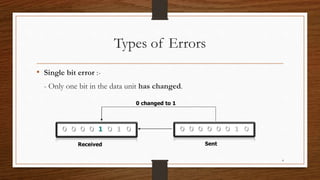
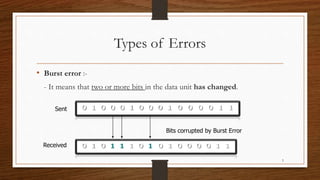
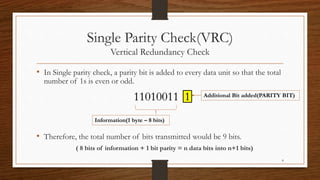
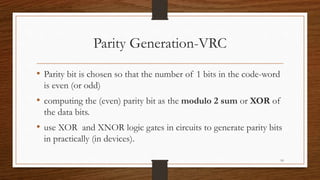
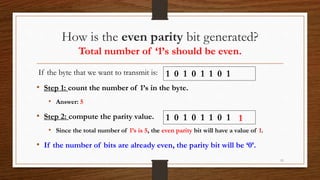
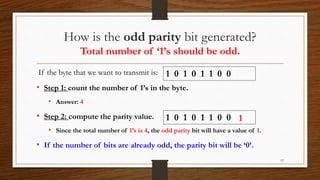
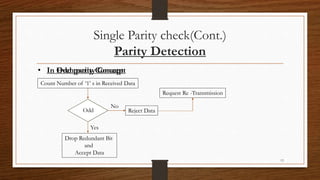
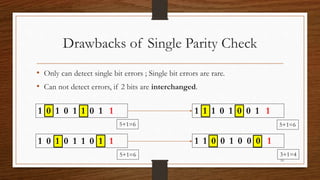
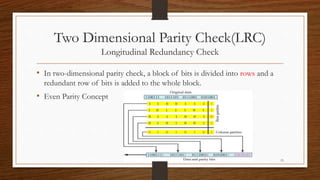
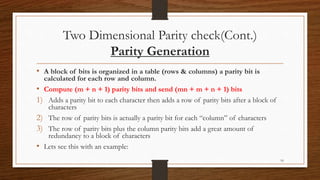
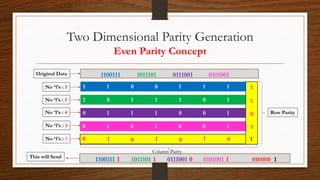
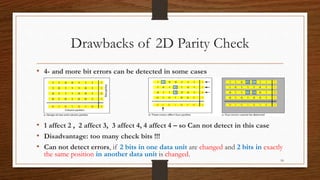
The document discusses error detection methods, focusing on parity checks, including single and two-dimensional parity checks. It highlights the types of errors that can occur during data transmission and the limitations of parity checks, especially in detecting multiple errors. Parity checking involves adding an extra bit to ensure the total number of 1's is even or odd, but it may not catch all errors, particularly double faults.