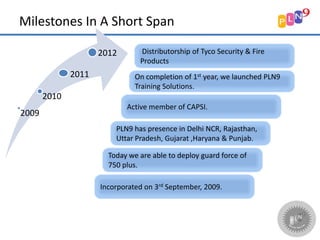
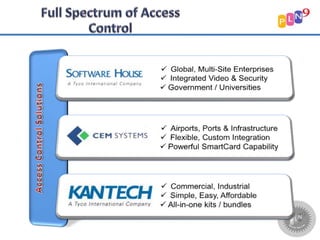
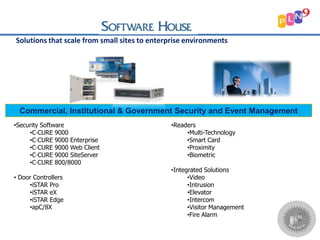
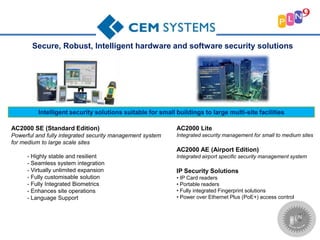
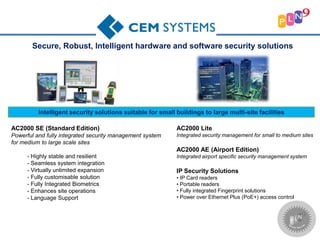
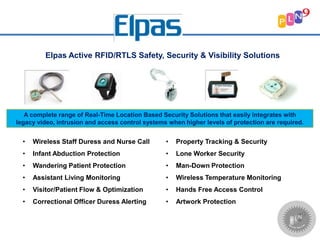
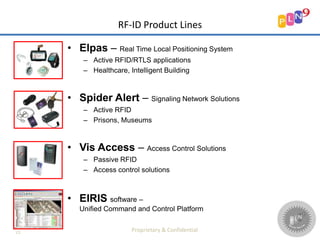
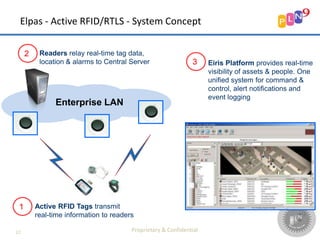
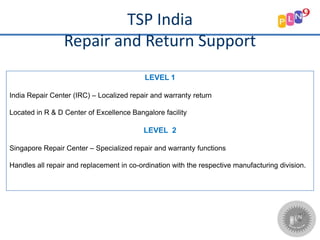
This document provides an overview of PLN9 Security Services Pvt. Ltd, including their vision, mission, values, products, and clients. Their vision is to be the most preferred security provider by satisfying customers. Their mission is to deliver reliable, safe, innovative and customer-driven security products and services. They provide security services across several Indian states and have partnerships with Tyco Security products. Their product portfolio includes access control, video surveillance, intrusion detection, and location tracking security solutions. They aim to protect several established corporate and government clients.