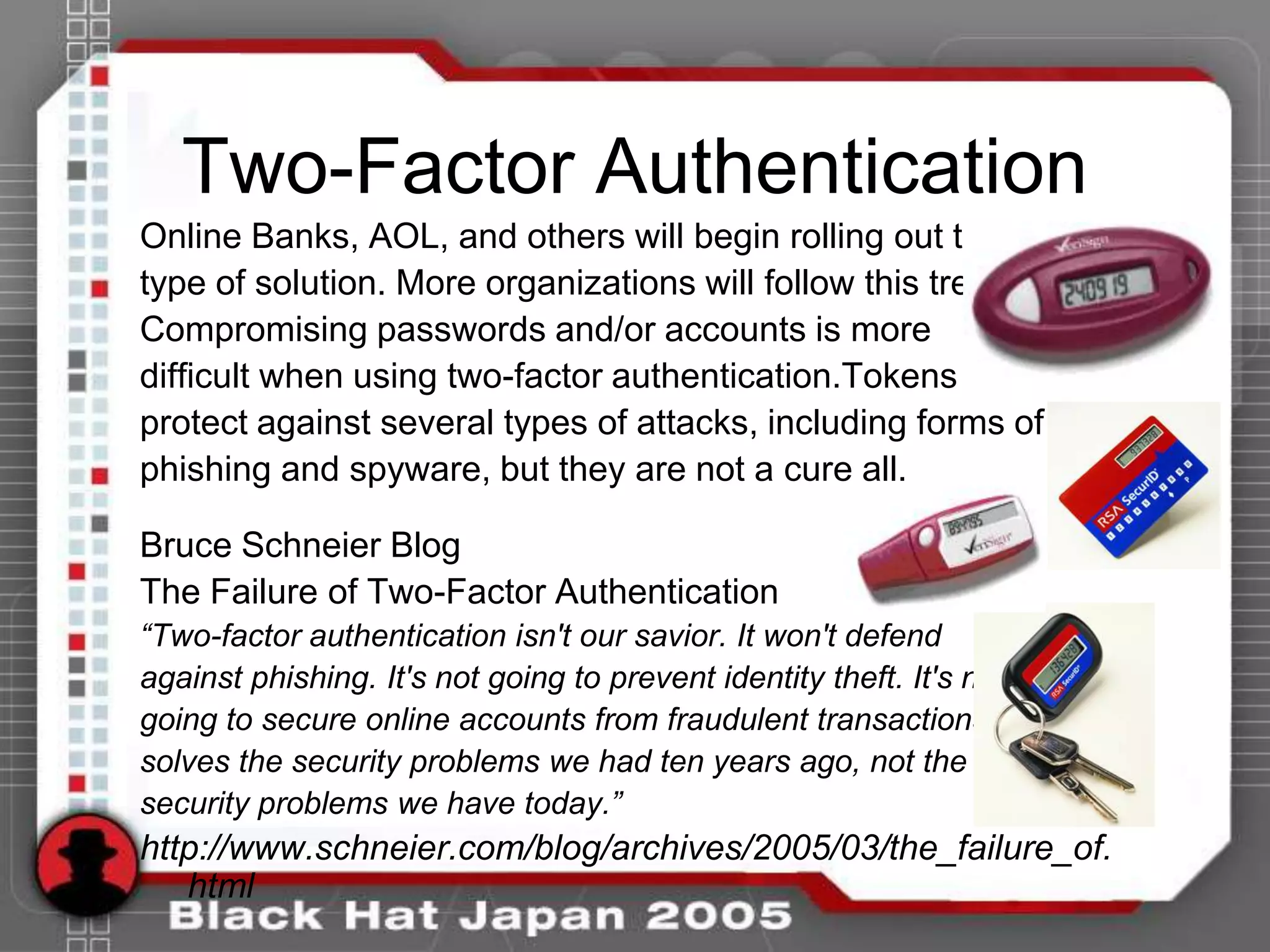
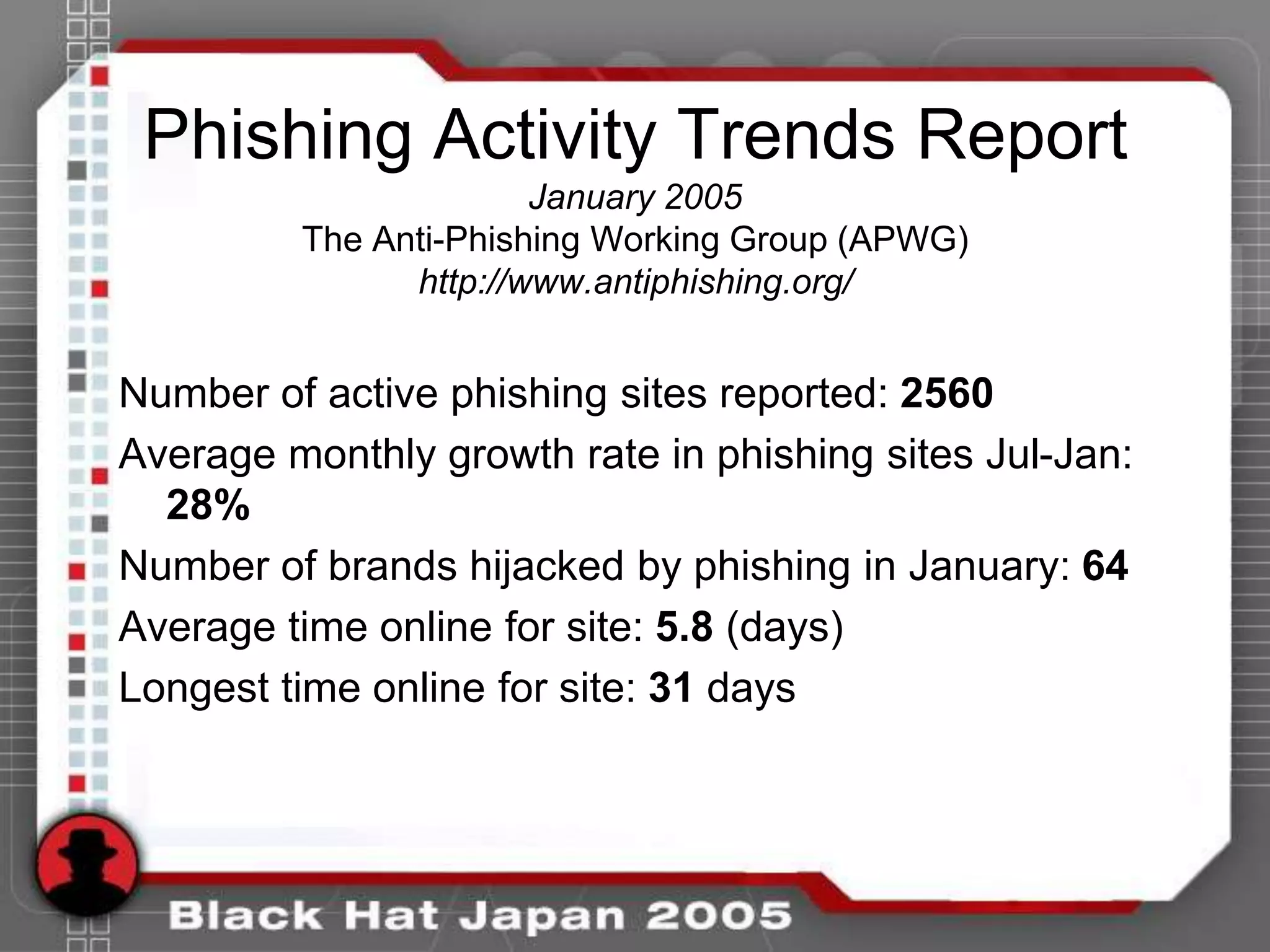
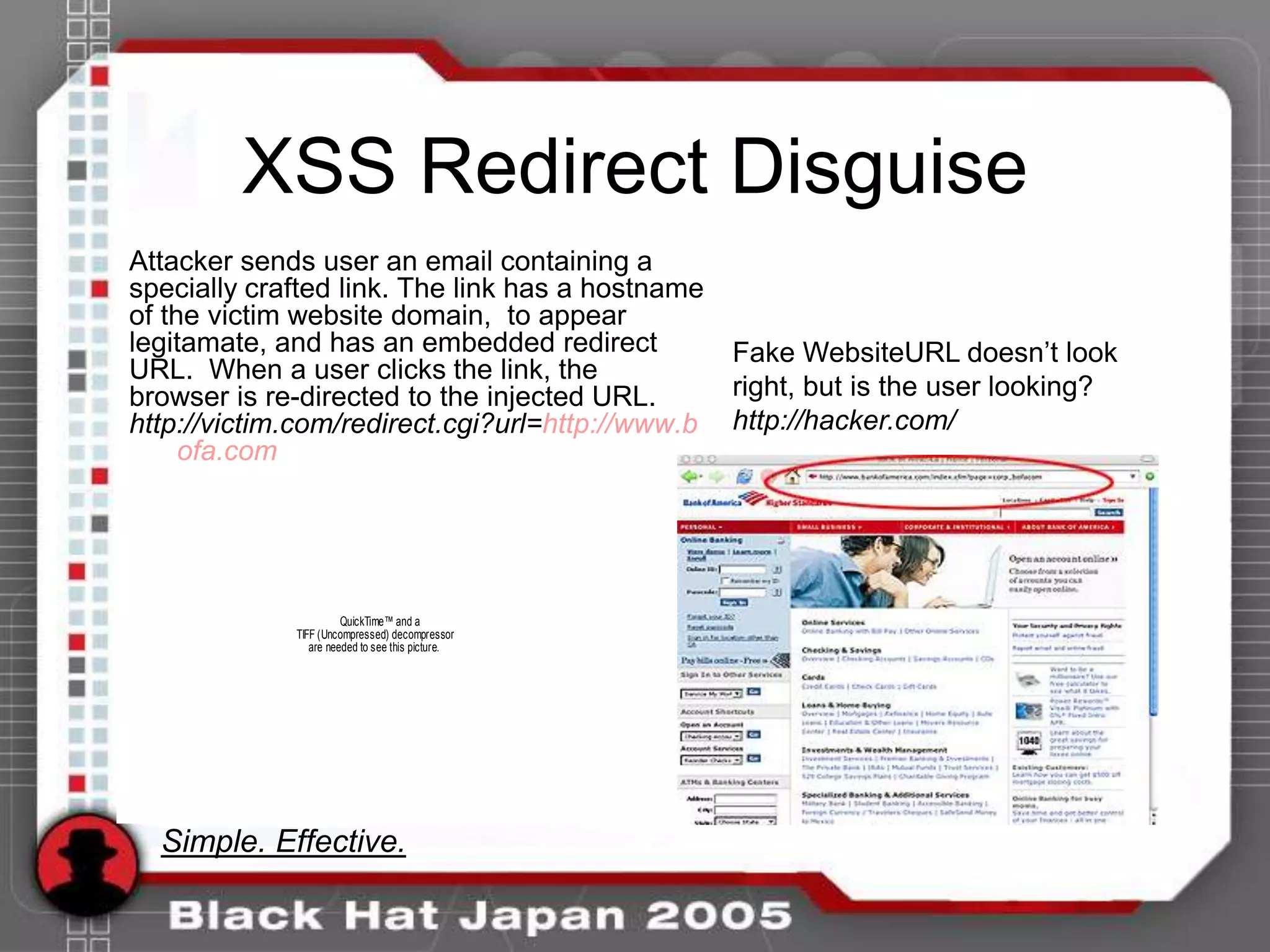
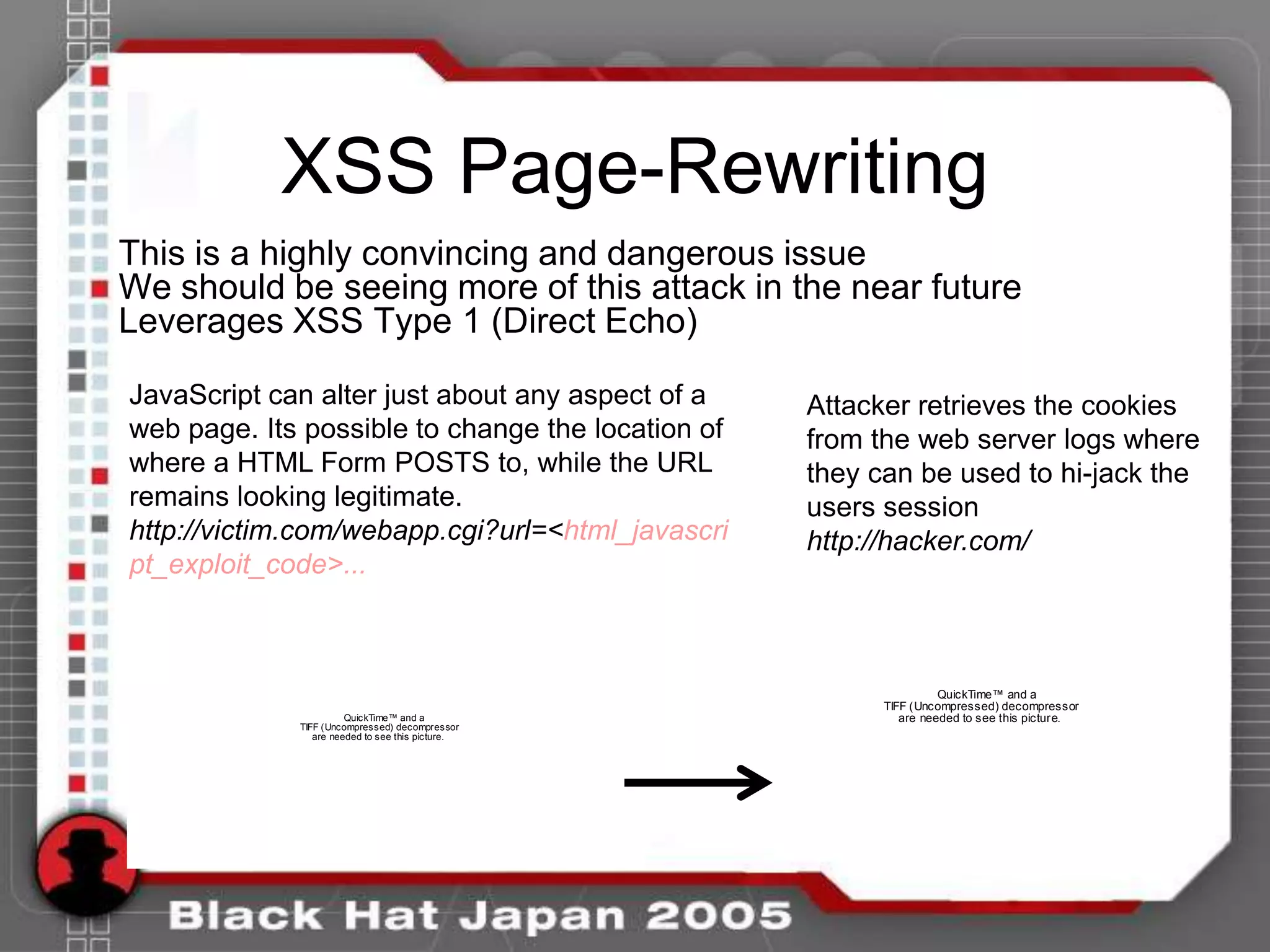
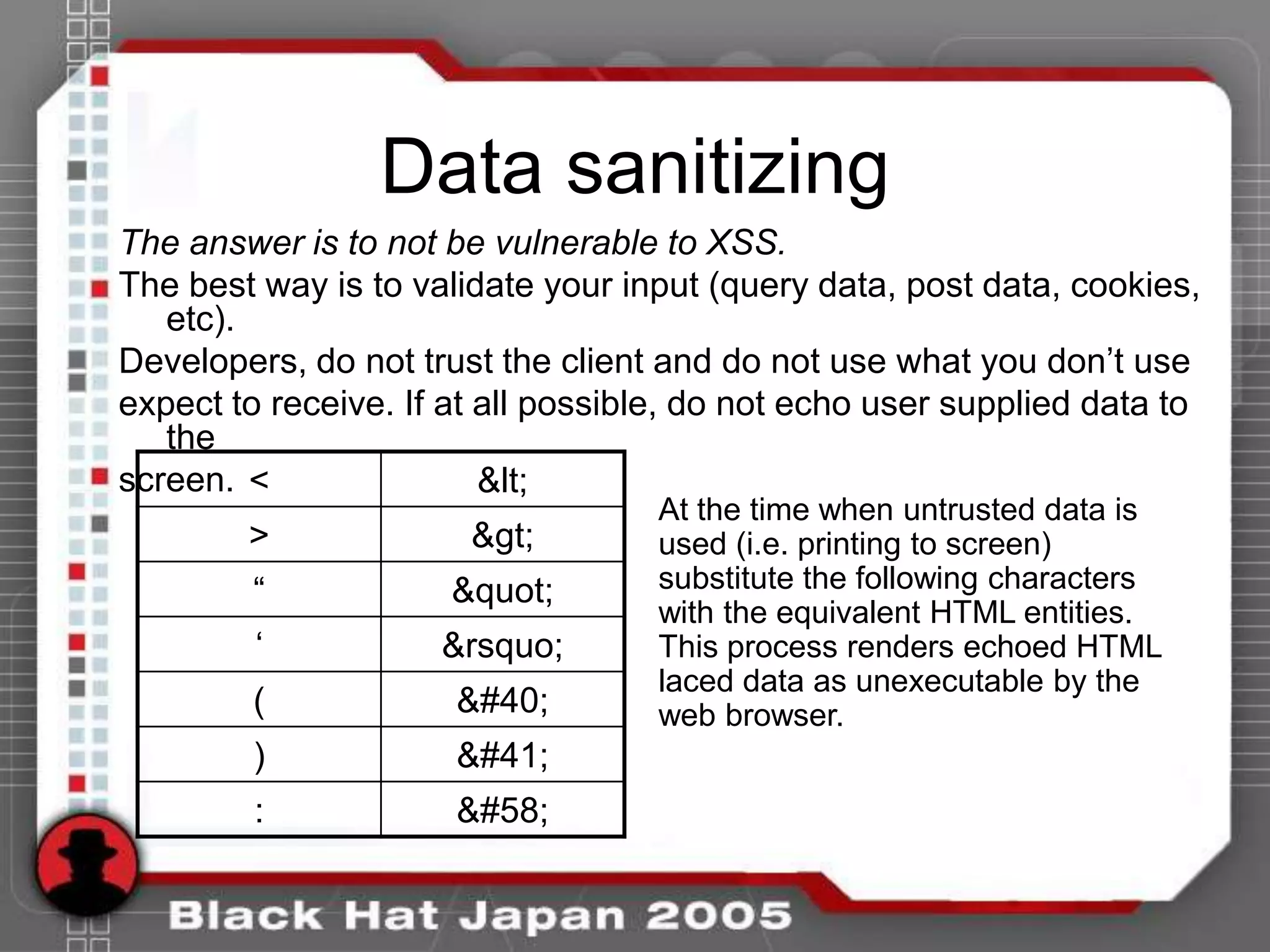
The document discusses various web security threats, focusing on phishing and cross-site scripting (XSS). It highlights the increasing sophistication of phishing attacks and introduces hybrid XSS-phishing attacks that exploit user trust, along with best practices for mitigating these vulnerabilities. Additionally, it addresses the limitations of two-factor authentication and methods for securing web applications against such threats.
![Code Snippets
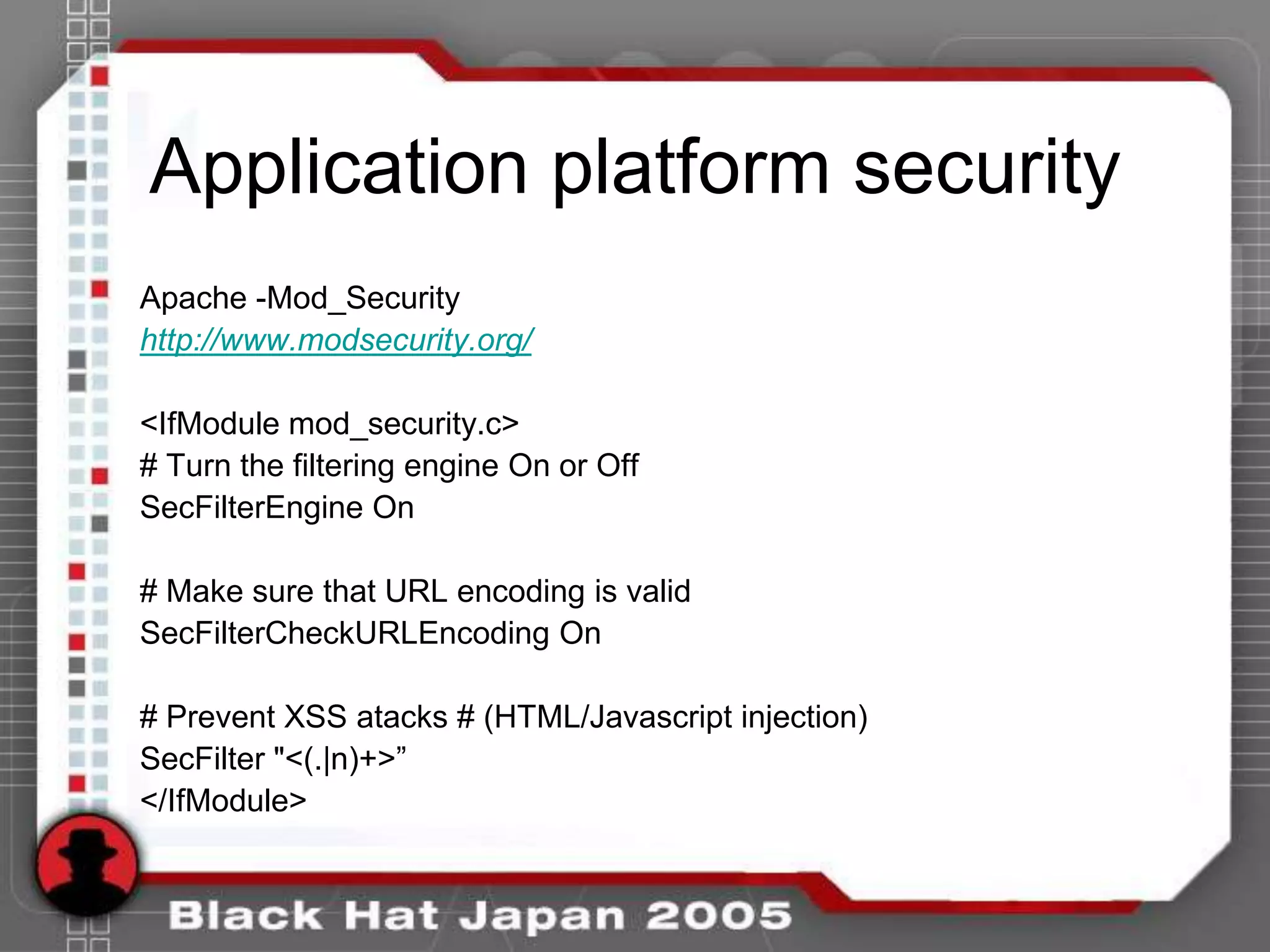
XSS Filters
Perl
$data =~ s/(<|>|"|'|(|)|:)/'&#'.ord($1).';'/sge;
or
$data =~ s/([^w])/'&#'.ord($1).';'/sge;
PHP
<?php
$new = htmlspecialchars("<a href='url'>XSS</a>",
ENT_QUOTES);
echo $new;
// <a href='url'>XSS</a>
?>](https://image.slidesharecdn.com/phishingwsuperbaitv1-0-100715101259-phpapp02/75/Phishing-with-Super-Bait-33-2048.jpg)