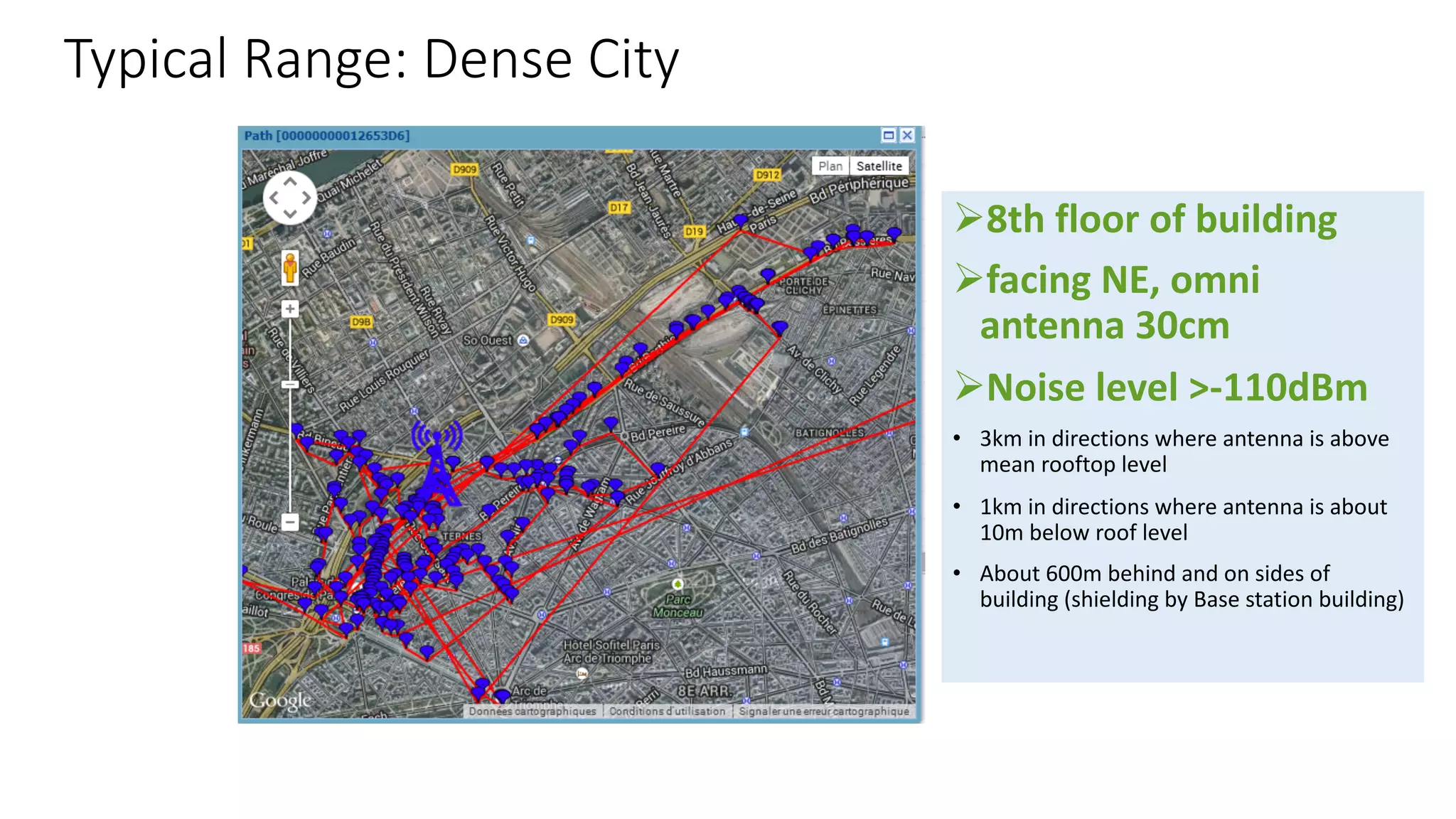
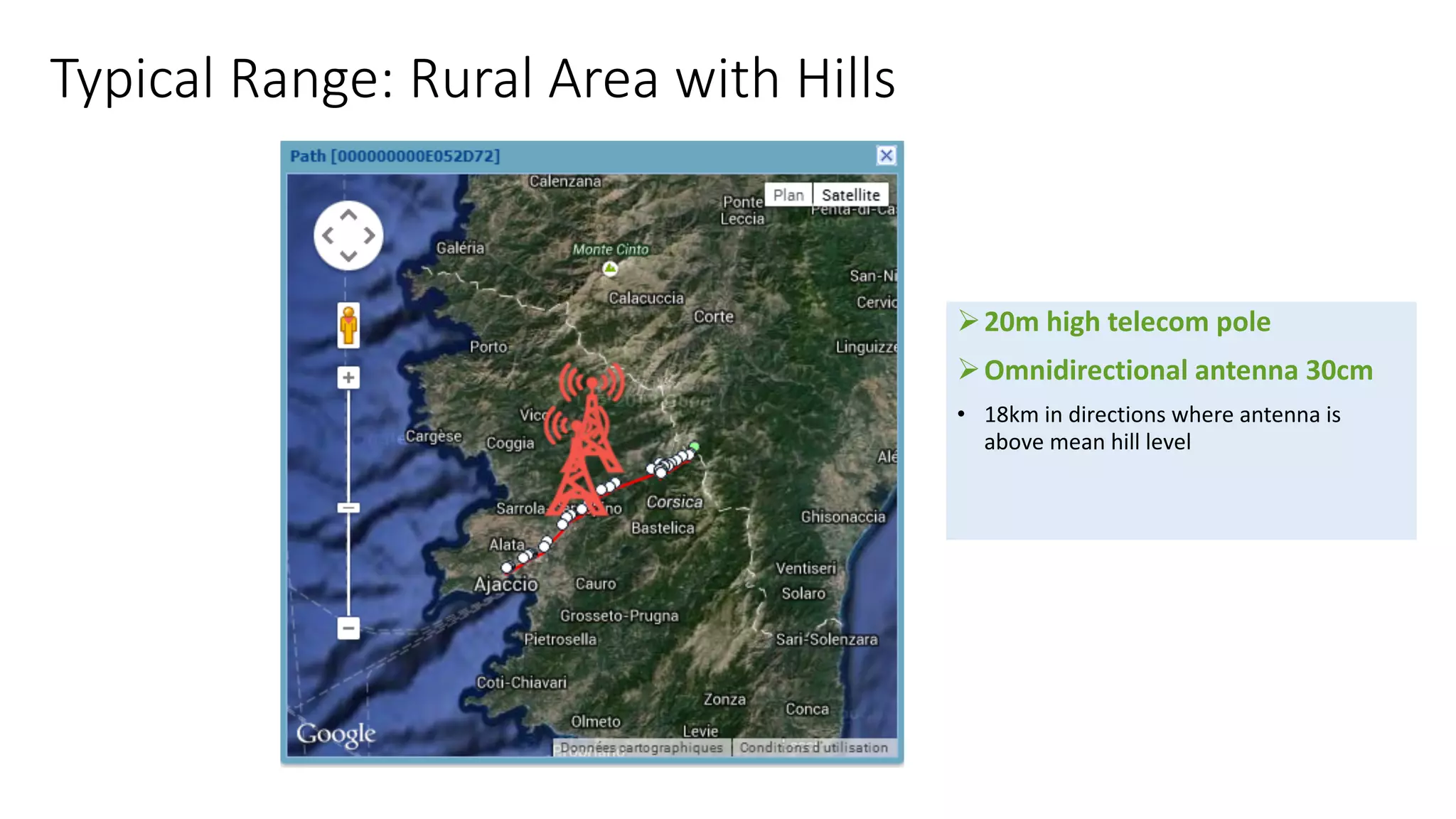
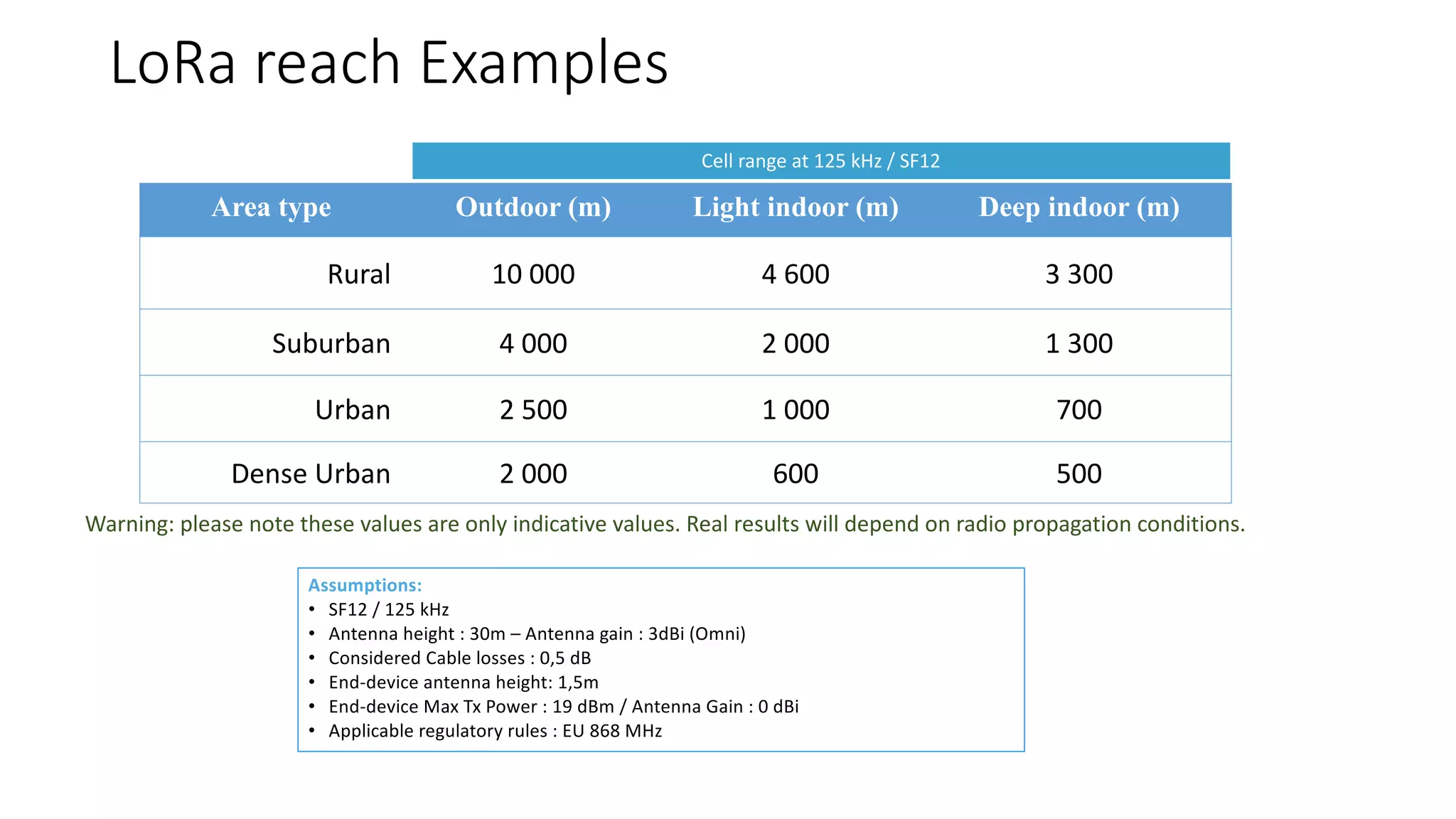
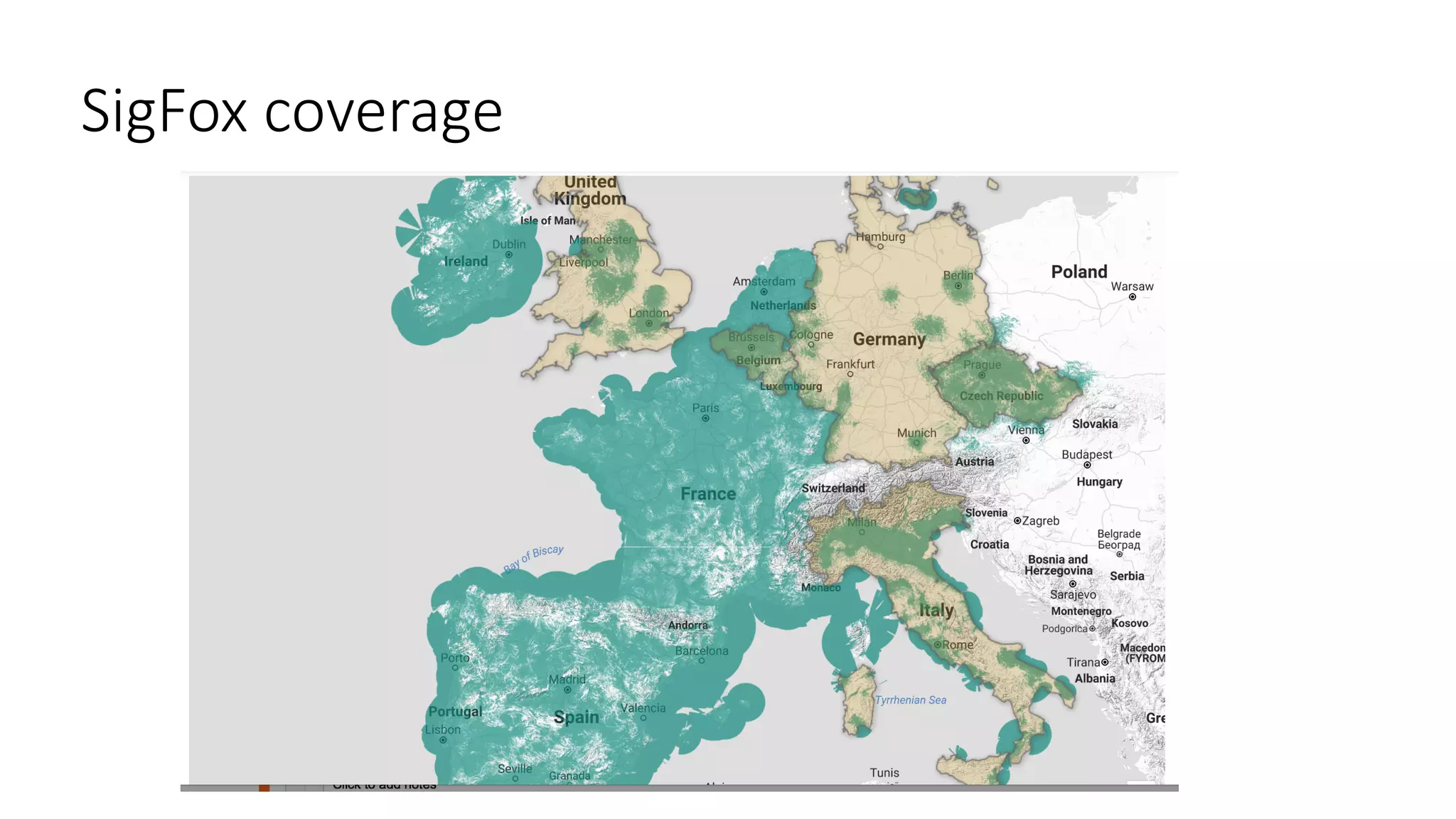
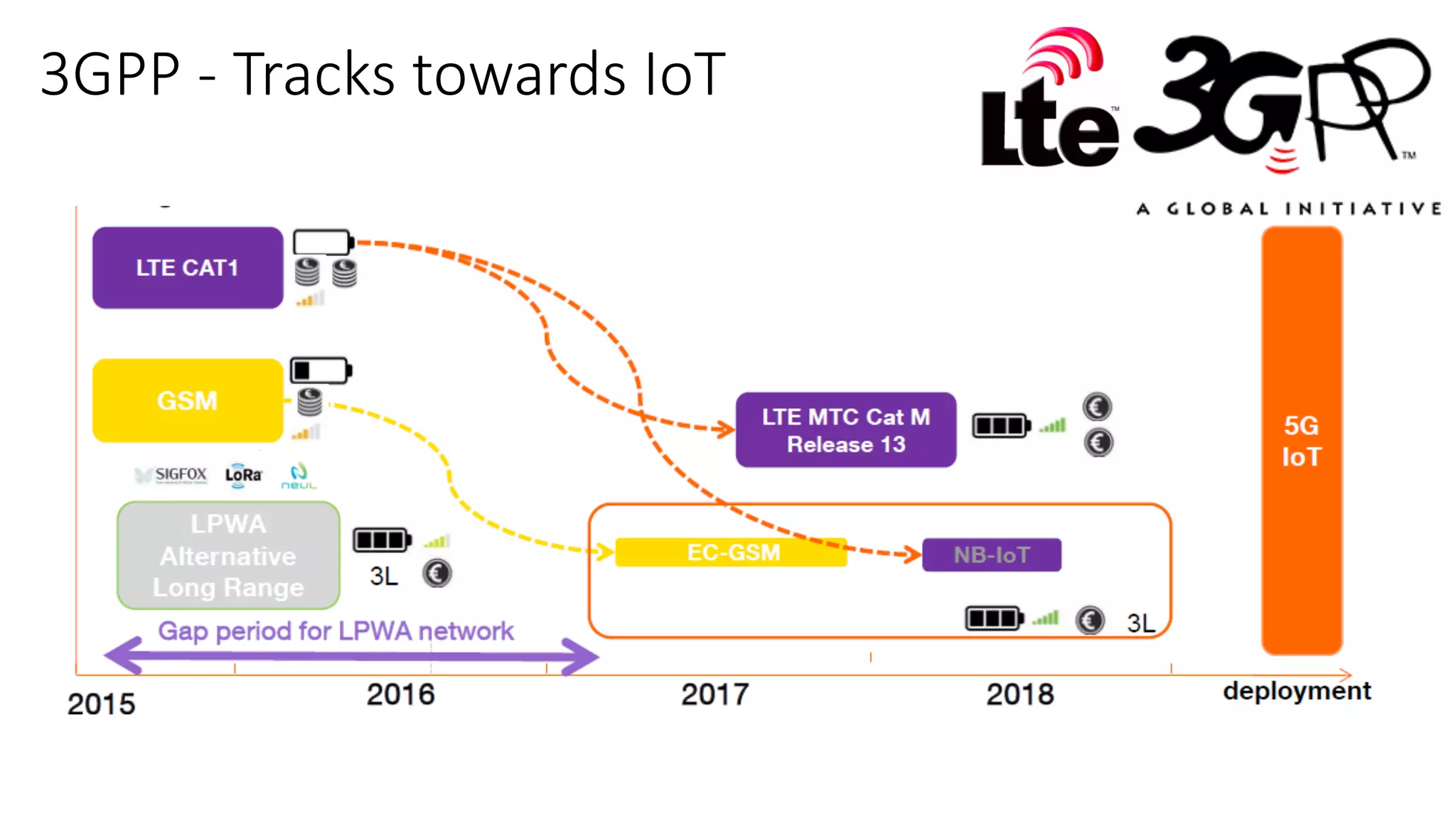
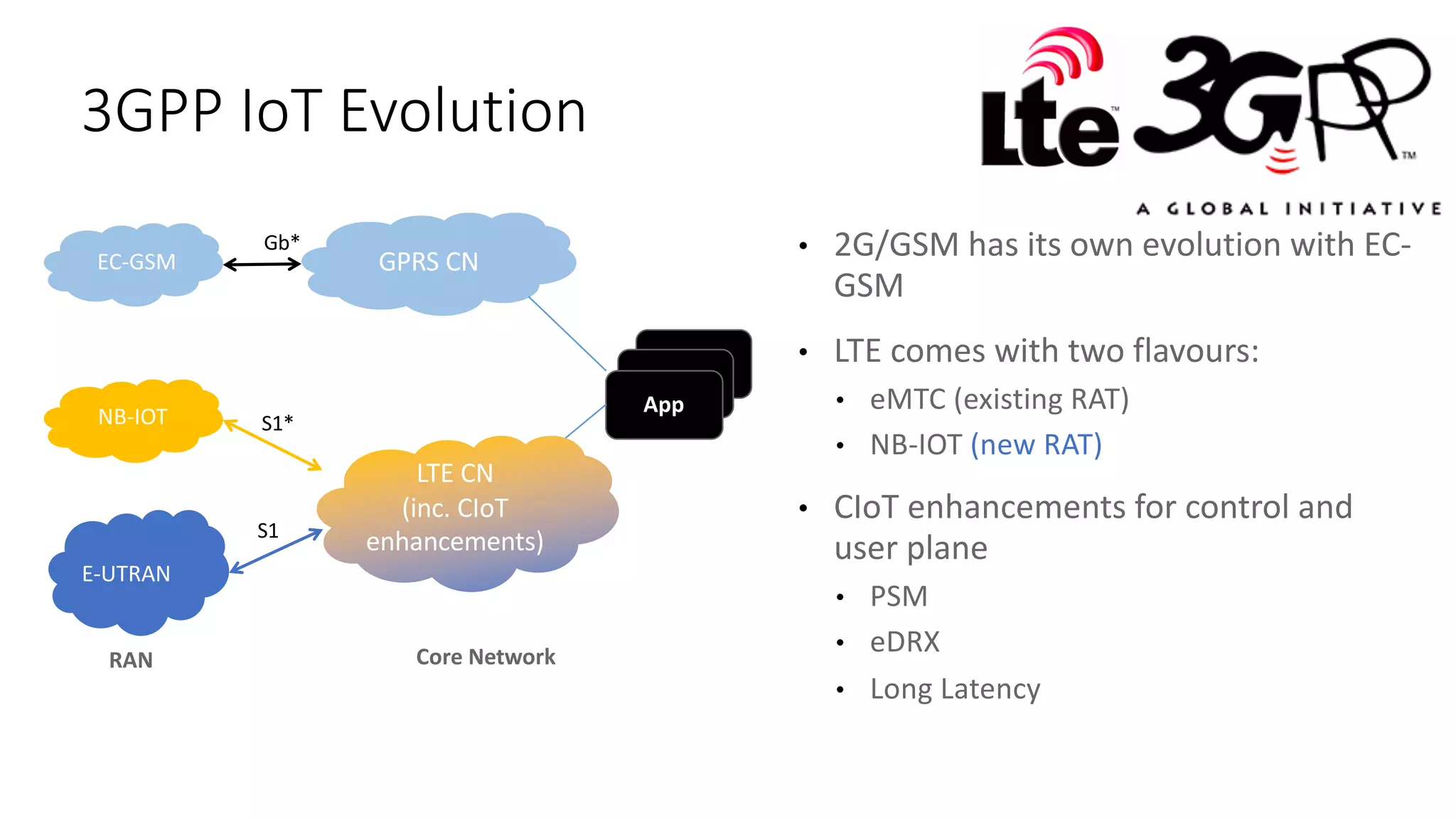
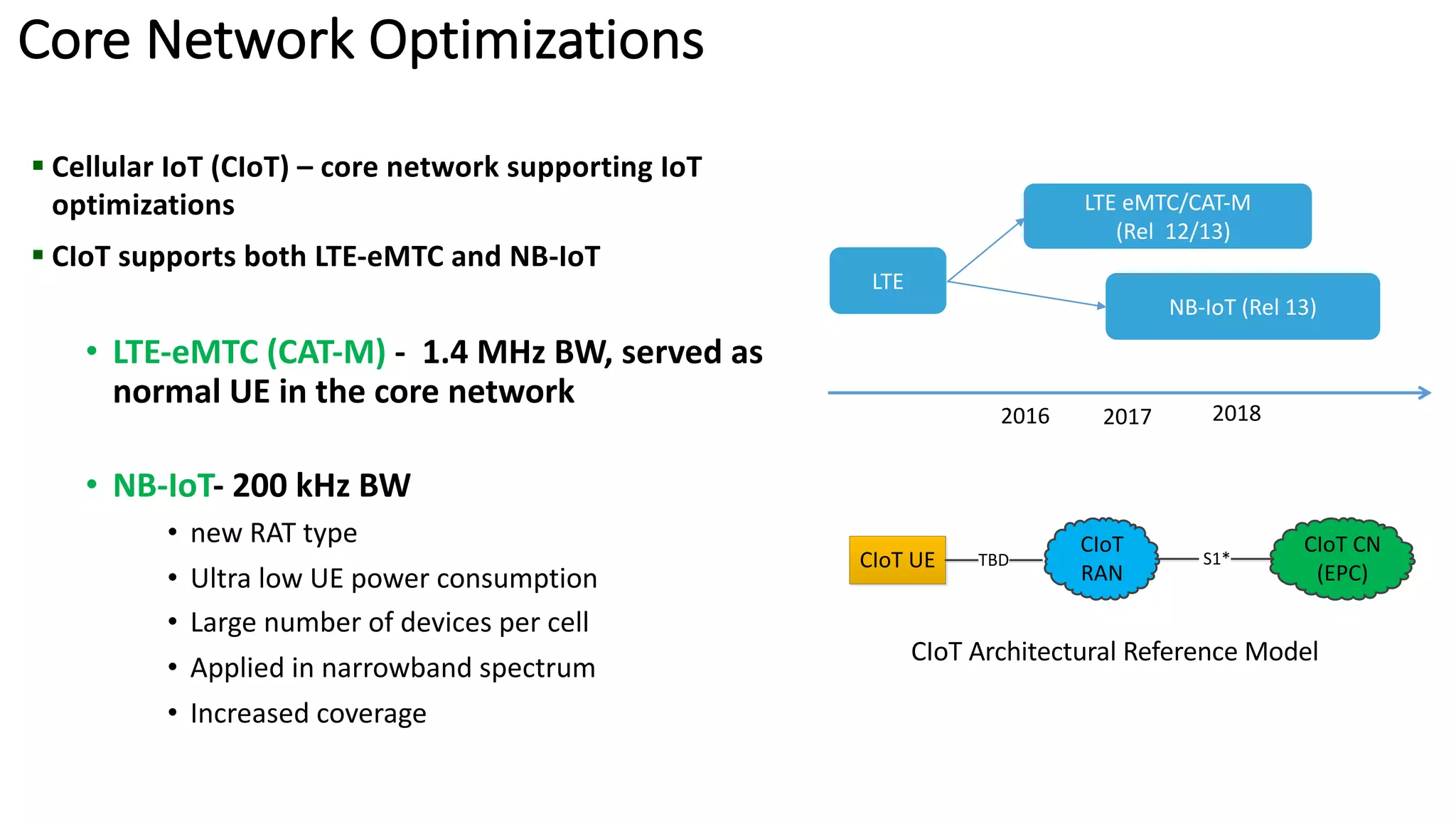
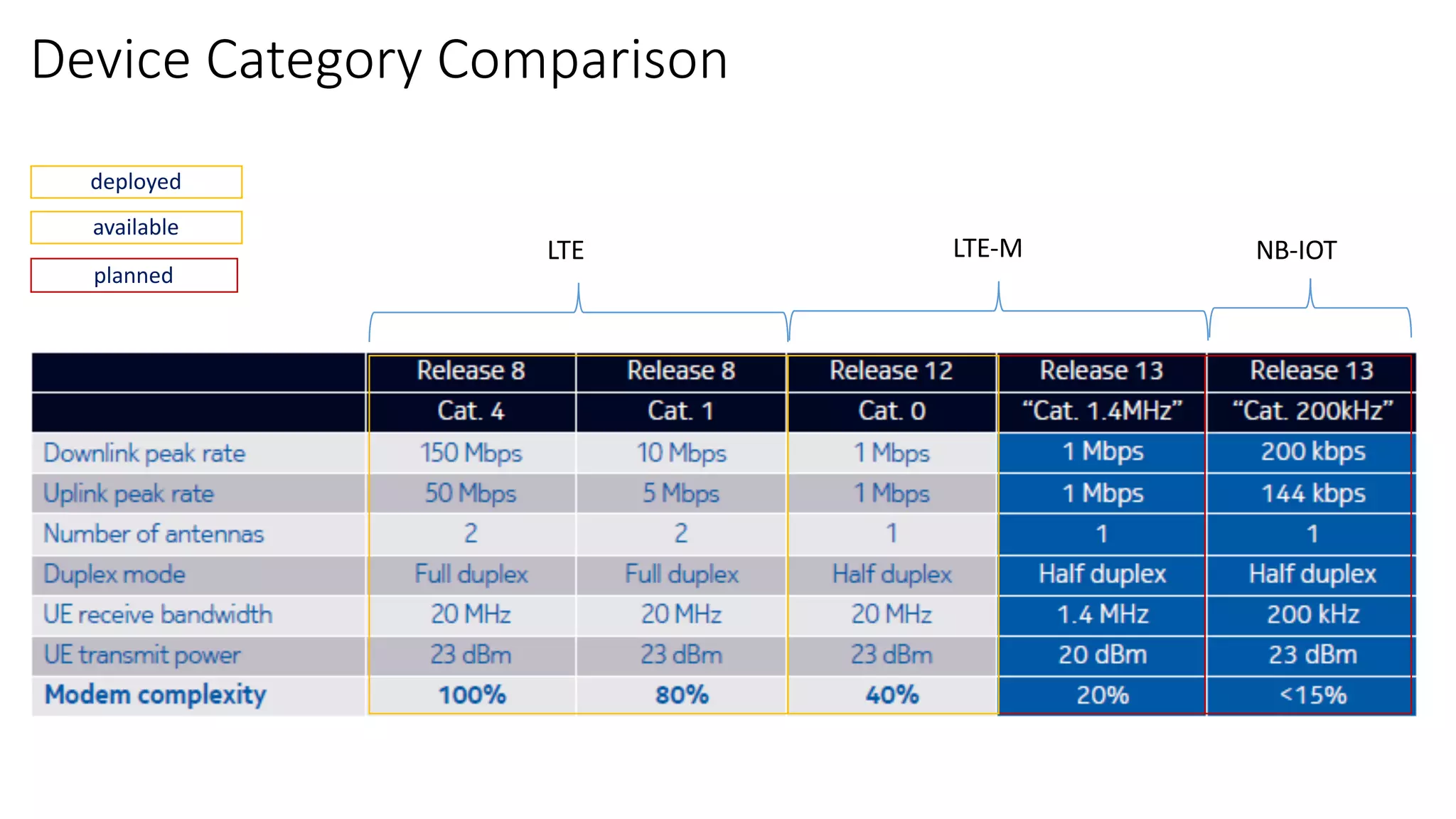
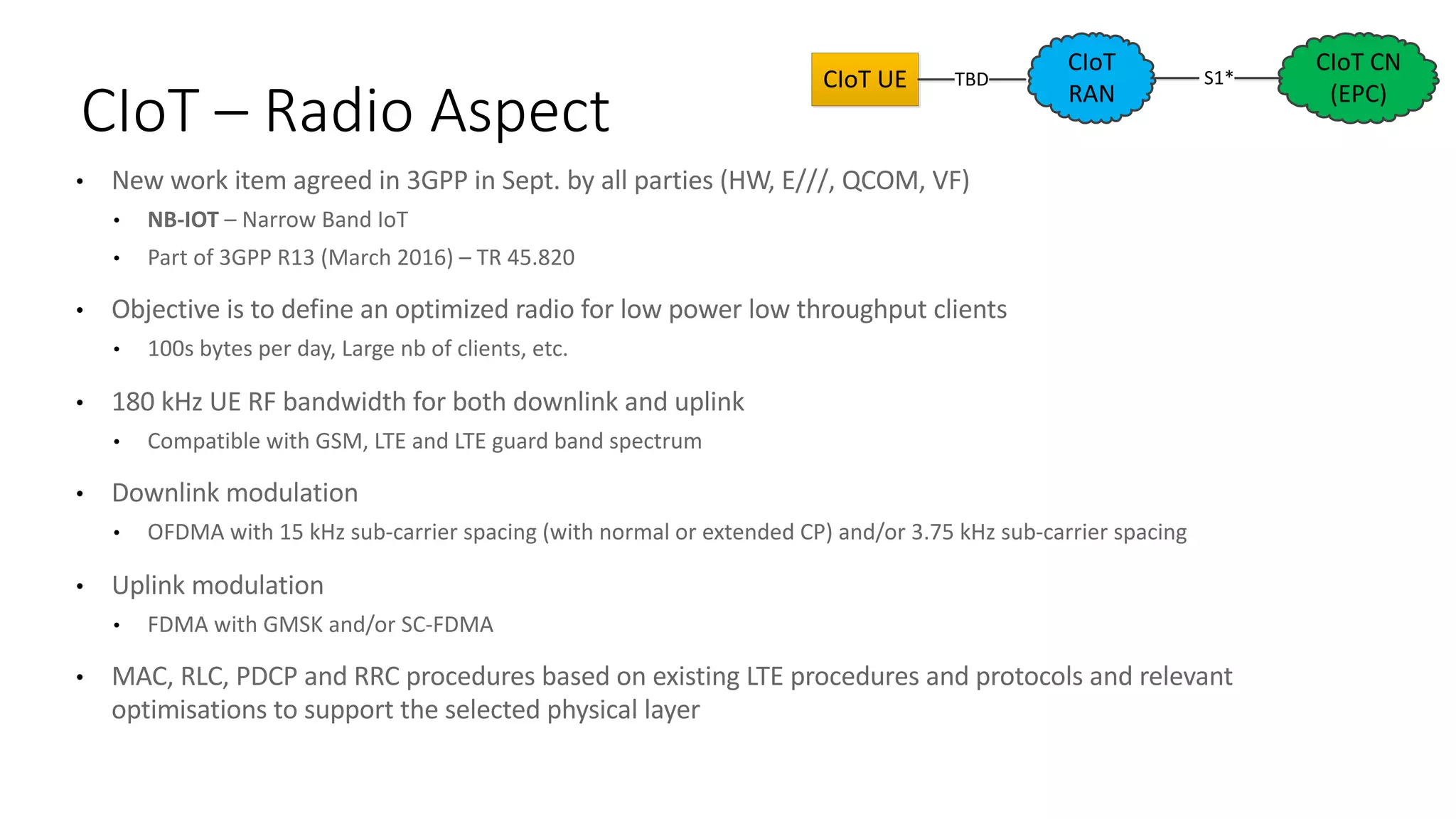
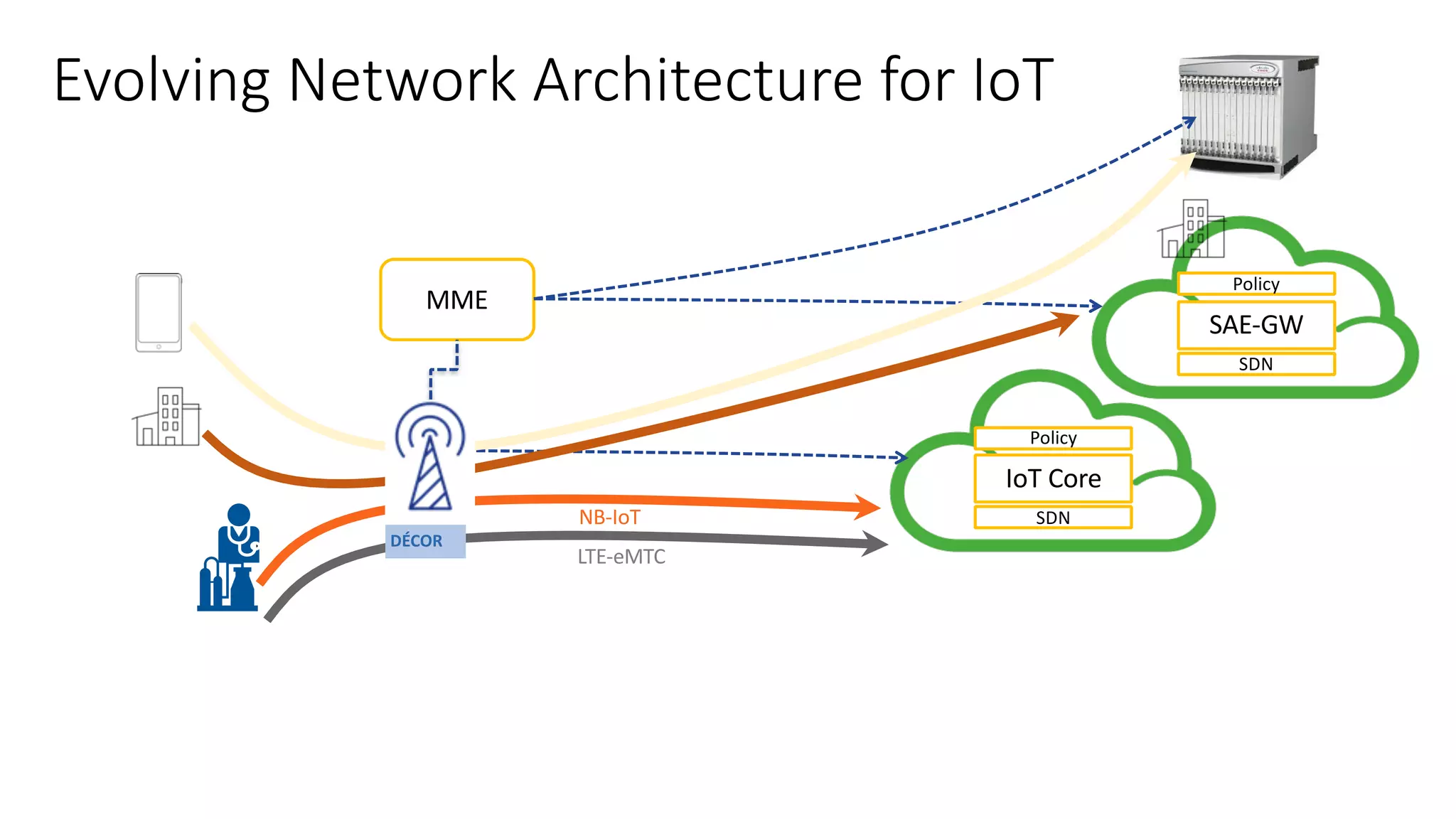
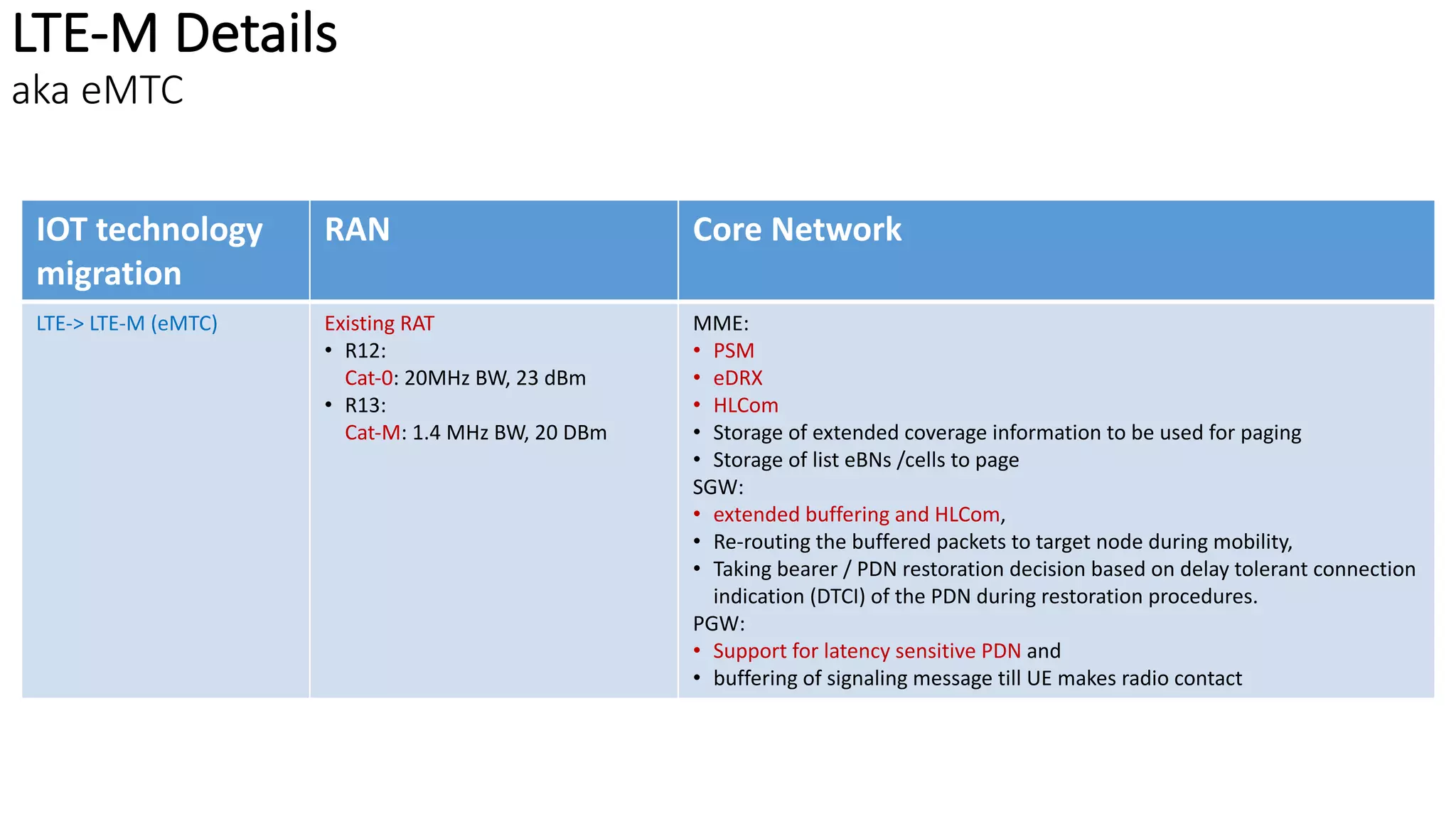
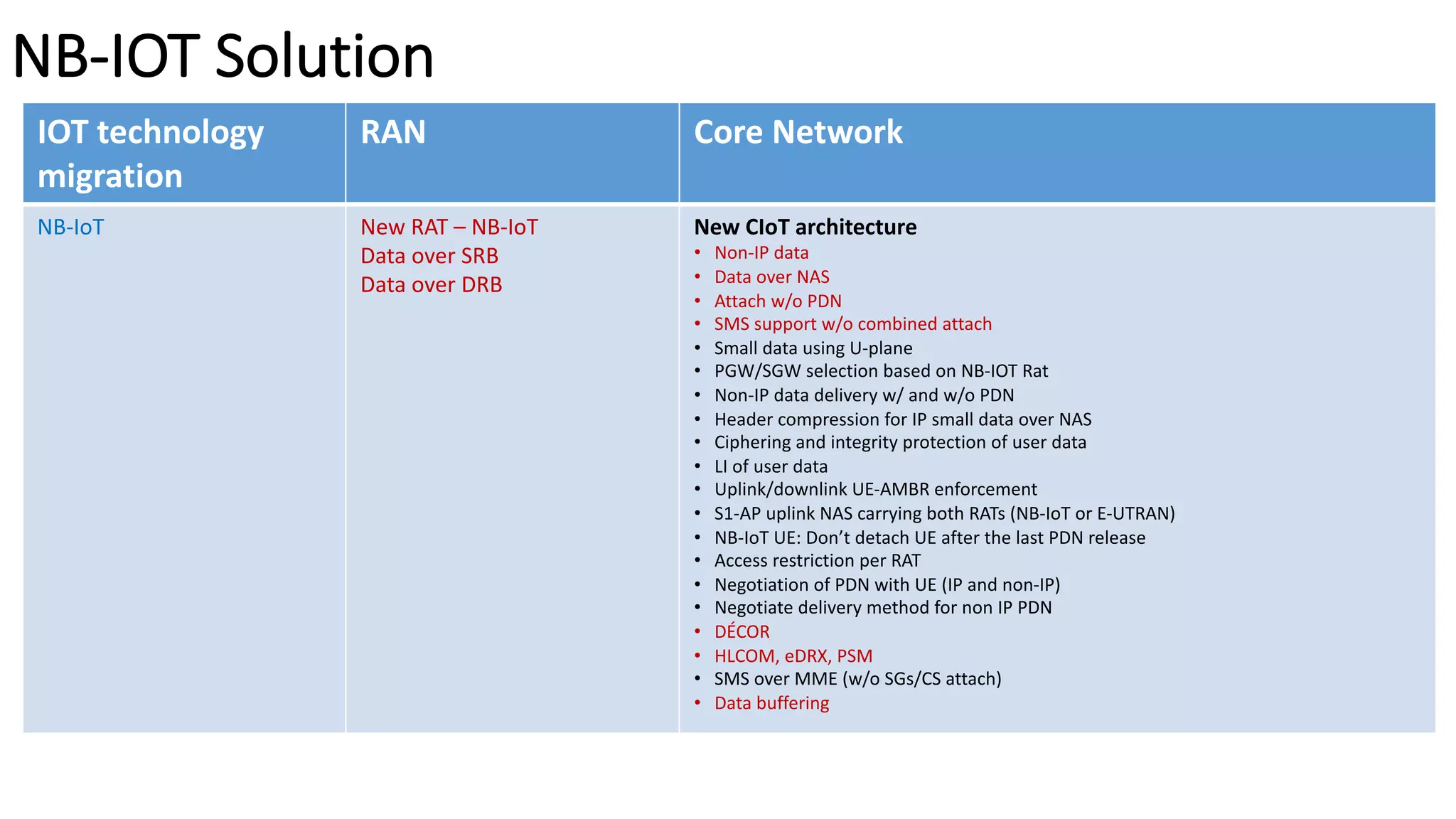
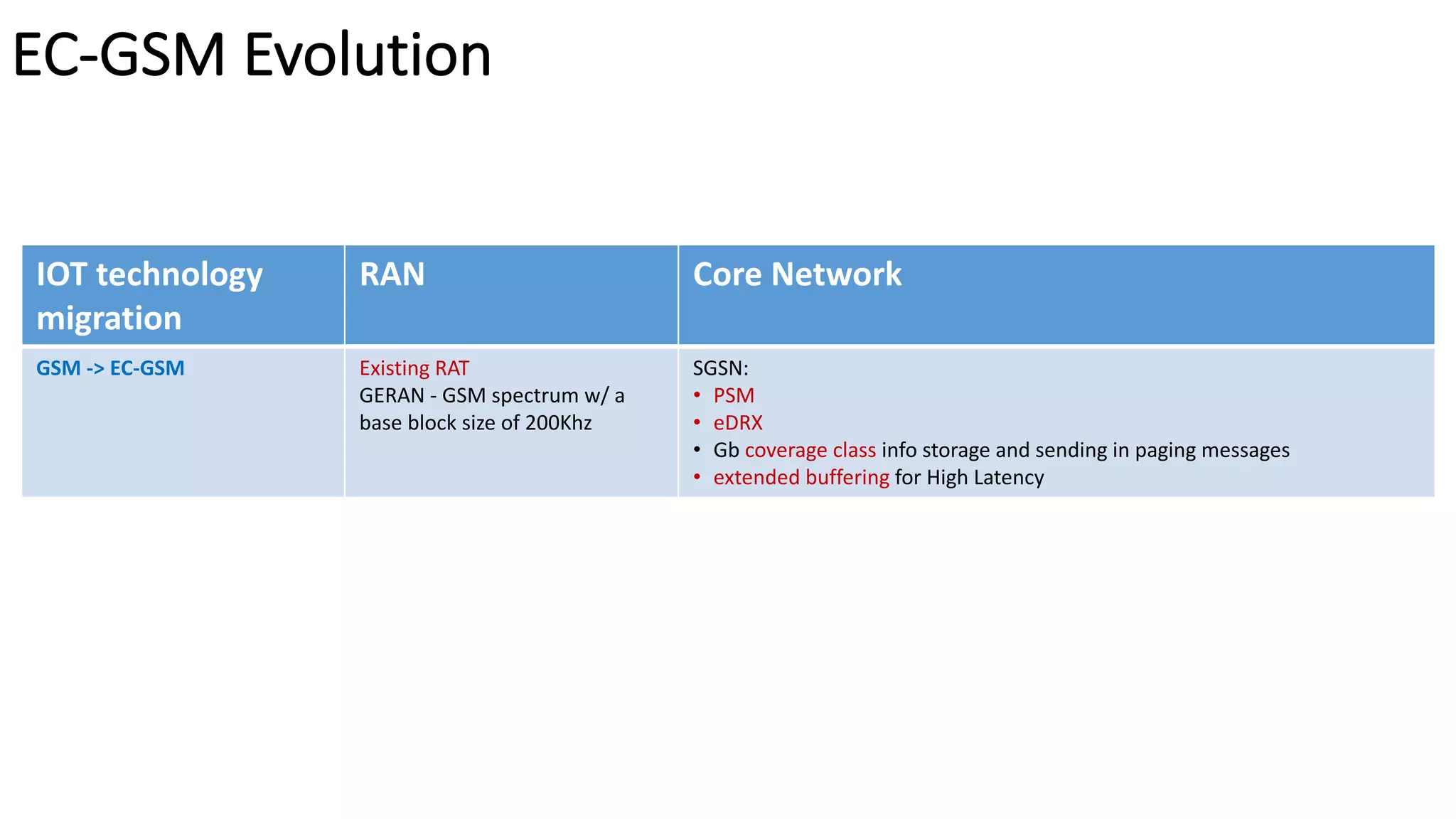
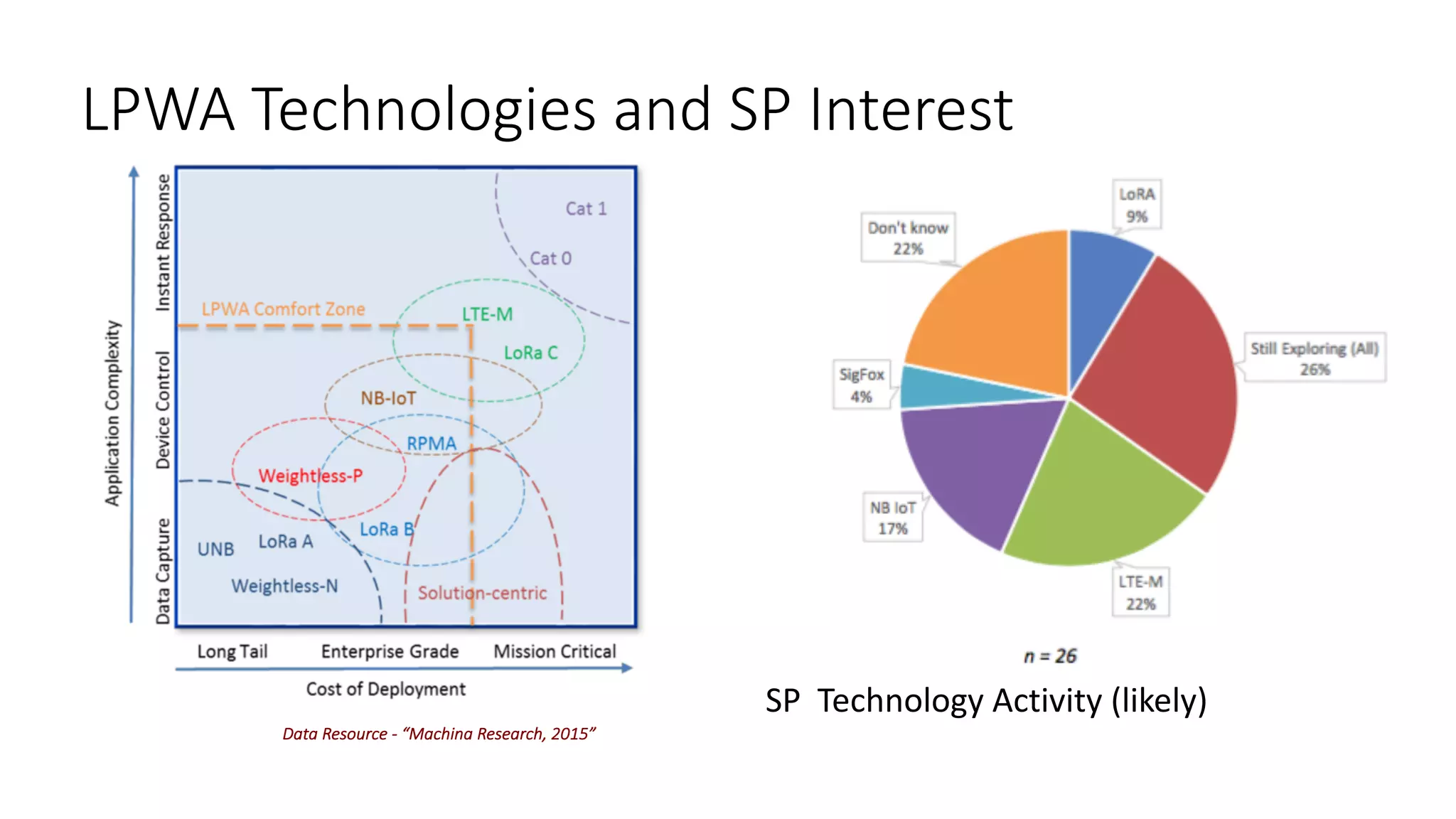
The document provides a comprehensive overview of Low Power Wide Area (LPWA) technologies and their characteristics, focusing on various connectivity options for Internet of Things (IoT) applications. It details the specifications and performance of different LPWA solutions like LoRa, Sigfox, and cellular-based options (NB-IoT, LTE-M), while highlighting their pros and cons related to deployment, cost, energy consumption, and network efficiency. Additionally, it discusses the need for tailored networks to support numerous low-power, constrained devices as the IoT landscape evolves.