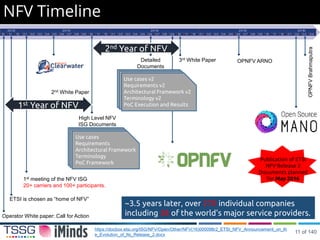
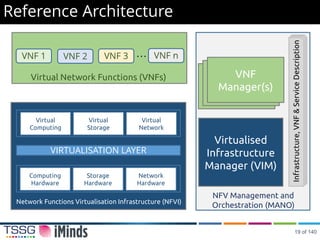
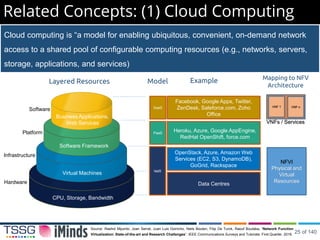
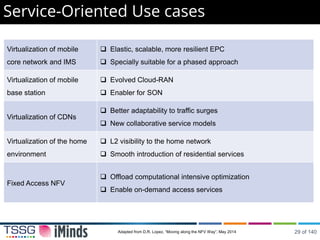
The document outlines the conception, current state, and future challenges of Network Functions Virtualization (NFV) presented at the Network Operations and Management Symposium in 2016. It covers NFV's motivations, architecture, proofs of concept, and related concepts like Software Defined Networking (SDN) and cloud computing, highlighting its benefits in reducing operational costs and enhancing service agility. The document also discusses future research directions and use cases for NFV in various domains such as telecommunications and cloud services.







![Anticipated Benefits Survey
Source: sdxcentral.com ,
Reduce Capital
Expenditures
13% Accelerate Time To
Market
14%
Reduce Operational
Expenditures
23%
Deliver Agility and
Flexibility
50%
SDxCentral survey involving 79 end-user respondents, including service providers, (46%), cloud service
providers (14%), enterprise end users (14%) and a variety of others (24%) from user communities.
NFV Hardware, Software, and Services had an estimated EUR 2.1 Bn value
in 2015, forecast to grow to EUR 10.6 Bn in 2019, [50% CAGR]
IHS Infonetics NFV Hardware, Software, and Services Report, 2015. https://www.ihs.com/index.html
10 of 140](https://image.slidesharecdn.com/noms2016nfvtutorial2-160501073053/85/NFV-Tutorial-10-320.jpg)


![VNF Design Patterns
Internal Structure
Virtualization
container
VNFC 1 VNFC 2
VNFC 4 VNFC 3
VNF with multiple
components
VNFC 1
VNF with single
component
VNF 1 VNF 1
VNF Instantiation VNFC 1
Non-parallelizable
VNFC
VNF 1
[1:1]
parallelizable VNFC
(min. & max. # of instances
VNF 1
VNFC 1
[1:n]
VNFC States
VNFC 1
Stateless VNFC
VNF 1
state
VNFC 1
Stateful VNFC
VNF 1
state
stateVNFC 1
VNFC with
external state
VNF 1
14 of 140](https://image.slidesharecdn.com/noms2016nfvtutorial2-160501073053/85/NFV-Tutorial-14-320.jpg)





















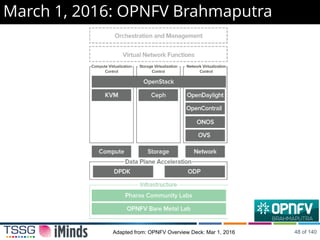
![June 4, 2015: OPNFV Arno
Initial build of the NFV Infrastructure (NFVI)
and Virtual Infrastructure Manager (VIM)
components of ETSI NFV architecture.
Baseline foundation to enable continuous
integration, automated deployment and testing
of components necessary to build an NFV
platform from upstream components such as
OpenDaylight, OpenStack, Open vSwitch,
Ceph & KVM.
Aimed at exploring NFV deployments,
developing VNF applications, or NFV
performance and use case-based testing.
[10/01/2015] Arno SR1: Designed to address known issues in the
initial release for incremental stability and improved predictability.
47 of 140](https://image.slidesharecdn.com/noms2016nfvtutorial2-160501073053/85/NFV-Tutorial-41-320.jpg)




![OSM Members: April 06, 2016
ParticipantsMembers
Within the next two months [May/June], OSM will launch Release 0, integrating and
documenting the code base from Telefonica, RIFT.io, Canonical and others.
New OSM releases are to be issued every six months
https://osm.etsi.org/ 54 of 140](https://image.slidesharecdn.com/noms2016nfvtutorial2-160501073053/85/NFV-Tutorial-48-320.jpg)





































![Set Login Password
1
use cloud-init to
assign a password
[noms2016] for the
user [ubuntu] to
login into the
instance
2
3
Launch Instance
4
99 of 140](https://image.slidesharecdn.com/noms2016nfvtutorial2-160501073053/85/NFV-Tutorial-90-320.jpg)