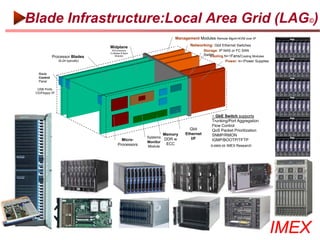
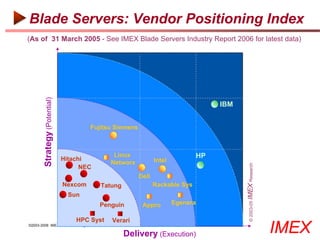
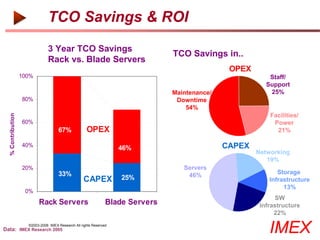
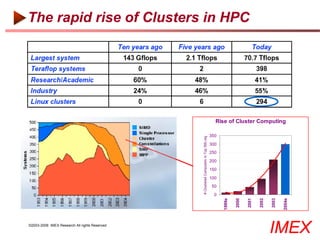
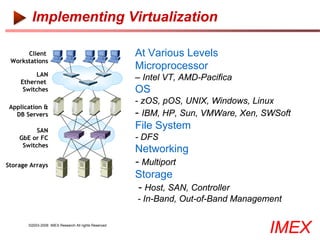
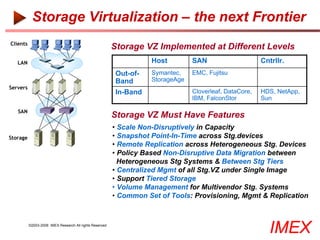
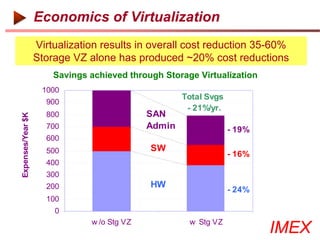
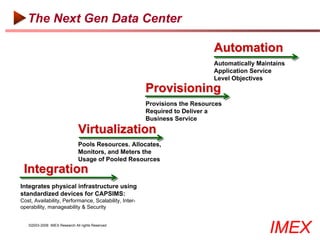
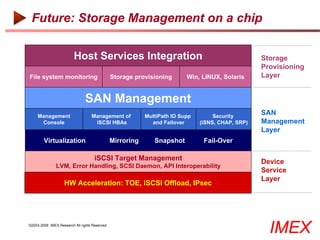
The document discusses implementing a next generation data center using server blades, clustering, and virtualization. It describes consolidating servers onto blade servers with shared networking, storage, power and cooling infrastructure for improved utilization and management. Key benefits include reduced costs, improved availability, manageability and scalability compared to traditional server architectures.