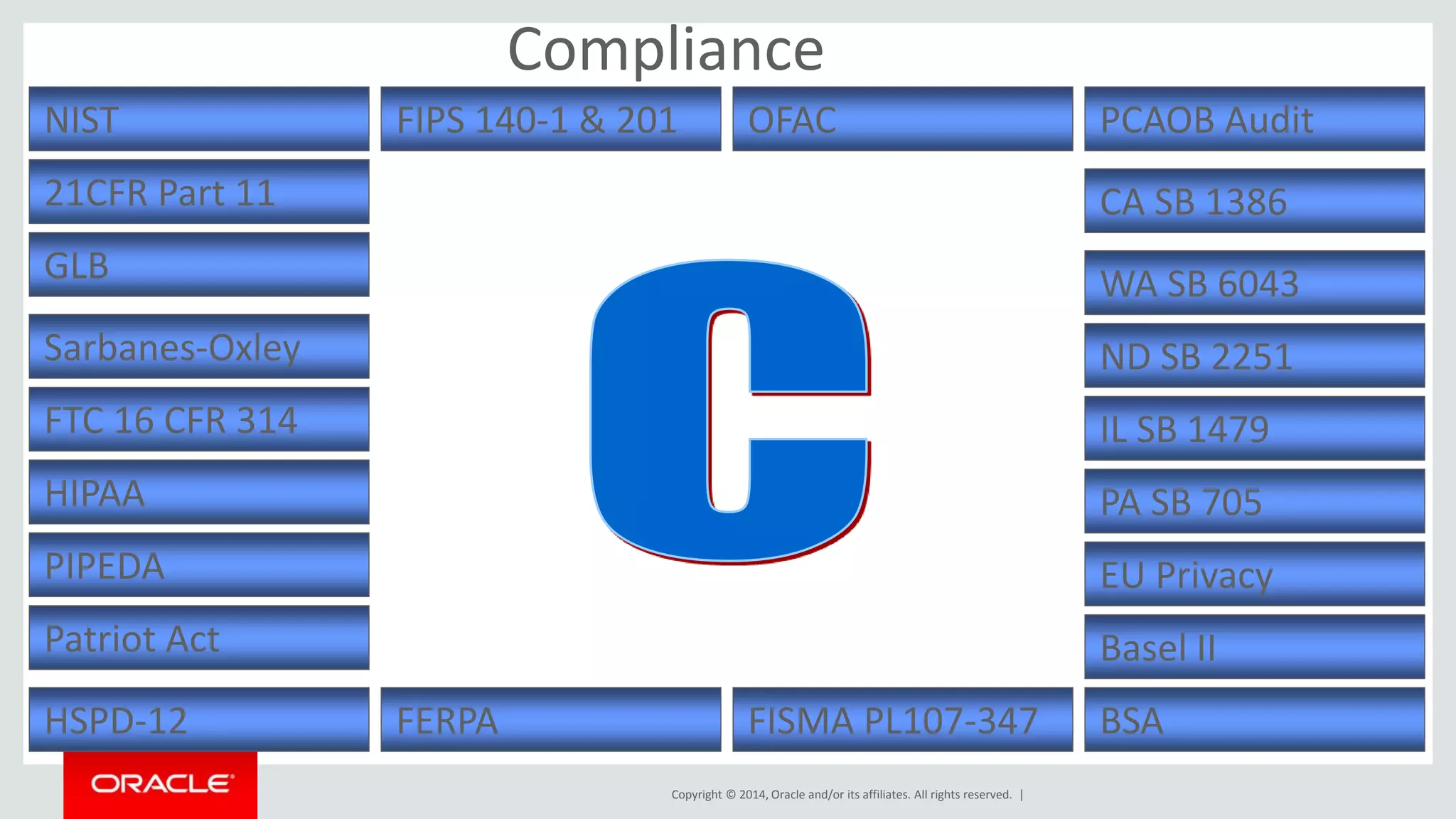
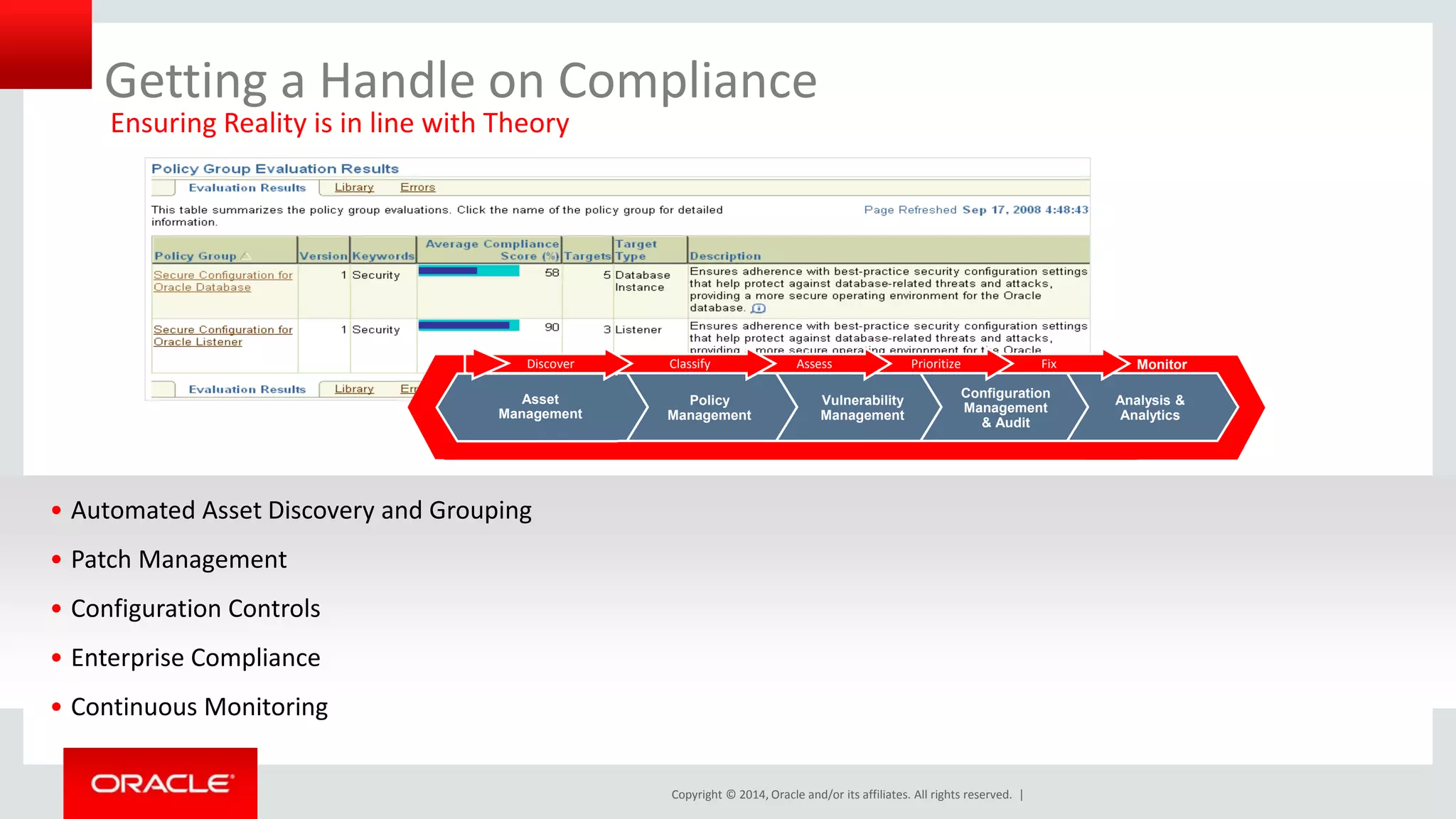
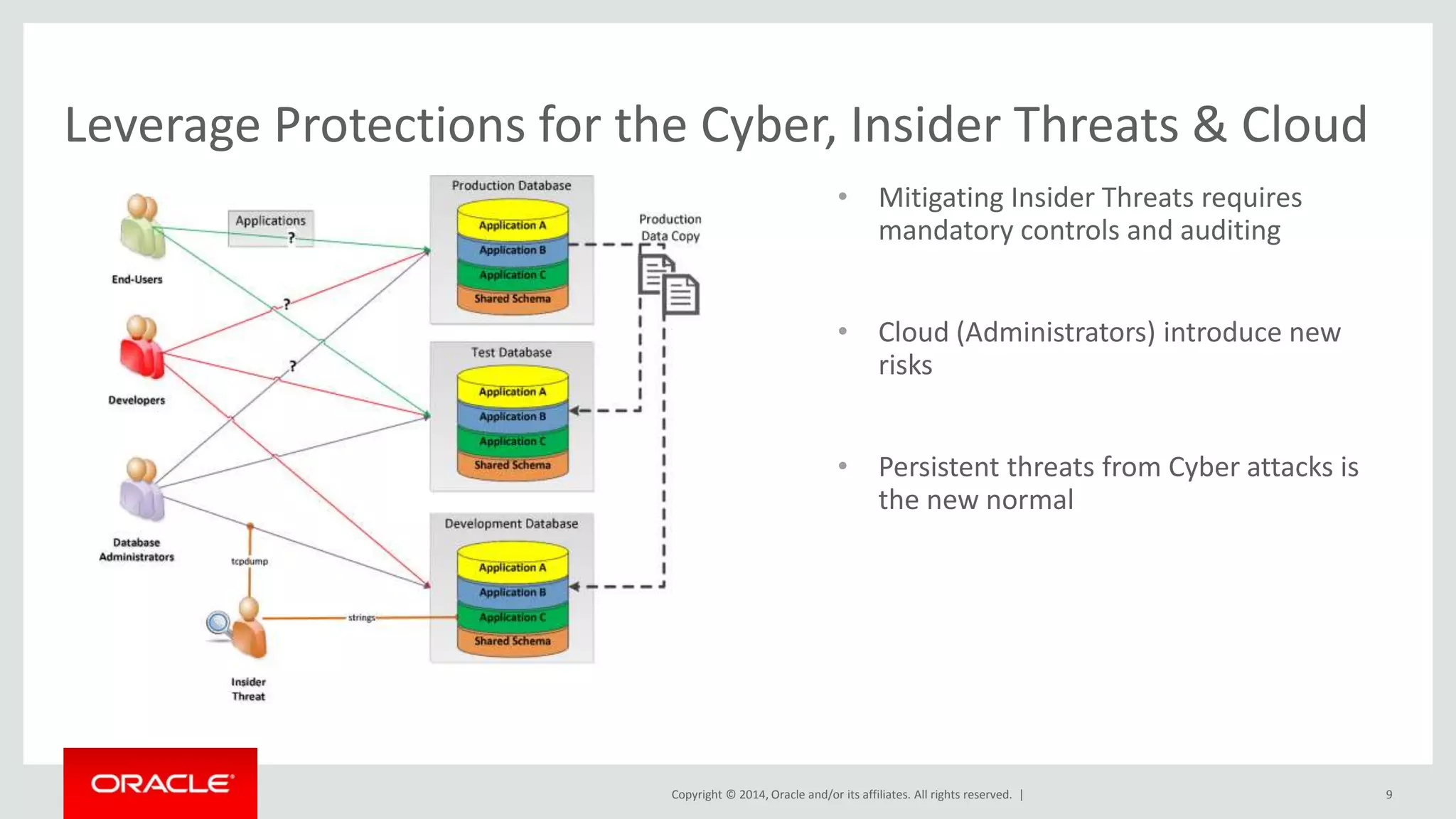
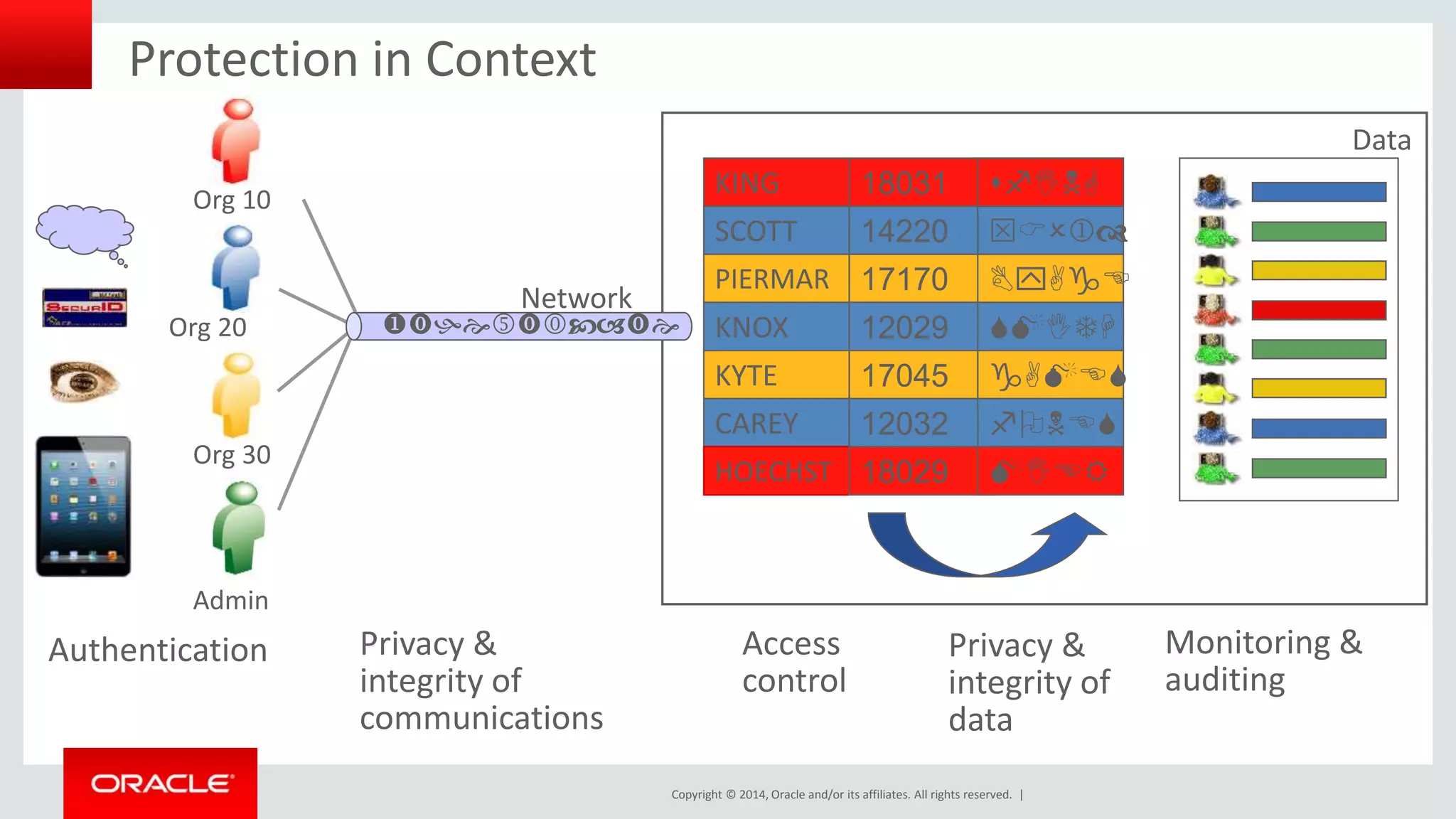
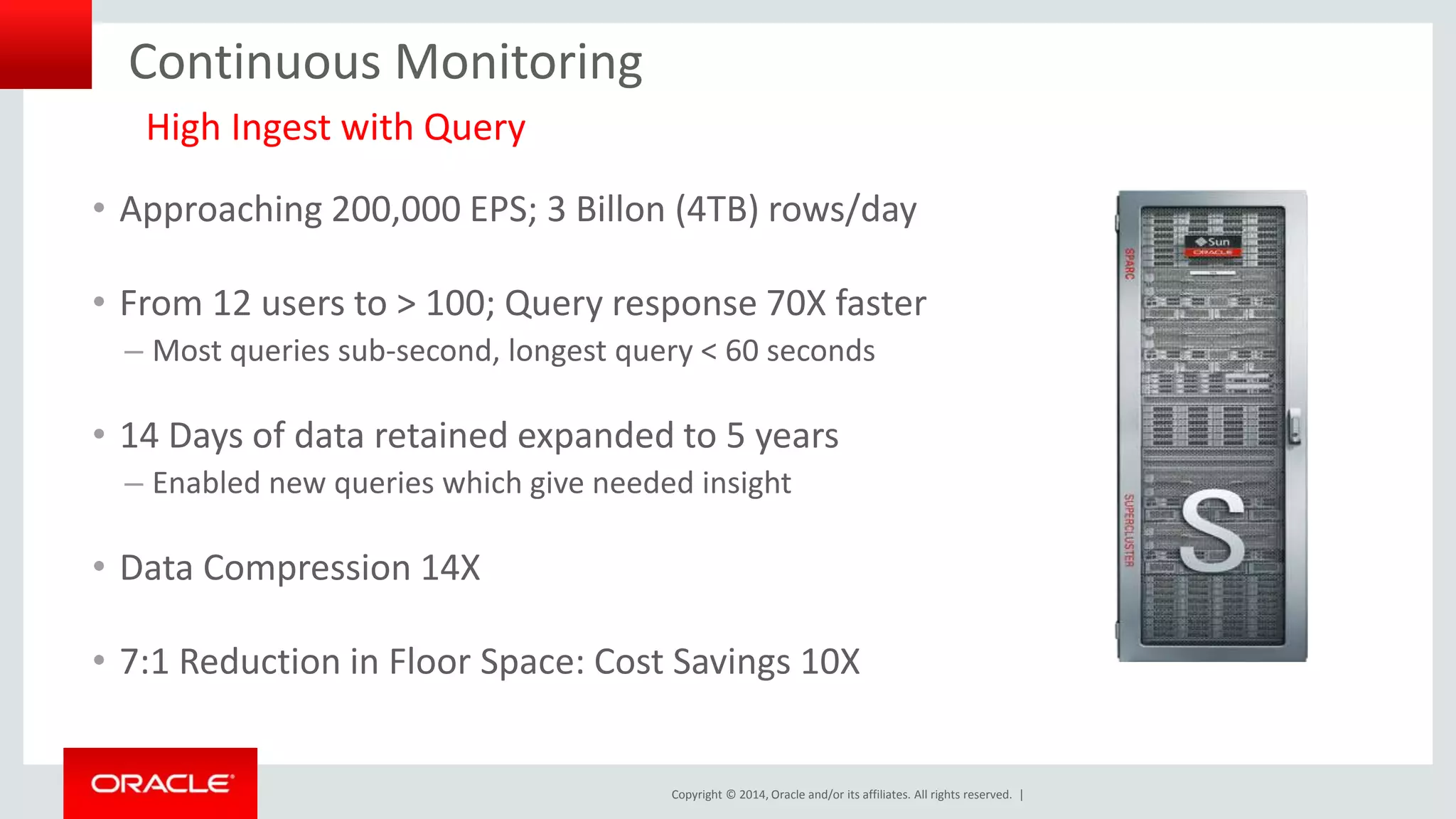
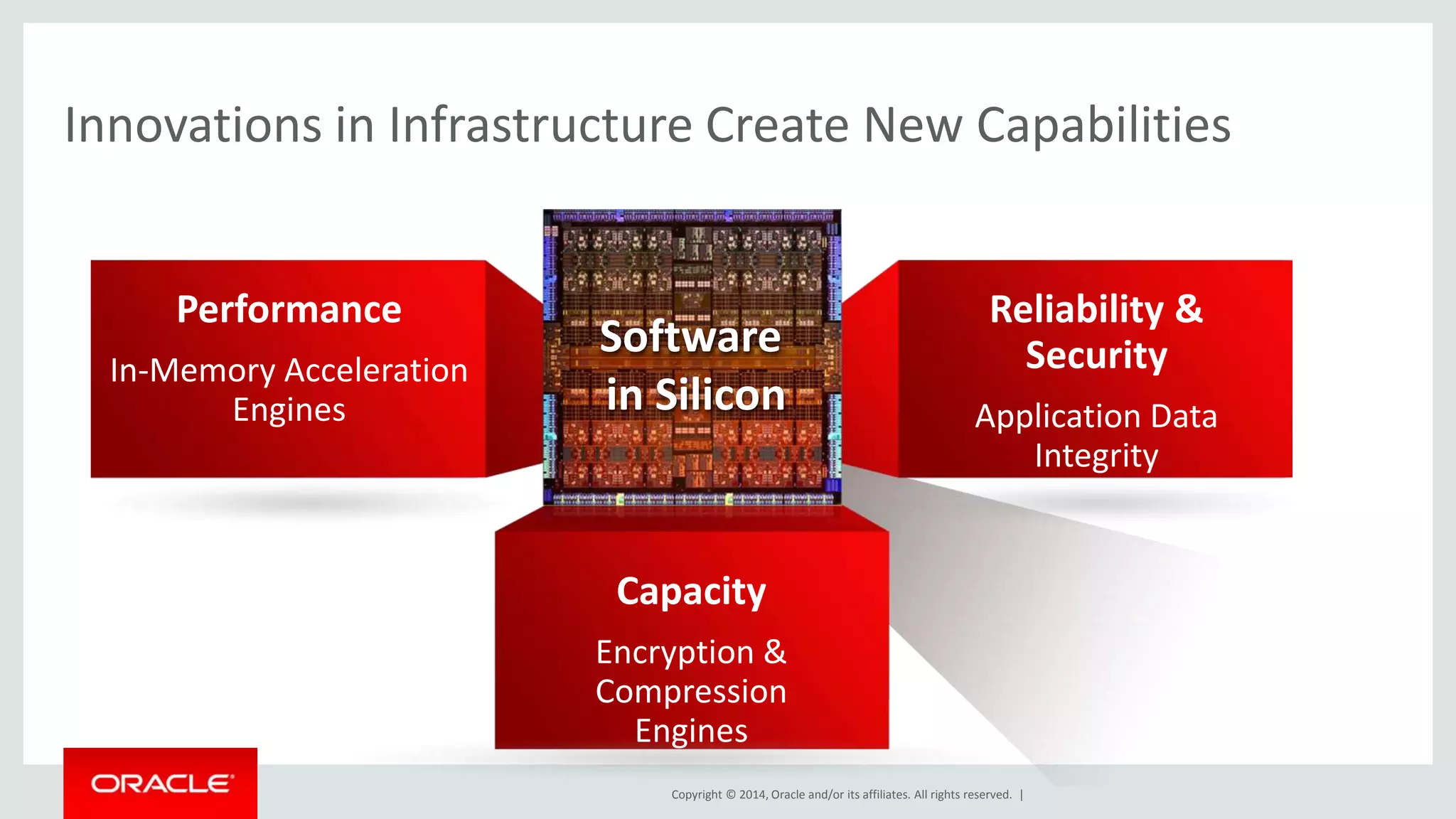
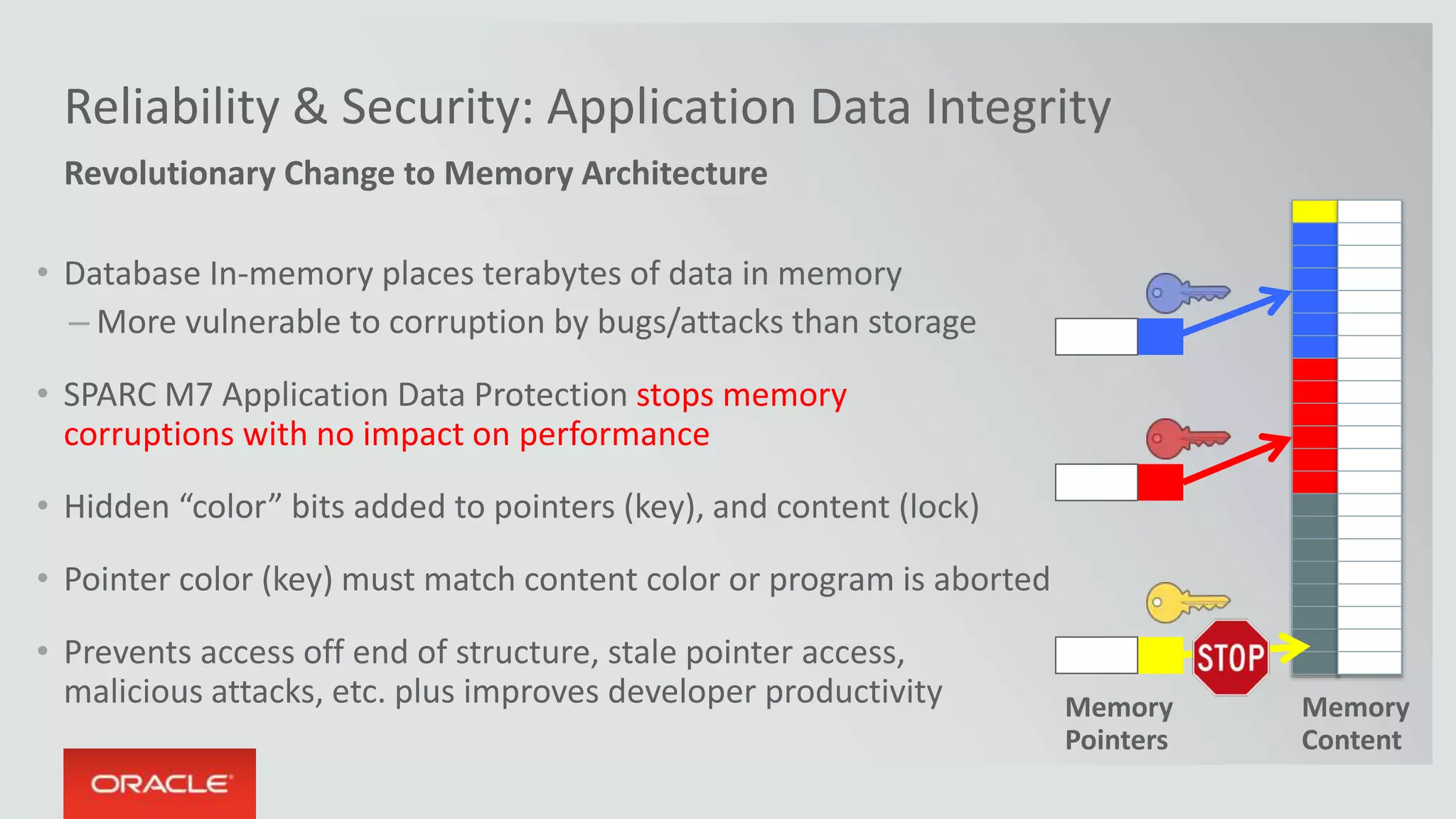
The document outlines a pragmatic approach to creating a secure information environment, emphasizing the importance of governance, compliance, and innovative technologies. It discusses challenges such as insider threats and cyber attacks while highlighting the need for continuous monitoring and advanced data protection techniques. The conclusion advocates for an integrated security strategy that combines technology innovations with practical governance measures.