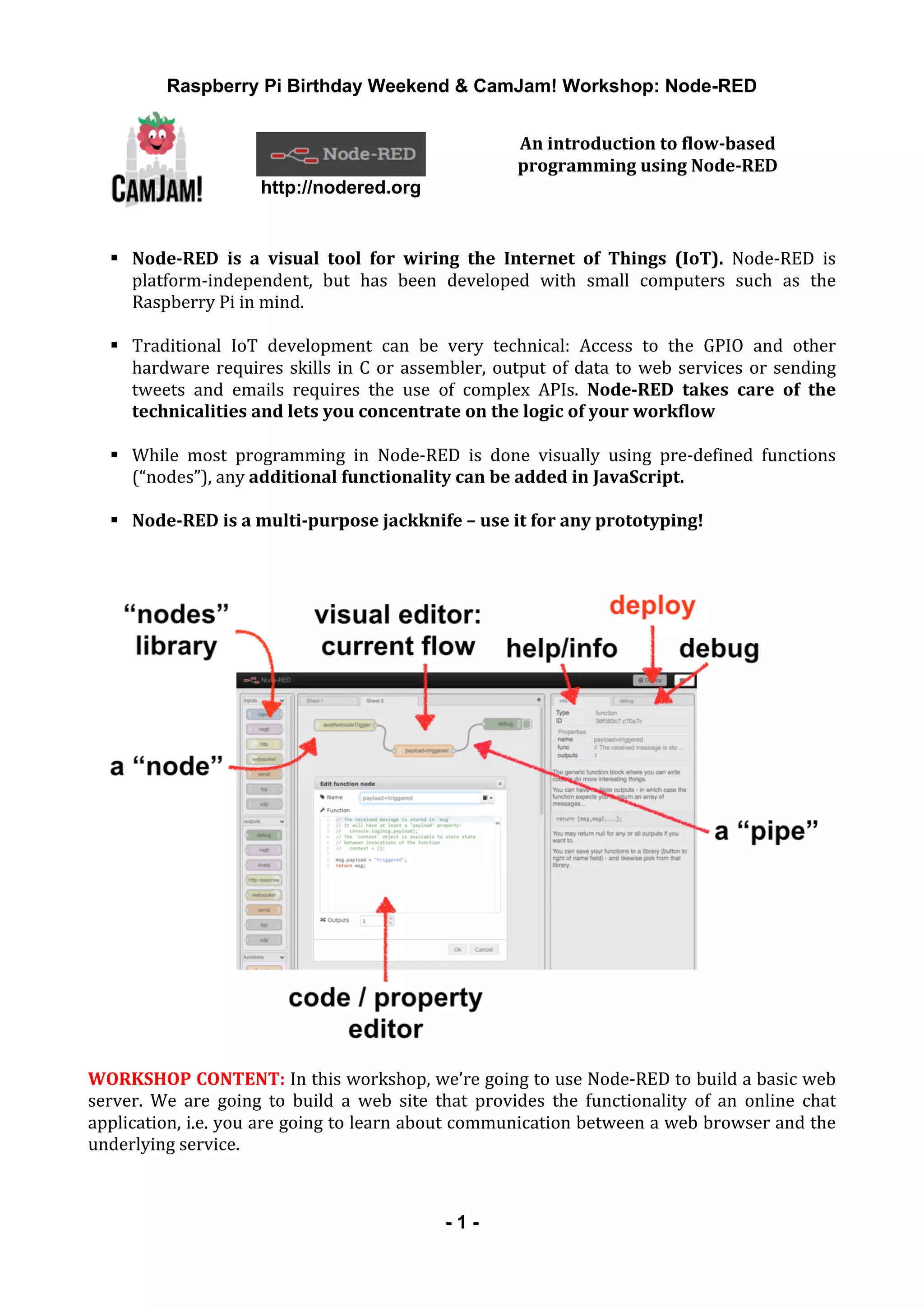
The document outlines a workshop focused on using Node-RED, a platform for flow-based programming, particularly designed to simplify Internet of Things (IoT) applications on devices like Raspberry Pi. Throughout the workshop, participants learn to create a basic web server and engage in exercises that build functionality for online chat applications, utilizing Node-RED's graphical interface to manage server-client communication. The document also provides technical prerequisites, installation guidance, and additional experimental suggestions to extend the learning experience.




![Raspberry Pi Birthday Weekend & CamJam! Workshop: Node-RED
- 6 -
6)
Exercise:
Returning
the
result
of
a
web
form
to
Node-RED
So
far
our
interaction
between
the
server
and
the
client
was
rather
unidirectional.
Following
the
http
request,
us
injecting
or
not
injecting
a
message
determined
the
actual
outcome.
Now,
we
extend
the
example
so
that
the
return
value
is
dependant
on
the
user’s
input.
1. Drag
and
drop
a
“http”
input
node,
a
“template”
node
and
a
“http“
output
node
into
your
flow.
Set
the
input
node
to
respond
to
GET
request
on
/login.
Wire
the
nodes
together
as
shown
below:
2. Add
the
following
HTML
to
your
template
node:
<form action="http://localhost:1880/chat" method="post">
<b>User</b><br> <input type="text" name="user"/><br>
<button type="submit">Submit</button>
</form>
3. Add
another
set
of
four
nodes
to
your
flow.
Configure
the
http
input
node
to
respond
to
POST
requests
at
/chat.
This
is
how
your
server
is
going
to
react
to
form
submissions:
4. Edit
the
function
node
to
extract
the
content
of
the
incoming
input
field
“user”
(if
not
empty)
and
assign
it
to
our
standard
payload:
if (msg.req.body["user"] != "") {
msg.payload = msg.req.body["user"]
}
return msg;
5. The
template
node
can
simply
say:
The user’s name is: {{payload}}
6. Deploy
and
test
your
flow
at
localhost:1880/login.
Does
it
do
what
you
expect?
If
so:
Congratulations,
you’re
now
seeing
the
key
ingredients
to
a
basic
chat
server.
Exercise
7:
Putting
it
all
together
In
the
next
step
we’re
going
to
put
all
of
our
new
skills
together.
To
build
a
basic
chat
server,
all
we
need
is
a
little
more
trickery
with
the
context.global
to
retain
our
conversation
(we’re
going
to
use
context.global.dialog),
some
HTML
concept
called
iframe
to
separate
an
input
field
from
the
conversation,
and
a
bit
of
client-‐sided
JavaScript
to
auto-‐update
the
iframe.](https://image.slidesharecdn.com/node-red-camjam-pi-birthday-feb2015-150215080731-conversion-gate01/85/An-introduction-to-workflow-based-programming-with-Node-RED-6-320.jpg)
![Raspberry Pi Birthday Weekend & CamJam! Workshop: Node-RED
- 7 -
1. Rewrite
the
function
node
following
the
/chat
http
input
like
this:
if (msg.req.body["user"] != "") {
msg.payload = msg.req.body["user"]
}
if (msg.req.body["message"] != undefined) {
context.global.dialog +=
msg.req.body["user"]+':'+msg.req.body["message"]+"<BR>";
}
context.global.dialog = context.global.dialog || "";
return msg;
2. The
template
node
hides
most
of
the
trickery:
<iframe src="http://localhost:1880/dialog" name="iframe_a" width="90%"
height="70%"></iframe>
<form name="frm" action="http://localhost:1880/chat" method="post">
<b>Message from {{payload}}</b><br>
<input type="text" name="message" size="90%"/>
<input type="hidden" name="user" value="{{payload}}"><br>
<button type="submit">Submit</button>
</form>
<SCRIPT language="JavaScript">
window.setInterval("reloadIFrame();", 1000);
function reloadIFrame() { window.frames["iframe_a"].location.reload(); }
</SCRIPT>
3. We
need
another
set
of
http
input,
function,
template
and
http
out
nodes.
These
will
represent
the
/dialog
page
that’s
shown
in
the
iframe.
The
code
is
fairly
simple.
4. Add
to
function
node
node
following
the
/dialog
http
input
msg.payload =
context.global.dialog;
before
return msg;
5. The
template
node
just
says:
{{payload}}
6. Deploy
your
web
server.
Open
localhost:1880/login
from
two
different
browser
windows
and
login
with
different
identities.
Both
windows
will
update
their
iframe
once
a
second,
showing
/dialog
as
it
continues
to
grow
on
the
server
with
lines
that
are
sent
via
the
form
field
“message”
from
either
client.](https://image.slidesharecdn.com/node-red-camjam-pi-birthday-feb2015-150215080731-conversion-gate01/85/An-introduction-to-workflow-based-programming-with-Node-RED-7-320.jpg)
