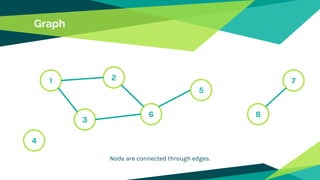
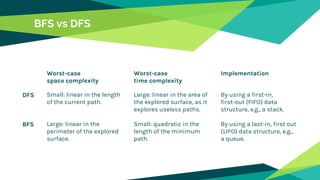
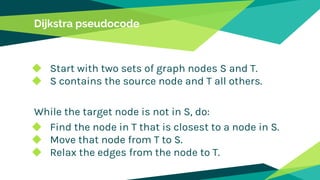
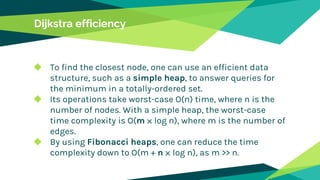
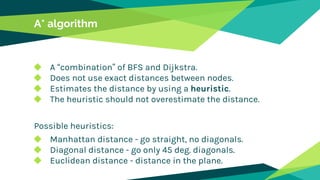
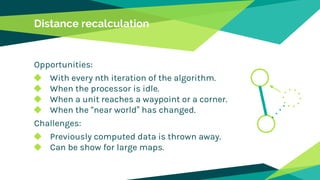
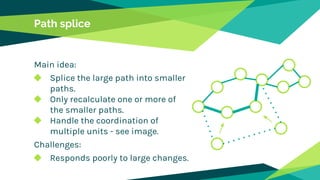
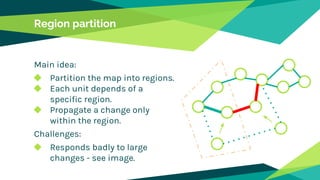
The document discusses pathfinding in games, focusing on algorithms used for navigating non-player characters and units in various gaming genres. It outlines space representation techniques, including data structures like grids and graphs, and explores several algorithms, comparing their efficiencies, such as breadth-first search, depth-first search, Dijkstra's, and A*. Additionally, it addresses challenges related to dynamic changes in the game environment and coordinating multiple units for movement.