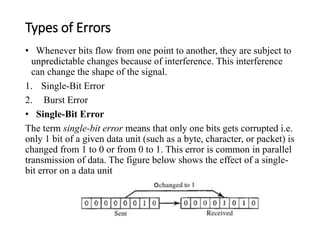
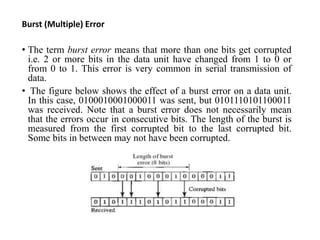
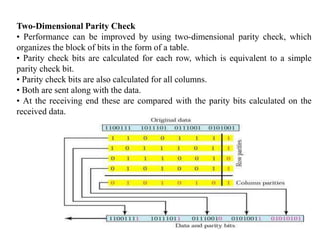
This document discusses error detection and correction techniques used in digital communications. It describes how errors can occur during data transmission and why error detection and correction is needed. It then explains different types of errors and various error detection techniques like parity checks, checksums, and cyclic redundancy checks. Finally, it discusses error correction techniques like backward error correction using retransmissions and forward error correction using redundant bits and provides an example of Hamming codes.